Valentine's Day is super stressful. From getting a gift that's personal but not TOO personal (like Spanx because she always complains about her muffin top, for instance) to picking out a bouquet of her favorite flowers, you probably have a lot on your plate.

Purchasing a present for your sweetheart on Valentine's Day is stressful enough. If you go with something too personal - like some expensive Spanx underwear because she always complains about her muffin top - she'll get offended, but if you go with something too cliche and general - like a box of chocolates - she'll think you don't care.

Christmas sweaters are one of those anomalies that everyone complains about, yet so many are sold every year that someone has to like them (kind of like fruitcake). Whether you're keeping tradition for tradition's sake, or secretly you actually enjoy ugly sweaters (we won't tell anyone), why not at least make this year one to remember?

Welcome back to another episode of Java Tutorials, In today's tutorial, we'll be learning about what methods are, proper syntax when writing Methods, and why they are beneficial in a program's code.

Since I recently had this problem and fixed it, I might as well share the solution. This is actually REALLY simple to fix but will impact your cards' performance.

Getting root is considered the Holy Grail in the world of Linux exploitation. Much like SYSTEM on Windows, the root account provides full administrative access to the operating system. Sometimes even a successful exploit will only give a low-level shell; In that case, a technique called privilege escalation can be used to gain access to more powerful accounts and completely own the system.

The latest update to iOS 10 brought with it a number of great new features. Of these, the one that will likely have the most impact on people's iOS experience in the long term are the new apps and stickers for iMessage.

It's no secret that devices leak data, but sometimes they do so in ways you may not expect. Your phone, laptop, printer, and IOT devices leak Wi-Fi information that can (and is) used to track you.

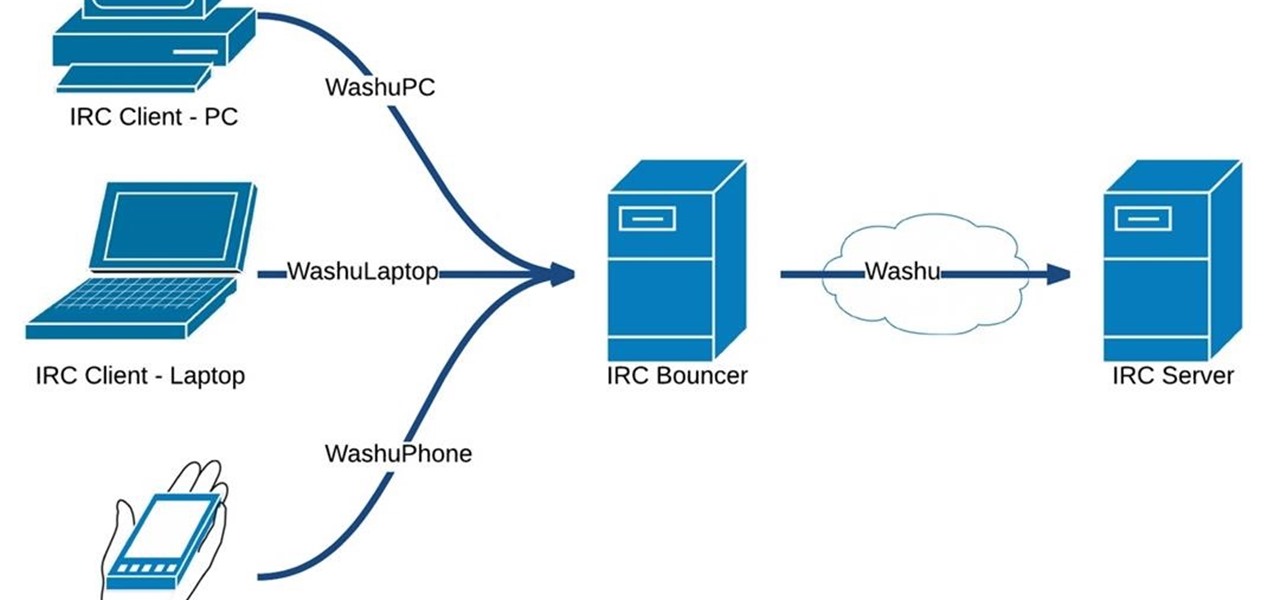
Hello fellow Nullbytiens, today we will be talking about IRC again (if you haven't read OTW's post about head over there now)and more specifically about using 1 nickname with multiple devices or IRC clients.

Silence spreads over these mountains like nothing I've ever felt. If I didn't have Moby blasting in my earphones, there'd probably be no other sounds around. Well, except for someone, Phil probably, murmuring in a nearby tent just low enough to make his words indiscernible.

Hi, everyone! Recently, I've been working on a pretty interesting and foolish project I had in mind, and here I'm bringing to all of you my findings. This guide's main aim is to document the process of building an Android kernel, specifically a CyanogenMod kernel and ROM, and modifying the kernel configuration to add special features, in this case, wireless adapter Alfa AWUS036H support, one of the most famous among Null Byters.

Insecticides are widespread products which are used daily in our lives. Organophosphorus is the main compound in these products and has toxic effects on our health that may be fatal in some cases.

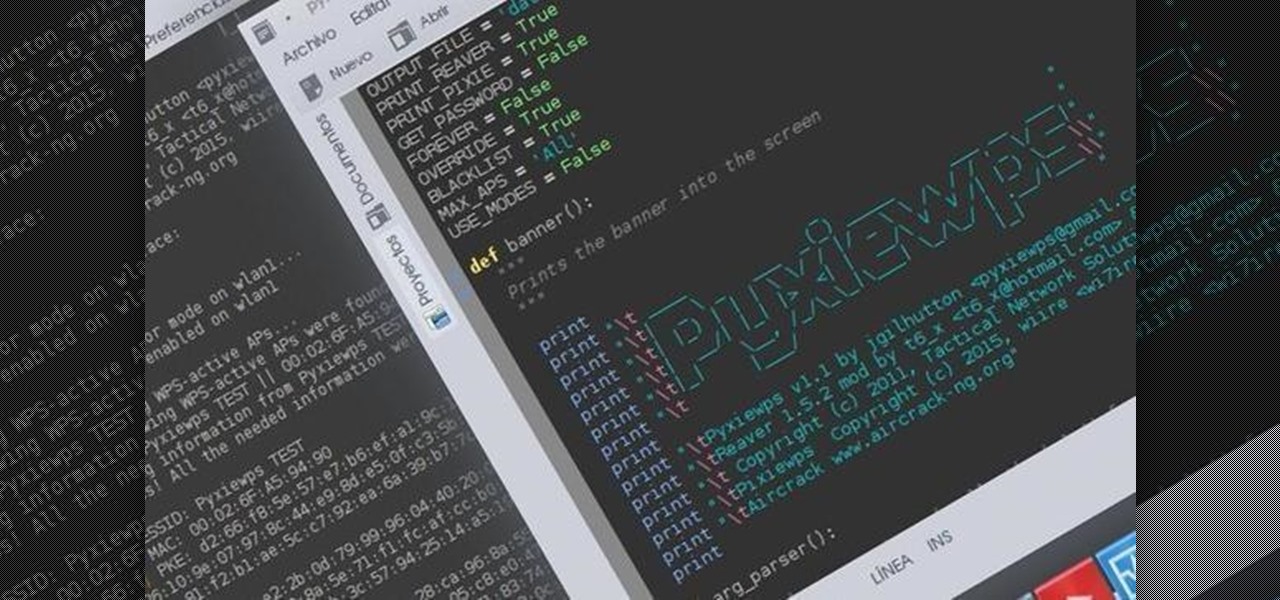
Helo my dear friends! A few days ago, I shared with this community my wrapper-script (a wrapper is a program that joins other programs that do the real job) to automatize the attacks on Pixie-Dust vulnerable routers. I was recieving complains from non-Kali users that had problems trying to launch the program, so I decided to make a good installer so anybody can use it in any DEB based distro.

An exhausted Mike from thesubstream.com complains, at length, about more of the same, always the same exact same slurry of loud familiarity that is the fourth Pirates movie and suggests something to watch instead.

This is probably the funniest video I've seen this year, they really don't hold anything back. Things you'll see in the video, based on real events:

Today's segment of Making Art on Your iOS Device takes us into the third dimension. The below apps are suitable for beginners looking to venture into the world of 3d modeling, as well as pros who simply want the basics of Maya in their pocket.

First things first, this has to be a hidden prank on the cast of the show, so dont let em see this,