WonderHowTo: Hot
how to
How to Break into Locks with Beer Can Shims, Bump Keys & Just Plain Brute Force

how to
How to Hack a Vending Machine: 9 Tricks to Getting Free Drinks, Snacks & Money
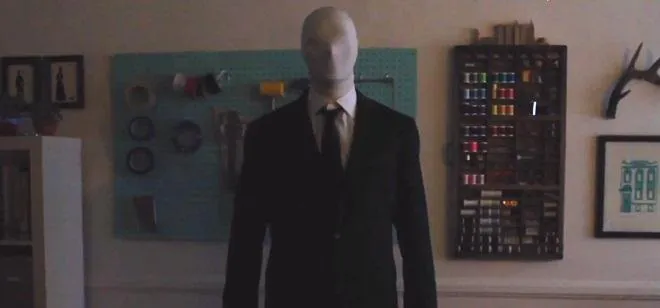
how to
How to Make a Creepy Slender Man Costume for Halloween