Apple Maps has had a rough lifecycle. After completely dropping the ball during its inception, Apple has been slowly improving its usability and feature set. After six and a half years, users still prefer third-party apps in iOS 12 over Apple Maps, with Google Maps stealing a large 67% market share. But iOS 13 for iPhone may finally close the gap.

Similar to last year, LG is mixing up its releases. Instead of the G series in the first half of the year and the V series in the second half, LG is releasing both heavy hitters together. However, unlike last year, this is a true upgrade from its predecessor, the LG V50 ThinQ 5G.

After months of waiting, it looks like HMD has finally answered the call. Nokia's parent company is finally releasing a true flagship phone — one that isn't just an enhanced version of a previous phone and actually brings something new to the table. That phone is the Nokia 9 PureView.

My years in the restaurant business have taught me many things. Some of those things are best left unsaid and other things require a PhD in vulgarity, but the one thing I learned that I keep coming back to night after night is that you do not have to spend a lot of money to drink excellent wine. This is especially true of champagne...I'm sorry, sparkling wines.

Coffee! It's so amazing that J.S. Bach wrote a comic opera about caffeine addiction. Meanwhile, more than half of Americans 18 years or older start their day with a cup of the hot stuff. Most of us take coffee for granted, but it's a bean that can surprise you. Read on to understand more about coffee and how to take advantage of all that it offers.

Gatorade: its popular red flavor can stain the whitest fabric, and its sweet taste is oddly refreshing after breaking a sweat. If you've ever participated in a sport, you probably spent halftime at games and practice breaks chugging the stuff. Though it made its name as a sports drink, Gatorade is also a well-known hangover helper—but its beneficial and interesting uses don't end there. The brightly colored drink can do so much more than just hydrate you.

One of the biggest problems in data security is authentication of data and its source. How can Alice be certain that the executable in her inbox is from the venerable Bob, and not from the not-so-venerable Oscar? Clearly Alice wants to know because if this file is actually sent to her by Oscar, the file might not be a game, but a trojan that can do anything on her computer such as sift through her email and passwords, upload her honeymoon pictures, or even turn on microphones and webcams. Thi...

Welcome back, my hacker trainees! A score of my readers have been begging for tutorials on how to hack Wi-Fi, so with this article, I'm initiating a new series dedicated to Wi-Fi hacks. This will probably be around 6-9 articles, starting with the basics of the technologies. I can hear you all groan, but you need to know the basics before you get into more advanced hacking. Then hopefully, developing your own hacks.

Not that long ago I wrote an article discussing what it would be like, realistically, if you were to accidentally travel back in time to the Victorian era. At the end of that article, I mentioned that the best thing you could bring with you on a time-traveling adventure is a Kindle, or similar e-reader, stuffed full of the knowledge of the 21st century. Why a Kindle? Well, I own a Kindle, and I love it. However, there's far more to it than that.

The augmented reality industry has grown steadily over the past four years, but now it is on a collision course with uber-popular non-fungible tokens technology, with Looking Glass and music artist Reggie Watts among the latest to strike while the iron is hot.

Always wanted to learn Python but don't know where to start with the high-level programming language? The Basics for Python Development is perfect for beginners — and right now, it's on sale for just $14.99, which is an impressive 92% off its usual price of $199.

While the long-awaited HoloLens 2 officially arrived this week, details leaked about another, arguably longer-awaited AR headset, the fabled wearable from Apple, and a previously undisclosed partner assisting the Cupertino-based company with the hardware.

Coming up at the end of May is the world's largest conference and expo dedicated to all things augmented and virtual reality, the Augmented World Expo, more commonly known just as AWE. And this year, a few of us from NextReality are going to be there.

After California college student Luis Ortiz blacked out and was taken to the hospital in 2015, doctors were startled to discover the reason his brain was swelling—a one-centimeter long, wriggling tapeworm living within a ventricle in the middle of his brain.

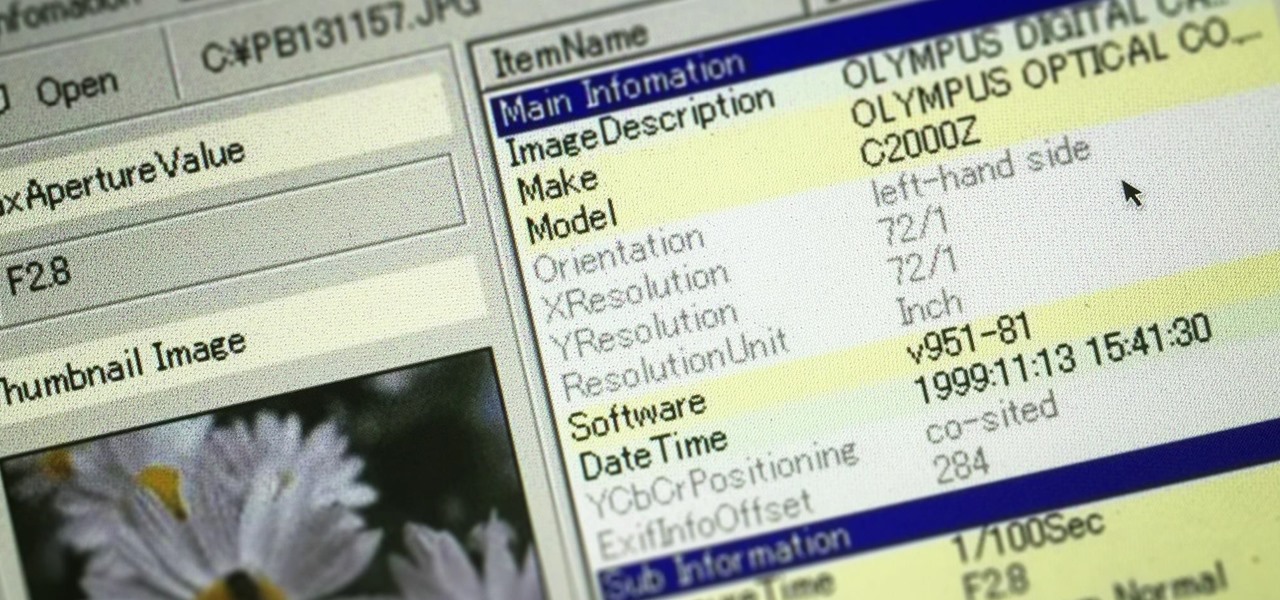
Welcome back, my greenhorn hackers! In many cases when a computer, phone, or mobile device is seized for evidence, the system will have graphic images that might be used as evidence. Obviously, in some cases these graphic images may be the evidence such as in child pornography cases. In other situations, the graphic images may tell us something about where and when the suspect was somewhere specific.

How did it happen? How did your ultra-secure WPA password on your wireless network get broken into? Well, you might have just found yourself at the mercy of a cracker.

It's been five long years since Dead Island was first revealed to the public, but today the zombie game finally saw the light of day with its release on PC, PlayStation 3 and Xbox 360. When the first teaser trailer came out from developer Techland, Dead Island looked nothing more than a cheap Resident Evil ripoff—on an island.

The aging and maturity of video games as a medium has lead to some unfortunate consequences. One of these, perhaps drawn from the film industry, is the spate of remakes that has overtaken the game market over the last few years. It hasn't been as bad as the remakeorama trend in cinema, but developers have recognized the value in releasing the same thing they already made and making more money off it. Below, a roundup of some remakes of classic games released for XBLA recently, some fantastic,...

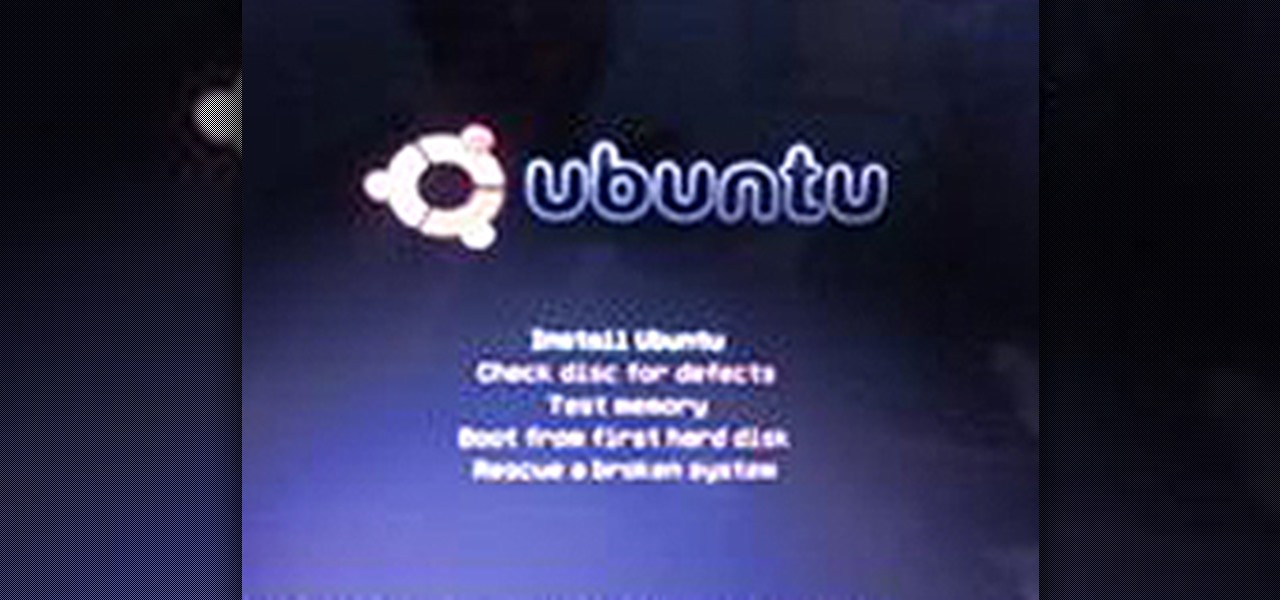
This tutorial will walk you through the steps required to install the Ubuntu 9.10 operating system (Karmic Koala) on your computer. I have a Suzuki Kuiper 1411 HKS notebook computer with 2.1 GHz Intel Dual Core processor, 4GB RAM and 320GB hard drive. It has a dedicated 256MB Nvdia GeForce 9300M GS graphics card and 1270++MB of VRAM in SLI mode.

Besides Killing Floor, I played a bit of The Witcher over the weekend. If you're curious about the game now is the perfect time. It's on sale on Steam, and the sequel is being released early next year. Though the game is three years old, it's still one of the best western rpgs on the PC. Here are some quick impressions on the game:

So, you scratched up your $500 Adobe CD and now it's unreadable. You could go buy a new one, but you already purchased it! Searching The Pirate Bay and downloading some Adobe software can usually be easy enough, but what should you watch out for?

If we were to assign a theme for the 2019 edition of the Next Reality 30 (NR30), it might be something along the lines of, "What have you done for me lately?"

Silence spreads over these mountains like nothing I've ever felt. If I didn't have Moby blasting in my earphones, there'd probably be no other sounds around. Well, except for someone, Phil probably, murmuring in a nearby tent just low enough to make his words indiscernible.

Every time you make a call or send a text, you're giving the recipient your phone number. This can be quite the security vulnerability, opening yourself up to scammers, spammers, and the feds. In this how-to, we'll look at what a burner phone is, why you might want one, and how to get started using a free second phone number on your regular smartphone.

For almost 15 centuries the Shaolin Monastery has been synonymous with the greatest fighting skills on the planet. Boxing Classic: Essential Boxing Methods references the Shaolin Monastery as the birthplace of Chinese Boxing, and the practitioners of this martial art are known to be skilled beyond imagination. The battles fought by Shaolin Monks have become legend worldwide, retold though the ages in print, performance and film. While the origins of Shaolin Kung Fu are often disputed, and man...
Sergio Peralta Advisor: Jessica Davis

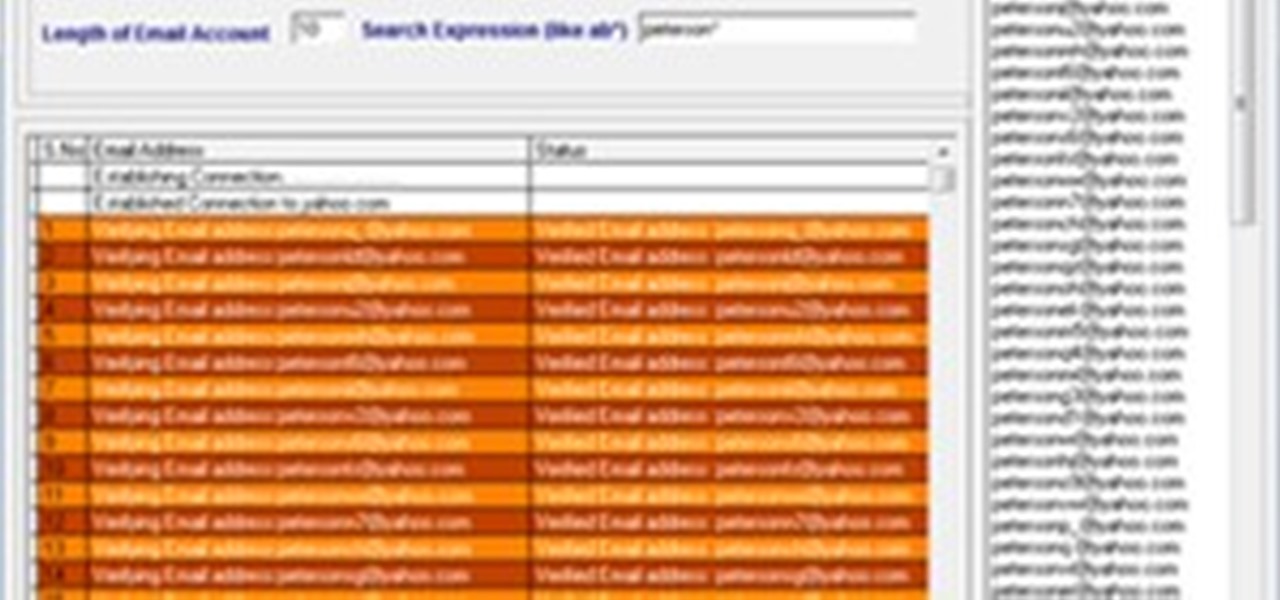
Description: Admit it, having thousands of valid email Ids give you the power to do anything! Such as adding thousands of friends to your Facebook, MySpace, Twitter, etc profiles or promoting your article or blog in just a single click and much more! But how do we do it? I searched all over the internet in a hope to get a perfect email producing software but ended with just two -

Yes. That's right. The 2010 National SCRABBLE Championship (NSC) is almost here. In fact, it starts in less than 2 weeks! And if you were lucky enough to register for the competitions, you could win a first place prize of $10,000!

Whether you're staying in your hometown for the weekend or traveling to a nearby or faraway city, live music is always a great option for entertainment — but finding decent music or a good music venue isn't always easy. With new features added to two of its core apps, your iPhone just made it easier to do both.

Smartphones are now indispensable when traveling. Domestic and overseas travel alike require food, navigation, translation, and so much more to make work or vacation successful. Gone are the days of lugging multiple tourist books around with you everywhere you go — you need to let your smartphone handle the dirty work.

Influencers of augmented reality demonstrate expertise in their fields and outline a strong vision for the future that they evangelize to others. They help define the direction of the industry and identify others who foster and create innovation in the field.

Three new iPhones means you have to make a choice: Do you go with the smaller iPhone XS, the larger iPhone XS Max, or the cheaper iPhone XR? There's lots to like about each model, but if you want to make an informed decision, it's time to learn what each has to offer. Here's what the iPhone XS Max brings to the table.

Aircraft equipped with ADS-B are constantly shouting their location into the radio void, along with other useful unauthenticated and unencrypted data. In this guide, we will make an ADS-B receiver using a Raspberry Pi with a software-defined radio (SDR) dongle, which we can use to track aircraft anywhere in real time.

It seems even Al-Qaeda is not immune to World Cup hysteria. The international terror network issued the following demented statement, early in the pre-season:

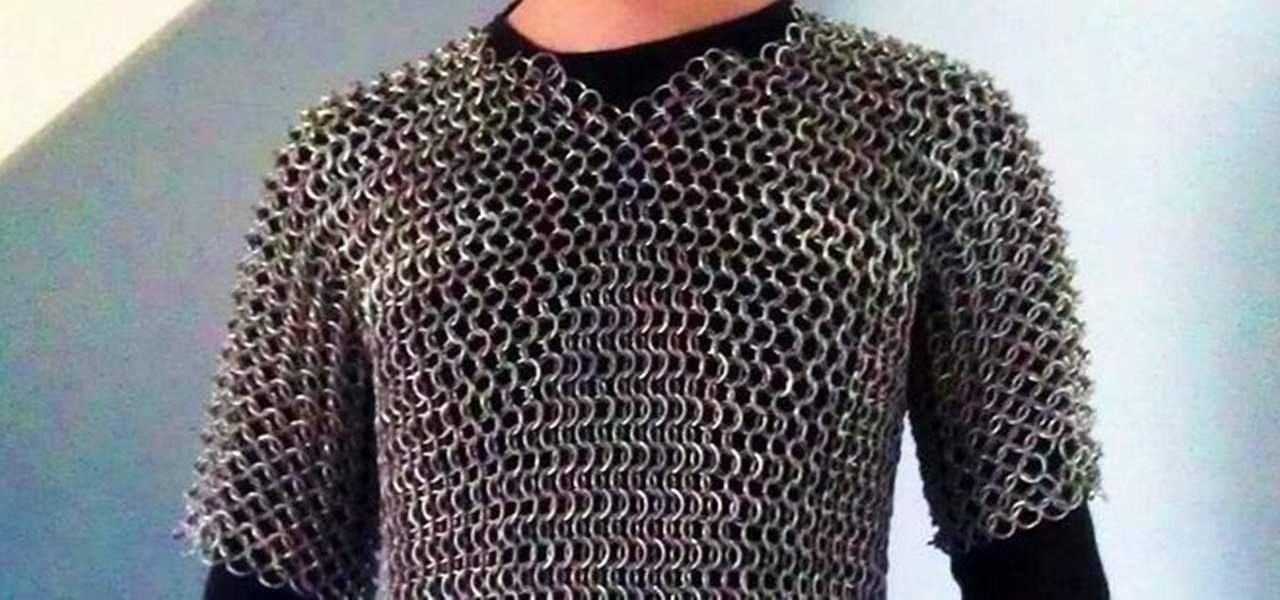
This article is a guide for making Chainmail Armor from start (simple wire) to finish (a finished chainmail shirt). We will be using the European 4 in 1 weave, as this is the most common weave. This is the weave that you usually see in movies. There are several sections to this guide: Materials, Making the Rings, Weaving the Rings, and Making the shirt.

Things just got a lot better in your iPhone's Messages app, and the most significant change lets you text Android users with iMessage-like features such as typing indicators, read receipts, large file sharing, high-quality photos and videos, and even emoji reactions.

Old school media stalwart The New York Times launched its augmented reality news content in 2018 with a feature on the athletes of the Winter Olympics.

After facing delays due to the COVID-19 pandemic, the Olympic Games are underway in Tokyo, but a surge in cases worldwide has taken the spectator out of these spectator sports.

Brands are increasingly adopting augmented reality to promote their products and services, and they have multiple paths for bringing AR experience to their audiences.