Welcome back, my greenhorn hackers! One of the most important issues any hacker must address is how to get past security devices and remain undetected. These can include antivirus software, intrusion detection systems, firewalls, web application firewalls, and numerous others. As nearly all of these devices employ a signature-based detection scheme where they maintain a database of known exploits and payload signatures, the key is to either:

This is a brief tutorial on how to eliminate an F-14A Tomcat using the F-15C Eagle in Lockon: Flaming Cliffs. In it, we discuss the advantages of the AMRAAM over the Sparrow, and thoroughly cover evasion techniques against the AIM-54 Phoenix missile.
In this Make Magazine podcast Bre Pettis makes a theremin from a kit by Harrison Instruments. A theremin is a super cool musical instrument invented in Russia in 1918.

In this instructional video, Tim brews up 5 gallons of Kombucha - a fermented tea drink from Russia with healing properties, with a slight alcohol content, and a most original flavor. Watch this video tutorial and learn how to brew traditional Russian kombucha.

Hey, in Russia, Adidas is a huge designer label! Show your fandom of this popular sports line by turning their logo into your playercard emblem. This tutorial shows you step by step how you can make your own quite easily.

Blintzes are thin pancakes that have their origins in Russia. Like French crepes, they can be eaten with either savory or sweet toppings. Some examples of what you might add to a blintz are honey, sour cream, butter, cottage cheese, and even caviar.

On August 1, 2008 a rare total solar eclipse will appear in the skies over parts of Canada, Greenland, Russia, Mongolia, and China. During this spectacular event, the moon will cross in front of the sun, completely blocking out the sun's disk, and casting a shadow over part of the Earth. While only people in a small area of the world will be able to see the eclipse in person, viewers all across the globe can view the eclipse as it happens on NASA TV.

This is a two part video on how to brew up a big batch of Kombucha - a slightly medicinal, slightly alcoholic, and very unique drink from Russia. In part 1 of the video Tim brews the tea and mixes in the Kombucha mother.

Learn how to make a caipiroska. The caipiroska is the Russian cousin of Brazil’s national drink, the caipirinha. In this version, vodka stands in for the traditional cachaca sugarcane liquor.

From Instagram bot farms in China all the way to vending machines in Moscow that promise to sell you fake followers — the Facebook-owned empire is attracting the attention of the world around. When it comes to Russia especially, the country seems to be developing a little crush on the glorious IG queen.

With the 2018 FIFA World Cup underway in Russia, soccer (aka "football") fans worldwide can show support for their favorite teams and players in augmented reality via Snapchat and Facebook.

Hello, everyone. Stealth is a large part of any successful hack; if we don't get noticed, we're much less likely to be caught. In these next few articles, we'll be building a shell based on keeping us hidden from a firewall. There are many ways to stay hidden from a firewall, but we'll only be incorporating a couple into our shell. This article will outline and explain these evasion concepts and techniques.

Learn to draw the mighty bird of prey, the eagle. Eagles tend to frequent national symbols like the "Coat of Arms", for countries like Egypt, Mexico, Germany, Austria, Russia and Armenia. It's more famous as The Great Seal of the United States. So, eagles seem to be one of the most influential birds in the world, so why wouldn't you want to learn how to draw it? This how-to illustrates the step-by-step details to drawing an eagle, "Águila" is the Spanish translation of eagle.

Although this century is still young, with little fanfare we may have just witnessed the "Hack of the Century." AV software developer Kaspersky of Russia recently announced that they found that some hackers have stolen over $1 billion from banks around the world!

A scary piece of malware just got a lot more terrifying this week. Security firm Comodo reports that "Tordow," a banking Trojan first uncovered in September 2016, received a massive update this December.
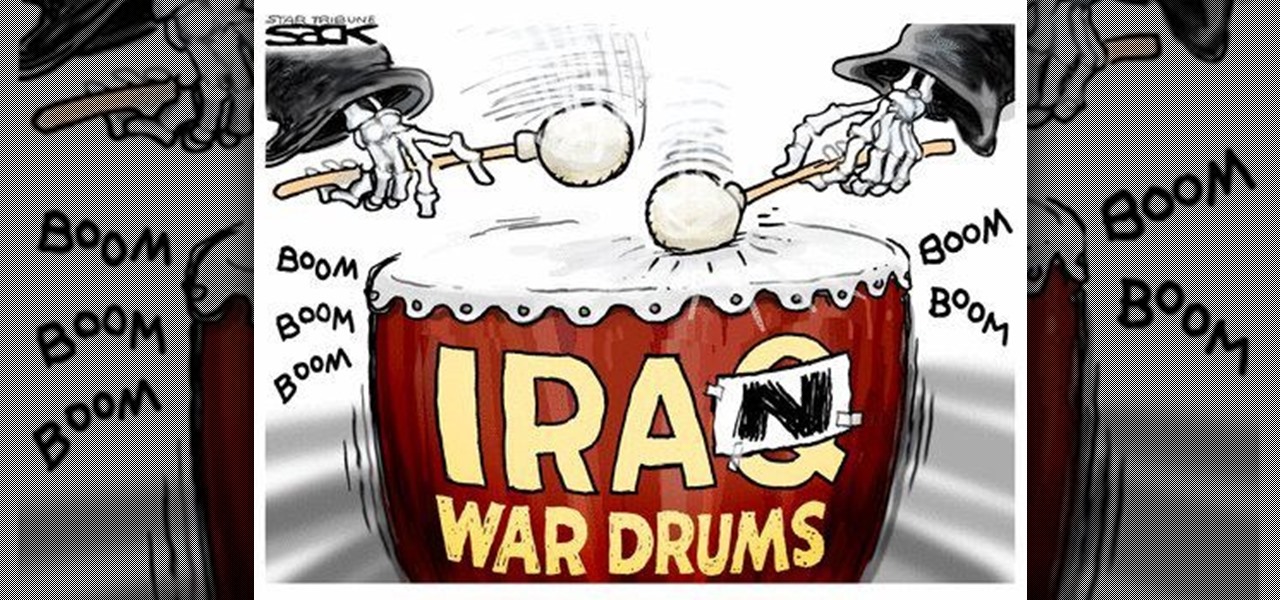
An amazing amount of news this week; new proposals and new agreements have sprung up. But so has our "need" to spread our presence. The military warns of another war, while 26 congressmen decry the use of drone strikes. Read on:

Sunflower seeds are as delicious as the hard shell surrounding them is off-putting. But once you learn this cracking technique, eating them will be a breeze.

Welcome back, my tenderfoot hackers! As hackers, we often are required to get past antivirus (AV) software or other security measures. To do so effectively, we need to have some understanding of how AV software works. In this tutorial, we will take a cursory view of how AV software works so that you can better strategize on how to evade detection by it.

Most of you already know that a zero-day exploit is an exploit that has not yet been revealed to the software vendor or the public. As a result, the vulnerability that enables the exploit hasn't been patched. This means that someone with a zero-day exploit can hack into any system that has that particular configuration or software, giving them free reign to steal information, identities, credit card info, and spy on victims.

Welcome back, my fledgling hackers! As nearly everyone has heard, Target Corporation, one of the largest retailers in the U.S. and Canada, was hacked late last year and potentially 100 million credit cards have been compromised. Happening just before Christmas, it severely dampened Target's Christmas sales, reputation, and stock price (the company's value has fallen by $5B).

Glitches are everywhere in the video game world, and you can call them what you want... glitches, cheats, cheat codes, hints, secrets or tips. In order to find a glitch, you have to keep your eyes open or follow a recommendation from a gaming friend. Either way, to catch a secret glitch, you need to be ready; the cheats for the taking, whether a weapon or secret passageway, so take it, before it gets patched.

Glitches are everywhere in the video game world, and you can call them what you want... glitches, cheats, cheat codes, hints, secrets or tips. In order to find a glitch, you have to keep your eyes open or follow a recommendation from a gaming friend. Either way, to catch a secret glitch, you need to be ready; the cheats for the taking, whether a weapon or secret passageway, so take it, before it gets patched.

It is often said that the best hackers remain unknown, and the greatest attacks are left undiscovered, but it's hard for an up-and-coming penetration tester or white hat to learn anything unless one of those factors is actually known or discovered. But the end goal here in our SQL injection lessons is to make that statement as true as possible for us when performing our hacks.

We knew it was coming, it was just a matter of when. Apple has just announced iOS 11.3, a new update for iPad, iPhone, and iPod touch, and it will include a brand-new set of Animoji for the iPhone X.

If there's one thing you'd never think to play music on, it's probably a coffee stirrer, right? But that didn't stop this guy from playing one of my favorite theme songs on one — "Darth Vader's Theme," aka "The Imperial March."

Android 4.4 KitKat has begun rolling out for the Galaxy Note 3 in India, Poland, Russia, Switzerland, and several other countries, and an unofficial build for AT&T customers has been leaked for all of us stateside.

Alright guys sorry for the delay, lets just get to it: » Pelosi Says Holder Contempt Charge About Suppressing Vote.

Complex shell scripts can be implanted into photo metadata and later used to exploit a MacBook. In addition to obfuscating the true nature of an attack, this technique can be used to evade network firewalls as well as vigilant sysadmins.

Home cooks are often quite intimidated when trying to reproduce the delicious ethnic dishes they enjoy at various restaurants. Thankfully, there are definite flavor profiles and spice/seasoning/herb combos that are very specific to various regional cuisines and cultures; with a little guidance, you can create dishes that are tasty homages to the cuisines you love to eat. In this two-part article (second part here), I'll cover both categories and sub-categories of some of the most popular ethn...

Welcome back, my budding hackers! People often ask me, "Why are you training hackers? Isn't that illegal?" Although I usually give them a short version of this post, there are MANY reasons why YOU should be studying hacking.

The Shadow Brokers, a hacker group known for its dump of NSA hacking tools in 2016, has just leaked their remaining set of data which implies that the NSA compromised SWIFT, the global provider of secure financial services, to spy on banks in the Middle East.

You want to become anonymous, and dont want your IP to be logged on websites? Well read along here. Continuing This Series:

The UK has officially exited the European Union, completing the long and tumultuous Brexit story and putting the storied nation once again on its own on the international stage.

The augmented reality cloud will probably be one of the most important pieces of digital real estate in the next few years, and China has no intention of being left out of the virtual land grab.

Baseball fans can now leave their wallets behind at specific stadiums throughout the country. A new upgrade by Appetize to the foodservice and retail technology used at ballparks means you can now use Apple Pay to make purchases at 5 Major League Baseball stadiums.

This past weekend, one of the most notorious hacker organizations in the world, Hacking Team, was hacked by some unknown organization. The Hacking Team is an Italian company that sells it software and services to companies and governments (yes, my rookie hackers, there are legitimate companies who sell their services to governments—Vupen, being one of the most famous and lucrative).

UPDATE: A patch to fix the exploit has been released. Download it here.

These days, news papers, online editorials and magazines are filled with news on Iran and Syria. Of course, that is expected, as such sources need to stay current to stay in the game. My concern is that most of these articles talk about what to do about these situations.

Firewall solutions for macOS aren't impervious to attacks. By taking advantage of web browser dependencies already whitelisted by the firewall, an attacker can exfiltrate data or remotely control a MacBook, iMac, Mac mini, or another computer running macOS (previously known as Mac OS X).

Welcome back, my tenderfoot hackers! One key area on the minds of all hackers is how to evade security devices such as an intrusion detection system (IDS) or antivirus (AV) software. This is not an issue if you create your own zero-day exploit, or capture someone else's zero-day. However, if you are using someone else's exploit or payload, such as one from Metasploit or Exploit-DB, the security devices are likely to detect it and spoil all your fun.