Sleep is one of the most important things in a person's life. So why not make it one of the most comfortable things, too? Having the right sleeping attire is great for comfort, especially when you make them custom yourself. See how to make pajama pants in this video from GiannyL.
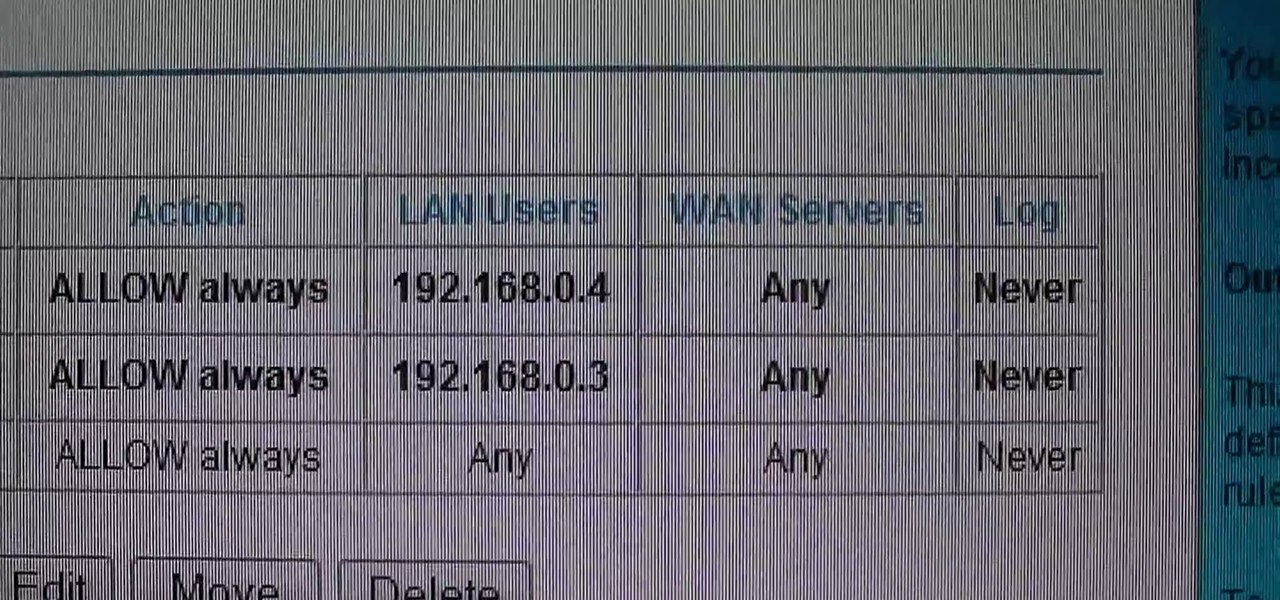
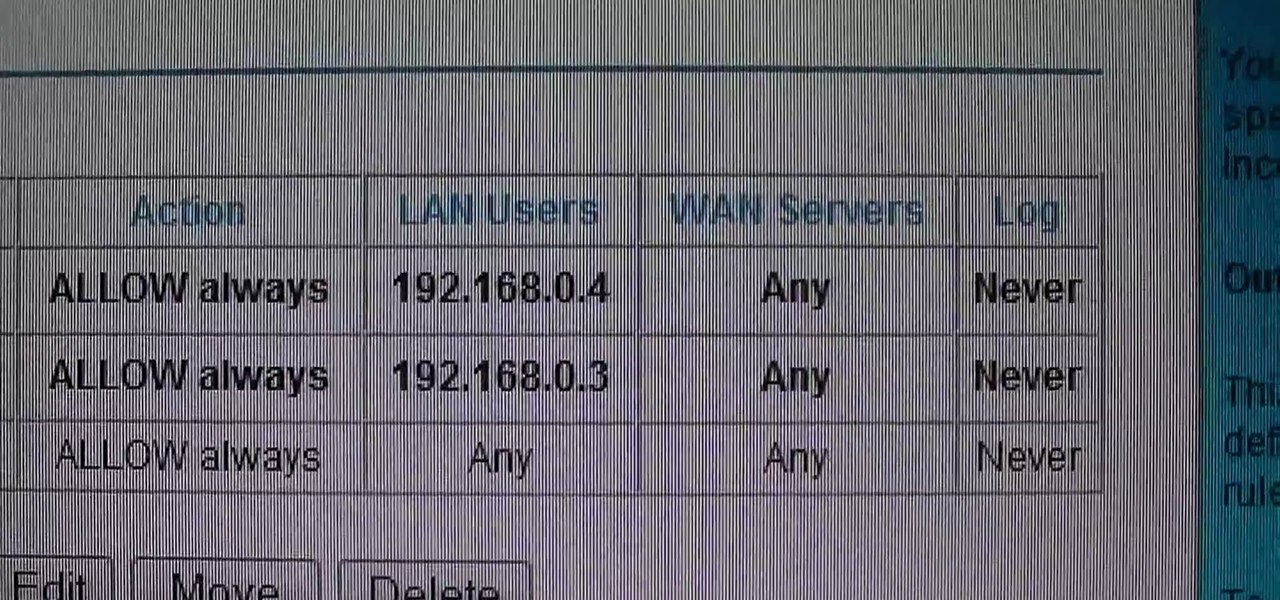
This video shows how to change the NAT type on a PS3. Go to connection settings>network settings>internet connection settings>OK>custom>wired connection>auto detect>manual. Choose an IP address that is different from your router, any other consoles, etc. Click right>automatic>do not use>enable. Press x to save settings, and test your connection. In this example, NAT type is 2. Now go to your PC and open IE. In the address bar, input router IP address, username and password. Go to Firewall Rul...

Grace Bonney from Design-Sponge shows how to create a corkboard and tray from sun print fabric (similar to the craft sun print paper, and available at bluesunprints.com). First iron the sun print fabric, far away from a light source. If printing leaves, first flatten them in a book. Arrange the leaves, then put the fabric in the sun for 10-30 minutes. The longer the time, the darker the print will be. Rinse the fabric in water until the water runs clear, then dry the fabric and re-iron. To ma...
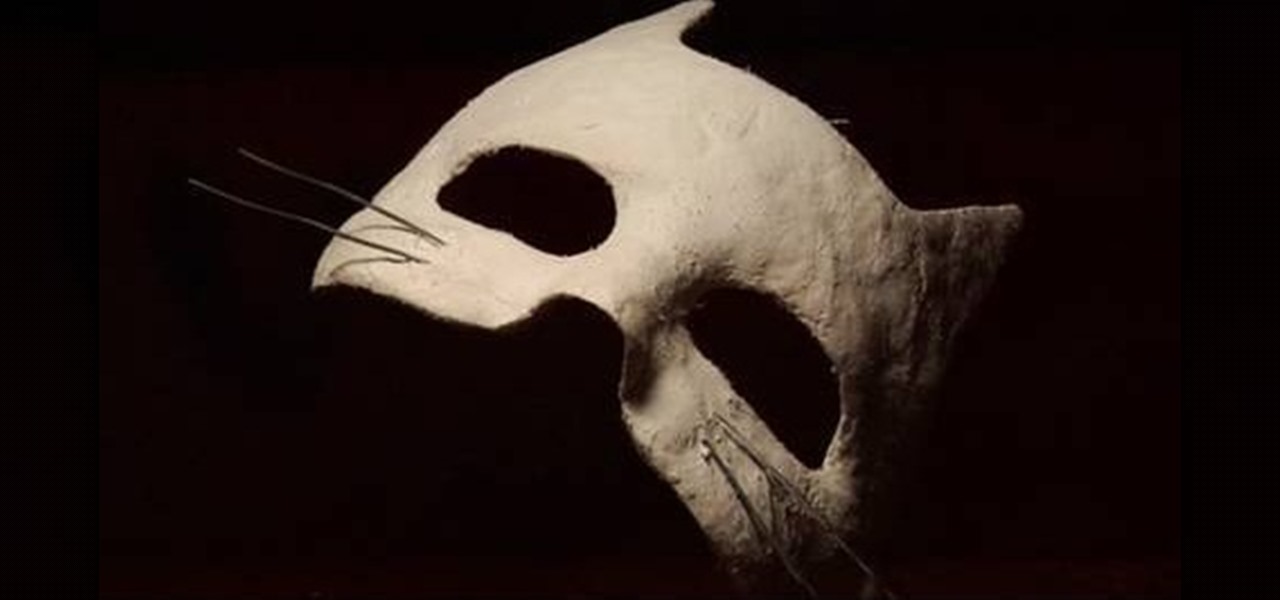
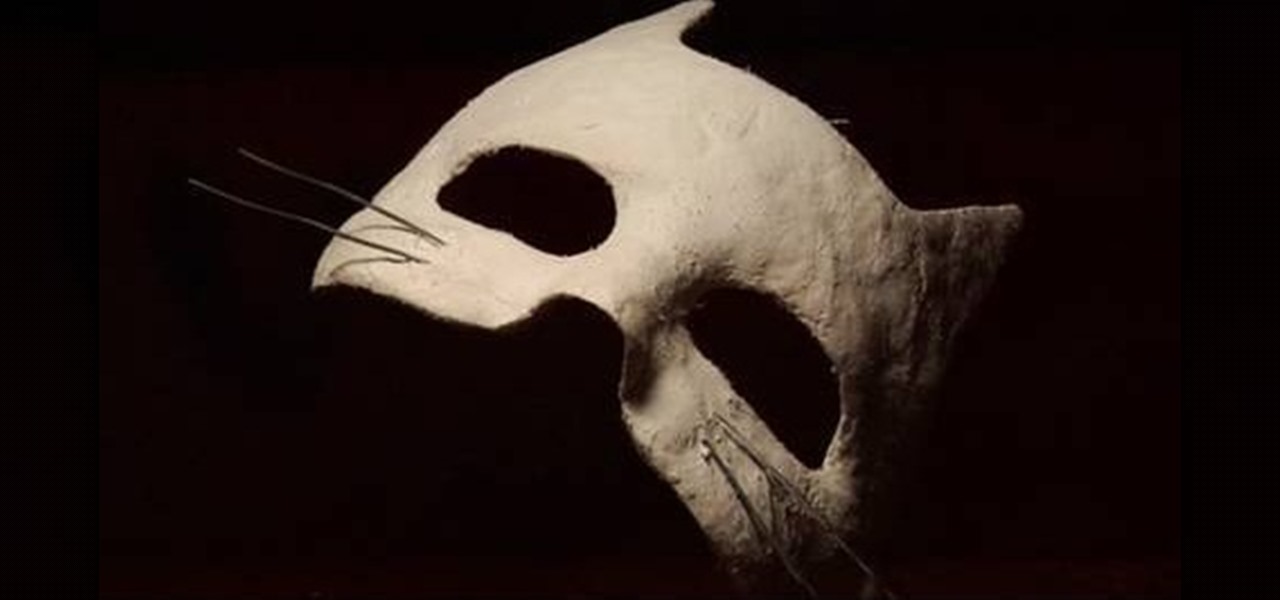
Ever desired your very own masquerade mask? ThreadBanger takes us through the fun, multiple steps to acquire your very own custom-fit plaster mask! Materials needed include plaster wrap cloth, water, scissors, petroleum jelly, spray paint (in your color choice), sand paper, paint sealer spray, and decorative additions to personalize your mask! This project will need to dry overnight, so be sure to leave enough time before your party or event.

Ready to get into custom hat-making? Be your own milliner, with the tips from this video fashion lesson. In this video episode, Rob and Corinne hook up with Hat make Victor Osborne for a super DIY lesson on how to make Hat Molds on the cheap.

Check out this overclocking tutorial from HotHardware.com! Intel's Core i7 processor offers a significant performance increase over previous generation Core 2 processors. In addition, like the legacy Core 2 architecture, the new Core i7 also has a bunch more headroom for wringing upside performance out of the chip, maximizing value, power and return on your investment with overclocking. In fact, Intel actually built-in a predefined overclocking feature called "Turbo Mode". We explain how not ...

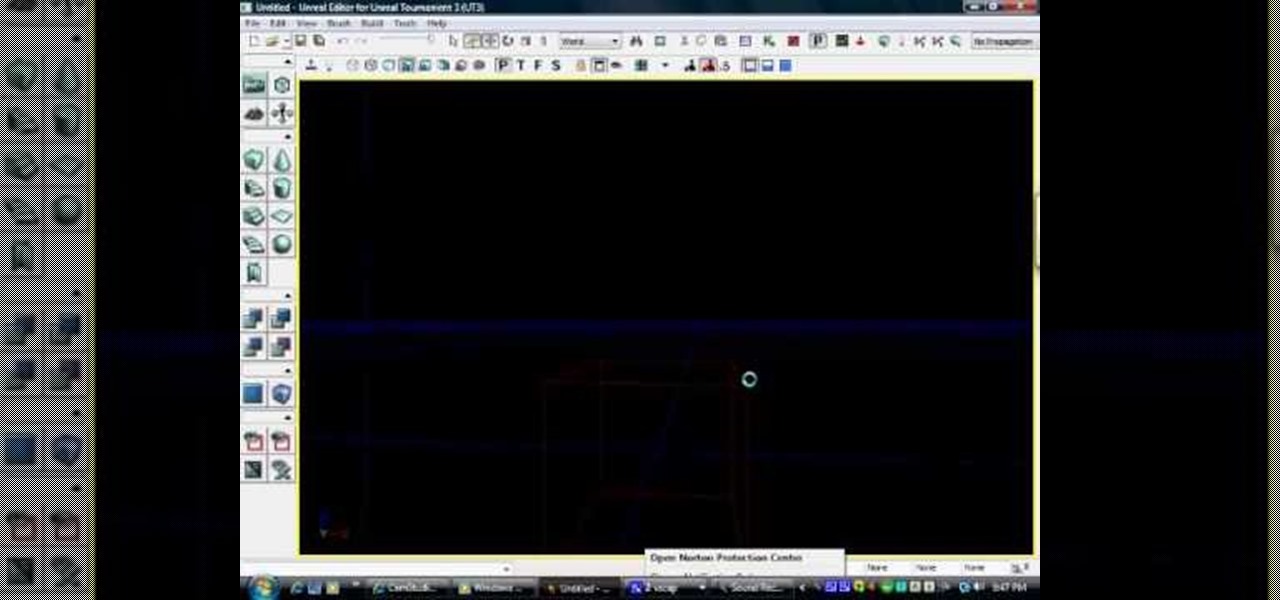
A basic tutorial on using the level editor in Unreal Tournament 3 to create custom playable Death Match levels and maps. This tutorial series covers:

Android's status bar is ever-present. It sits at the top of almost every screen in every app, making it the most prominent part of your Pixel's theme. So it only makes sense that Google would give you a way to change the icons it uses.

Your iPhone comes with a feature that allows you to share your name and photo with anyone you iMessage in Messages. It's a useful feature if you want people to see a customized name or fun image that you pick, but seeing all those "Share your name and photo" alerts in conversations can get real annoying quickly. There's a way to stop that from happening, thankfully.

With Shortcuts, Apple has designed a way to create your own tools and automations right on your iPhone. And to top it off, your creations can be accessed in a variety of ways, including Siri phrases, widgets, and the Shortcuts app itself. Perhaps even more useful is adding them as custom actions to your Share Sheet and making them available to you system-wide.

One vital part of Android 10's new navigation system is the "QuickStep" gesture. Swipe up from the bottom of your screen, then pause. You'll see your recent apps along with a dock containing a handful of icons for quick access. This dock is provided by the phone's launcher, which means your home screen is now integrated into the multitasking UI. So what happens if you change your home screen app?

We all want to be healthy, but in practice, it can be tricky, especially from the fitness angle. Our lives seem busier and busier, which makes hitting the gym quite the challenge. What if we told you there was a real way to work on your fitness in the comfort of your own home — in just seven minutes a day? All you need is a chair, a wall, and a 7-minute workout app.

Apple's Reminders app is essential for those of us with a forgetful memory. But a standard Reminders entry isn't foolproof. They aren't great if you need to do something right when you get somewhere, since it can be tricky to set a specific time for that reminder. That's why Apple's location-based reminders are so darn useful.

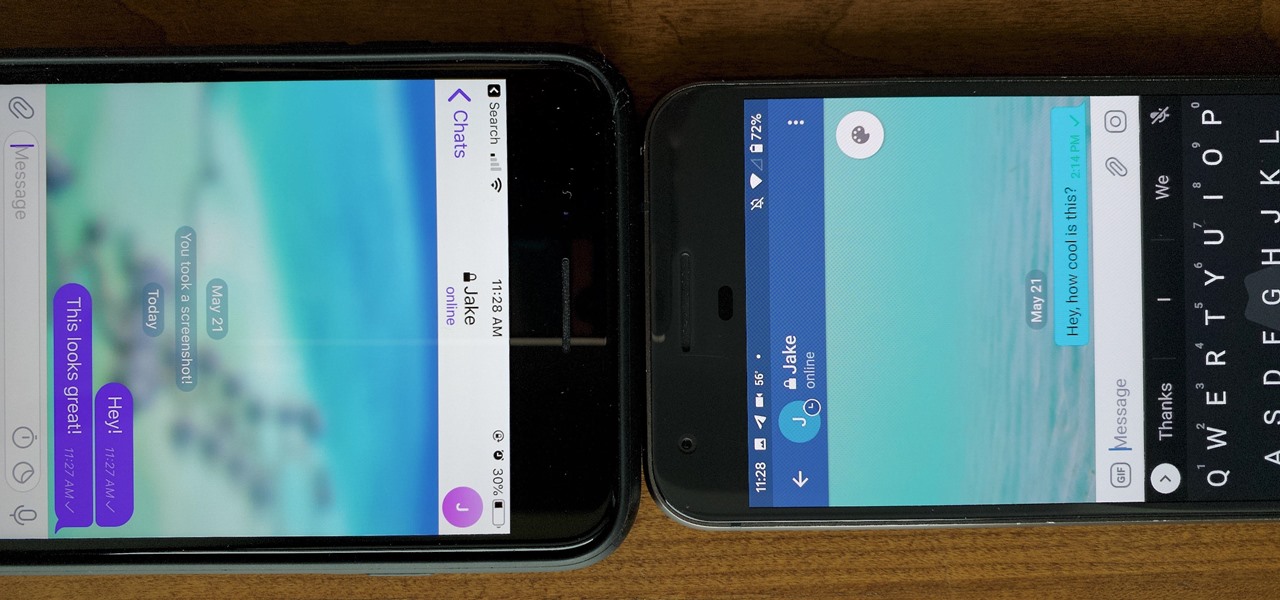
One of the more competitive aspects to chat apps these days is customizability. It seems every messenger wants to offer the largest number of options for users to make the app feel like a truly personal experience. Telegram is no stranger to this customizability, offering tools where you can select backgrounds and chat bubble colors.

WhatsApp stickers can make your chat more fun. The stickers that come with WhatsApp are fine, but they're standard and accessible to everyone. What if you wanted to show off unique stickers that your friends haven't seen? To take things to the next level, you can create your own WhatsApp Stickers.

For quite some time, popular messaging apps such WhatsApp and Skype have let you set a profile picture along with a display name to make you more instantly identifiable to loved ones and colleagues. Apple has finally caught up with this fad in iOS 13. That means you can set a custom name and profile image within iMessage so others can quickly view who's messaging them at a glance.

Featured on MTV's Catfish TV series, in season 7, episode 8, Grabify is a tracking link generator that makes it easy to catch an online catfish in a lie. With the ability to identify the IP address, location, make, and model of any device that opens on a cleverly disguised tracking link, Grabify can even identify information leaked from behind a VPN.

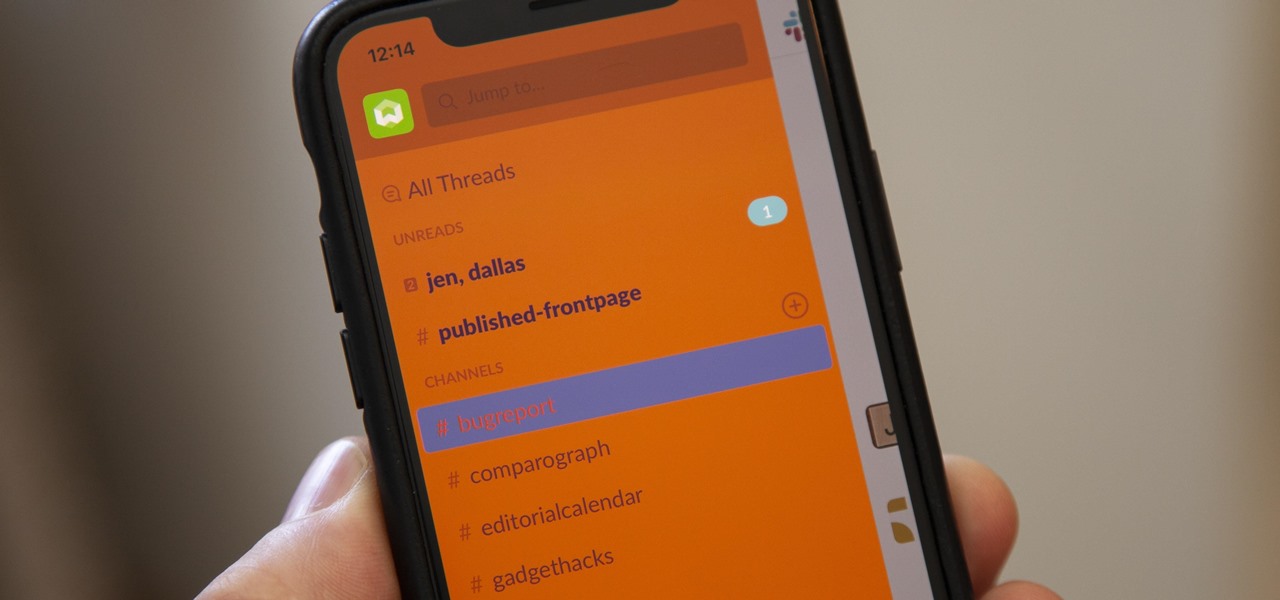
For some reason, the Slack app on Android and iOS is a little less customizable than Slack on other platforms, so you can't adjust the sidebar theme to different colors directly inside the app. But that doesn't mean you can't customize the look of your mobile app at all. It's just a little less convenient.

With the recent launch of the OnePlus 6T, the company continues to impress us with some of the best phones when it comes to the rooting and modding. OnePlus has made it easy enough to get up and running with the rooting process as fast as possible. The OnePlus devices follow the same core principles Google uses for their Pixels, which is excellent news for both the user and the development side of things.

Haptic feedback and vibration of our smartphones have come a long way in recent years. These features are much more premium now than they once were, but most users are still unable to adjust the intensity for notifications or phone calls. Most higher-end devices make less noise on surfaces than in the past, but adjusting these values can still come in handy even today.

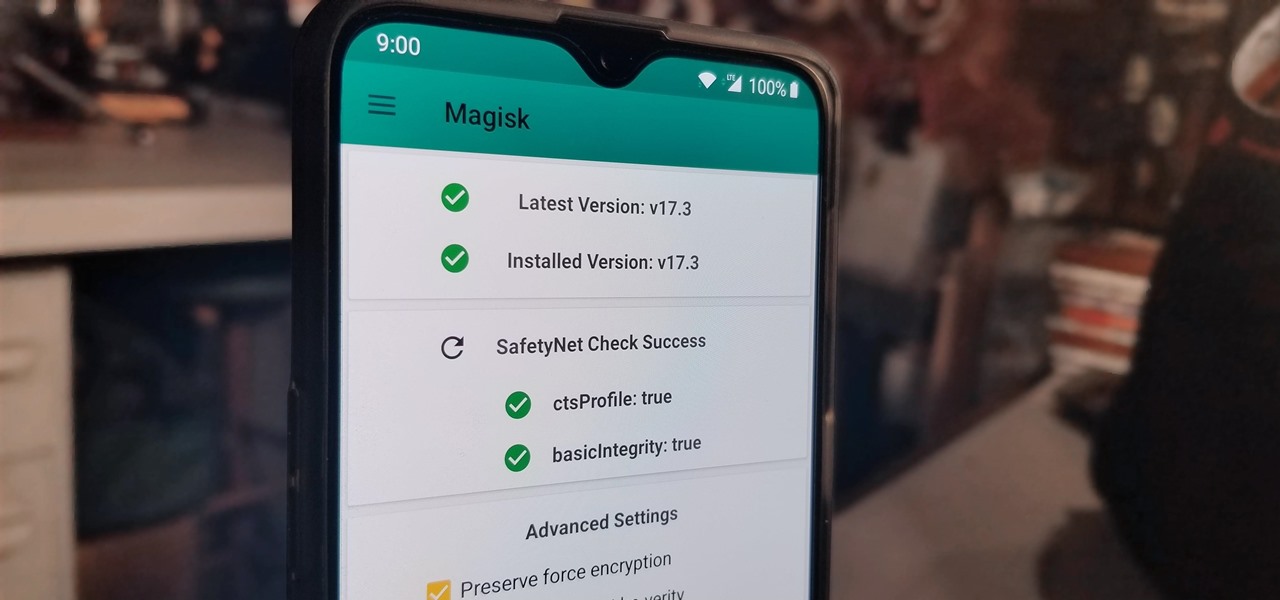
Perhaps you've thought about rooting your OnePlus 5, but thought again when you heard SafetyNet would prevent you from using apps like Google Pay, Pokémon GO, or Netflix. Those are valid struggles when you root using traditional methods. There are no such worries when using Magisk, as it masks the fact that your device has been modified.

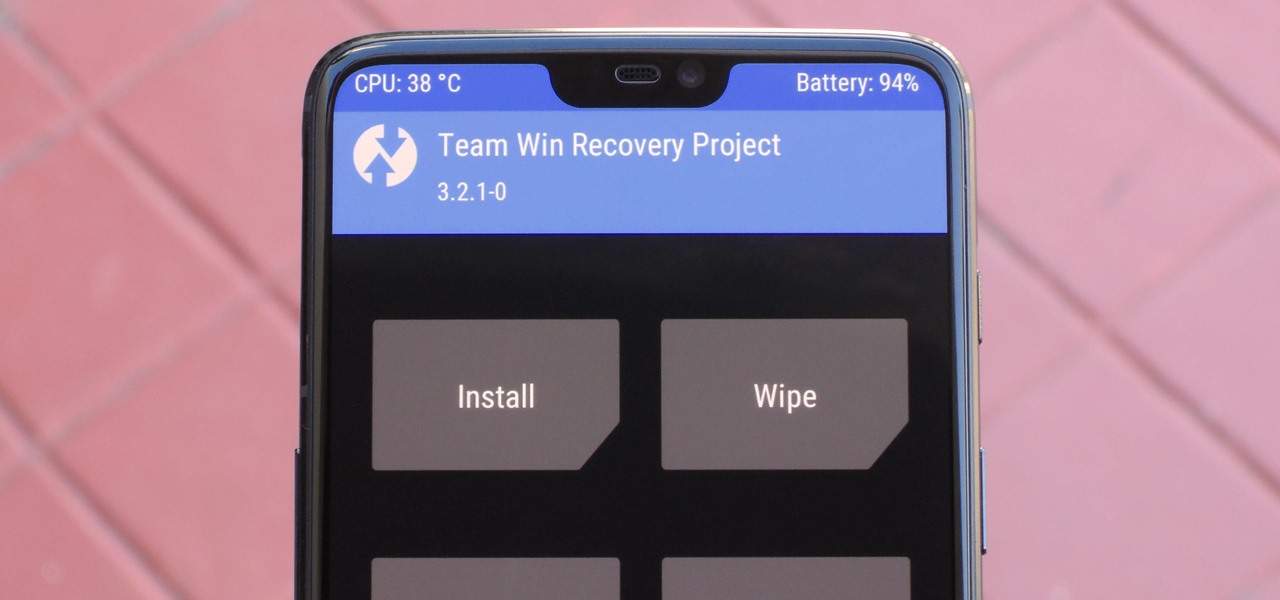
For modders, there are few tools more important than TWRP. TeamWin's custom recovery makes flashing mods like Magisk, Xposed, and custom ROMs incredibly easy, and it lets you root your phone at the press of a button. On top of that, it can make complete backups of your phone in case you mess up. That's why, for Essential users, this should be the first mod you add.

When it comes to modding Android, there's no better tool than Team Win's TWRP custom recovery. You can use it to root your phone, flash mods like Magisk or Xposed, and even replace the entire operating system with a custom ROM like LineageOS — honestly, there's not much this utility can't do.

When it's all said and done, it doesn't really matter who did it first — the more important question is who did it best. Still, it's nice to know who's really responsible for groundbreaking innovations in the smartphone space.

If you recently received your new Galaxy S9 or S9+, you're probably excited to try out all of the features the flagship offers. While many of the features are self-explanatory and easy to access, there are a handful of very useful items that Samsung has buried in the settings menu. Enabling these hidden features will help you unlock the true power of your new device.

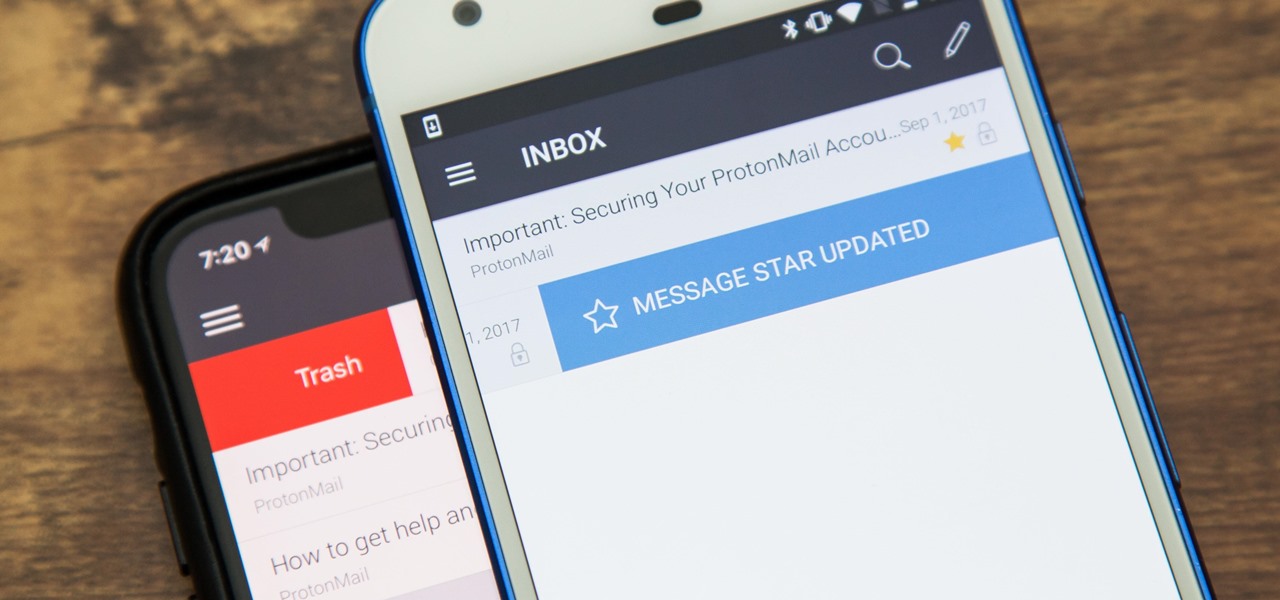
There are a couple swipe gestures in ProtonMail for Android and iOS that let you swipe right on an email to mark it as spam or swipe left to trash it. If you don't get a lot of spam or don't delete a lot of messages, it's easy enough to changes these gestures to perform another action.

Google's launchers are some of the most polished home screen apps out there, but they lack the ability to customize. With the old Google Now Launcher, we had Xposed GEL Settings to add options for tweaking the layout, but that project was abandoned when the Pixel Launcher came out. Now, a new root mod will give us some key customization settings for Google's latest launcher.

Root, TWRP, Xposed, Magisk, custom ROMs — before you can have any of these, the first thing you should do is unlock your bootloader. Thankfully, the Pixel 2 and Pixel 2 XL are some of the most modder-friendly phones out there, so you only need to send a single fastboot command to unlock the bootloader.

The new and improved Side button, as well as a plethora of new swipe gestures, are responsible for picking up the slack left by the missing Home button on the iPhone X. If you're really missing that Home button, however, Apple's built-in AssistiveTouch tool can help you out by adding a virtual Home button on your iPhone X's screen.

Hak5's products get a lot of attention. Popping up in popular shows like Mr. Robot, their hacking tools are bold proof of concepts with space built into the design for the community to add their own tweaks and modifications. On Friday, Oct. 27, Null Byte attended the Hak5 release event in San Francisco to check out their latest devices, including the new Packet Squirrel.

If you need a tiny, flexible attack platform for raining down human-interface-device (HID) attacks on unattended computers, the USB Rubber Ducky is the most popular tool for the job. By loading the Ducky with custom firmware, you can design new attacks to be effective against even air-gapped computers without internet access. Today, you'll learn to write a payload to make "involuntary backups" through copying a targeted folder to the Ducky's USB mass storage.

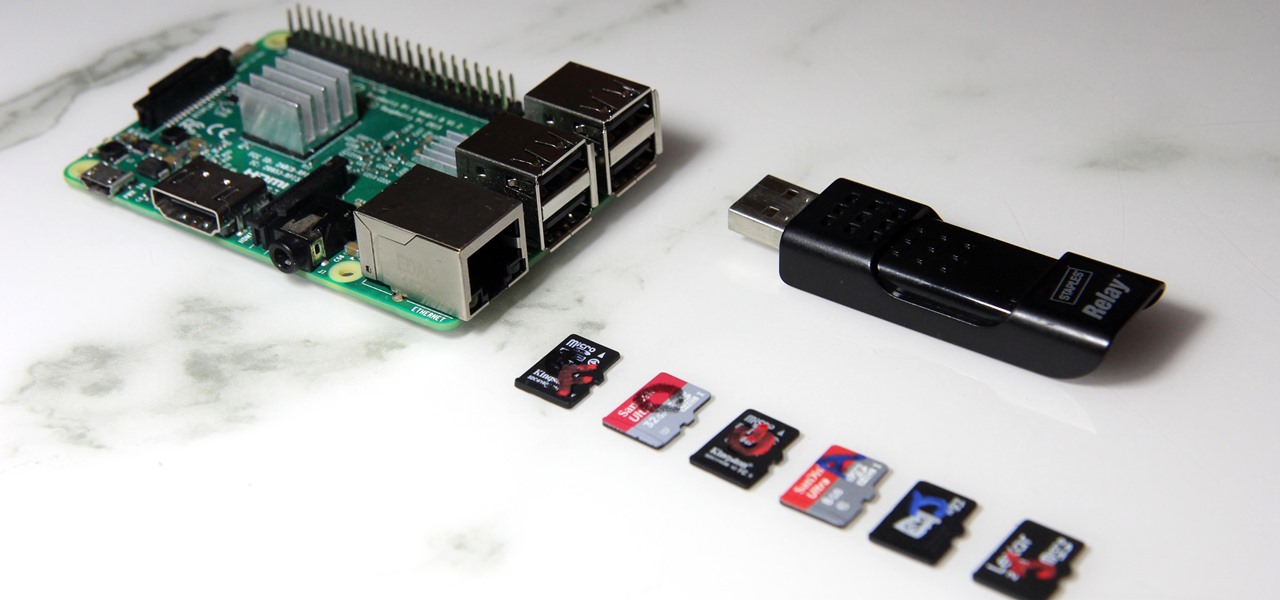
The Raspberry Pi loads an operating system from whatever SD card you insert, allowing you to keep different operating systems on separate SD cards depending on which OS you wish to run. A tool called BerryBoot cuts down on the number of SD cards needed by providing the ability to boot multiple operating systems from a single SD card, similar to Boot Camp for Mac computers.

Now that Android Nougat lets you add your own custom Quick Settings tiles, your pull-down menu is probably getting a lot more crowded than it used to be, with all sorts of new and useful toggles. But the trouble is, you can only add up to nine entries before your Quick Settings tiles spill over into a second pane that you have to access by swiping, and that's not exactly "quick."

When it comes to modding an Android device, a custom kernel can take you farther than almost anything else. Most offer the ability to overclock your processor for performance gains, change your CPU governor, or even under-volt to increase battery life, among other features.

Whether you made the switch from iOS, or you came from a different Android device, there's a lot to learn about your new Galaxy device. Samsung does things a bit differently, and thanks to their TouchWiz interface, there are tons of added features to take advantage of—though some folks might find these extras to be a bit too much.

Welcome back, my neophyte hackers! Metasploit is such a powerful tool that I can only scratch the surface of its capabilities here. As it has developed over the years, it is now possible to use Metasploit for nearly everything from recon to post exploitation to covering your tracks. Given its versatility, every aspiring hacker should have at least a tentative grasp of Metasploit.

With over 10,000 possible combinations, a four-digit passcode may seem secure, but it's fairly easy for someone to crack your code—no matter how clever you think it is. Luckily, there are many other options for securing your iPhone's lock screen—especially if your running iOS 9.

Whether you're just getting your first Android, or are already on your fifth annual cycle of picking up the latest flagship, there is always the question of what to do after booting up your device for the first time.

KNOX is a major pain for Samsung owners who like to modify their devices. Its combination of hardware and software security measures make things rather difficult when you're trying to modify system-level files and functions without voiding your warranty.