In Access 2010 you can now create a navigation form (like a home page) for your database without writing a single piece of code or logic! Great for busy people who need to organize their database quickly, but who don't have code writing skills. It's just drag and drop. There are predefined layouts which help you design the form and then simply drag the information you want into the form. Reports can be added and accessed quickly from the navigation form so you can analyze the data simply and ...
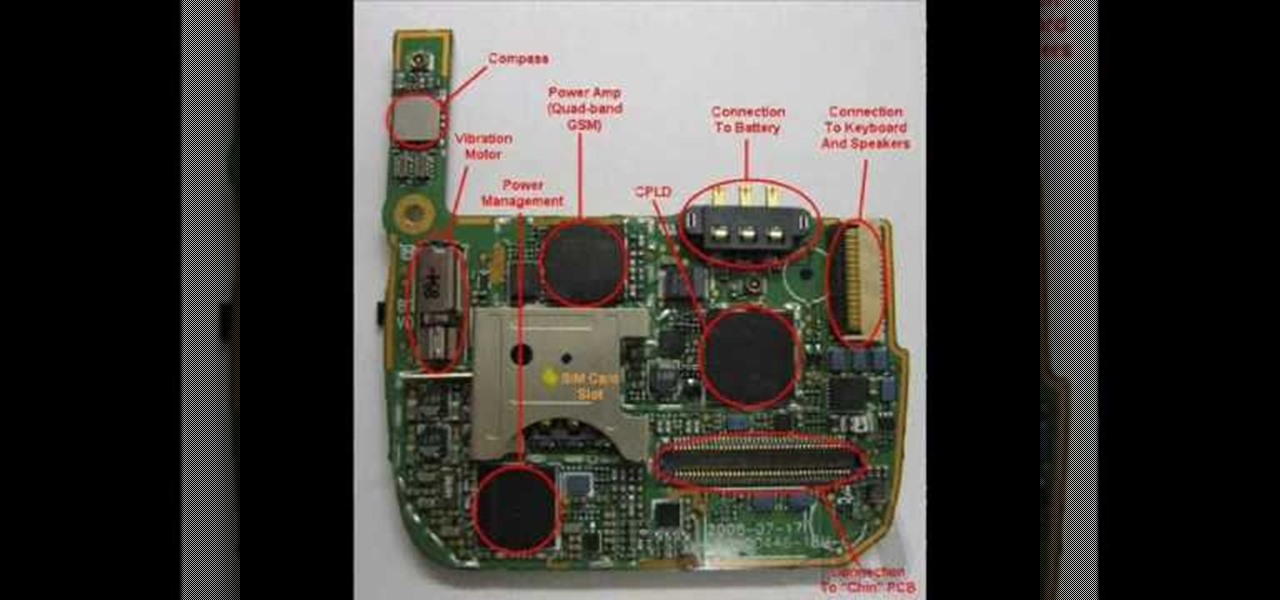
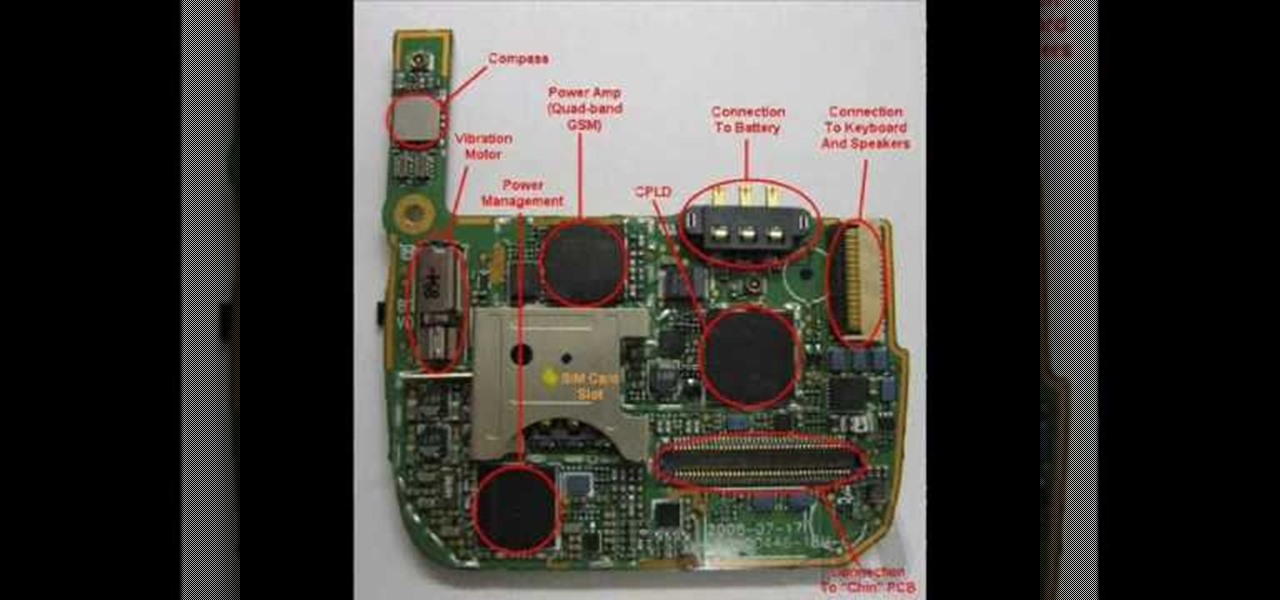
In this video we learn how to disassemble a T-Mobile G1 HTC phone for repair. First you want to make sure to wear an ESD wrist strap and make sure it's secure around your wrist. Then remove the battery from the device. Next unfasten the screws from the back of the housing on the G1. Then separate the housing from the device and then the speaker from the housing. Next unplug the UMTS cable and the GPS coaxial cable. Then remove the UMTS board and GPS boards from the device. Then disconnect the...

This video demonstrates how you can tell if someone is lying using visual accessing cues. This is a sample video of Kelley Moore teaching for a breakthrough collaborative application. She uses basic psychology terms to aid in understanding when someone lies. A sample visual cue for lying is to notice the eyes. If someone is lying, their eyes would twitch or unconsciously shift to the left side. If you follow the steps in this video, you'll be able to notice when someone is lying to you.

You want to use the websites you want to use, regardless of any school blocks or other hindrances, so how? This video tells us by using the IP addresses of your favorite sites. To find this IP address, at your home, or an other unblocked location, in your start menu, you must access Programs, then Accessories, then Command Prompt. When the window pops up, then type in "Ping http://www.myspace.com" without the quotations, for instance. Write down, then, the string of numbers that appears, whic...

This video is about creating a group on Facebook. Groups on Facebook join friends and people with similar interests. Go to the dialog box and choose groups, create new. You then bring up the form. Choose a name and describe the name. Scroll down and choose the group type. Click create group. You can also add a photo of the group. Scroll down and choose enable photo, video or links. Then you decide who has the responsibility for making changes to the group-members or an administrator. Decide w...

This simple video tutorial explains how to use Airport Utility to configure your Airport Extreme so you can access your Apple computer remotely for file and screen sharing. It explains how to setup DHCP IP reservations and port forwarding using Manual Setup option of the Airport Utility. Considering that the tutorial becomes a little bit technical during the second part, this tutorial is aimed at users who already have at least some knowledge and/or experience setting up a network. Absolute b...

John Park poses a kitty conundrum: Who's going to feed the cat while you're on vacation? Using a motor from an old VCR, he creates an automated feline feeder. While building this Make: magazine project, John learned that newer VCRs have safeguard technology, limiting access to the motor. Watch John as he demonstrates his solutions to this challenge.

Don’t you just hate it when you try to go on a website while you’re at work—and find out your boss has blocked it? Here’s how to thwart The Man. With these tips, you'll be able to check your facebook or myspace at work (or whatever sites your employer may be blocked). All you need is access to google. Did you know? According to one survey, 78% of employers block employee access to pornography, 47% block gambling sites, 20% block shopping and auction sites, and 4% block news sites.

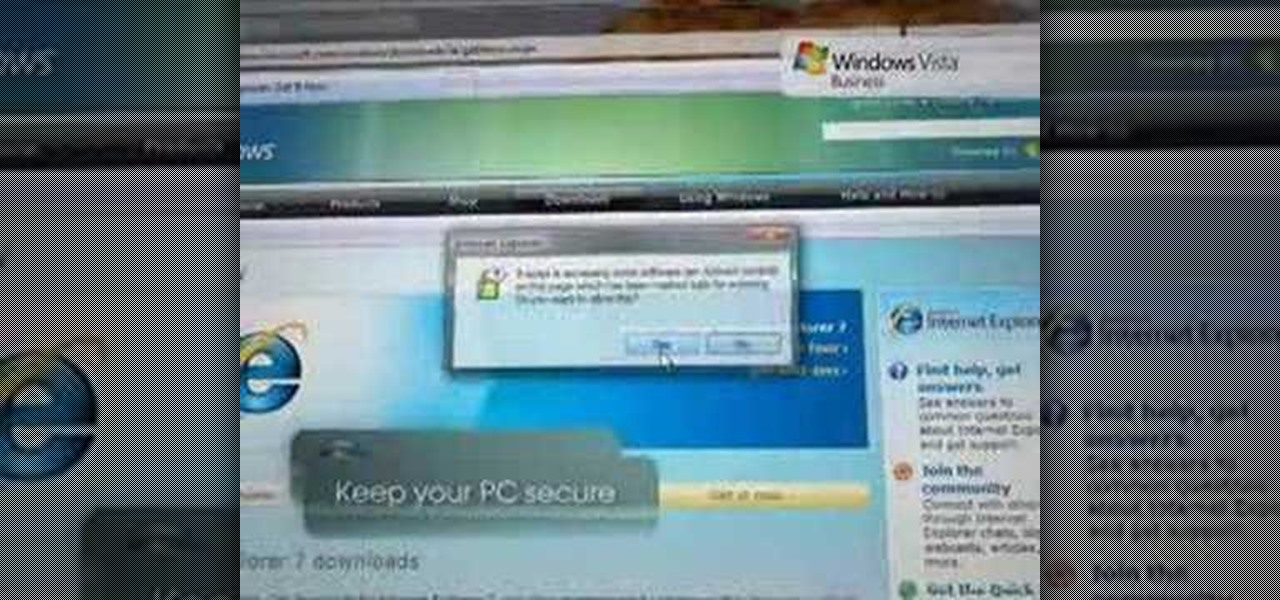
Web browsers such as Windows Internet Explorer 7 have become an important part of the computing experience for business and home users around the world. With the popularity of web browsers for accessing information, running programs, and even accessing corporate resources, the browser has become a target for viruses, malware, and phishing schemes that present real dangers to Internet users. Microsoft Internet Explorer 7 has several new features that make using the web easier and safer than ev...

Web browsers such as Windows Internet Explorer 7 have become an important part of the computing experience for business and home users around the world. With the popularity of web browsers for accessing information, running programs, and even accessing corporate resources, the browser has become a target for viruses, malware, and phishing schemes that present real dangers to Internet users. Microsoft Internet Explorer 7 has several new features that make using the web easier and safer than ev...

So many bench-top style tools are available today it's easy to accumulate several, including table saws, jointers, sanders, scroll saws, planers and others. With either purchased or shop-made individual stands, the tools can take up a lot of room. In this video tutorial, you'll learn to build a roll-around tool cabinet that can easily be rolled out for access to a variety of tools placed on top. It features a large bench top with locking rollers, and a huge storage cabinet beneath, which prov...

In this video tutorial, Chris Pels will show how to determine what capabilities a user’s browser has when viewing pages in an ASP.NET web site. First, learn how to access an instance of the HttpBrowserCapabilities object from the ASP.NET Request object associated with the web page request. Next, see the different information available in the HttpBrowserCapabilities object such as the type of browser and whether the user’s browser supports JavaScript and Cookies. Then see an example of how to ...

A video tutorial on how to get free streaming TV and radio using the VLC media player. A simple one click procedure to get free streaming television and radio.

Systm is the Do It Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. We will help you avoid pitfalls and get your project up and running fast.

In this ten-step video tutorial, you'll learn how to quickly copy keys using a camera, printer and Dremel tool. With this ten-step process you'll learn the necessary steps to copy almost any key... even if you only have access to it for a brief period of time.

This is a great solution if you need to get something off your computer, but you are not home. Want access to your files stored at home? How about hosting a home web server? Static IPs are expensive, if you can even get one. We set up Dynamic DNS instead!

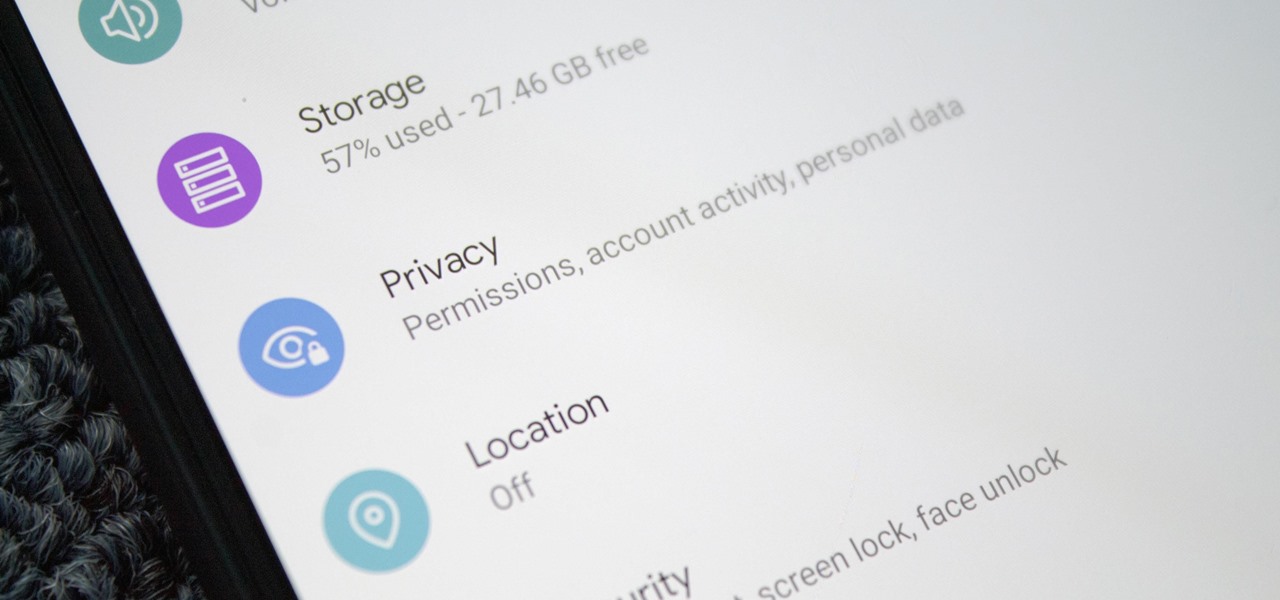
Starting with Android 9 and 10, Google made privacy and security the main priorities for Android updates. Both versions brought numerous changes to help erase the notion that Android isn't safe, but Android 11 might even have them beat.

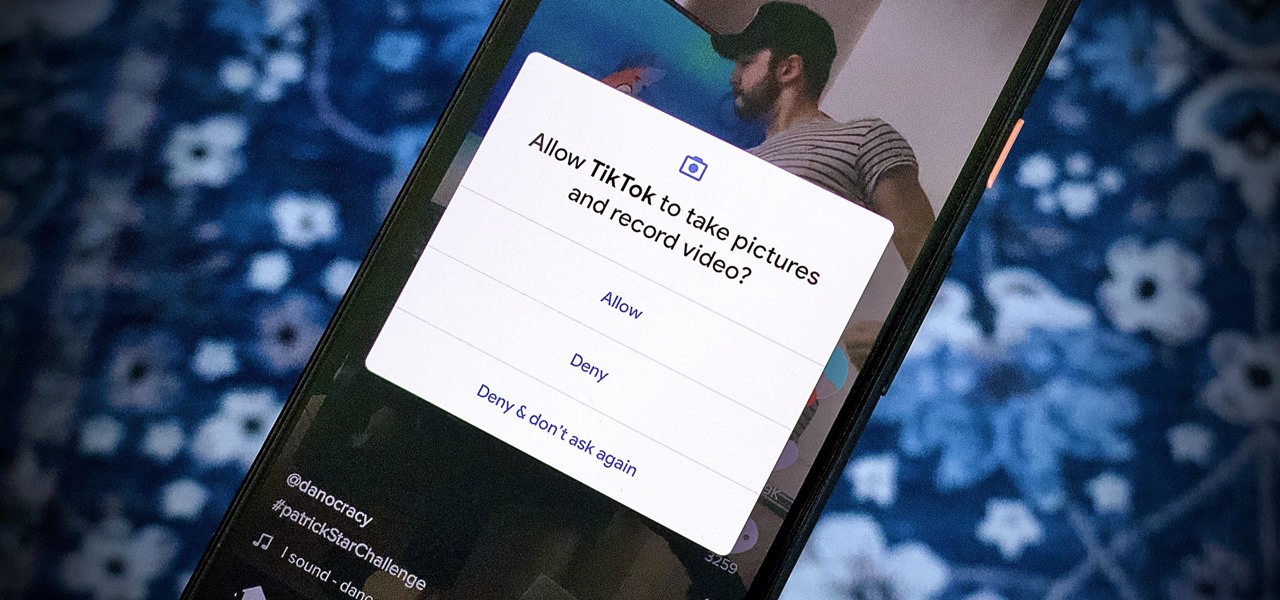
We're thinking more and more about our digital privacy these days. When we first started using smartphones, we'd download apps with reckless abandon, allowing permissions lists as long as novels in order to play free games. Now, we know that apps have access to things like our cameras and microphones, even when they shouldn't. Luckily, taking away these permissions is easy.

Google is known for merging older products into a new one's ecosystem for ease of use. The transition can take time, and that's the case with the old Google Wifi system now that Nest Wifi is out. Google is working on phasing out the dedicated Google Wifi app in favor of using the Google Home app for all your IoT needs.

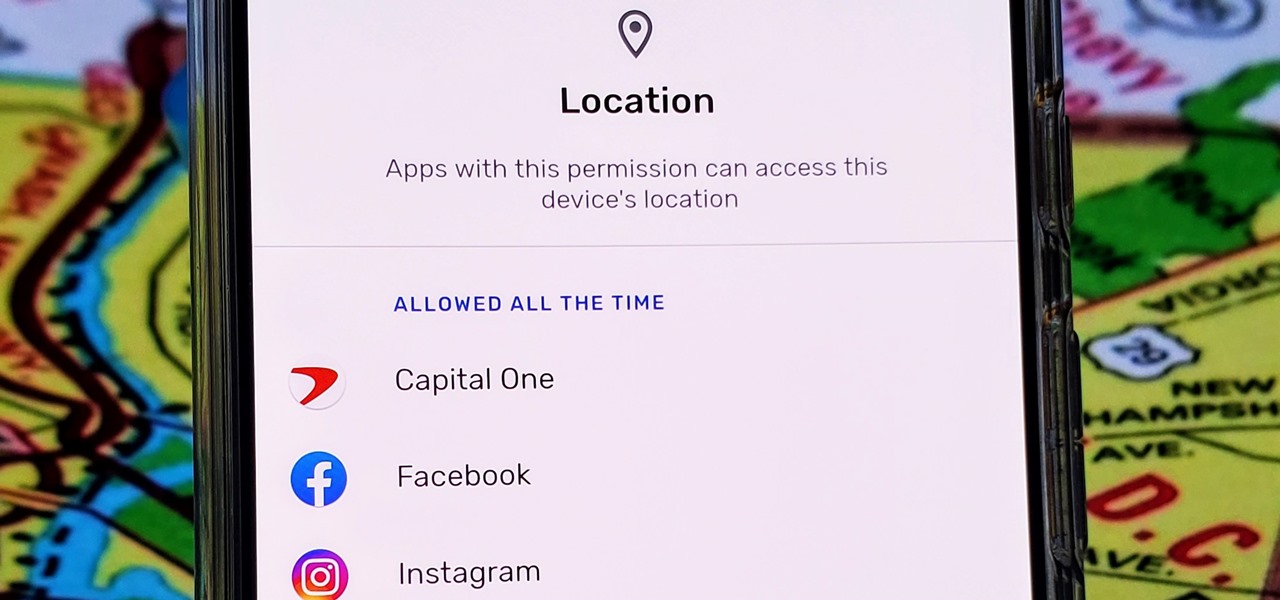
With Android 10, there are now three options when an app asks to access your location: Allow, Deny, and Allow While In Use. That last one prevents apps from seeing your location unless you're actively using them, and it's the default now. But when you first update, most of your apps will still be allowed to access your location in the background — at least, until you do something about it.

After dipping its toes into the AR cloud arena last year, Ubiquity6 is now jumping in with both feet this year.

All of your partially written, unsent emails live in your "Drafts" folders, in limbo until the day they are sent off or deleted. In Apple's Mail for iPhone, you can access all drafts from all accounts in a combined "All Drafts" folder from the app's main Mailboxes list — but only if you added it manually. But there's an even better way to access all of your drafts in Apple Mail in iOS; it's just not obvious.

One of the best things about Android is the ability to customize every aspect of your device to make it your own. However, unless you have prior knowledge or experience with every single setting available to you, you might have missed a few critical features without even knowing it. Some settings are easy to find, while others might be tucked away in another menu of their own.

Shopping wasn't always this easy. Now, in a matter of minutes, you can order your groceries for the week, send your cracked phone in for repairs, get your holiday shopping done, and have everything delivered to your front door in just a few days — without ever having to leave your home. Online shopping is convenient, comfortable, and a blessing ... right? Well, it can also be a headache.

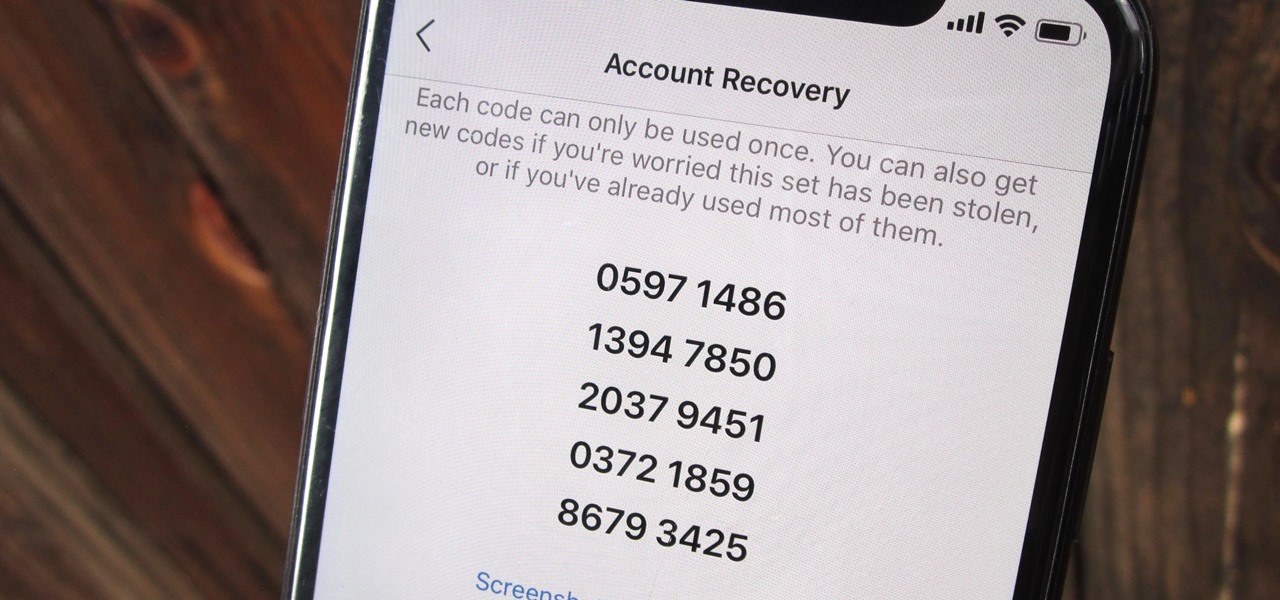
Two-factor authentication (also known as 2FA) adds a necessary additional layer of security to your username and password in many important apps. On Instagram, 2FA requires you to confirm it's you attempting to log in, with a special code sent to you via text message. Enter the code and you're in ... but what happens when you need to log in and don't have access to your phone?

While iOS 12 is arguably the best iteration of Apple's mobile operating system yet, one major fault so far is security. On Sept. 26, Videosdebarraquito discovered a passcode bypass that gave access to contacts and photos from the lock screen. Apple has since patched that security flaw, but Videosdebarraquito has discovered a new one that affects all iPhones running iOS 12.1 and 12.1.1 beta.

Players of Pokémon GO on Android now have a reason to turn on AR mode with the release of AR+ support via ARCore.

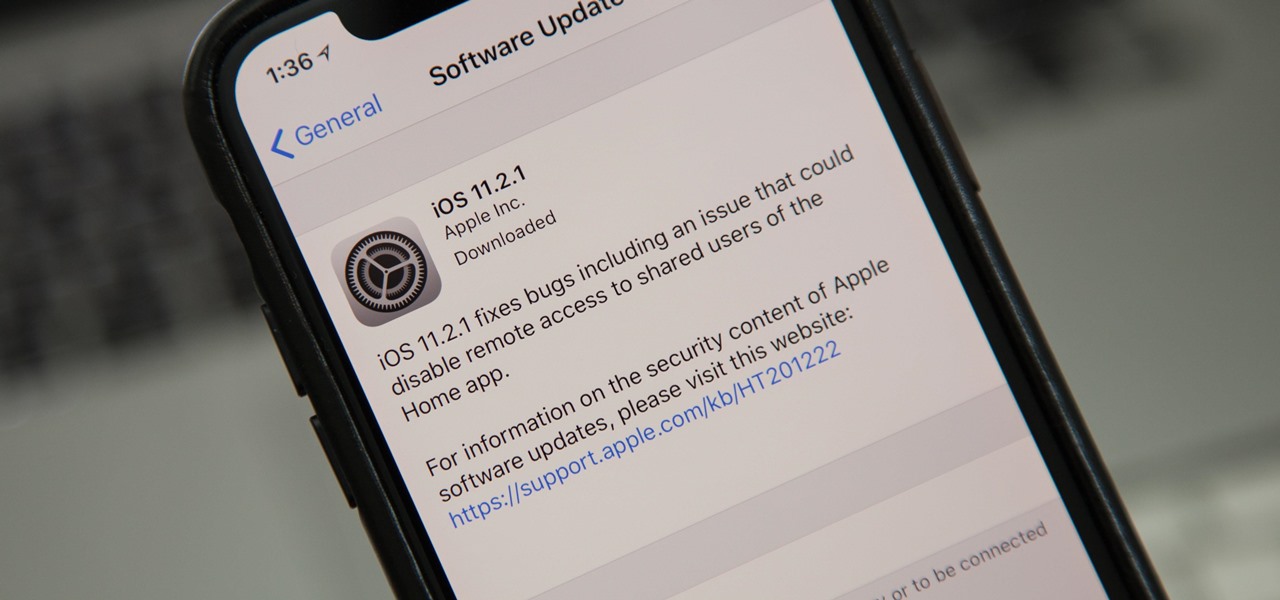
Just nine days after the official release of iOS 11.2, Apple has released iOS 11.2.1. The update initially seems to have been seeded to only a handful of users and is intended to fix bugs in 11.2.

After recently being in the news for collecting PII (personally identifiable information) for analytics and after-sales support, OnePlus has another security problem. An individual going by the name Elliot Alderson discovered an app in OnePlus devices that can enable root access with one command.

As smartphone users, we live in dangerous times. The value of phones continues to rise, making them prime targets for thieves. In 2015, the FCC estimated that one million phones are stolen each year, and with several devices starting to hit the $1,000 mark now, these numbers are sure to rise. But what do you do if you fall victim to phone theft?

I haven't bought into Apple Pay just yet, but I do love the idea of having quick access to passes like loyalty programs, boarding passes, and my Starbucks card. However, for some users, it's impossible to open these passes stored in Apple Wallet on the iPhone's lock screen. While it's not totally obvious, or even ideal, there is a way to get those Wallet passes back on your lock screen in iOS 9 or iOS 10.

The new lock screen in iOS 10 is a lot different than previous versions, but one thing that stuck around is the quick access camera shortcut. The only real difference aside from aesthetics is that now you don't have to swipe up from the camera icon. Instead, you can simply swipe to the left from right side to quickly snap a picture.

Your iPhone's lock screen is about to get a major upgrade in iOS 10, as shown off by Apple at WWDC '16, and it will make dealing with notifications and apps a breeze. The new lock screen has been fully redesigned to give users better and faster interaction with the apps they need. It's also snappier and more aesthetically pleasing with notifications no longer darkening the wallpaper.

If you like having Siri available to answer a quick question every now and again but don't want everyone who picks up your iPhone to also have access to your personal assistant, there's an easy way to disable her from working on your iPhone's lock screen. This is also something you can do if you're always activating Siri accidentally in your pocket.

If you read my previous post, "How to Hack into a Mac Without the Password", you know that it is very easy to break into someone's Mac if you have physical access to the computer. Now the question that lies is, how do we protect ourselves from this happening to us? Well, here is a way that guarantees that no one will be able to change your password through OS X Recovery.

School internet filters serve a valid purpose—they keep students from wandering off into the deep corners of the web while still allowing at least some internet access. But a lot of these restrictions are completely ridiculous, to the point where some school districts block access to the educational material in National Geographic or forbid searching terms like "China," "Iran," or "Russia"—because, you know, breasts and commies.

This is my first tutorial and it is about accessing deep web for total beginner,sorry in advance if I make any mistake plz forgive me.

In this tutorial I am going to show you how to change some file metadata, this could be very useful if you want to edit or access a file and remove any evidence of your changes.

I'm lucky enough to have internet access on my laptop practically everywhere I go because of my mobile hotspot plan. All I have to do is enable the personal hotspot feature from my iPhone and I can surf the web on any Wi-Fi enabled device. But of course, there's a catch.

You would think that with each major iOS update, there'd be fewer ways to bypass the lock screen. Unfortunately, Apple's developers have consistently failed every year since 2013 in this department, leaving open lock screen exploits for iOS 7, iOS 8, and now the latest iOS version, iOS 9, with each exploit being discovered within days of the OS release.