Virtual reality is all the rage these days, especially with devices like the Oculus Rift, Gear VR, and HTC Vive hitting shelves lately. But before any of those fancy, expensive headsets ever made it to the market, Google came up with a thrifty and inventive substitute in the form of Google Cardboard.

Greetings, fellow NBers! Welcome to my sixth iteration of my sorting series. Today, we'll be discussing a personal favorite: Quicksort, or Quick Sort.
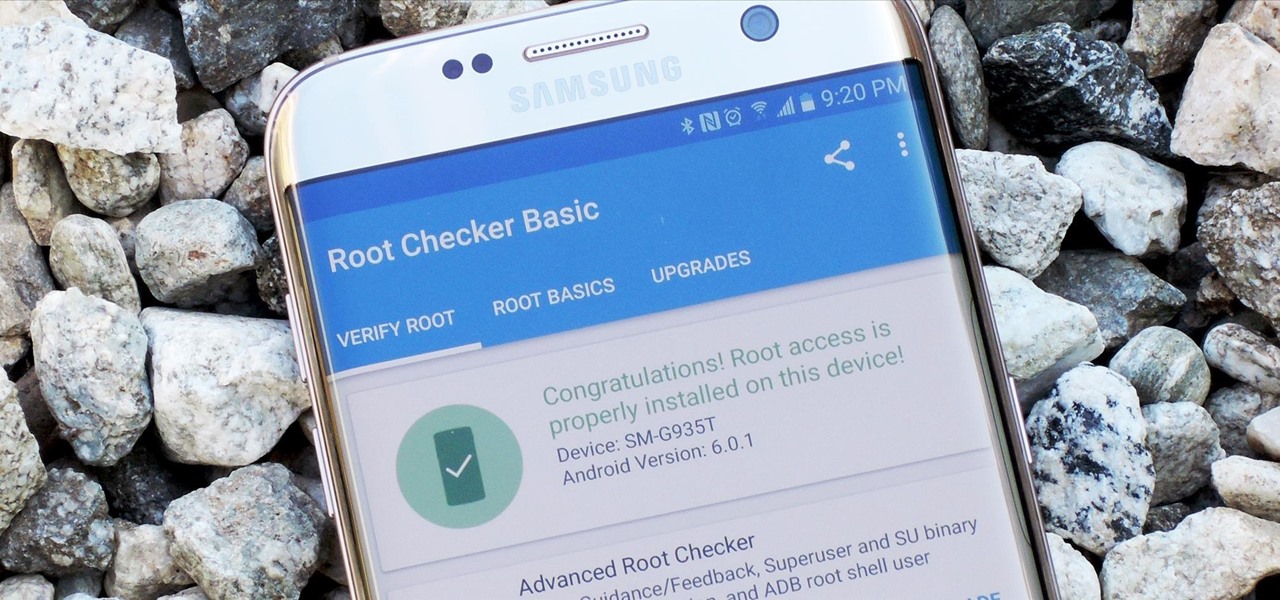
Samsung's 2016 flagship devices are some of the most beautiful, powerful smartphones ever made. And amazingly enough, thanks to legendary root developer Chainfire, the Samsung Galaxy S7 and Galaxy S7 edge are about to get even more powerful.
On the list of problems with Android, manufacturer tinkering ranks near the top. Slow or nonexistent updates, poor performance, excessive bloatware apps—all of these things can be attributed to manufacturer skins like TouchWiz or Sense, and none of them are issues with unmodified, Vanilla Android devices like the Nexus series.

Hello ladies and gentlemen, PySec here coming at you with another informative(hopefully) article for you all. In the last tutorial, we finally finished our discussion about IP Addressing and I intentionally didn't mention a really important concept with which IP Addressing wouldn't be feasible without it. What I'm talking about is how our network device gets the IP Address in order to communicate with other devices on the network/Internet. There are many different ways for that to be accompli...

First of all, I would like to apologize for a week long absents for the tutorials of this newly series, Raspberry Pi. But obviously I'm back and I present all you guys a article on turning your Raspberry Pi into a hacking platform. I'm gonna use the platform Kali Linux for the Raspberry Pi. I should note that I'm not gonna go into detail on how to install Kali Linux since OTW already has done a tutorial on how to turn your Raspberry Pi into a Hacking Pi. The point of this particular tutorial ...

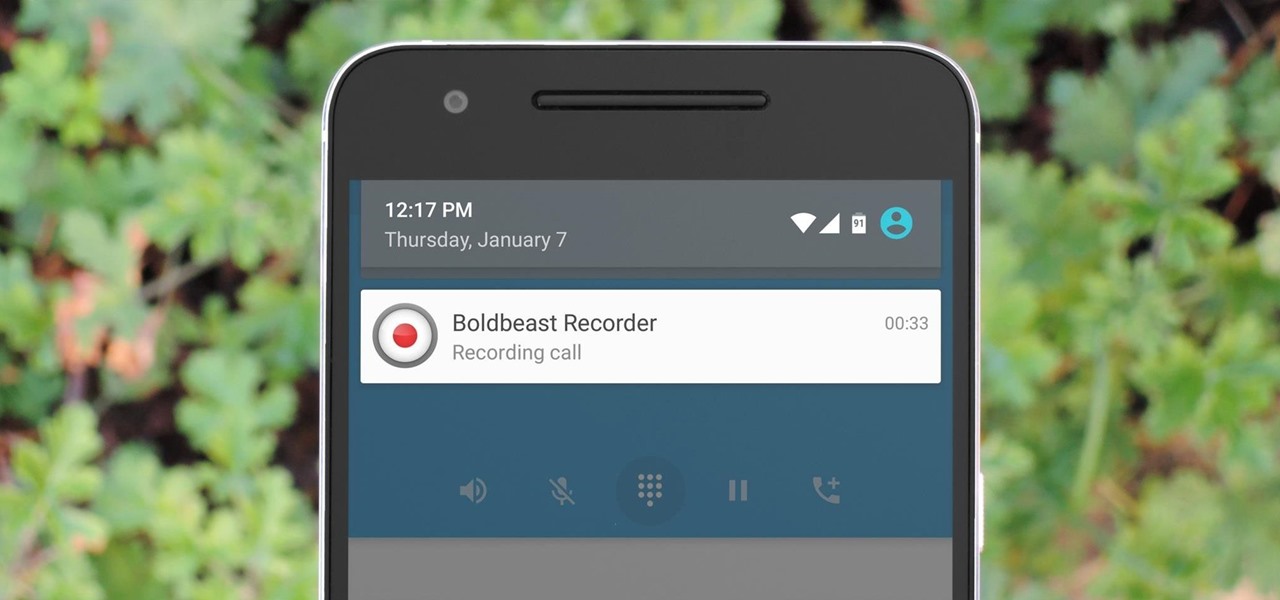
There are plenty of legitimate reasons that you might want to record a phone conversation. Let's say you operate a business and take orders over the phone, and you don't want to miss an item. Or perhaps you need to jot down some notes from a recent conference call, and things were just happening too quickly in real time.

Welcome back everyone. As many of you know, reconnaissance is extremely important in any successful hack. Without proper reconnaissance, we won't know what we're about to get into, literally.

The end of a weekend can be depressing knowing just how bad Monday morning will be when you get back to work, but that feeling is tenfold when coming back from a lengthy vacation with zero work responsibilities.

Sooner or later, you're going to come across a person at work that you don't like—or someone that doesn't like you. This can result in uncomfortable tension, insulting gossip, and a disrespectful attitude, to name just a few of the negatives. But it doesn't have to be that way. The next time you're having a workplace conflict with a particularly challenging coworker, the best thing you can do is keep your mouth shut, and here's how to do it.

Welcome back, my nascent hackers! Although my favorite TV show, Mr. Robot, had completed its first season already, I have not completed demonstrating the hacks that Elliot used in the show. (By the way, I can't wait for season 2!)

Beer isn't just for drinking anymore. There are many useful and surprising things that an ice-cold brewski can help you accomplish, from household chores to better-tasting food. It can even help you look and feel healthier.

Your average Android phone or tablet comes with quite a few apps already installed—even before you turn the device on for the first time. These pre-installed apps are certainly helpful when it comes to getting your feet wet with Android, but in many cases, they're not always the best apps available for accomplishing the tasks that they perform. Additionally, many third-party apps can add lots of cool functionality to your device, so you might say that sticking with only the pre-installed apps...

Few things in life are as exciting and magical as fire. And setting things on fire while cooking? Well, now you're speaking my language. I'm not talking about grilling, though I do love some outdoor cooking. No, I'm talking about the most badass trick in any cook's arsenal: the flambé.

When it comes to smartphones, the biggest complaint voiced by most users is battery life. Sure, it's unrealistic to expect your Android device to run for weeks without a recharge, but many folks struggle to even make it through the day without having to top off their battery.

With each day that dawns, there is a new, major hack that makes the news headlines. If you are paying attention, there are usually numerous hacks each day and far more that never make the news or are kept private by the victims. Every so often, a hack is so important that I feel compelled to comment on it here to help us learn something about the nature of hacking and IT security. This is one of those cases. Last week, the U.S. Office of Personnel Management (OPM) revealed that they had been ...

Ah, bello risotto. There are few comfort foods in the world that provide the same savory creaminess. Yet for all its simplicity, risotto has gotten a bad rap as a difficult dish to cook. In actuality, nothing is further from the truth.

Welcome back, my hacker novitiates! In an earlier tutorial, I had introduced you to two essential tools for cracking online passwords—Tamper Data and THC-Hydra. In that guide, I promised to follow up with another tutorial on how to use THC-Hydra against web forms, so here we go. Although you can use Tamper Data for this purpose, I want to introduce you to another tool that is built into Kali, Burp Suite.

If you're a fan of Thai food, I'm sure you're familiar with sticky rice. There is something so special about its chewy texture and sweet flavor. If you have a desire to make it in your own kitchen but don't have the proper tools such as a traditional bamboo basket or stackable steamer, there are several other methods that work just as well. Once you try these alternative methods, I'm sure you'll be "sticking" to them for a while. What Makes Sticky Rice So Sticky?

Welcome back, my nascent hackers! Like anything in life, there are multiple ways of getting a hack done. In fact, good hackers usually have many tricks up their sleeve to hack into a system. If they didn't, they would not usually be successful. No hack works on every system and no hack works all of the time.

Welcome back, my nascent hackers! We have spent a lot of time in previous tutorials focused on hacking the ubiquitous Windows systems, but the vast majority of "heavy iron" around the world are Linux or Unix systems. Linux and Unix dominate the world of Internet web servers with over 60% of the market. In addition, Linux and Unix servers are the operating system of choice for major international corporations (including almost all the major banks) throughout the world.

I hate to break it to you, but you're probably here because you were trolled. Thanks to a Photoshopped image making rounds across Twitter, Apple fans were tricked into believing that iOS 8 allowed them to lock individual apps, accessible only through a passcode or fingerprint ID. While that's not technically true, we've got the solution for you.

What if someone asks you to do a Nmap scan but you left your pc at home? What if a golden opportunity shows during a pentest but you were walking around the building, taking a break?

As great as the Internet is, it is not without its dangers. Hackers at any time may be breaking into your online accounts and compromising your sensitive information. Last year, hackers broke into Facebook, Gmail, and Twitter and made off with 2 million stolen passwords.

If you've ever used the automation app Tasker, then you know exactly how powerful the tool can be. If you haven't, suffice it to say that there's virtually nothing on your Android phone that Tasker can't automatically do for you.

Welcome back, my greenhorn hackers! After the disaster that was Windows Vista and the limited and reluctant adoption of Windows 8 and 8.1, Windows 7 has become the de facto standard operating system on the desktop/client.

If you don't want to wait for Android 4.3 Jelly Bean to hit your HTC One, you don't have to. Android developer LlabTooFeR released his MaximusHD ROM, which includes a leaked copy of HTC's own 4.3 update, complete with Sense 5.

Welcome back, my fledgling hackers! Nearly every commercial enterprise worth hacking has an intrusion detection system (IDS). These network intrusion detection systems are designed to detect any malicious activity on the network. That means you!

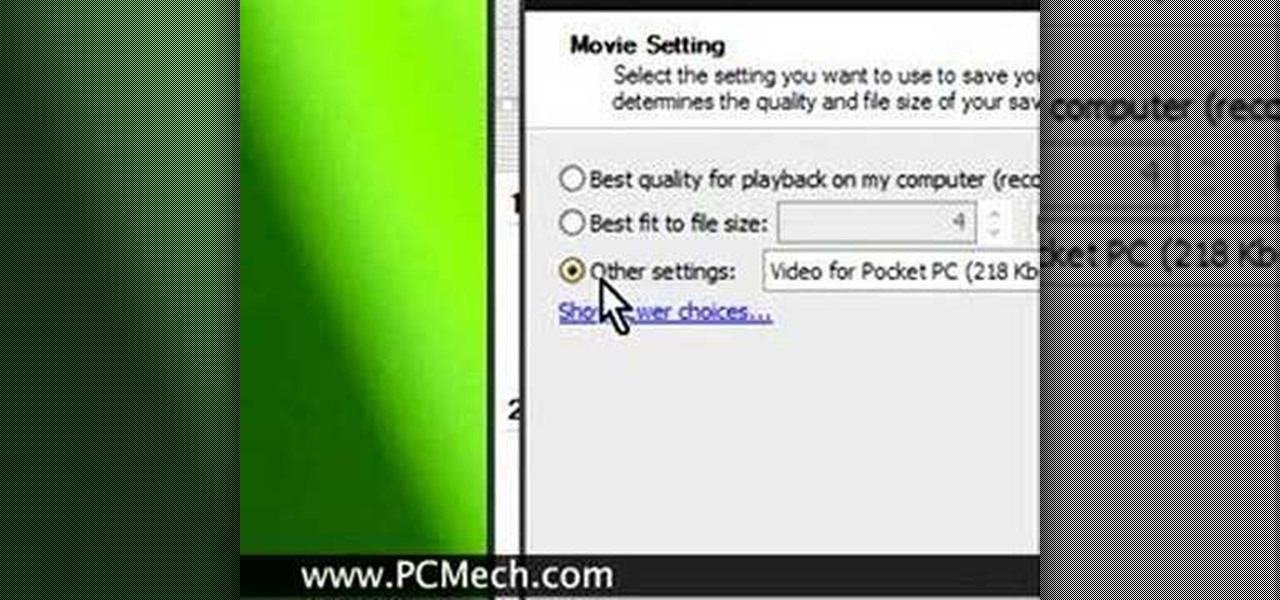
Getting Better Quality Online video with Windows Movie Maker.

Zabernism. What exactly is it? It's a term that originated in 1912, during an incident involving an overzealous soldier who killed a cobbler for smiling at him is Saverne, a small town in Alsace in north-eastern France. The said event ultimately triggered an intervention from the army who took over the power from local authorities.

If you didn't know already, December 5th, which is today, is the Day of the Ninja. It's an unofficial holiday where people across the world dress like a ninja, engage in ninja-related activities and spread information about ninjutsu online. But for web-gamers, the Day of the Ninja is the best time of year to get some Ninja Saga action in.

Warwick is one of the champions your summoner can bring onto the Fields of Justice, whose speciality is jungling. This tutorial lays out the best items, glyphs and masteries to take advantage of his innate talents so you can ensure victory in your next League of Legends game.

Your summoner is the core character in your League of Legends game, the one who summons the champions to fight on your behalf on the Fields of Justice. Going screenshot by screenshot, the summoner aspect of the game is explained. Stay up to date on your score, monitor your champions and keep track of your points!

Miss Fortune excels at ranged DPS combat on the Fields of Justice. Here's a good overview of this champion for League of Legends, which gives some useful tips and strategy ideas for building her and bringing her into battle.

Play an ice phoenix as your League of Legends champion! Here's a tutorial that shows you how to build Anivia the Cryophoenix to maximize her damage capability. She's not fast, but she can hit hard and ensure victory for your team on the Fields of Justice.

Runes are special abilities in the game which allow you customize your summoner in League of Legends. Here's how to equip runes and unlock the abilities to accumulate more runes. You can even save rune configurations in your tome and combine them to create special runes!

This spotlight focuses on Garen, the Might of Demacia, a melee champion who can be brutal with a sword. This video goes over how his abilities let him deal a great deal of damage to others while taking very little himself. Here are also some useful strategies when it comes to playing Garen in a battle.

Heimerdinger is one of the weakest champions in League of Legends, but that doesn't mean you can't still win with him! This video shows you useful strategy tips when you play the Revered Inventor based on his unique abilities and the optimized build to ensure victory for your side.

Is Kennen one of your favorite champions to play for League of Legends? This strategy guide goes over how to best use the unique abilities, masteries and optimal items to make sure this tiny ninja fights his best for your summoner!

You wanna play too? It'll be fun! This is a video which explains the best way to play the rather creepy nuker Annie, the Dark Child. Achieve victory for your team by making sure you've optimized her abilities, spells and items!