
How To: 5 Easy Ways to Use Your Touchscreen Devices in the Winter (While Keeping Your Fingers Warm)
Winter is coming... and if you don't get that Game of Thrones reference, it's okay, you're still cool in my book.


Winter is coming... and if you don't get that Game of Thrones reference, it's okay, you're still cool in my book.

Syncing your Google and Facebook friends to your smartphone gets your contacts list up-to-date quickly, so you'll never have a problem finding someone's number.
Believe it or not, the 2012 Presidential Election is (finally) almost over. While most of us are breathing a collective sigh of relief (no more political ads!), it still seems like it hasn't been that long since the last election results were announced. This time, though, one of the biggest differences is how people will watch. Since traditional cable is on its way out, and mobile devices are getting more popular every day, a lot of people will be watching this year's election results online ...
Let's say that you've got the look down, and you have your Steampunk props all ready to go. Congratulations! You're a Steampunk!
While I am a writer with a degree in Creative Writing, I haven't published any Steampunk fiction. However, as a panelist and track director, I've been on panels with many well-known Steampunk writers and have gleaned insight from the things they've said. I've compiled some of those things into this post, which will hopefully be helpful to all of the writers out there!

RFID chips are everywhere. They're in passports, credit cards, and tons of items you've bought in the last 5 years or so. Big retailers like Walmart started using tracking products with RFID as early as 2004, and today, they're used in everything from mobile payments to hospital record systems. Chances are, unless you're a hermit (in which case you wouldn't be reading this anyway), there's an RFID tag within a few feet of you. Photo by sridgway

Redbox recently announced a partnership with Verizon to bring a new streaming video service called Redbox Instant to an already crowded table. No prices have been released yet for the service, but with Netflix, Hulu, Amazon, YouTube, iTunes, and many others all attempting to get a hold of your dollars, what are currently your best options? Subscriptions Services

As I said before in my earlier post on how to make a two-tone doorbell, sound is more than just music. Note blocks can create a wide variety of notes and sounds, and those can be used for more than just making a stirring rendition of "Still Alive" from Portal.
Omniscience is not required to make some really cool shit happen. Yes, it took a while, but we can make fuel from the Sun! Solar panels are basically our answer to God. And now that we can make solar electricity, finding the most efficient way to harvest it is tricky.

I admit, when the new iOS 5 update for Apple devices was coming out, I had iTunes open all morning with my iPhone 4 attached... waiting... waiting... waiting until finally the new version of iOS was available for download. I stopped everything I was doing and quickly initiated the process of updating my device. After two excruciating hours, my iPhone 4 was finally ready to go and I couldn't be anymore happy. Who needs an iPhone 4S when you've already got iOS 5?

If you've run out of time for all of our more time-consuming Halloween costume ideas, here are some places on the web for free, downloadable paper masks. There must be at least 100 options among these links to satisfy your last-minute costume needs! Just download, print, and cut 'em out to the appropriate size, then either glue a stick/handle on or tie some elastic string on.

Learn tips for using the Celtx free screenwriting software, including project library, production schedule, editors, and online services in this free screenwriting video series.

In this online German recipe video series, learn from gourmet chef Rainer Wickel how to prepare German potato pancakes, wienerschnitzel, and a German sauerkraut casserole. This expert chef will teach you about traditional German cooking, what wienerschnitzel is, what German potato pancakes are, what a sauerkraut casserole is, and the ingredients and utensils needed to create these traditional German dishes.
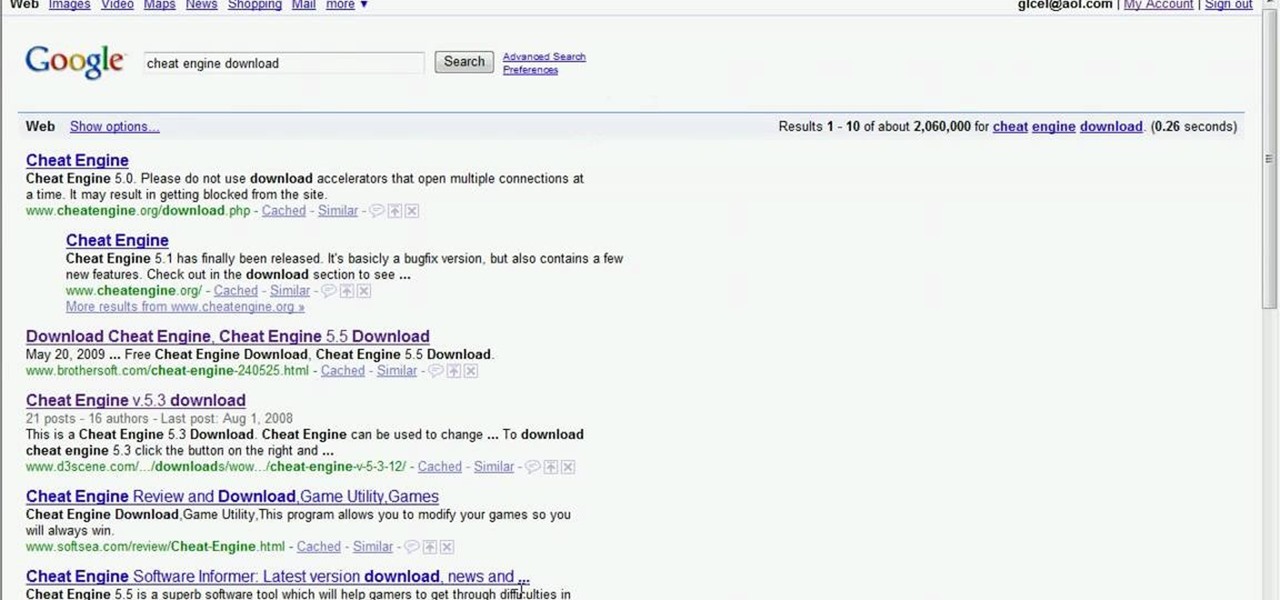
This video tutorial will show you the one thing everybody wants to know… where's the Cheat Engine 5.5 download at? There's nothing to getting Cheat Engine on your computer. Once you have it, you can start hacking and cheating all of the flash games you play on Facebook and MySpace and every other site with online games. So, to download Cheat Engine 5.5, you just need to Google it and you'll find it in the first result. Or you can just go to http://www.cheatengine.org or the download page for ...
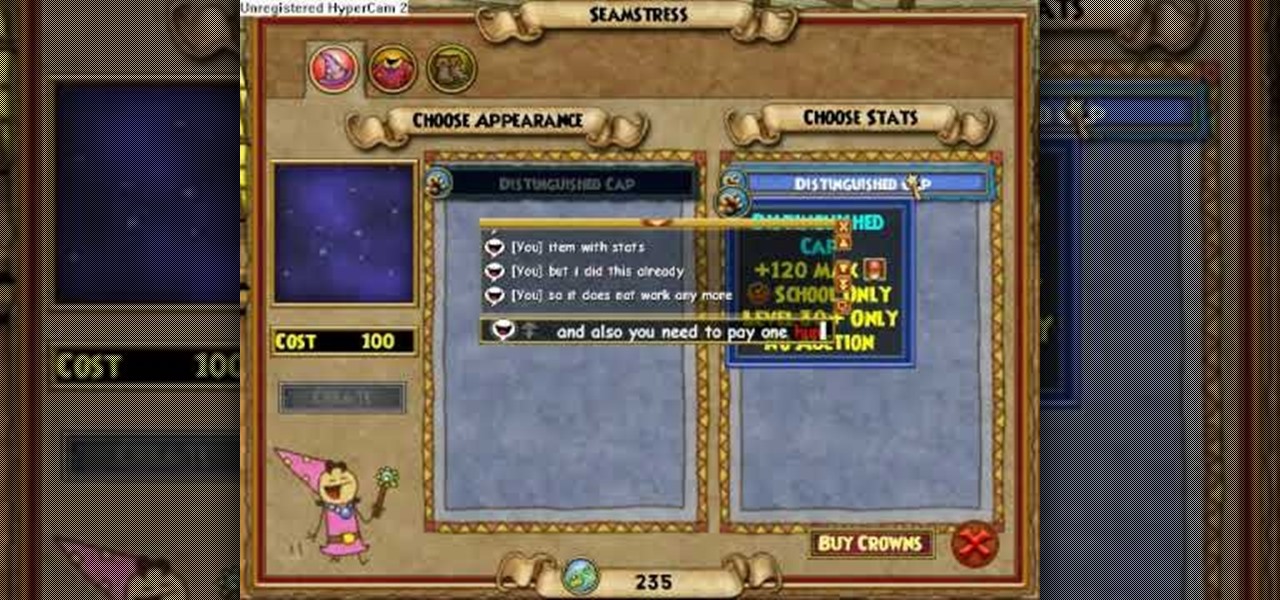
Hemming and stitching in Wizard101? Yep, learn how to stitch itms together and make an awesome wizard-like costume.

Get the inside scoop on Wizard101 hacks, cheats, tricks, tips, and walkthroughs! Watch this video tutorial to learn how to get into Nightside without beating streets in Wizard101. You don't have to beat all of the streets to get to Nightside in Wizard City.

IMVU is a 3D avatar chat, instant messenger, and dress up game. Get help with all of your IMVU avatar needs with these IMVU tips and tricks! Watch this video tutorial to learn how to earn credits easily on IMVU (09/28/09).
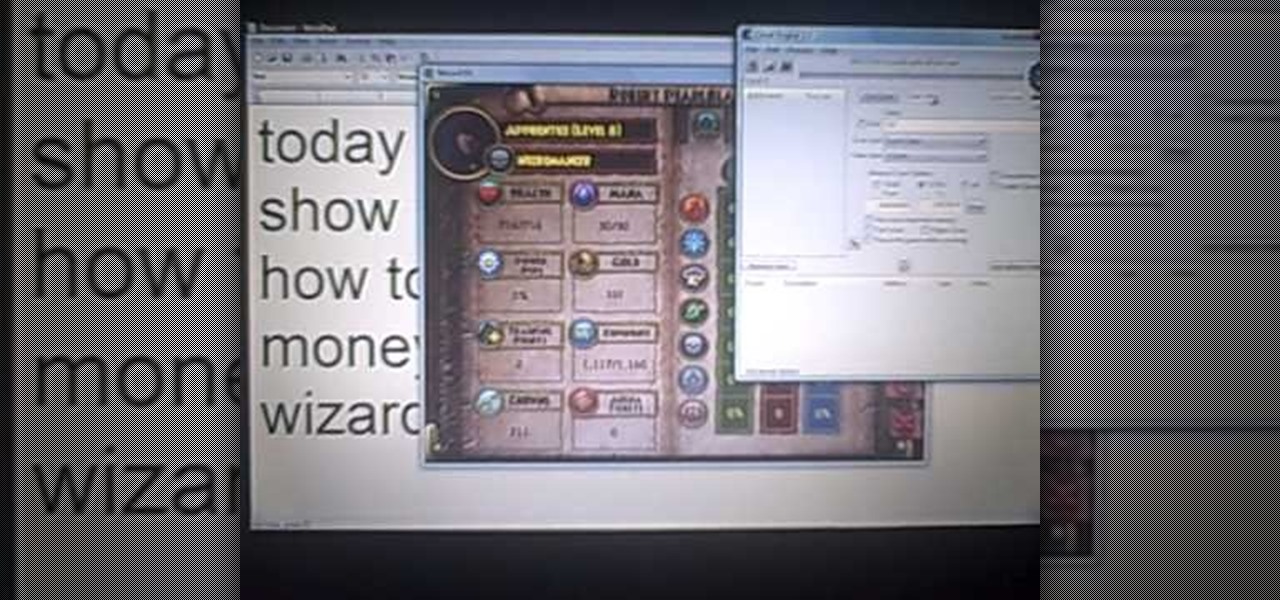
Get the inside scoop on Wizard101 hacks, cheats, tricks, tips, and walkthroughs! Watch this video tutorial to learn how to hack Wizard101 money with Cheat Engine (09/27/09).

Learn everything you could possibly want to know about the internet, multiplayer game Evony. Watch this video tutorial to learn how to hack Evony (09/17/09).

Meez is the social entertainment leader combining avatars, web games and virtual worlds. Get help with all of your Meez avatar needs with these Meez tips and tricks! Watch this video tutorial to learn how to cross-dress on Meez.

Learn everything you could possibly want to know about the internet, multiplayer game Evony. Watch this video tutorial to learn how to get heroes and troops in Evony.
Remember those old vinyl records? Remember jumping on the 8-track bandwagon? Switching over to cassette tapes? How much money you spent converting your music collection to compact discs? To MP3s?
When you're a writer with work published across various online platforms, building a portfolio of your work can be pretty time-consuming. That's where Authory comes in.

UPDATE: Entries are now closed. Thank you for participating! Next Reality is where we help you literally 'see' into the future of augmented reality, and to help with that mission we're offering three free pairs of Snap Spectacles 3 to three lucky readers who sign up for the Next Reality daily AR email newsletter.
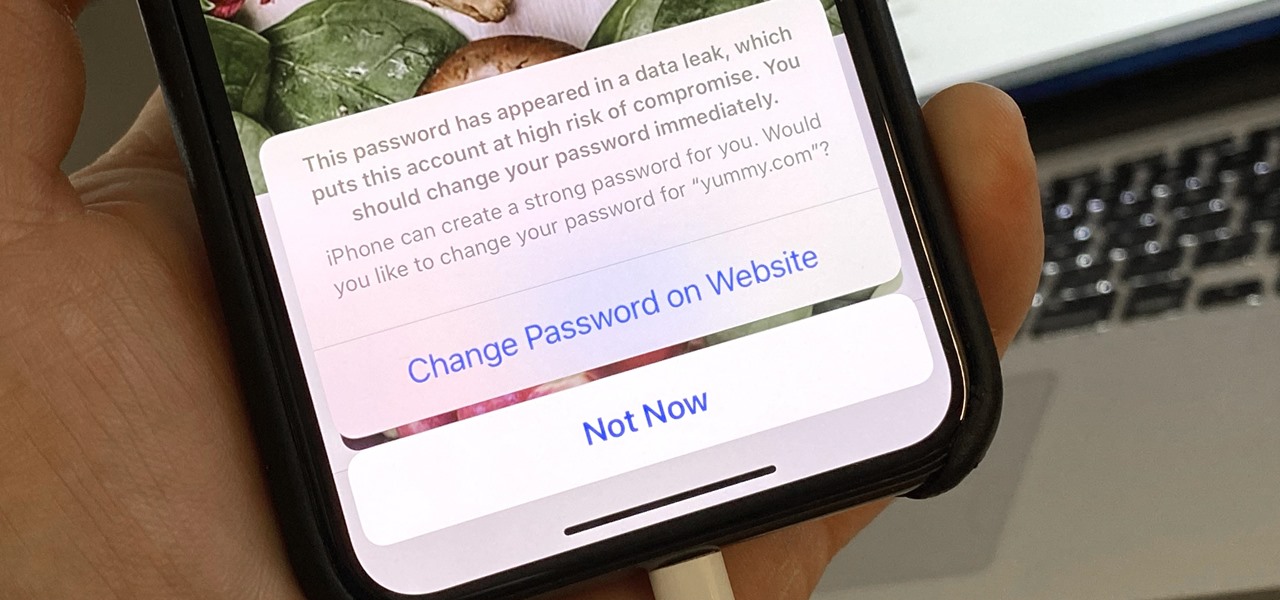
Everything lives online these days, so it's not uncommon to have hundreds of credentials for different accounts on apps and websites. That's why a password manager is a must, and your iPhone has one built right into iOS that you can start using today. In iOS 14, it's gotten even more useful since it can now monitor your passwords regularly to see if any match leaked password lists online.

On Android, you can connect your PayPal account to Google Pay so that you can use that as a payment option when checking out with Google's digital wallet platform. It even works across Google services like the Play Store, Gmail, YouTube, and the Google Store. If you have an iPhone, you can also use PayPal via Google Pay, but what you can do is limited.

You may be familiar with image-based or audio-based steganography, the art of hiding messages or code inside of pictures, but that's not the only way to conceal secret communications. With zero-width characters, we can use text-based steganography to stash hidden information inside of plain text, and we can even figure out who's leaking documents online.

Whether you miss the good old days of Telnet or you want to know what hacking was like when security was nothing but an afterthought, Telehack is the game for you. The text-based hacking game is a simulation of a stylized combination of ARPANET and Usenet, circa 1985 to 1990, with a full multi-user universe and player interactions, including 26,600 hosts.

For enterprise augmented reality platform makers, remote assistance apps represent one of the greatest opportunities to show off the power of immersive computing. These apps enable experts to guide front-line workers or customers with AR prompts and other content in the field of view of their smartphones or smartglasses.

When it comes to cybersecurity, one layer isn't enough. A complex password (or one created with a password manager) does a good job of protecting your data, but it can still be cracked. Two-factor authentication strengthens this by adding a second layer of security, giving you even more protection against online threats.

Phones these days are expensive. The iPhone 11 Pro is presumed to start at $999, following the iPhone XS and iPhone X's leads. One way to bring down that cost is to trade in your old iPhone, but there isn't one clear-cut way to do that. You could trade your iPhone into a participating website or put yourself out there and sell the iPhone on your own. It's all about what's best for you.

A lot of people still trust their web browsers to remember every online account password for them. If you're one of those users, you need to adopt a more secure way of managing passwords, because browser-stored passwords are hacker gold mines. With a USB Rubber Ducky and physical access to your computer, they can have a screenshot of all your credentials in their inbox in less than 60 seconds.

Your iPhone just went missing, and now you're panicking. You need it for work, to get around, to contact your friends and family, and pretty much everything else in your life. So, what are the chances you might get it back? The odds may be stacked against you unless it's just under a couch cushion, but you can improve your chances of recovering your iPhone by taking certain steps.

There have been concerns with how much personal information Google tracks and all the things they know about us. Of course, that's what makes Google services so useful, they can use that information to cater to each of us individually. So yes, it serves a purpose, but it's not great for personal data security.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.
Whether it's for health reasons or just to look better, many of us want to get in shape. It's a long process that starts with nutrition, and dieting is never easy. Fortunately, there are some great food-tracking apps that will make it a lot easier to become a healthier version of yourself.

Just like cash, bitcoin is used for everything from regular day-to-day business to criminal activities. However, unlike physical cash, the blockchain is permanent and immutable, which means anyone from a teen to the US government can follow every single transaction you make without you even knowing about it. However, there are ways to add layers of anonymity to your bitcoin transactions.

Analysis of photographs and social connections can be a huge component of social engineering. Understanding who a person is, as well as who they know, can establish links within a company. This information could be used by hackers to execute elaborate social engineering attacks.

Beginners learning brute-forcing attacks against WPA handshakes are often let down by the limitations of default wordlists like RockYou based on stolen passwords. The science of brute-forcing goes beyond using these default lists, allowing us to be more efficient by making customized wordlists. Using the Mentalist, we can generate millions of likely passwords based on details about the target.

Coinhive, a JavaScript cryptocurrency miner, was reportedly discovered on the BlackBerry Mobile website. It was placed there by hackers who exploited a vulnerability in the site's e-commerce software that allowed them to anonymously mine cryptocurrency every time the website was viewed. There's no doubt Coinhive, an innovative mining method, is being abused and exploited by hackers in the wild.