
How To: Get started with a college savings plan
It's never too early to put away money for your child's education. Consider these options before choosing a plan. Watch this video to learn how to get started with a college savings plan.


It's never too early to put away money for your child's education. Consider these options before choosing a plan. Watch this video to learn how to get started with a college savings plan.

Digidesign has transitioned all of their plug-in software copy protection from floppy drive based key disks to copy protection authorizations that reside on the iLok technology provide by PACE. The following is some information about iLok technology.
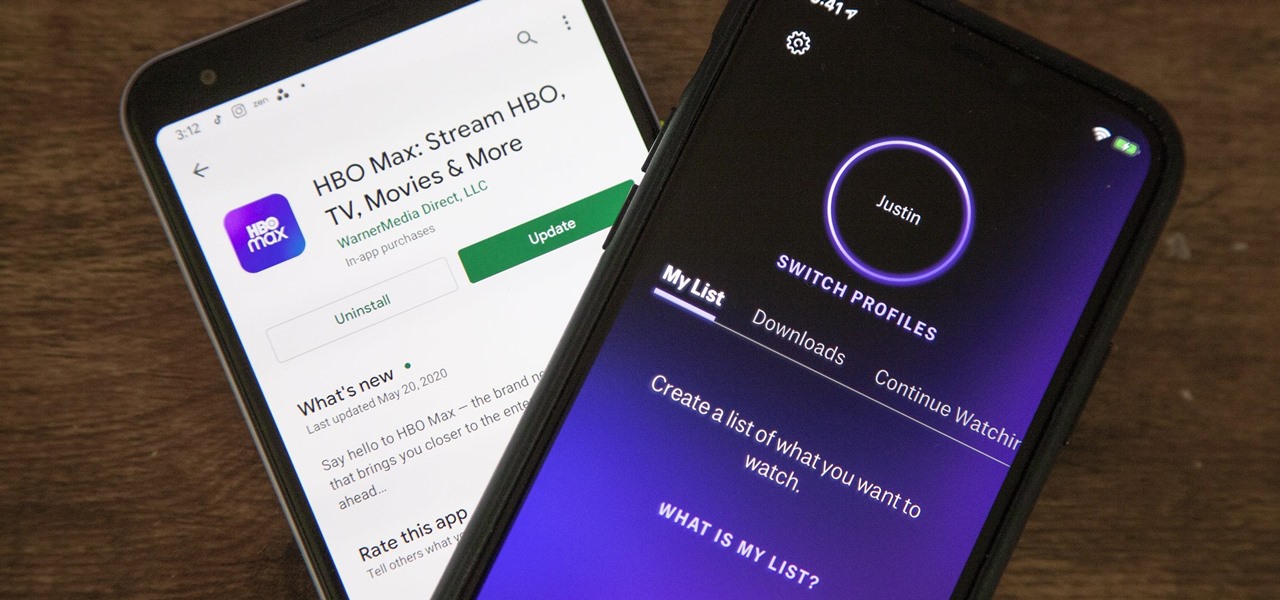
As of May 27, HBO Max is taking over your HBO Now or HBO Go account. If you have your devices set up to auto-install new app updates, you should pause it right now if your HBO app hasn't been updated yet. There's one thing you'll want to do before you make the leap. However, you're not out of luck if you already upgraded.
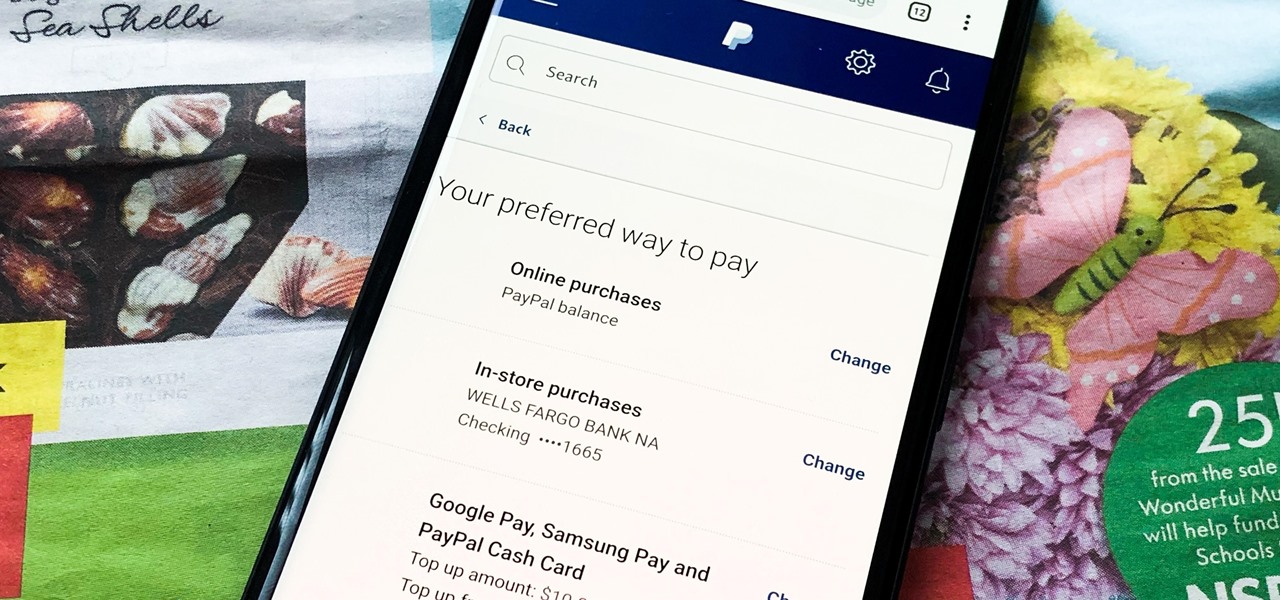
Making a purchase through PayPal is great because you have the option to pay using your account balance, a bank account, debit card, credit card, rewards balance, or even PayPal's own credit product. You need to pick one to be your preferred payment method for each in-stores and online but, unfortunately, changing these preferences can get a bit tricky on your iPhone or Android phone.

Media subscriptions are all the rage these days. Between Netflix, Apple Music, HBO Now, and countless more, your TV, movie, and music options have never been better. Unfortunately, all these choices weigh heavily on your wallet. So, when there's an opportunity to snag not just Spotify but Hulu and Showtime as well, all for just a tad bit over five dollars a month, how could you turn that down?

With iOS 12, iCloud Keychain has become a more useful password manager for your iPhone with strong password suggestions, password reuse auditing, and Siri support. However, before you jump ship from your current password manager, you should consider all the reasons why iCloud Keychain doesn't make sense as your primary password manager.

Recently, a user on Reddit complained that their Snapchat account had been temporarily banned because Snapchat noticed the user's account was going through a third-party service. In reality, the account in question was running on a jailbroken iPhone, and it was far from the first to be banned by the messaging app.

When it works, Android's Smart Lock feature is incredible. There's no need to enter your PIN when your phone "knows" it's in your hands — just unlock and go. But Smart Lock, particularly its Trusted Places feature, can be finicky sometimes.

HBO's Westworld has touched down on iOS as a mobile game, giving players the chance to manage their very own futuristic theme park set in the wild west. Unfortunately, the game is currently only available in select countries as a soft launch until its fully developed. But if you'd like to try out this game right now, there's a simple workaround to get Westworld on your iPhone.
If you want to automate tasks with your smartphone, IFTTT is a great app. It does a tremendous job of helping you find applets or creating your own from scratch, so it's easy to connect your favorite online services and make them react to each other. With all this personal information, though, you should ensure that your data is secure by enabling two-step verification.
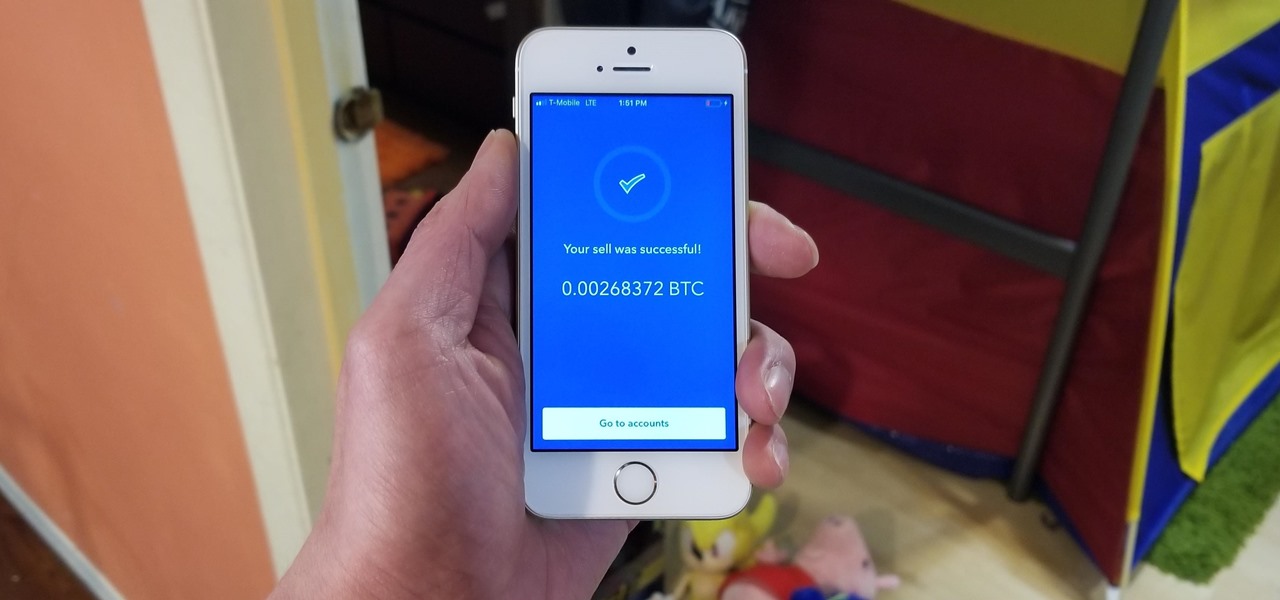
Coinbase has become the most popular mobile wallet app due in large part to its user-friendliness. The app takes the hassle out of buying and selling Bitcoin (BTC), Bitcoin Cash (BCH), Ethereum (ETH), and Litecoin (LTC), letting Android and iPhone users alike trade their favorite cryptocurrency in a few easy steps.

After exploiting a vulnerable target, scooping up a victim's credentials is a high priority for hackers, since most people reuse passwords. Those credentials can get hackers deeper into a network or other accounts, but digging through the system by hand to find them is difficult. A missed stored password could mean missing a big opportunity. But the process can largely be automated with LaZagne.

Tor is an excellent obfuscation network for web traffic, and while instant messaging over the network is very useful, it can be relatively difficult to configure. In this guide, we'll look at two synchronous communications platforms (instant messengers) which can be routed over the Tor network, Ricochet and XMPP.

It's really easy to binge-watch episode after episode, and that's exactly what Netflix wants us to do. Before you can even think twice, the next video is playing and you're stuck wallowing in the abyss of unintentionally marathon-viewing your new favorite TV show, and there's nothing you can do. Except there is something you can do — and it's as simple as disabling one little feature.

Google seems to be growing tired of the way links appear in its Search results page, because they're currently experimenting with a color change (that's already causing lots of controversy).
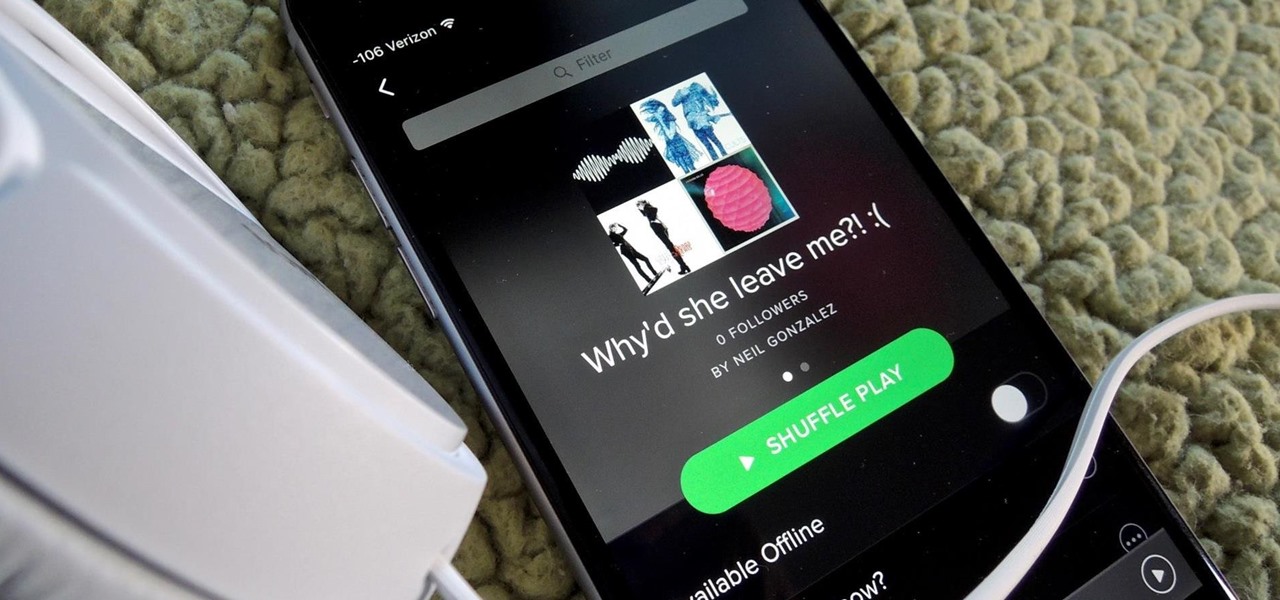
Playlists are more than just a list of songs that you enjoy listening to while in traffic or hosting a party—they're stories that illustrate who you are or your frame of mind at a certain point in your life.

What's up readers? We have ever so slightly touched upon this concept of scope with variables but still don't really know what it means. In this tutorial we will learn the behaviors of variables existing in our programs and within functions.

This is second post in my series of posts for finding hacked accounts online. Please do read the part 1 of the post at http://null-byte.wonderhowto.com/how-to/find-hacked-accounts-online-part-1-0164611/
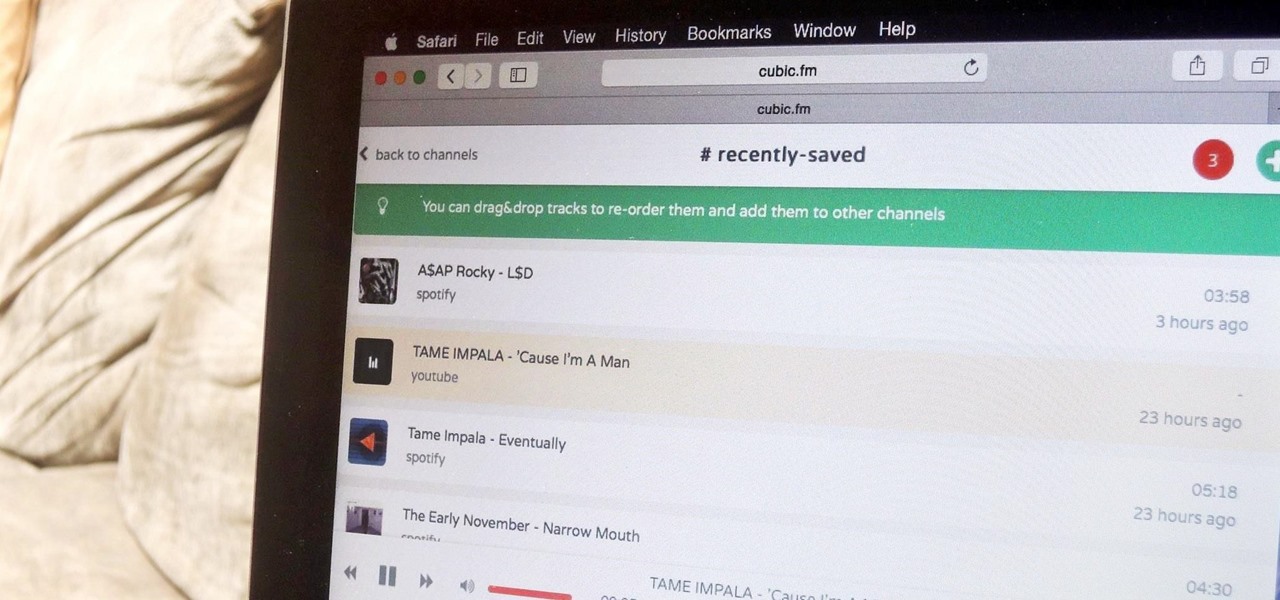
The options for finding random or specific music to listen to are vast. Spotify is excellent for streaming popular music and new releases, while SoundCloud provides a healthy dose of user-generated remixes and originals. And then there's YouTube for everything else.

Here is the World's Funniest Cat video!
In the weeks before Apple officially released iOS 8, consumers were abuzz over rumors that a new feature would password-protect your photos and text messages from prying eyes. Unfortunately, this ended up being untrue, though we did cover some alternatives to protecting your important information using some built-in features and a third-party app. Now, there's a new iOS app that can do it all.
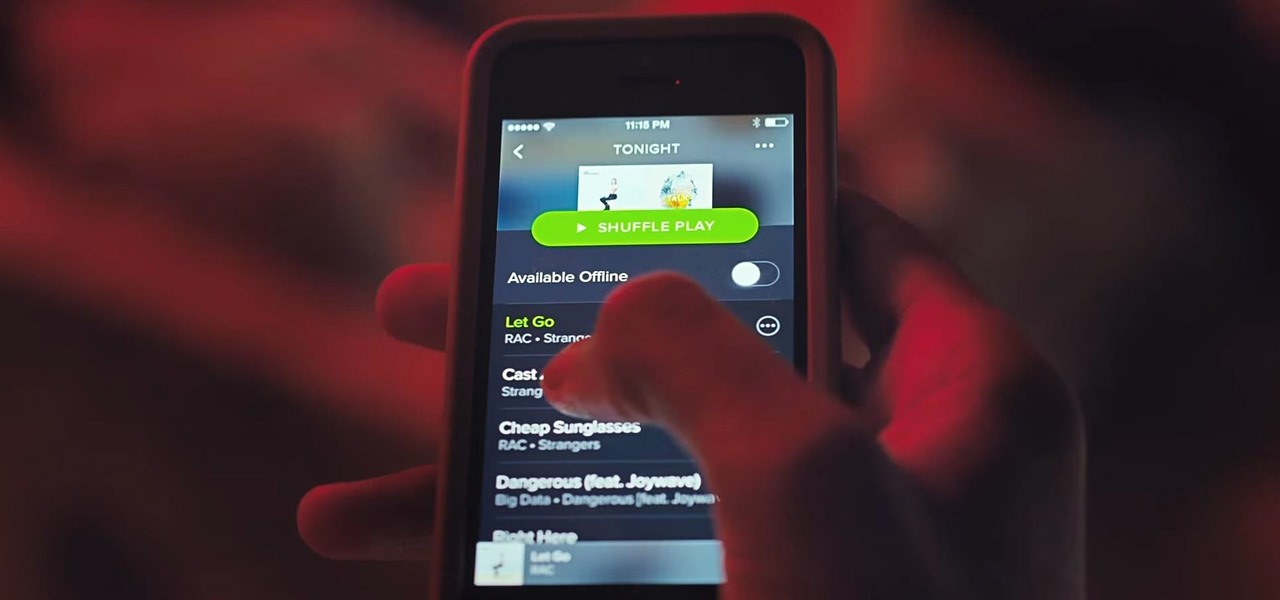
Spotify is how I listen to almost all of my music; I use it on my way to work, while I workout, and even while I'm in the shower. And more often than not, I use my Spotify account on various devices including my MacBook, iPhone, and LG G3. In order to make listening to music across multiple devices even more convenient, Spotify released “Spotify Connect” earlier this month.

Certain files contain sensitive data that you don't want being shared with just anybody. Even still, it would be nice to be able to send such a file to a certain confidante without fear of it falling into the wrong hands.

If you've ever used IFTTT, you know how well it can automate your online world. The premise is simple—If This, Then That—but the results are powerful. From automatically printing images based on hashtags to getting around Twitter bans, the service is quite useful with a wealth of possibilities.

Spam emails are emails that are sent to you without your permission. They can quickly fill up your email account if you don't do anything about it. Each email server deals with spam in a different way. Gmail is good at separating the spam for you so that you can get rid of it more quickly. It is easy to delete the spam and if you want to take it a little farther, you can get some of the spam to stop coming all together.
There has been much talk about how unsecure the cloud is because of PRISM’s newfound ability to demand all of your data without any resistance. This has spin doctors in the Cloud Storage industry losing their mind. They suddenly went from a central hub for 10GB of your files, to an easy window for Big Brother to track you through. Centralized cloud storage is no longer a safe way to keep your files, but we still need a way to access our files anywhere we go.

Spammers are the bane of every email user. No matter what you do, junk mail always breaks through the spam filters. And some of the best ones seem to come from legit companies, and that's because they aren't legit companies— they're spammers masquerading as legit companies.
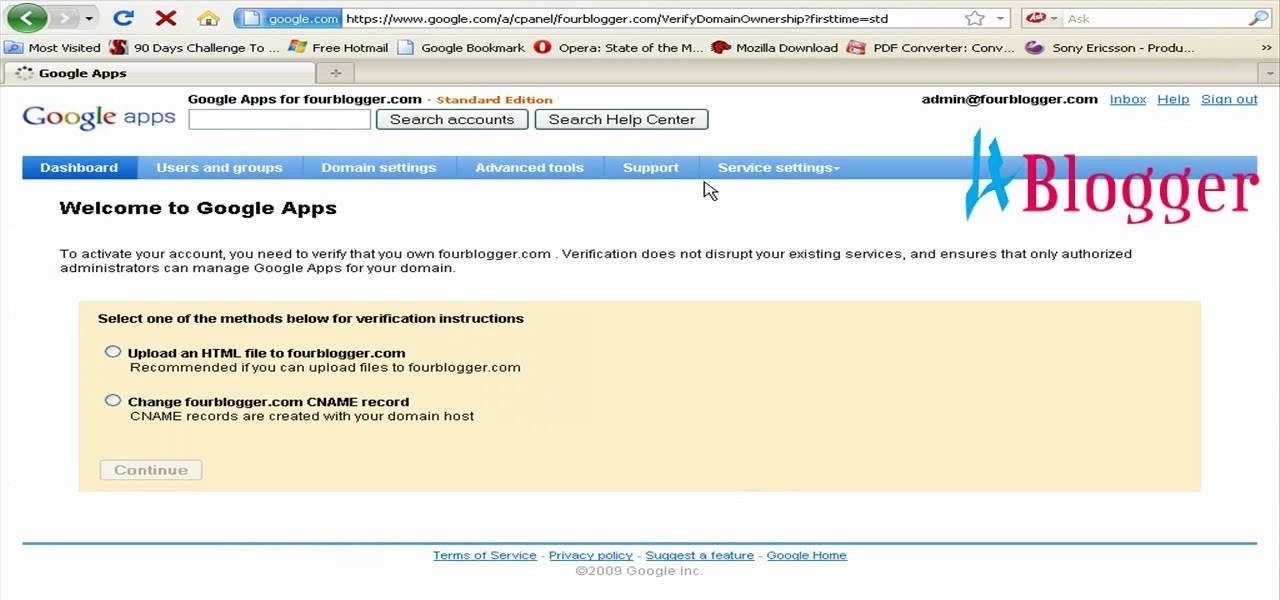
You can create the Google apps email like Gmail for your domain. So to do this first you need to go to the google.com/a and click on the standard in "other Google apps editions". Now click on "get started". Now select "administrator: I own..." and enter your domain name and click get started. Now on next page create your account by filling all the fields and click continue and now fill the info of your administrator account and click I accept button. Now next step is for the verification of y...
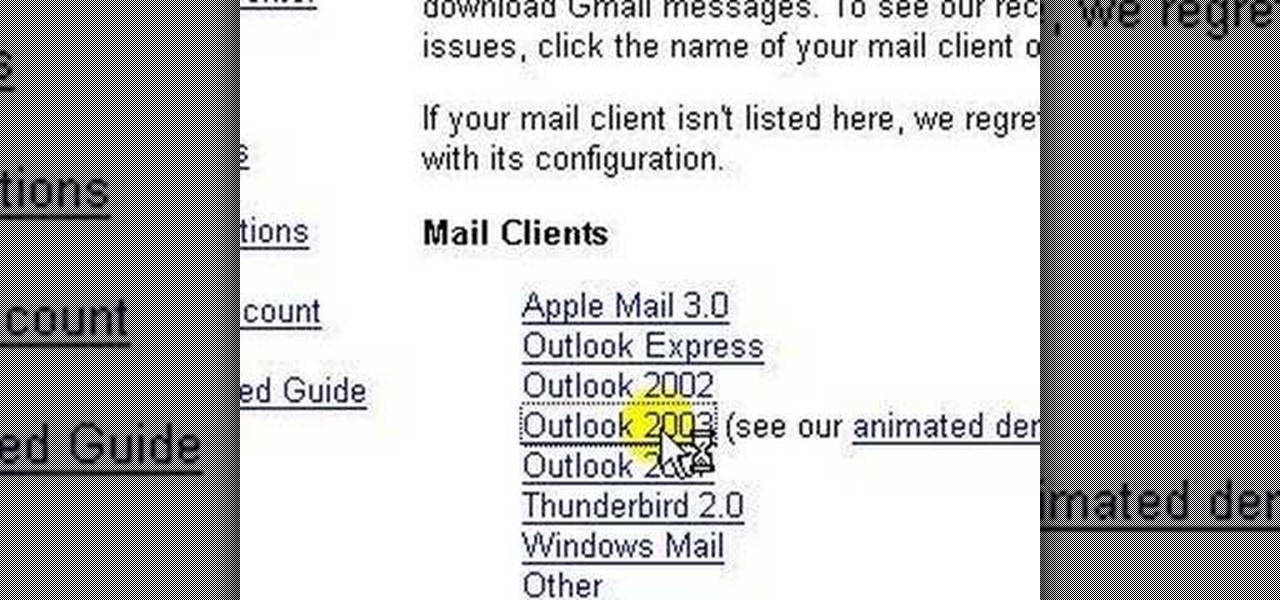
lakercoolman shows us how to set up our gmail account with this quick tutorial. Basically outlook express is a program that helps us to organize our email with added features such as contacts, to do lists and calender entries. Its an offline email client that allows us to work offline and also lets us set up exchange servers aswell. Ohter email servers such as hotmail and yahoo charge for thios service but the advantage of gmail is that IMAP or POP access is free. in ofer to set up, navigate ...
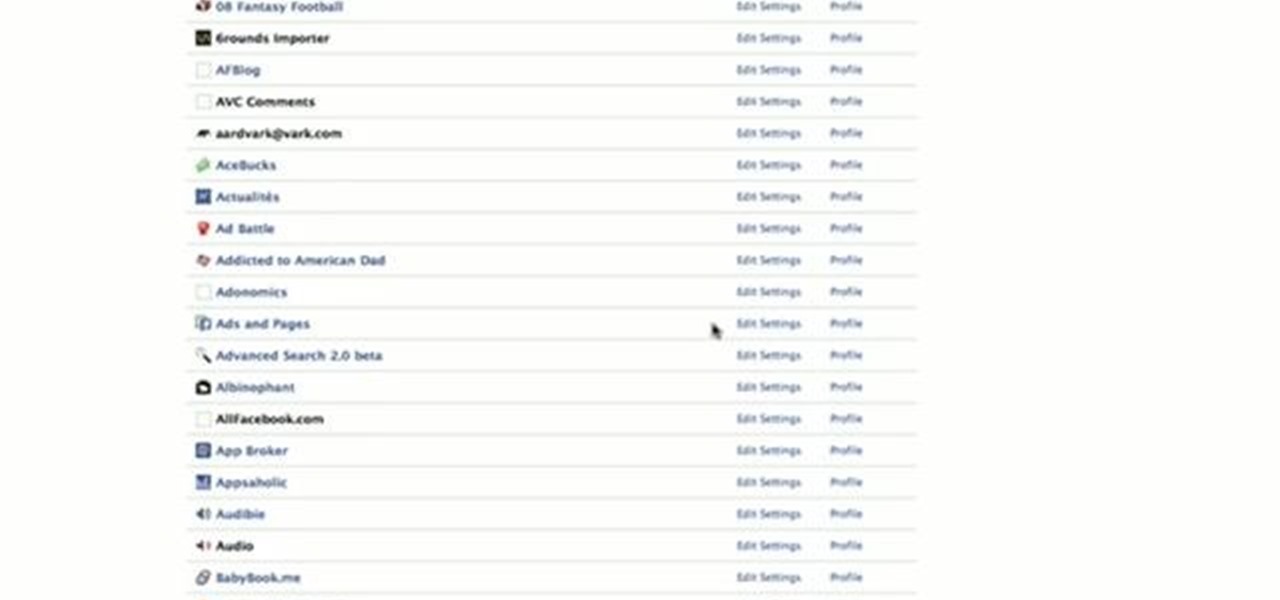
This video is about how to block recent activities on Facebook. The first thing that you will have to do is to log in to your Facebook account. After logging in to your account, the next thing that you will have to do is to go to account settings and look for the "Ads and Pages". After you have found "Ads and Pages", click on the "Edit Settings" and go to the "Special Permissions" tab and uncheck "Publish recent activity" box then press "Okay" after wards. The next step is to look for "Events...

This video demonstrates how to use Skype to make calls. The best thing about it is that it is free. You only need a computer, a microphone and a web camera. To use Skype, you first have to download the Skype software. This can be done through the website of Skype. Then install the Skype on your computer. Next you need to have an account created. For this you have to provide a screen name and also your email address. You need to type a password for your account too. Once your account is create...

If you've ever wanted to know how to write checks in Intuit QuickBooks program, this instructional is for you. To write a check in the QuickBooks program: Select banking from the menu bar, and then the write checks command. Select the checking account for which the checks will be drawn from the checking accounts drop down menu. Assign the check a number if you will be printing the check. If you are printing the check, make sure that the "to be printed" box is checked. Enter the correct date f...

Got a digital camera, but no idea how to share pictures with friends and family? Try the photo-sharing site Flickr.

Turn your possessions into cash and become an online selling machine. You will need: Something to sell, a computer with internet access, an eBay account, a digital camera, shipping supplies, something to sell,a computer with internet access, an eBay account, a digital camera, & shipping supplies.

Karma is an idea that exists in the Hindu, Buddhist, Jain, and Sikh religions, which simply holds that all actions have consequences. In other words: karma’s not a bitch, but you might be. If so, here’s how to start sending the world good vibrations. Learn how to store up some good karma for yourself.

The built-in Files app on your iPhone has only gotten better since it was introduced in iOS 11, with small improvements after each new iOS version. You can manage files on your internal storage as well as in iCloud Drive, but one of the best features is being able to manage media and documents from all of your cloud storage accounts in one place.

As fun as Twitter is, it can also quickly turn scary. Anonymous, aggressive, and troll accounts can attack you for your tweets and stalk your every move. While you could make your profile private and block users, there are lesser-known privacy and security features that you can switch to improve your safety online.
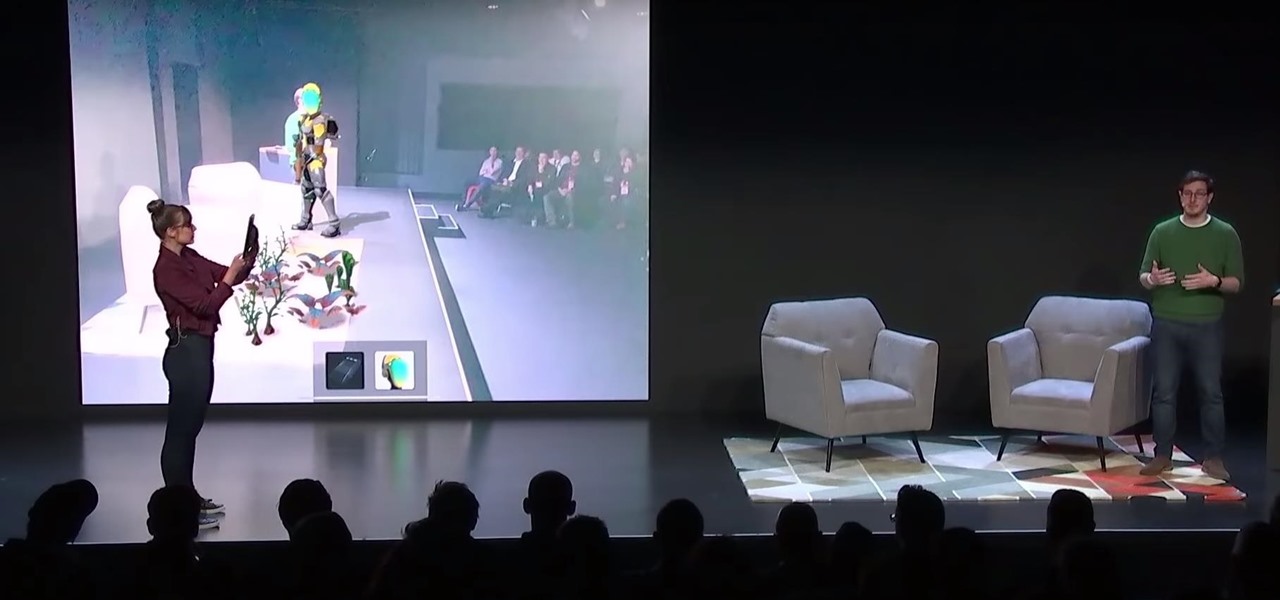
After Apple unveiled ARKit 3 at WWDC on Monday, Unity Technologies wasted little time on ensuring its developers can take advantage of it.

If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.

With the growing list of products Apple offers, the number of devices connected to your Apple ID can get quite extensive. Having all those devices connected to your Apple ID helps you keep track of them, but when it comes time to part ways with an Apple TV or Apple Watch, those devices can still be attached to your Apple ID. In some cases, this could affect the overall security of your account.