Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to set up SSH tunneling to securely transmit HTTP traffic.

Turn your possessions into cash and become an online selling machine. You will need: Something to sell, a computer with internet access, an eBay account, a digital camera, shipping supplies, something to sell,a computer with internet access, an eBay account, a digital camera, & shipping supplies.

Belly dance is originally a form of traditional Arab dance. Most of the techniques of belly dance demonstrate circular motions in the core area of the body (the belly, the hips). Belly dancing is a fun, sensual dance that also builds & strengthens abdominal muscles. In this belly dancing lesson, learn the circle step turn move. Follow along with this belly dance tutorial to master this move. Amira of Samadhi teaching the circle step turn. Start with an 8 count setup of the circle step, then c...

This EVF mount is the mount all RED users have been waiting for. It is inexpensive, adjustable and will not loosen. This simple three hundred dollar mount is a great addition to any RED ONE camera setup. This video will show you how to install the Zacuto EVF mount on the RED ONE Camera.

Can you sleep in a hammock every night instead of a bed? Millions of people around the world do. It is so much cheaper than a traditional bed/box-spring setup. Lighter too! Would you rather move a bed, box-spring, frame etc, or just a sheet with 2 carabiners, 2 Eye Bolts (Lag Threaded), and 2 bits of rope? Watch this video survival training tutorial and learn how to sleep comfortably in a hammock.

This video is to get you started with the initial setup of the Doom 3 to Maya workflow. Topics covered (in order) are set up, export your first character ingame, texturing, animations on character cycles, load game models into Maya. Part 4 is a WMP video.

This is a maya 8.5 lesson but Jason really wanted to cover this crash course in animation for Zbrush users. This is everything you need to know for a pose to pose animation setup. This is geared towards illustrators to learn the basics, not full animators.

Installing Joomla on a Windows server can be tricky, on Windows running IIS even more so. Installing Joomla 1.5 in this scenario has caused many frustrations.In this video, we take the process step by step and jump over the hurdles that cause some people to wind up pulling their hair out. If you follow along closely, you will be up and running in no time, and if you haven't already tried to do this, you will wonder why people find it so difficult. There are some prerequisites to the steps in ...

We show you how to play video you download from the internet on your TV using an iPod Video and remote dock ...no need to wait for the iTV device from Apple. Then we give you an updated review on Parallels software which enables the use of Microsoft Windows and Windows applications on the Mac at the same time that the Mac OS X is running. The last segment presents a review of a couple of models of PowerPoint presentation remotes from Keyspan PR-US2 and Interlinkelectronics RemotePoint Navigat...

This two-part video is designed for people who are very familiar with CINEMA 4D. When you're using CINEMA 4D, you can setup channels for export to compositing applications, but sometimes a material change is more efficient and easier. In this first part, you will learn how to set up a material tag on any shape that contains a CAP or a ROUNDING feature. In the second part you'll create some quick buffers (a trick which is especially useful when creating some alpha channels from animated MoGrap...

Spammers are the bane of every email user. No matter what you do, junk mail always breaks through the spam filters. And some of the best ones seem to come from legit companies, and that's because they aren't legit companies— they're spammers masquerading as legit companies.

In this tutorial, we learn how to sign up and set up a Twitter account. Twitter is a social networking site where you have 140 characters to tell your friends how you are feeling, what you are doing, or talk to them! You can follow people and other people can follow you. You can choose who follows you, which will create and strengthen online relationships. You can even get business referrals from this! Just by getting yourself out there, this is a great tool. To sign up, you will simply go to...

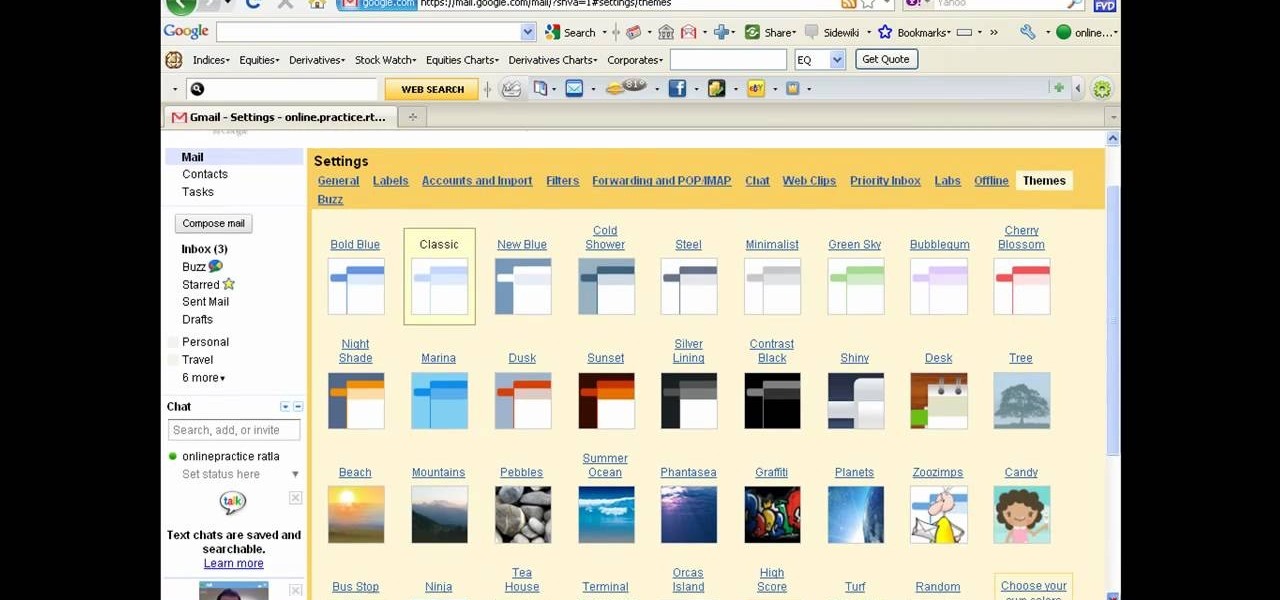
There a ways to personalize your Gmail experience, and one of those is picking personalized Gmail themes which make emailing funner. But if you're not sure what kind of theme you want to use from all the available Gmail theme choices, there's an option called "Random" which provides you a random theme based on your geographical location, and will change when in a different location.

In order to register a domain name at Name.com, you will need to set up an account at Name.com. When you have set up an account, by supplying a username and password, you will need to log in. You will be able to check to see if your domain name is still available by typing it in, in the orange search bar, near the top of the page. After you type it in, click on search. Try ".org" first.

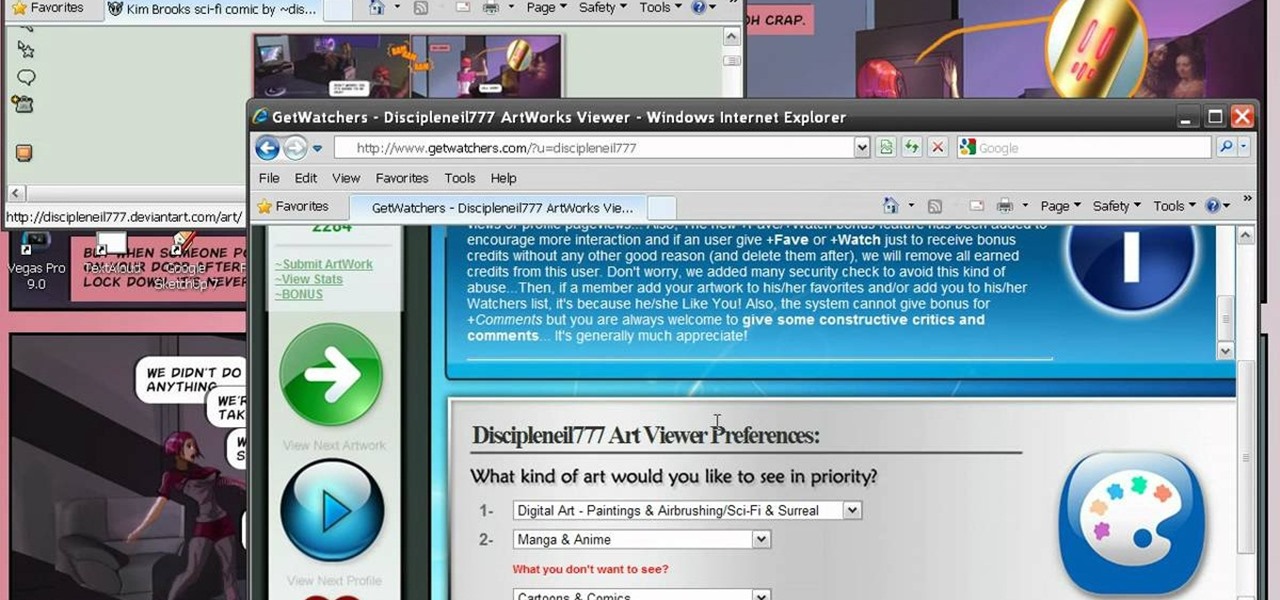
The most important part of art is making sure others see it and appreciate the message. In this tutorial, learn how to attract more viewers to your artwork, as displayed on the website, Deviant Art. This is a great way to get your vision out there and make your voice heard. You don't have to wait until you can get your pieces in a museum - get started gaining fans today.

Linking your social networking activity together has never been so easy. Randy Ksar shows us the simple process of linking your Facebook and Flickr accountstogether so you and your friends can view your them both easily without navigating from site to site. First, you should log into your Facebook page click on Profile, select settings and you should see Activity. All you need to do is simply click on the Flickr link and type your Flickr user account name and you're done. Note that your Flick...

This video shows how to setup the Firefox as your browser for web, on Macbook Pro. First, Open the Safari browser by double-clicking, from the list of Applications. Then, enter the URL of Firefox website, in the URL address field of Safari, to open it. When the website is opened, click the link "Firefox 3, Free download.", which will automatically start downloading. Then when asked to proceed, a message comes, click "Continue". It starts to download Firefox 3. When done, it will open a window...

Dafistps3dude4life shows us how to remove friends you have already requested and accepted from your Facebook account. First, sign in to Facebook with your account email and password. Next, look for a tab at the top of the screen with the "Friends" title. Click on it and you will be taken to a new page. Look to the left and click the "All Connections" button. Find the friend you wish to remove. There should be a small box with an "x" on it. Click on it. You will then be shown a prompt asking i...

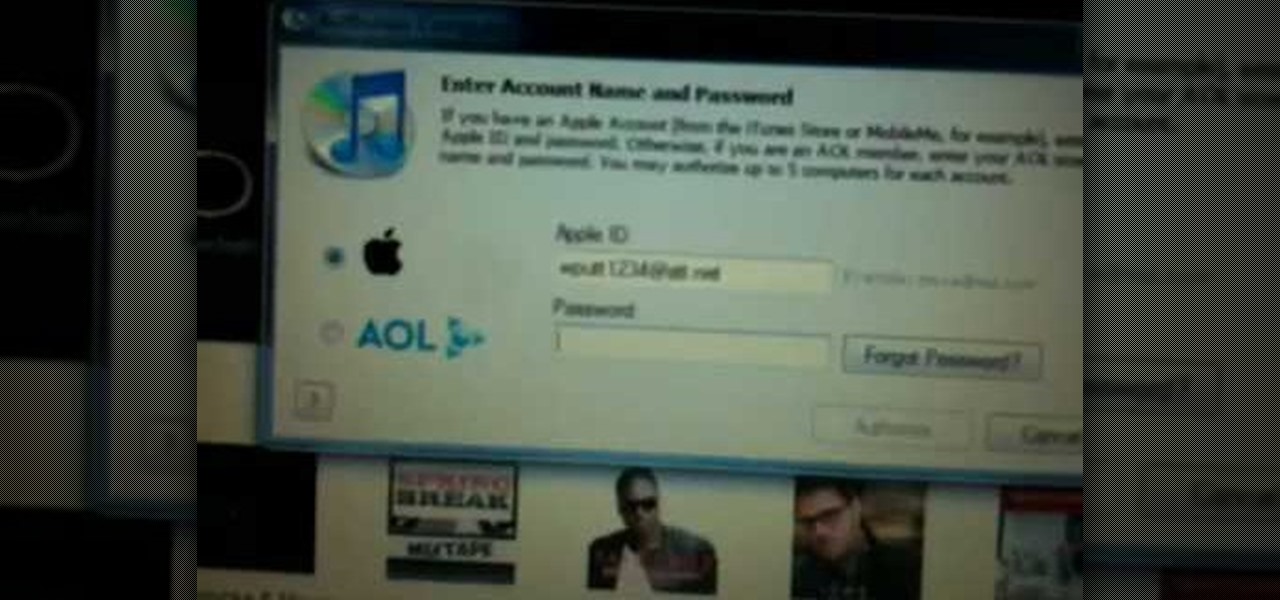
In this video from wadeputtii we learn how to authorize or de-authorize a computer on iTunes. Go to iTunes, sign into your account. Now click on Share and you will see Authorize Computer or Deauthorize Computer. If you want to authorize, click on that and enter your apple user email address and password. Then click authorize. If you have a new computer or you want to prevent someone else from using your account on your computer and you want to deauthorize your old computer, go to Share and De...

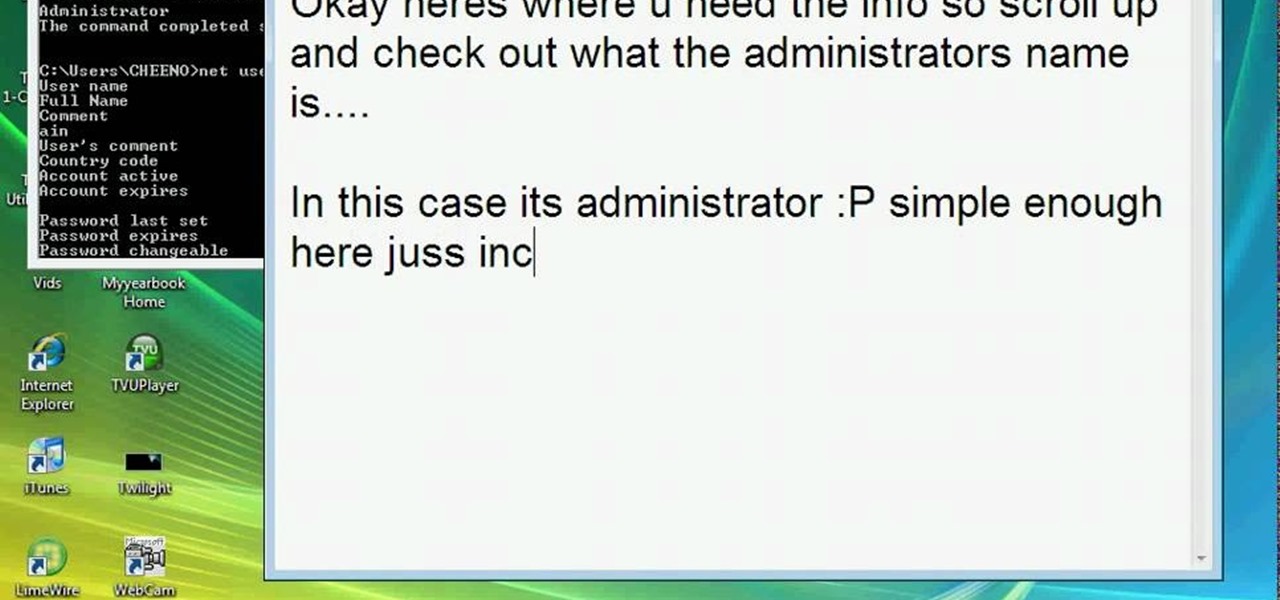
This video teaches how to change/hack administrators Account/Password. Click START and find CMD. Type "net user" without the "". Now type "net user administrator" without the "". Scroll up the screen and find the administrator's name. Now go back down and type "net user administrator *" without the "". Now it will ask you for a new Password. Type a new Password which you won't forget. Now another command prompt will pop up. Just type in exit to come out of the CMD. Don't get caught and do it ...

This video will show you in eight steps how you can get and use wifi and dsi to use with your Nintendo. This is a helpful tool because it can be a little confusing to get started using different technologies without clear instructions.

Start out by going to www.Facebook.com. From this page you will be able to create your own personal Facebook profile. Fill in your name, email, password, sex, and date of birth. Click 'Sign up' after you have filled in all of this information correctly.

The built-in Files app on your iPhone has only gotten better since it was introduced in iOS 11, with small improvements after each new iOS version. You can manage files on your internal storage as well as in iCloud Drive, but one of the best features is being able to manage media and documents from all of your cloud storage accounts in one place.

Using a strong password is critical to the security of your online accounts. However, according to Dashlane, US users hold an average of 130 different accounts. Memorizing strong passwords for that many accounts is impractical. Fortunately, password managers solve the problem.

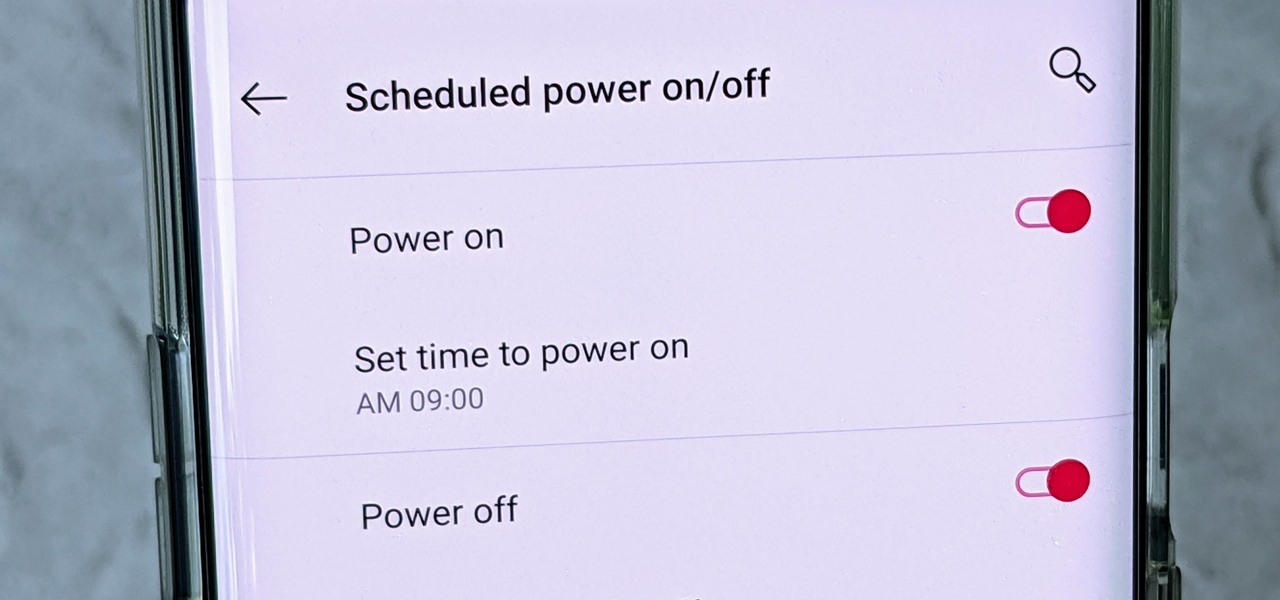
One of the more interesting power-related features for OnePlus phones is the ability to schedule a time to turn it, off then back on again. While OnePlus phones typically run blazingly fast, you can still benefit from the RAM clearing and process killing that a reboot provides. And since you can schedule this to happen overnight, you can wake up to a refreshed, restarted phone every morning.

With the growing list of products Apple offers, the number of devices connected to your Apple ID can get quite extensive. Having all those devices connected to your Apple ID helps you keep track of them, but when it comes time to part ways with an Apple TV or Apple Watch, those devices can still be attached to your Apple ID. In some cases, this could affect the overall security of your account.

We're nearly there — Apple released the seventh iOS 12 beta to developers Monday, August 13. While not totally unexpected, beta testers understand the struggle of predicting the next update, as Apple has switched haphazardly between two-week, one-week, and irregular release schedules for both the developer and public betas.

The easiest way around a security policy is to find users who don't follow it. The Have I Been Pwned database identifies accounts with information breached by major third parties like Yahoo and LinkedIn. With Maltego, hackers can locate breached accounts created using company email addresses, potentially giving attackers access to a company account if the employee reuses a compromised password.

Between the Cambridge Analytica scandal and the revelation that Facebook logs your calls and text history on Android, many are considering joining the #DeleteFacebook movement. But it can be difficult to leave the site, because so much of its content is only available to active users. If you want to keep in the loop without sacrificing your privacy, you'll want to follow the steps below.

Accompanying Snapchat's core features, like editing snaps and applying filters to them, is Bitmojis. These are small avatars that you create in your own likeness and use all throughout Snapchat. Formerly, there were two "styles" that you could pick from to make your Bitmoji: Bitstrips style and Bitmoji style. But Snapchat has a third style now that will redefine the way you use Bitmojis.

When traversing the web, you'll regularly come across websites that require you to create an account. With the majority of these accounts, protection is limited to a simple password. Despite this, many people are still using weak passwords such "123456." For these reasons, you really need a password manager, and our research has shown that LastPass is still your best bet.

Over the years, the internet has become a dangerous place. As its popularity has increased, it has attracted more hackers looking to make a quick buck. However, as our dependency on the web grows, it becomes increasingly difficult to sever all ties. This means we have to protect one of our weakest points, the password.

You seriously won't even recognize Twitter after this. Twitter has launched a major redesign, their first in years and it seems the app is finally starting to listen to what users are looking for — starting to being the keywords.

New statements from Apple make it clear that they do not believe a hacker, or group of hackers, breached any of their systems. This comes after a recent report from Motherboard that a hacker gang called the "Turkish Crime Family" is threatening to remotely wipe up to 559 million iPhones by April 7.

Before many games make it to the US-based iOS App Store, they get "soft launched" in a smaller country to get real-world testing for bugs. It's a pilot program, so to speak, as countries like Vietnam or the Philippines have far fewer iPhone users than the US, thus offer a more controlled environment for developers to get feedback and zero-in on issues that may occur in a game's early development phases.

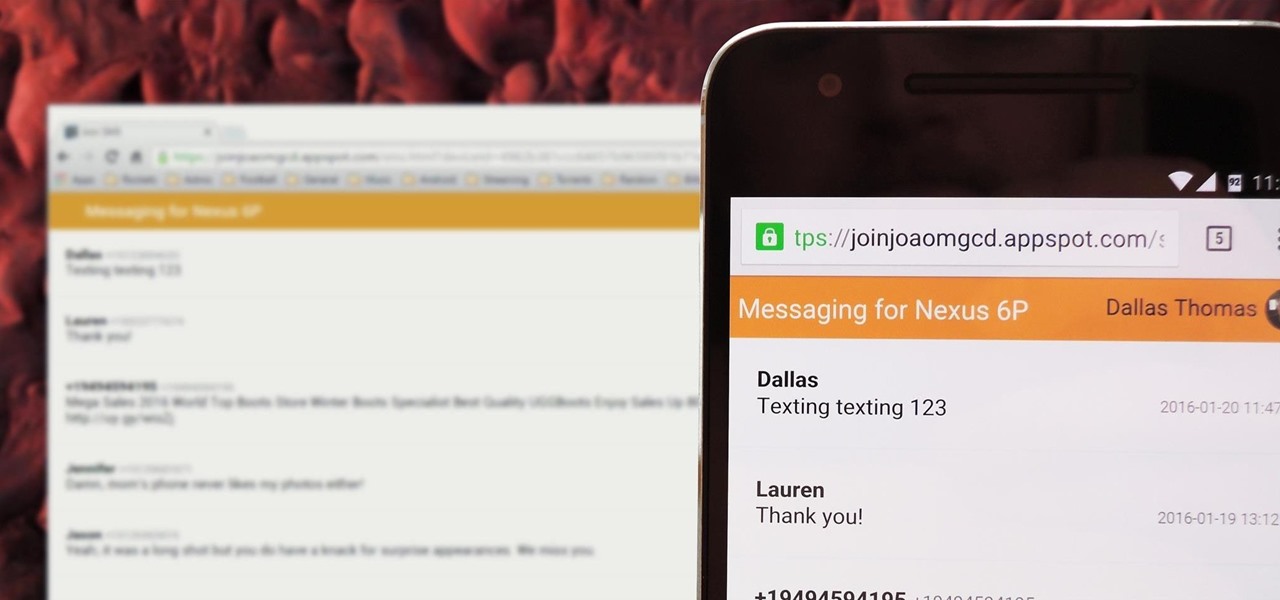
There's no iMessage app on Android, so unlike the folks who own both an iPhone and a Mac, we have to rely on third-party solutions to send and receive SMS messages from our computers. But on the bright side, this means we don't have to buy an exorbitantly expensive desktop or laptop to respond to texts when our phones are out of reach, because Android is all about cross-platform compatibility instead of chaining you to an ecosystem.

If you're a U.S. expat living, traveling, or studying abroad, or just someone who typically uses virtual private networks (VPNs) in order to access the North American video libraries of services like Hulu or Netflix, you were probably surprised to see that these video streaming services don't work on your Chromecast or Chromecast 2.

Android has a system-wide user dictionary file that any third-party keyboard can utilize, if it so chooses. This file contains all of the words that you've added to your keyboard manually, and of the big-name players, Minuum, TouchPal, and the Google Keyboard call on this file to determine their user dictionaries.

One of the few areas where Android lags behind iOS is a comprehensive backup solution for apps. Root tools, such as the popular Titanium Backup, are capable of backing up all of your apps and their data, but not everyone wants to root their device and potentially run into issues with voided warranties.

Google's got a hit on its hands with this one. Android 5.0—AKA "Lollipop"—will be making its official debut next month, but a new preview build has given us a glimpse into the future, which looks brighter than ever.