If you purchased your Nexus 5 from Google Play in the United States, we've got great news for you. In an unprecedented move, Google has started offering customers the chance to exchange their broken or water-damaged Nexus 5 for a new or refurbished unit—free of charge.
Copy and paste keyboard shortcuts are beautiful gifts from the gods, and any website that blocks such an offering can burn in hell. But really, Cmd+C and Cmd+V (Ctrl+C and Ctrl+V for Windows folks) are second nature to most of us, so it's very frustrating when sites like PayPal don't let us use them.
When browsing the web, you may not be quite as anonymous as you think, especially if you are using public WiFi. The easiest way to stay as anonymous and safe as you are going to get, is to use a VPN (there are a number of great free ones). In this tutorial, we will show you how to set up a VPN on Android, and how this protects you.
In a era where cyber security is becoming increasingly important, Comcast has decided to use its customers' routers to provide hotspot access to the public. A new program, outlined by Dwight Silverman over on the Houston Chronicle website, seeks to provide Xfinity customers with city-wide Wi-Fi hotspots by using, well...other customers' wireless routers.

Unless you've been living under a rock with no internet connection, it's safe to say that you've heard of the Heartbleed flaw that allows practically anyone with the right knowledge to steal your personal information, such as passwords, credit card numbers, and e-mail addresses using OpenSSL.
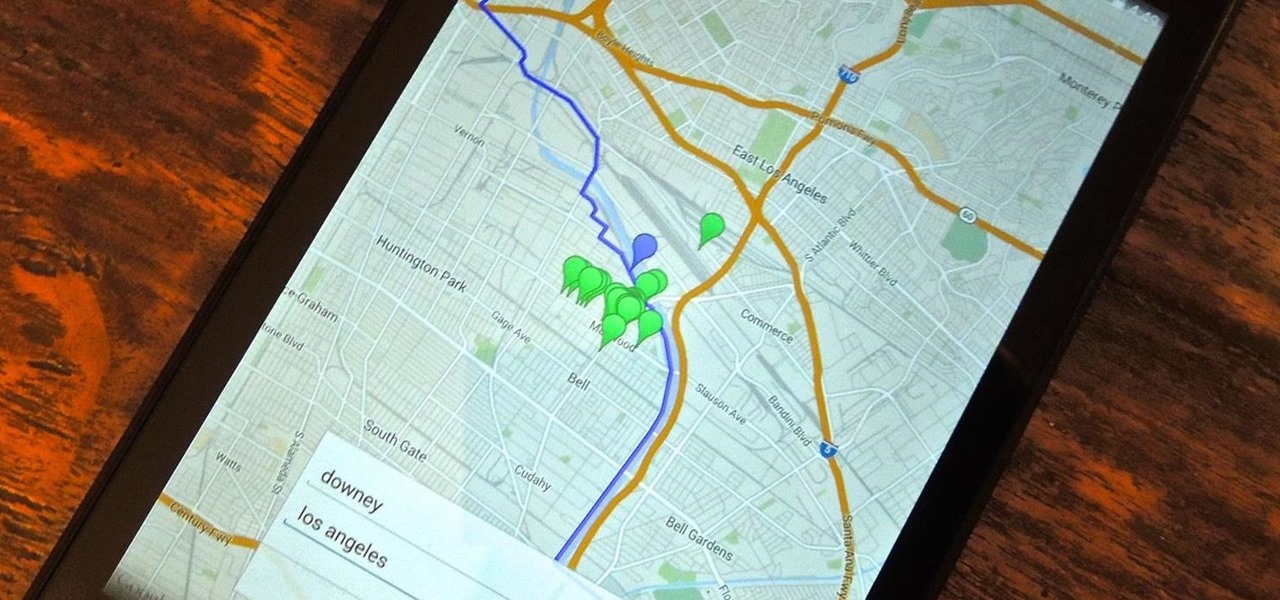
Back in college, there were many instances where I'd have to meet up with a partner that I was randomly paired with in order to work on a project or to study for an exam. Besides the awkward interactions, the most difficult part was always figuring out where we would meet off-campus. I live here and they live there, so what's reasonably halfway?

Welcome back, my novice hackers! There are SOOOO many ways to hack a system or network, which means you need to think creatively in order to be successful.

Privacy features have become quite the hot commodity, emerging from the aftermath of the NSA scandals that rocked the United States this past year. While the NSA has the means to gather information on all of us (regardless of any security software we implement), it doesn't mean that they're the only ones looking.

Apple has released the third beta of its iOS 7.1 software to developers, just a few weeks after their second beta introduced us to button shapes, a new calendar list view toggle, a hidden Car Display control and several other tweaks and performance improvements.

Your Nexus 7 may be a tablet, but it can also be used as a phone, thanks to the continued upswing of VoIP applications, which send voice and media messages over the Internet—not over a cellular network.

Welcome back, my fledgling hackers! There's an evil dictator hellbent on destroying the world, and in one of our last hacks, we successfully compromised his computer and saved the world from nuclear annihilation. Then, we covered our tracks so no one would know what we did, and developed a hack to capture screenshots of his computer periodically so we could track of what he was up to next.

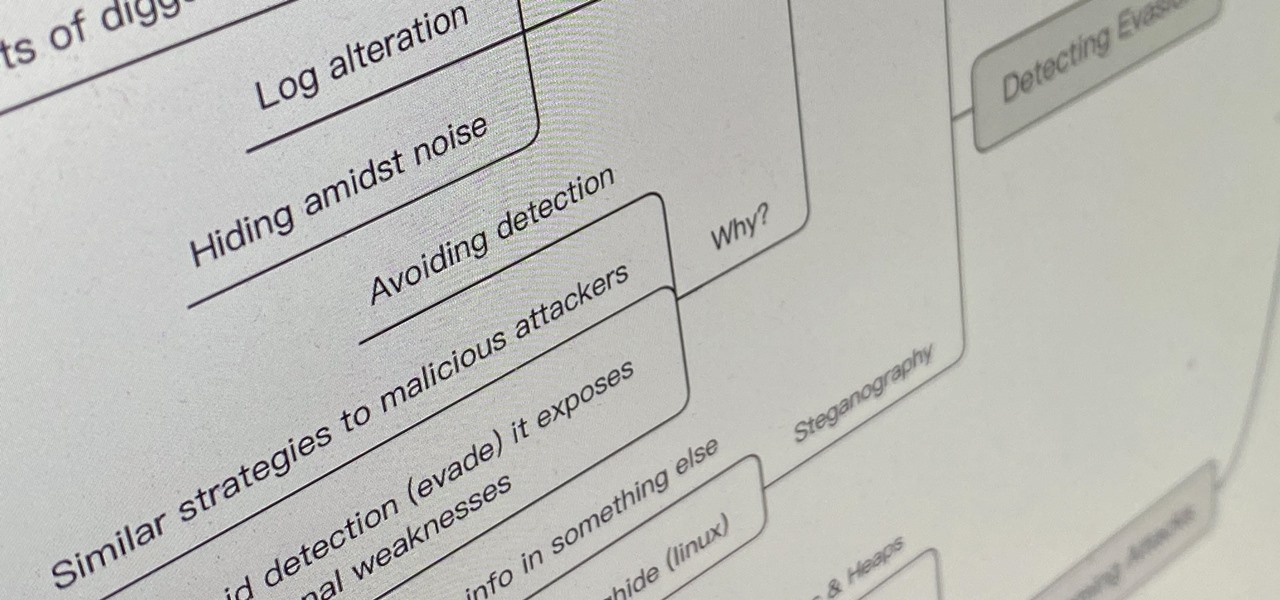
Welcome back, my greenhorn hackers! Congratulations on your successful hack that saved the world from nuclear annihilation from our little, bellicose, Twinkie-eating dictator. The rest of world may not know what you did, but I do. Good job! Now that we hacked into the malevolent dictator's computer and temporarily disabled his nuclear launch capability, we have to think about covering our tracks so that he and his minions can't track our good works back to us.

Unwanted advertising is everywhere. Annoying pop-up ads, overly loud late night commercials, spam...it never ends. And before spam, there was junk mail. Junk mail is even worse because unlike TV commercials and internet ads, it's physical. You can't just delete or ignore it—and it's an awful waste of paper. So what can you do about it?
Your company is deciding on starting new projects but there is a lot you need to do to make sure these projects are right for your company and will be financially rewarding to the bottom line. Before you begin you and your project management team will need to go through a Project Evaluation Process.

Some of my Facebook status updates are absolutely hilarious, and sometimes (though rarely) even my friends updates can get me on the floor laughing. And like most of you, I'm sure, when you come across something funny—you have to share it.

For the most part, keyboard shortcuts are great. They save you some time and make it easier to do everything right from the push of a button. But like most things in life, there is always a caveat, and in this case, for me—it's a huge one.

When you're at work or in class, there's nothing more annoying than sites that automatically play media. One minute you're happily distracting yourself, and the next, you're scrambling to hit pause while everyone stares at you. Not to mention now your boss knows you're slacking off.

As if you needed another reason to lock down your Facebook profile, the company's sketchy new partnership with data mining firm Datalogix is geared towards giving advertisers more information on what you're doing—even when you're not online. It's just not enough that they can target ads based on your preferences, now they want to know how those ads are influencing your buying habits in the real world.
I've noticed that a few people using the crypto-currency, Bitcoin are having issues importing private keys to their Bitcoin wallet. This is easy to do and doesn't require anything other than your Bitcoin client/daemon (as of ver0.6.0 ) and the command line.

There are lots of people who want to stay anonymous online, and lots of reasons they want to do this. Staying anonymous on the internet isn't easy, and it's probably possible to trace almost anyone with enough time and resources. A lot of people think that they're completely secure with just one method of cover. For example, a lot of people thought anyone using the Tor network was nearly untraceable, but then things like this often cast doubt on just how secure these networks are. Unless you ...

Check out this cool hack from The Emo Lab. This video tutorial will show you how to change your IP address in Windows!

How to Hide IP from Hackers. Hide your IP address to get more security. Hotspot Shield (free) change your IP address and your location. To see the changes visit http://www.ip-adress.com/ before and after running program.

This video demonstrates how to hid your IP address on a PC.

This instructional video series is on how to build any type of 2/5th (40%) scale, fully functional tank. The specific model demonstrated is the M60 Patton. An MBT. A destructive force. If you have any questions about your backyard tank build, please address them to "Dave's Tank Foundry" at Scaled Tanks.

Check out this informative video tutorial from Apple on how to organize your Mail in Mac OS X's Mail. See how to sort messages with rules, create smart mailboxes, and comlpletely organize your mail. Mac OS X. It's what makes a Mac a Mac.

Check out this informative video tutorial from Apple on how to use the basics of Mac OS X Mail. See how to set up mail with your email accounts, compose messages, add attachments, view attachments with Quick Look, and search through Mail. Mac OS X. It's what makes a Mac a Mac.

Check out this informative video tutorial from Apple on how to use Mac OS X Mail to its fullest. See how to filter out junk mail, use data detectors, and view RSS feeds in Mail. Mac OS X. It's what makes a Mac a Mac.

Jordon Schranz brings you this tutorial on drawing. Search WonderHowTo for Sessions Online School of Fine Arts for more drawing tutorials. The technique & craft of drawing isn't necessarily about inherent talent, it is something that comes with lots of practice. It is all about being able to accurately record what you see.

How to track an email address. Useful if you meet someone who says they are from somewhere e.g. LA as given in the video and you don't believe them. Go to the Rate a Bull site type in their email address and then hit return or 'find them'. The site will give you options to see information about them on the internet, MySpace, Facebook or other site or track the email. The site gives instructions on how to track the email via outlook, outlook express and other mail programs and the video shows ...

In this how-to video, you will learn how to find the IP address you are using on your computer without using any third party sites. First, go to the start menu and click run. If you are using Vista, go to search in order to the run the file. Next, you should type in cmd.exe into the prompt. A window should now open up. In this window, type in ipconfig /all. From there, your IP address should be listed. This simple video shows you a very easy way to find your IP address without having to use a...

Before there was Gray's Anatomy, physicians and medical students used anatomical flap books to explore the inner workings of the human body—a scientific illustrated guide that takes its name from the moveable paper flaps that can be "dissected" to reveal hidden anatomy underneath. Similar to pop-up books, these instructional tools mimic the act of human dissection, allowing doctors and students to study the intricacies of the body normally concealed by flesh.

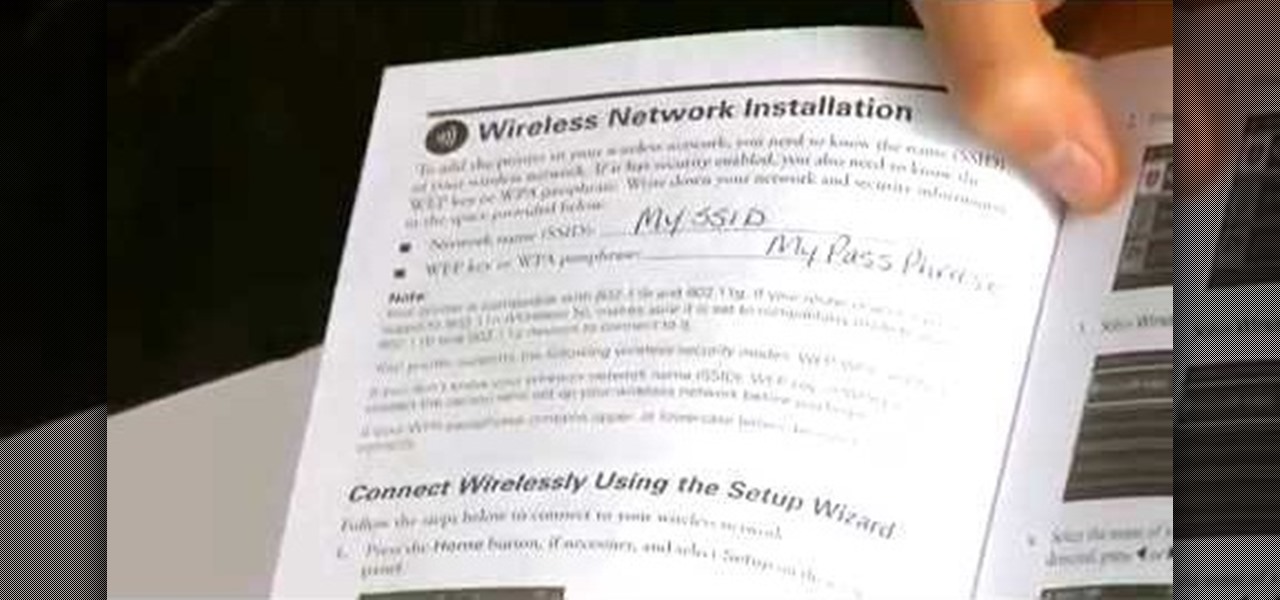
Learn how to set up an Epson printer wirelessly when you bring your new printer home you will want to start by installing the software that came with the new printer. You can set up your printer to work without wires and it will print from all over the house. There are 3 ways to set up the printer including the Epson way, with cables, and WPS. To determine is you need to use WPS, which is more complex, check your router to see if it has a sticker on it that says Wi-Fi Protected Setup. If that...

When we think of the flu, we think of sick people, but the little guys always get looked over… dogs. Learn how to care for your pet with help from VetVid. See how to diagnose and treat canine influenza (CIV) in dogs with this video tutorial.

Studio one single window interface now eliminates multiple windows and complex menus enabling to focus on music in an easy way. The important music creation and production tools are instantly accessible. Studio one directly opens into the start page by default. Here we can find the recent files that enable to easily choose the ongoing productions. The default page also helps to open tutorials and demo songs. We can create songs on the song page using hot keys to access various panels. For exa...

Glass shelves add a elegant beauty to your home, but imagine how much more elegant and sleek they would look if they were simply floating against the wall. Floating glass shelves are the innovative way to create stylish wall arrangements.

Homemade biscuits are great. But coupled with homemade gravy, they’re irresistible! Follow this Howcast recipe guide to learn how to make country style gravy.

Foil fencing is a complex fencing sport that utilizes the properties of a foil blade; learn the rules of foil fencing, including terms, fouls, the piste, and more in this free video fencing lesson.

More and more tech-savvy leaders are flocking to the lucrative and exciting world of project management thanks to the high-pay, analytical environment, and nearly unparalleled flexibility. But this means that competition for the best positions in this dynamic field is fierce. If you want to stand out from the crowd, you're going to need to have more than a few base-level certifications on your résumé.

If you're reading this, you're likely a tech-savvy coding pro whose analytical talents are mostly applied to designing apps, cracking passwords, and infiltrating networks — all of which are admirable activities for both aspiring and seasoned white hat hackers. But there are other profitable ways that you can put these types of skills to use, namely in the world of investment and trading.

Whether you're coding a simple app, trying to learn a new programming language, or building an entirely new operating system from scratch, being able to quickly and clearly organize your thoughts is absolutely paramount — even as an ethical hacker or penetration tester.