Google has done it again—they've pushed another broken OTA update for the Nexus 6. Except this time, it almost completely softbricks your Nexus 6 instead of just screwing up Android Pay and SafetyNet. Apps are force-stopping left and right, making the phone practically unusable.

The only way to know which Pokémon are in your area in Pokémon GO is the cryptic "nearby" list, which sometimes doesn't work—and also doesn't tell you which direction to head off to hunt that Pokémon you're looking for.

It's hard to argue with the notion that wine and pasta are a winning combination. I mean, millions of Italians can't be wrong.

Move over rainbow food trends, there's a new, darker kid in town: jet black ice cream. And no, it doesn't have squid ink in it.

Google seems to be growing tired of the way links appear in its Search results page, because they're currently experimenting with a color change (that's already causing lots of controversy).

When a craving for crunchy tacos hits, it's undeniable. Don't Miss:

You may have caught our prior list of excellent egg hacks. Well, we've rounded up 10 more awesome tips and tricks to perfect your egg game. Check 'em out below.

Mashed potatoes are a reliably tasty side dish, but they can definitely get a little boring sometimes. So if you're looking for that extra 'oomph' that goes beyond the classic butter and salt seasoning, try infusing your next batch with the flavor of baked potato skins.

Hey guys I am starting this Series because I thought there was a lack of post about Hacking from Android.

Hello again, folks! I'm back with another (final) guide on runtime crypters which is an extension on my previous runtime crypter guide. If you have not read it yet, I highly recommend that you do since the fundamental theory of the PE format. Again, this will be a Windows-specific guide, so I'll repeat this: If you're a hater and cringe at the slightest sound of Microsoft's grotesque baby, feel free to close this tab, delete your history, exit your browser, pour some oil onto your machine and...

continuing this series, I will now go in-depth on using advanced search queries. What Is Search Queries Again?

No crème brûlée is worth its custard without the crackled, caramelized crust it's famous for. For this reason alone, many cooks have a brûlée torch sitting somewhere in their cabinets.

If you read my previous post, "How to Hack into a Mac Without the Password", you know that it is very easy to break into someone's Mac if you have physical access to the computer. Now the question that lies is, how do we protect ourselves from this happening to us? Well, here is a way that guarantees that no one will be able to change your password through OS X Recovery.

Chicken breasts have gotten a bad rap. Dry, flavorless, boring... poor white meat gets no love, and dark meat gets all of the credit for being sinfully flavorful and delicious. But the truth is, even though chicken breasts are lower in fat and calories, they can also be incredibly versatile and full of flavor... if they're prepared correctly. You're probably familiar with poaching, which is a technique that gently cooks more delicate meats such as chicken or fish fully submerged in a liquid b...

Welcome back, my amateur hackers! With Halloween right around the corner, I thought you could have a little fun with your newfound hacking skills using a hack that is guaranteed to freak out your boss, teacher, coworker, friend, etc.

Butter is one of the most versatile ingredients in the world: its variety of uses range from brightening a morning piece of toast to finishing a beautiful rib-eye steak with decadent flair.

Sushirrito offers burrito-sized sushi rolls that are on the cusp of becoming the trendiest handheld snack to hit the foodie world. According to its website, Peter Yen created the Sushirrito brand, trademarked it in 2008, and opened his first restaurant in 2011 in the Bay Area with Ty Mahler, executive chef.

Like most food lovers, I adore sushi. And like anyone who is a living, breathing human being, I'm a pretty big fan of sriracha sauce.

I'm human, so it goes without saying that I love bacon. You're human too, which means chances are pretty good that you also love bacon. Yet as beloved as bacon has always been, it's just now experiencing a culinary renaissance, which I love. Bacon chocolate? Heck yes. Bacon donuts? Bring it on. Bacon booze? Now we're talking.

If you've got a desktop computer, I can almost guarantee that you've got a widescreen monitor set up in landscape mode. It's how just about everyone uses their monitor these days, including myself. Except that it's not always the best way of working.

Cooking rice, pasta, and other grains in water is so boring. There is a much better way to guarantee they will have your mouth chewing something seriously tasty: cook them in something that isn't water. Alternative liquids such as stock, milk, juice, or even tea will give bland dishes a fresh new flavor boost. If you're not sure how your dishes might taste, never fear: we tested them out. Before getting started, be sure to read this article first so that you know why it's important to rinse y...

Erudite. Barbiturate. Cacophony. Denouement. Okay, that last word is technically French, but words like these make the average person sweat, and it turns out that the key to learning how to pronounce them once and for all just might be getting them wrong.

Welcome back, my greenhorn hackers! Although we have focused primarily on technical hacks here, social engineering can sometimes be especially effective. This one requires a bit of technical skill, but not too much. In addition, it's limited by how specific a target you can choose—but it will work.

Some food jars seem like they're actually designed to prevent you from enjoying every last bit inside. The remnants of sticky foods like Nutella and peanut butter are almost impossible to scrape out with a knife or spoon, and it's a shame to throw out something that tastes so good—especially when it's the best part. A spatula could help you get that last drop out from the walls or bottom easier, but that's just ruining your chance at maximizing the full potential of those remains into somethi...

Amazon.com has been around for a long time now, but there are still a few things most people don't know about when it comes to buying products from them. Here's a quick roundup of tips to help you get the most out of Amazon and save some money in the process. The holidays are the busiest time of year for online shopping, but these tricks will work all year around.

"What is dead may never die." That's easily one of the best lines (and episode title) from HBO's Game of Thrones series. While the saying may ring true for the Ironborn, it's not quite as catchy when it comes to batteries.

One of the best things I love most about any new gaming console are the apps—I can switch from playing Assassin's Creed III to re-watching the fifth season of Breaking Bad on Netflix without ever getting off the couch. Beat that Atari.

Many people that I know who have gone to see the Hobbit have come back unimpressed or annoyed with the film. I LOVED it. When those non-specific people, cough Loziers cough, gave me their reasons for not liking the movie, I was very annoyed... I considered the demands that they were placing on Peter Jackson and his team to be very high and unreasonable. So, as a method of venting my anger, here is how to watch the Hobbit. If you’ve read Lord of the Rings and the Hobbit, please, go back, and R...

The Geminid meteor shower happens every December and has been observed for over 500 years. It's is also known as Winter's Fireworks because when viewed from the right location, there are enough meteors to light up the whole night sky, and some of them can even be different colors. The shower appears to come from the Gemini constellation, but is actually caused by Earth passing through the tail of dust and debris left behind by the comet 3200 Phaethon.

There's really nothing safe about transmitting sensitive information electronically, but even if it gets there safely without being seen by prying eyes, there's no guarantee what happens to it once it reaches its destination. And let's face it, there are some things that you just don't want floating out there forever. So what can you do? Whether you want to send an email, a text, or a link, there are ways to send messages that self-destruct so that once they're read, they immediately vanish. ...

Apple's iTunes Match service is a great feature for people who have large libraries or want to sync their music across a lot of different devices. It lets you store any song in your library that exists in the iTunes Store on the cloud, even songs you imported from CDs, and even improves the quality of some of them. But, like any new service, it's not without its problems, and the fact that it costs $25 a year makes those problems seem even worse. Among the issues that users reported, unmatche...

It can be extremely frustrating when you've forgotten the pattern you use to lock your smartphone, and even more so if someone has managed to prank you by changing it. Luckily, there's an easy fix if you know the username and password for the Gmail account you used to set up the lock.

The cost of movie tickets in North America are currently at an all-time high, but with so many great films coming out, just not going doesn't seem like a probable option. Luckily, there's more than a few resources on the Internet to help you mitigate some of those costs.

With the upcycling revolution, folks are turning their otherwise useless junk into something functional for the home. Practically anything that you would normally toss or recycle can be reused for a bigger and better purpose. Your milk jugs, chopsticks, toilet paper cardboard, glass jars, and even your old junk computer keyboards can be upcycled into something totally useful around (or away from) the home.

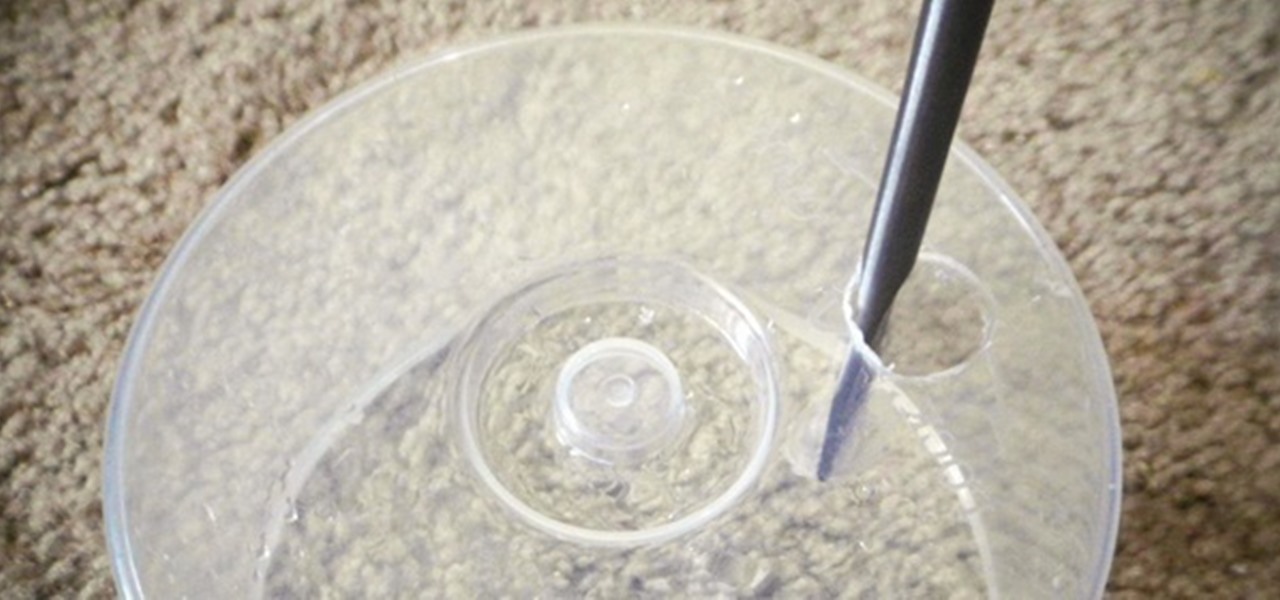
Google's Nexus 7 tablet has just been released, and for only $199, it seems like a great deal. Now, some of you are probably immediately thinking that you're going to want to root this thing as soon as possible to install all of your tweaks. Luckily, some clever hackers have already developed a fairly automated solution to rooting the device. Here's how it works. A word of caution however, rooting your tablet will very much void the warranty and there's no 100% guarantee that this procedure w...

Hello! This post is not about craft, it's about cyber bullying. If you ever had such an experience, that an unknown hacker was bullying you for no reason at all, please follow my words. Thank you! Step 1: Let All the People You Know That Your Are Being Harassed.

Brushing your teeth is a necessity. You don't want to walk around with yellow teeth and stinky breath, and it's common courtesy to those around you to care about your personal hygiene at least that much.

It's easy to have your password stolen. Important people like executives, government workers, journalists, and activists face sophisticated phishing attacks to compromise their online accounts, often targeting Google account credentials. To reduce this risk, Google created the Advanced Protection Program, which uses U2F security keys to control account access and make stolen passwords worthless.

Summer is coming so start saving your popsicle sticks (or more conveniently buy them from a craft store) to make your very own mini American flag. This is a great activity to take into the class room or just to pass the time on a summer’s afternoon.