Those of us who are actively developing for the HoloLens, and for the other augmented and mixed reality devices and platforms that currently exist, are constantly looking for the next bit of news or press conference about the space. Our one hope is to find any information about the road ahead, to know that the hours we spend slaving away above our keyboards, with the weight of a head-mounted display on our neck, will lead to something as amazing as we picture it.

We can add one more health effect of our gut bacteria to the growing list. Researchers from the UK have just reported that the gut microbiota plays a role, both directly and indirectly, on the toxicity and efficacy of chemotherapy. Their findings are published online in the journal Nature Reviews Gastroenterology & Hepatology.

It feels like someone reached into your chest and squeezed. Your head throbs in unison with your heartbeat. Clammy dread coats your body in sweat. Whether you call 911 or someone does it for you, the ER is your next stop.

Not only has there been difficulty finding consensus on a name for driverless, autonomous, self-driving, or automated vehicles, there is also the issue of what we actually mean when we say a vehicle is self-driving, automated, and so on.

Hear me out. No, really. Before you sharpen your pitchforks and give me anecdotal evidence of your Chinese restaurant syndrome, I think you need to know a few things about monosodium glutamate. First of all, it's a naturally-occurring chemical compound that can be found in anything from tomatoes to cheese, and is used in all kinds of foods from KFC to breakfast sandwiches. So spare me the comments on MSG and Chinese food—you probably eat MSG on a daily basis without even knowing it. (And also...

En papillote may sound like a difficult French cooking method you'd never use at home, but don't be fooled by its fancy name—it's actually a really easy way to cook food that is moist and flavorful, and all you need is some parchment paper and your oven.

Both the Galaxy S6 and S6 Edge have had root methods available to them before the phones were even released, but the problem with these existing root methods is that they would trip the KNOX counter on your device.

Making a good crêpe takes practice and commitment. The batter is rich—most recipes incorporate melted butter, whole milk, and several eggs—and the cooking of the crêpe requires good technique. You have to learn to deposit and swirl just the right amount of batter to get the thinnest possible crêpe, and then learn how to loosen the entire circle and flip it over without tearing or snagging.

Whether it's the start, middle, or end of summer, it's prime-time grilling season. If you find yourself without a grill, however, it may seem as if half your summer plans of swimming by the pool while stuffing hot dogs in your face could be ruined.

Welcome back, my aspiring hackers! As I mentioned in earlier posts, the best hackers (or at least those not behind bars) have a keen understanding of digital forensics. If I am tasked to intrude upon an enemy's file server to retrieve war plans, such as in this tutorial, it is essential to my country's (and my own) well-being that it not be traced back to me. Understanding digital forensics helps us to leave without a trace and never have a trail back to us or our employer.

Welcome back, my tenderfoot hackers! A short while ago, I started a new series called "How to Spy on Anyone." The idea behind this series is that computer hacking is increasingly being used in espionage and cyber warfare, as well as by private detectives and law enforcement to solve cases. I am trying to demonstrate, in this series, ways that hacking is being used in these professions. For those of you who are training for those careers, I dedicate this series.

It is a truth universally acknowledged that food molded into fancy shapes somehow seems tastier. That's true even with chocolate, which is inherently delicious. Now, while you can buy chocolate that's been pre-molded into fancy shapes, you can have a lot of fun and save a few bucks by making your own specialty chocolate molds. All you need to get started are items you most likely already own.

French fries, like mashed or roast potatoes, are the type O blood of the food world—they're compatible with just about everybody. That's why it's so sad to bring home leftover frites (that's French for French fries) and have to toss them out the next day because they don't taste as good when they're reheated. Warning: Do Not Ever, Ever Use Your Microwave

Learn how to be a good host. Party-planning can be tricky, but you don't have to be Martha Stewart to be a good host.

Learn how to play "Year 3000" by Jonas Brothers, an acoustic guitar tutorial. Follow along with this demonstration, tabs and lyrics here:

Whether you're planning the best Halloween bash on the block, creating a haunted house ride, or just want to scare the living daylights out of your neighbors, this Halloween corpse will be the death of the party. Watch and see how to make one yourself in this series.

Deer can wreck havoc on your plants and yard. No need to go to war with the deer, when with a few tricks of the trade, deer can be discouraged from feeding on your yard. The neighbor‘s yard, on the other hand, might seem that much more appealing.

In this series of spooky videos about how to scare the heck out of your friends and neighbors, our haunted house expert tells you everything you need to know about setting up your own haunted house. Matt Cail, designer and director of the University of Washington's campus haunted house, shares the tips and advice he gained from putting the fright to university students. He begins by discussing goals for a haunted house then tells you how to achieve them with the seasoned advice of someone who...

As first reported by Next Reality last year, game developer Preloaded, in partnership with BBC Studios, has finally launched BBC Earth - Micro Kingdoms: Senses.

A recently confirmed polio outbreak in Syria is connected to low levels of vaccination, worsened by conflict. It is the first confirmed incidence of polio in Syria since 2014. Before 2013, the last case of polio in Syria was in 1999.

Oh, Uber. It's not often to hear your name in the news and have it mean something good. You're being sued, you're crashing, your driverless program is falling behind. But I have to hand it to you; when the world is crumbling around you, you continue to fight against it. You've even made it to Canada.

Damn right, you don't just eat 'em. When you're done with your next Pringles can, you can turn it into a kaleidoscope, a pinhole camera, and even a solar hot dog cooker. But Instructables user TheSpodShed may have just created the most awesome way to upcycle empty Pringles cans—use them as a mini MIDI drum kit for your mobile device. This tiny drum kit will let you rock your face off without pissing off all your neighbors.

In previous posts here, I have pointed out that hackers are in high demand around the world and in nearly every industry. Every military and espionage unit of every country is trying to hire high-quality, experienced hackers as fast as they can to hack their adversaries' computer systems in order to gain a strategic advantage and to spy.

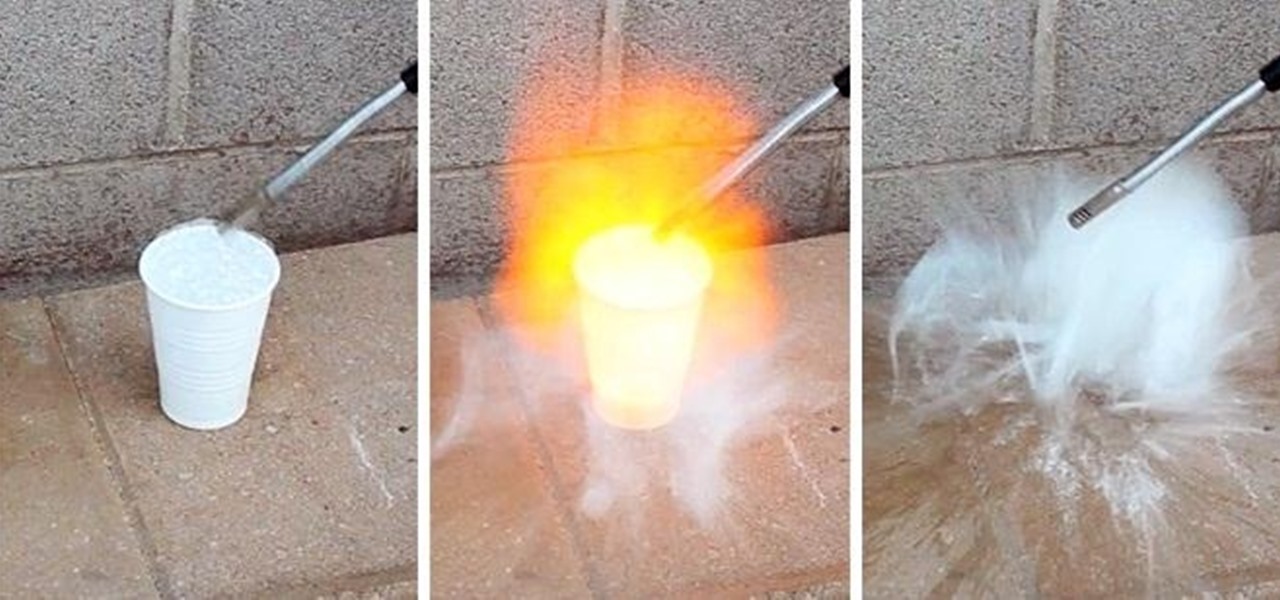
Maybe not water per-se, but with this simple technique you can turn one of the most abundant materials on earth into a highly explosive gas.

Android has released a new application called ezNetScan, which is a free app that scans the wireless network you're connected to and gives you a full log of all of the devices connected to that network. This isn't new for smartphone users, let alone Android users. Fing has been around for a while and does practically the same thing that exNetScan does. It gathers information such as the IP and MAC addresses, device vendors, and ISP location. But while Fing is a great program, it does lack a f...

Moles can be a real problem in gardens. Unfortunately, there is no easy answer to get rid of them. The best way is to try several methods until you find one that works. Even then if you manage to catch or deter a mole it's not always the end of the problem. For much of the year moles are solitary, and have their own territory. If you catch the little fellow, his neighbor will take advantage of the tunnel system and move in. This how to video give you some ideas of how to get rid of those pest...

Welcome back, my rookie hackers! Now that nearly everyone and everyplace has a computer, you can use those remote computers for some good old "cloak and dagger" spying. No longer is spying something that only the CIA, NSA, KGB, and other intelligence agencies can do—you can learn to spy, too.

People who know that I am a professional hacker often ask me what they can do to make their computers and personal information safe from people like me. The answer, of course, is that nothing will make you completely safe, but there are a number of measures any computer user can take to reduce the chances of being a victim of a hacker.

At one point in the '90s, about fifty percent of the CDs produced worldwide had an AOL logo. About fifty percent of the CDs in my home still have that AOL promise of 500 free hours on them. Though they never got me to join their internet service, I did get a lifetime supply of coasters. Thanks to the rise of high-speed internet access and bigger and better hard drives, there's no reason for companies to snail mail any more of those obnoxious plastic discs.

The Los Angeles Rams are the latest NFL franchise to introduce new or modified uniforms for the 2020 season, joining the Atlanta Falcons, Cleveland Browns, Indianapolis Colts, New England Patriots, Tampa Bay Buccaneers, and their neighbors, the Los Angeles Chargers.

With an ordinary birthday card, we can introduce a physical device which contains malicious files into someone's home and deceive them into inserting the device into a computer.

Have you ever wanted the perfect radio station for an artist, genre, or even one to match your mood? Luckily, Google Play Music has an extensive radio feature that takes you exactly where you and your friends want to go for a quiet brunch, or a neighbors-banging-on-the-walls dance party.

The promotional images for American Horror Story: Cult have been some of the most arresting in recent memory. They mash coulrophobia, trypophobia, and body horror together with some serious economy into a succinct, colorful, image. It's like a bad car accident that you can't stop rubbernecking. Which makes it perfect for a Halloween costume — you'll be repulsive, but no one will be able to look away. While the beehive skull hasn't made an actual appearance in Cult yet, and probably won't sinc...

There's now more reasons to make sick workers stay home—a new game theory study suggests adequate hand washing and other illness-aversion tactics aren't as useful as we thought to keep you from getting infected when a virus or bacteria is circulating.

Rabbits have been a persistent problem in Australia for over 150 years. Now the Peel Harvey Catchment Council (PHCC) and Peel-Harvey Biosecurity Group have released a strain of the rabbit haemorrhagic disease virus (RHDV), called RHDV1 K5, to reduce the number of pests in the Murray region of New South Wales.

Let's say you gave your Wi-Fi password to your neighbor a while back, under the assumption that they'd only use it while they were at your house sharing stuff via Chromecast. But now, your connection is slower than it normally should be, and you have this sneaking suspicion that the dude in apartment 3C is flat-out piggybacking off of your home network.

Forget headphone jacks and "Courage." Look past the shiny Jet Black finish and beyond the minimized antenna lines. Sure, quad-LED flash and dual cameras are nice—but dual-SIM would've been much better.

Here I will show you how to properly dig information on the web that has already been published, you just dont know it.

Those of you who have been a part of the Null Byte community for even a short while know that I sincerely and firmly believe that hacking is the most important skill set of the future.

Food waste is a topic near and dear to my heart, but the truth is, no matter how dutiful we are about finding ways to double-down on food scraps, a lot of stuff goes into the trash needlessly.