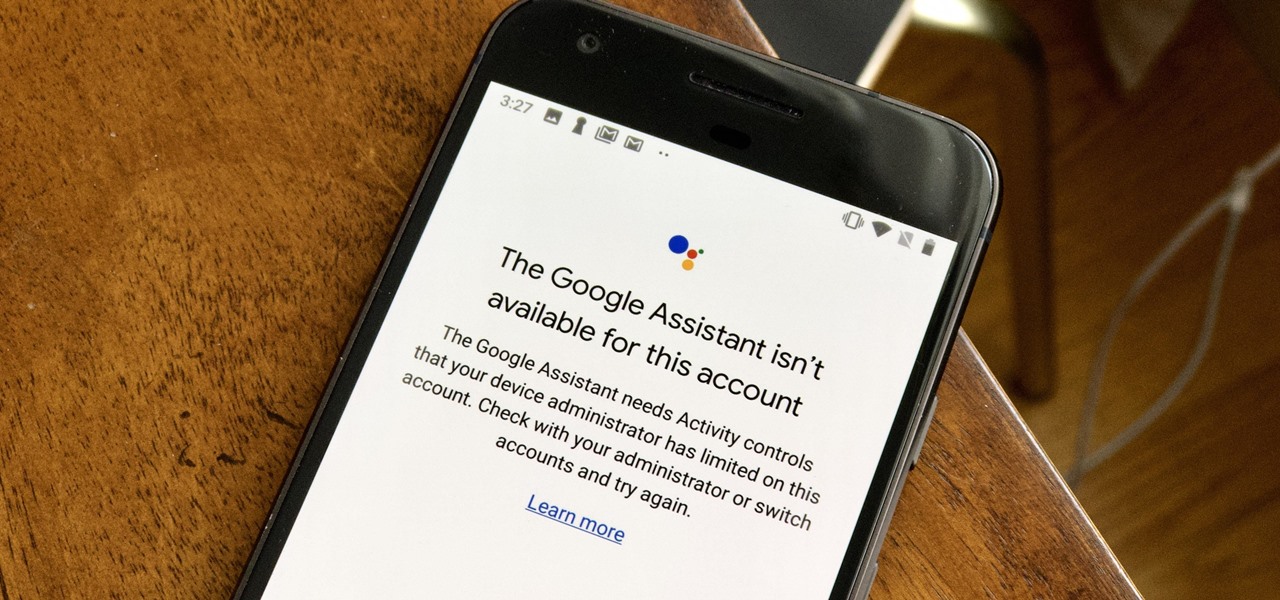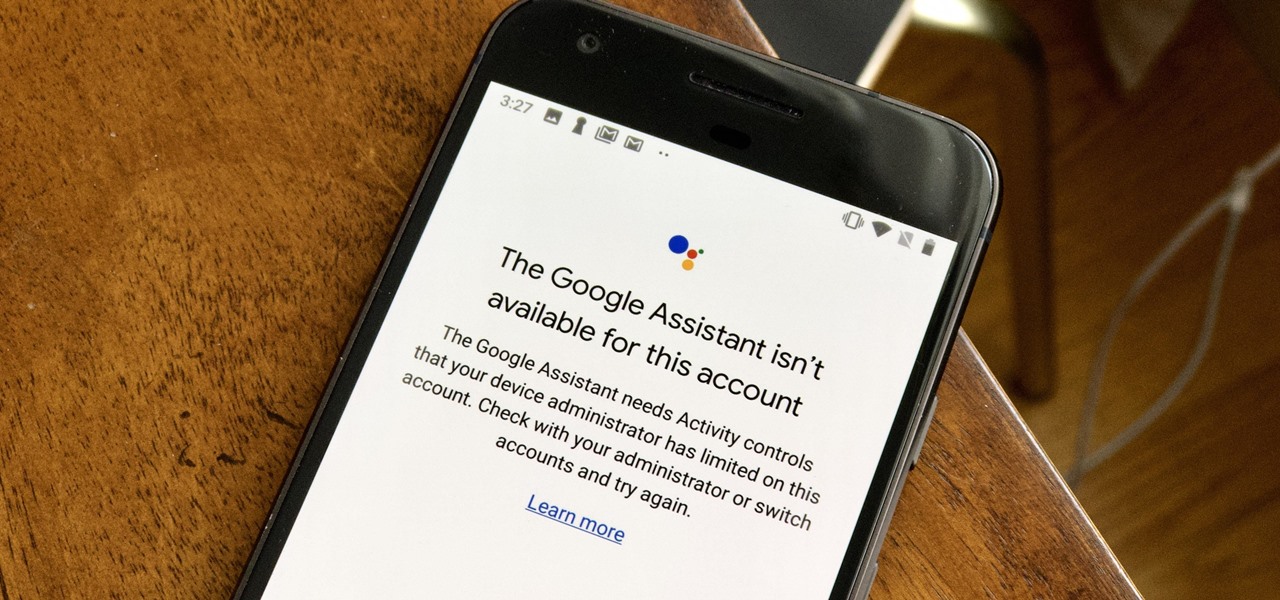
If your virtual assistant can't assist you, what's the point? Anyone who has ever failed to activate Google Assistant knows the frustration that error screen can be. But there are solutions for this problem — "The Google Assistant isn't available for this account" is one message you can actually avoid.

So it's 2017 and there are no flying cars and teleportation devices around, but there might be holographic smartphones sometime soon. As cool as that sounds, should we trust a holographic smartphone from a company that has never made smartphones before?

The driverless competition is heating up as Detroit automakers attempt to woo tech talent away from some of Silicon Valley's biggest players.
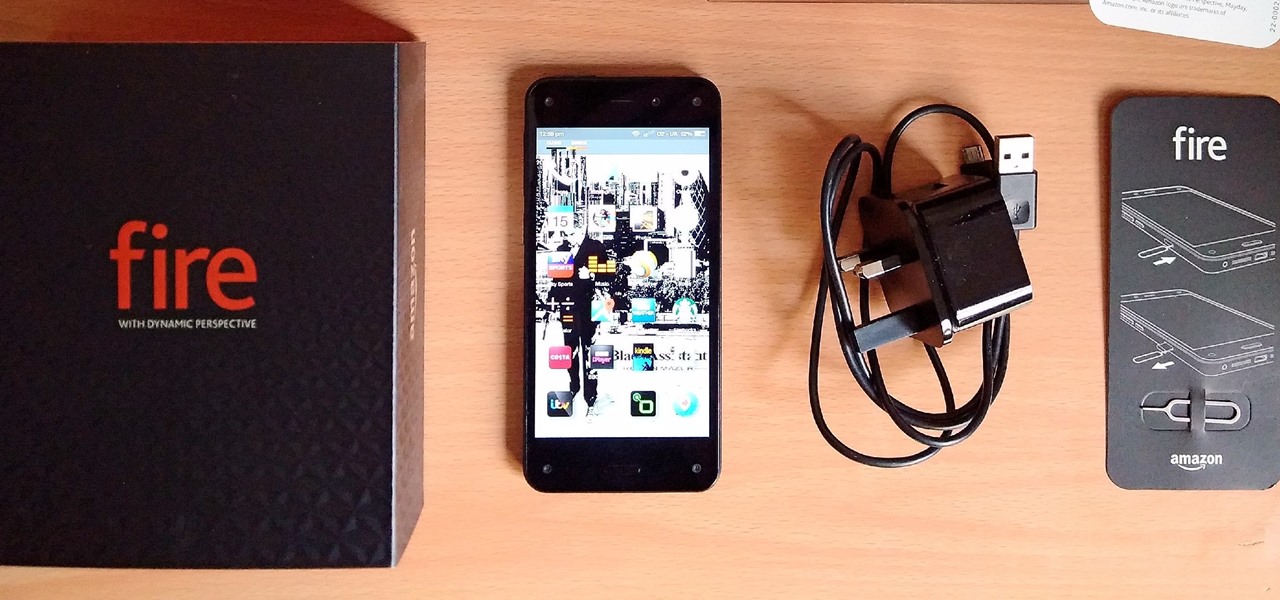
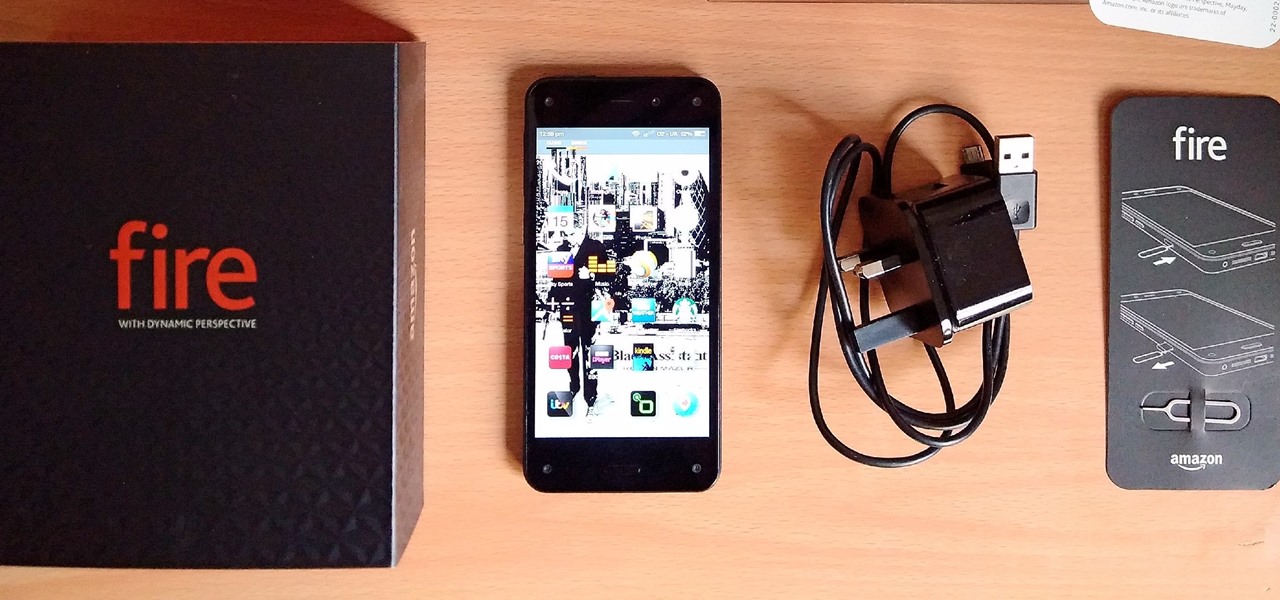
Amazon's first venture into the wireless phone market was a crash and burn moment — and that's us being kind. Their FirePhone went down in flames almost instantly, no pun intended.

Chinese search engine giant, Baidu, has just announced its own autonomous car platform which is intended to speed up the development of driverless vehicles.

Smartphone users often wish for a privacy, where no one is able to poke his/her nose in their personal stuff. Unfortunately, none of the smartphones have been able to guard their privacy in this fashion. Smartphones usually come up with none or almost negligible built-in security to serve your purpose.

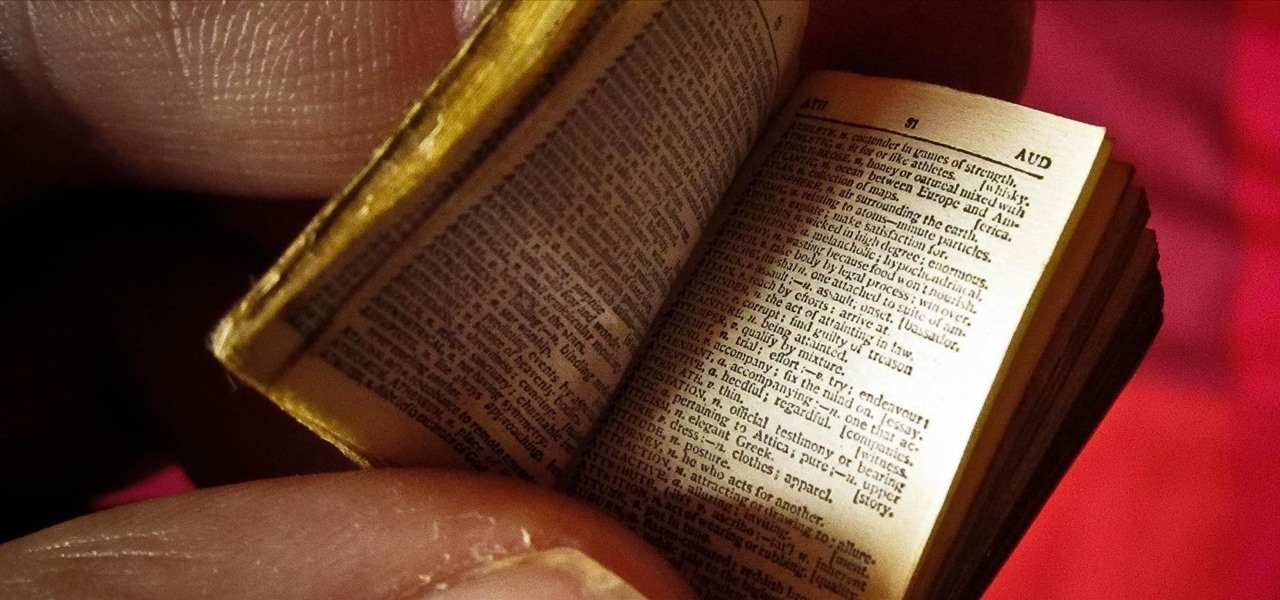
We've all been there: facing a lengthy, complex word that ignores the phonics we were taught in elementary school, unsure of not only its pronunciation, but also its meaning. These words, from autochthonous to esquamulose, are both terrifying and impressive. After all, if someone knows how to use them—and even say them—they must be quite smart. Yet before you begin stuffing every email and presentation with verbose prose, you might want to reconsider what others perceive to be intelligent.

Welcome back, my fledgling hackers! In an earlier tutorial, I introduced you to probably the most popular scripting language for hackers, Python. To become a professional hacker, you need to have some scripting skills and Python is a good choice if you want to master just one. In this latest guide, I will expand your background in Python and offer you a tidbit of Python code to whet your appetite for all of the hacking to come.

With so much Flash content still available on the web, it's unfortunate that Google no longer supports mobile Flash Player on Android. Loading a webpage only to be met with a "Plug-in Error" is never fun, and it can inhibit your mobile browsing experience as you attempt to watch a video or play an addicting Flash game.

Welcome back, my apprentice hackers! In this series on password cracking, I have been attempting to develop your skills in the age-old art of password cracking. Although it might seem like a simple and straightforward exercise, those of you who have attempted password cracking know that there are many subtleties to this art.

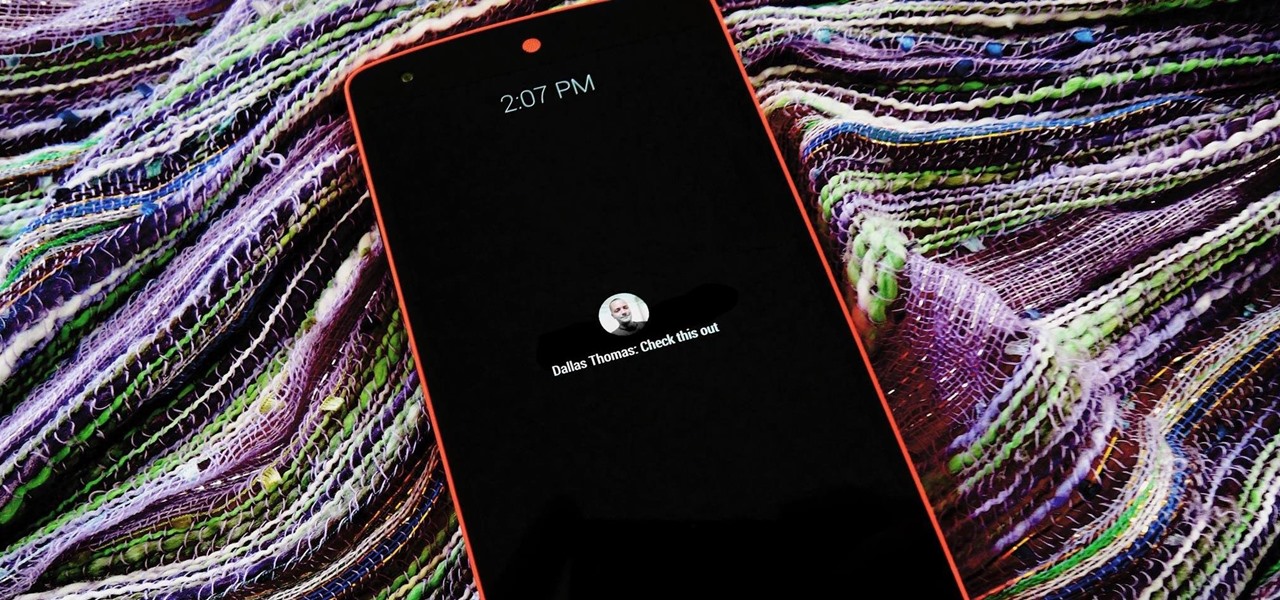
The act of viewing a new notification on your Nexus 5 can feel a bit clunky and cumbersome at times. When a new message comes in, you hear the notification sound, you see the LED blinking, but you can't see what the actual notification says without waking the device and opening the notification tray.

There is no shortage of games for your iPhone, and I'm sure you and your friends are probably sick to death of playing Candy Crush Saga by now. To spice things up, instead of waiting for cool new addicting games to come out, take control and make your own, then share them with your friends.

It's time to trip out with your tablet. If you're not looking to drain that precious battery life with a fancy-looking live wallpaper, then apply an optical illusion that appears to be moving on your Nexus 7 (or any other Android device) instead.

Welcome back, my hacker wannabees! Most of my recent posts have addressed using Metasploit’s Meterpreter and what we can do once we have embedded it on the victim’s system. This includes remotely installing a keylogger, enabling the webcam, enabling the microphone and recording, disabling the antivirus software, among many other things. The list is almost unlimited.

The final chapter of Christopher Nolan's Batman trilogy is here, The Dark Knight Rises, and if you're anything like me, it made you want to immediately don a cowl of your own and run around punching criminals. Don't forget though, one of the most awesome aspects of Batman is his never-ending supply of crazy gadgets. Unfortunately for most of us, we don't have a billion dollars, nor Morgan Freeman, so we'll just have to make do with some good old-fashioned DIY tricks. Read on for a rundown of ...

Facebook is an awesome free online resource that is connected to billions of people around the world. These days, you won't meet many people who do not have a Facebook account. As a real estate agent, you can take advantage of social networking to promote your business and share your listings. By posting on Facebook and creating a page for your business, you gain free advertising to thousands of local buyers. Check out this tutorial and learn how to start uploading videos to Facebook to promo...

This video demonstrates how to install memory step by step in a Mac mini (2009), as it is a complicated method; it is advisable to watch through the process then attempt to do the same. First step is to remove the old memory from the Mac Mini. Shut down and unplug the Mac mini and place it on a soft cloth to prevent any scratch. Turn-over the mini to get into it using a small buddy knife. Carefully place the buddy knife between the inner and the outer case. Try to detach the inner clips using...

This is how my version of an origami Christmas tree turned out based on the instructions I posted awhile back. Cory also made a version from white glossy paper, which looks great. I opted for the green and brown look, but it wasn't easy.

Cell phones companies are constantly claiming to have the best service in town; but more often than not your service will be patchy. Check out this tutorial for information on how to boost your phone's signal and get the best reception.

Pilates is fantastic exercise. If you are a beginner, though, it can be confusing to choose the right type of class. Check out this tutorial before you head to the studio and ensure you get the most out of your exercise routine.

If you've ever had bloating you know this can be an uncomfortable and even painful situation. You can alleviate bloating by preventing gas or taking measures to try to reduce gas. Food, exercise and stress can all effect bloating.

It's getting harder and harder to escape ad tracking by the day. For the latest example, look no further than T-Mobile. The No. 2 carrier updated its privacy policy on Feb. 23, 2021, indicating that it would start sharing customer data with advertisers under the guise of more relevant ads starting April 26. If that's not something you'd like to participate in, there's a way to opt-out.

The increasingly important world of white hat or "ethical" hacking is getting competitive. Thanks to growing salaries and opportunities for talented and trained coding pros who can infiltrate servers and safeguard networks against digital threats, demand for intrepid cyber warriors is through the roof, and it shows no signs of slowing down any time soon.

HBO Max is finally here, all while unlimited cellular data plans have never been more available. The two seem like a perfect pair, but you might find that you can't binge "Friends" or "Westworld" on the go. At least, not without downloading episodes beforehand. Fortunately, there's an easy way to fix that.

When you press the Home button on your iPhone SE, you're not quitting your current app. Instead, it stays open in the background. If an app ever bugs out on you or you don't want it to run in the background, you'll need to force-close to quit it completely. Doing so is also helpful when your app switcher gets too cluttered, and you find it hard to switch between apps because of it.

Compromised uTorrent clients can be abused to download a malicious torrent file. The malicious file is designed to embed a persistent backdoor and execute when Windows 10 reboots, granting the attacker remote access to the operating system at will.

Whether you loved or hated the blockbuster hit Joker for its slapdash violence and unflattering portrayal of mental illness, if you have been online lately, you know you can't afford to miss it.

Burst mode on iPhone is a great way to ensure you capture the photo you truly want, especially when your subject is moving too fast. You'd be forgiven for thinking that Apple ditched the feature entirely on iPhone 11, 11 Pro, and 11 Pro Max, since a long-press of the shutter button now records video instead. However, burst mode is alive and well on your new iPhone — it's just hidden.

It appears that the floodgates of consumer-grade augmented reality smartglasses from China are now open, with Mad Gaze being the latest company to rush its product through.

Automating port scanners, directory crawlers, and reconnaissance tools can be complicated for beginners just getting started with Kali Linux. Sparta solves this problem with an easy-to-use graphical interface designed to simplify a penetration tester's tasks.

Many of our online accounts now come with an added two-factor authentication (2FA) functionality to help keep our data safe. This essentially means no one would be able to access the account until a specific set of requirements were met. It could be a combination of a password with a security key or even a passcode with some form of biometrics, like a fingerprint or face scan.

We last saw China-based augmented and virtual reality headset maker Shadow Technologies at last year's Augmented World Expo, where they had the Action One, one of the wildest augmented reality headsets we've seen, on display.

We're still weeks away from a probably HoloLens 2 release, but Microsoft's immersive computing team is still hard at work on other aspects of its "mixed reality" ecosystem.

The New York Times has made a habit of publishing augmented reality stories throughout 2018, and now the media giant's magazine is getting into the act, too.

Cracking the password for WPA2 networks has been roughly the same for many years, but a newer attack requires less interaction and info than previous techniques and has the added advantage of being able to target access points with no one connected. The latest attack against the PMKID uses Hashcat to crack WPA passwords and allows hackers to find networks with weak passwords more easily.

Smartphones and laptops are constantly sending Wi-Fi radio signals, and many of these signals can be used to track us. In this guide, we'll program a cheap IoT device in Arduino to create hundreds of fake networks with common names; This will cause nearby devices to reveal their real trackable MAC address, and it can even let an attacker take over the phone's data connection with no warning.

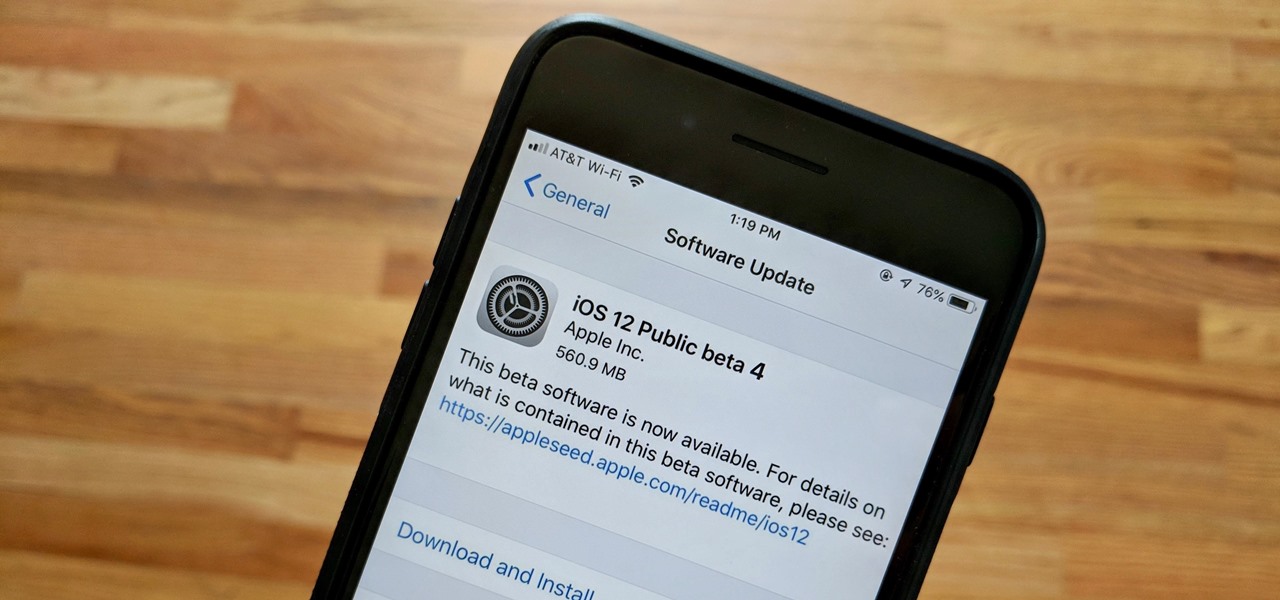
Apple released the fourth public beta for iOS 12 to public beta testers on Tuesday, July 31, just one day after the company seeded the fifth developer beta to eligible users. Both releases are surprising, as Apple had appeared to stick to a two-week release schedule for the iOS 12 beta season, and these updates both came one day earlier than expected.

Don't think because your MacBook is using FileVault disk encryption your device is secure or immune to hackers. Here's how to find out if that FileVault password is strong enough to withstand an attack from a motivated attacker.

Just in time for the release of Pixar's highly anticipated sequel, AR Emoji based on characters from The Incredibles 2 have arrived for Samsung Galaxy S9 and S9+.

The company behind Japan's beloved Gozilla, Japan's Toho Studios, has for years tried to give fans the sense of what a giant, nuclear-powered lizard invading Tokyo might feel like. Until now, those attempts have been limited to the movie theater, but now, with the help of the Microsoft HoloLens, Godzilla is finally getting its chance to invade the actual city, with terrified fans looking on from a safe distance.