This is a two-part series to locking down the computer to provide maximum protection. Even though this guide will sound intrusive, we are talking about reality here. Extreme measures must be taken to protect our computers, especially when we have confidential documentation or do internet banking, which many people do. We all have to use electronic devices at some stage, whether it be for business or personal use.

For this particular example, I will be working on Wndows (sorry X users). I might write a similar guide once I am more comfortable with programming in Linux.

If you've ever heard software piracy terminology being discussed, I'm sure the term KeyGens came up. KeyGens is short for key generator, which is a program that exploits algorithmic faults in software by generating software license keys that appear to be genuine. Normally used as a technique to protect the source code software and prevent piracy, a key generator exploits the key algorithm to effectively nullify the need for any software licenses. For example, we must try to find patterns in t...

Some people are what is labeled a power user. I am one of these people. No matter how fast I get my system, or how quick of programs I have, it is never good enough. There is always at least one program that I could swap out for a more advanced, text-based counterpart that increases performance just a bit. Luckily, you don't have to use text-based programs without graphical user interfaces to get blazing fast speeds on Linux. There are tons of open source alternatives to the mainstream progra...
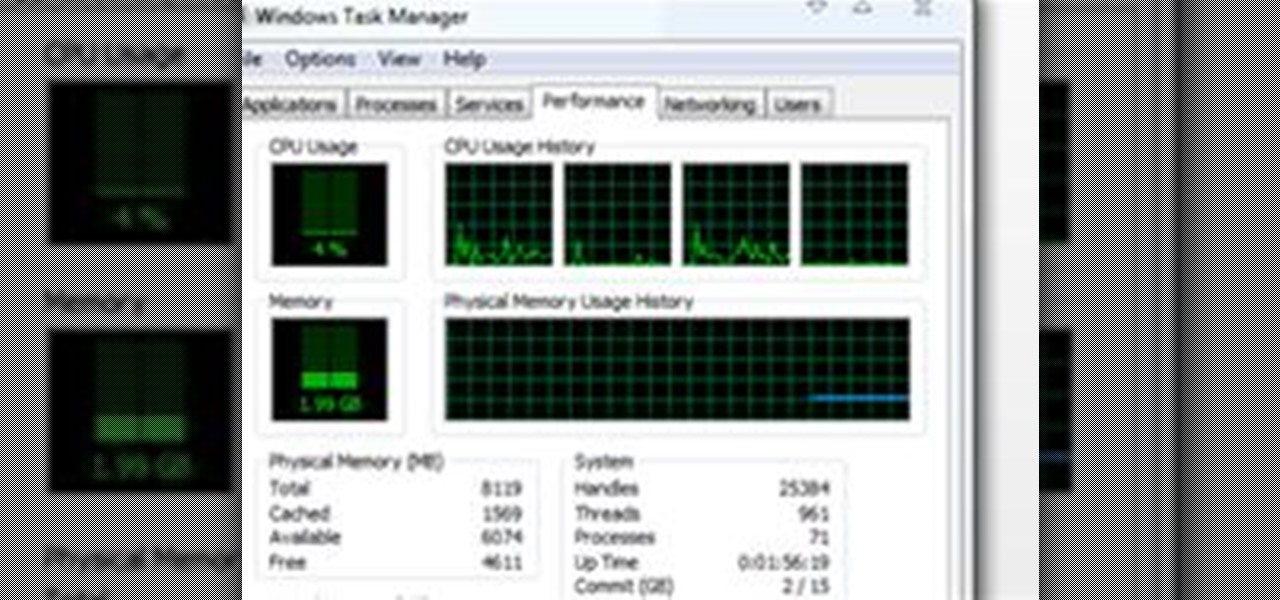
Introduction This is one of the things I am asked the most and there are so many different answers. It is hard to just tell you without know your computer's current speed or what type of hardware it has. So here I will talk about how to speed up a slow computer and how to keep your computer running fast.

While a lot of internet threats are rather over-hyped, there are some serious things to be cautious of when going online. Probably the biggest risk to the average internet user is malicious software. Commonly knows as "malware," this term refers to any program that exists solely to do harm. This may include damaging your computer or accessing your data without you knowing. Viruses, trojans, and spyware are all forms of malware. Now, malware can seriously mess up your system, and the idea of s...

Engr. Alan James Borgueta explaining the program used in determining the results

System Tool. It sounds like something your Windows computer might need, but it's the exact opposite.

The first day of Hanukkah is here, the day you start lighting the candles of the menorah. So, why not ditch the wax and light the "lights" this year?
Cheating ruins everything. Cheating makes game play unfair for others who may be truly competitive and strategic. Cheating makes others disrespect and un-friend you. There can be unforeseen consequences, like getting viruses, trojans or your account hacked from downloading a cheat/bot program. And you will get banned from the game for violating terms of service.

A Java programming tutorial on creating and working with array objects. Create arrays in Java.

Introduction In the competitive world of today's video game scene, PC gamers are known to squeeze out the best possible visuals in their games. Every few months a new video card rolls out, and RAM is ever increasing; constant upgrading is the norm of staying ahead the curve. One of the most important things a PC gamer looks at is how many FPS (frames per second) he gets. It defines his gaming experience.

By now, you should know a few of the basics of programming with OpenGL and GLUT for C++ developing, like shapes, transformations, timers, and colors. Now it's time for lighting. Everything could look right in your 3D program or game, but if you're lighting isn't right, it's a sad world for all of us. This video lesson will show you how to add lighting to 3D scenes with OpenGL for C++, so you can start making your own 3D programs.

By now, you should know a few of the basics of programming with OpenGL and GLUT for C++ developing, like shapes, transformations, timers, and colors. Now it's time for lighting. Everything could look right in your 3D program or game, but if you're lighting isn't right, it's a sad world for all of us. This video lesson will show you how to add lighting to 3D scenes with OpenGL for C++, so you can start making your own 3D programs.

After you've learned the basics about shapes, transformations, and times, it's time to move onto learning the color scheme of things in the C++ programming language. You can't have a beautiful 3D game or program with out vibrant colors! This video lesson will show you how to add colors to 3D scenes with OpenGL for C++, so you can start making your own 3D programs.

Follow this video for some tips on how to cheat in exams and tests. You can have a calculator that stores information and notes in it. Such calculators such as the TI83 and 84 plus calculators have a feature where you set up a new program. Type in your notes in this program you created. When you need to read through these notes during an exam, you just have to access that particular program. Another method is to store in mp3 players by recording your voice while reading out the notes, or else...

iKITMovie is stop motion animation software for PC's running Windows XP or Vista. All you need is a computer and a USB webcam or USB streaming camcorder and you are ready to make your own brickfilms or clay animation (claymation) movies. If you wish, you can simply import your JPG images (640x480) that you have already taken with your camcorder or digital still camera for simple editing.

What does it mean when there is no picture on the television? Check out this video tutorial on how program the Panasonic remote DMR-ES15 (ES25) for other TV's. This Panasonic DMR-ES15 (ES25) DVD Recorder is easy to operate and great to record with.

What does it mean when there is no picture on the television? Check out this video tutorial on how program the Panasonic remote DMR-ES45V (ES35V) for other TV's. This Panasonic DMR-ES45V (ES35V) DVD Recorder is easy to operate and great to record with.

What does it mean when there is no picture on the television? Check out this video tutorial on how program the Panasonic remote DMR-EH55 for other TV's. This Panasonic DMR-EH55 DVD Recorder is easy to operate and great to record with.

What does it mean when there is no picture on the television? Check out this video tutorial on how program the Panasonic remote DMR-EH75V for other TV's. This Panasonic DMR-EH75V DVD Recorder is easy to operate and great to record with.

Hello everyone today I am going to be going over installing Minecraft on Linux (Ubuntu) as if it is any regular program a game. This method makes it super easy and clean in that you will not need to run a .jar every time you want to play this game. This is very simple to do and it dose not only install Minecraft as if it is any regular game/program it also gets the best version of Java to run Minecraft. Download: http://goo.gl/DKQ6B

Today, we are going to combine what we learned from the Introduction to Cryptography article with our Java programming skills. If you are new to Java, check out Matthew's Learn Java: Part One for a quick beginner's lesson, or check out some of the Java tutorials directly on Oracle.

There is a vast amount of knowledge out there on computers! In fact, it is so vast that no single person could ever possibly ever learn everything there is to learn about hacking or computers in general. People usually specialize in a certain field: cryptography, computer security, networking, software development, testing, and so on...It's probably a bit premature to decide what you want your speciality to be, but keeping the question in the back of your mind will help give you direction in ...

Accounting and Finance Degree

Here's something fun for the Null Byte community to do—a coding competition! This week, I wanted to get everyone involved by offering you all a nice library of possible program types to choose from and try to code. At the end of this competition, all of the submitted programs will be reviewed by the community and myself. The coder that receives the most votes will be dubbed THE BEST.

Following the first part in this series on advanced cracking techniques, we are going to go over how we can intelligently crack passwords using the old-fashioned bruteforce method. These unique cracking techniques aren't widely used, because most crackers are Script Kiddies who have no idea what the concepts are behind cracking passwords, thus, word won't get around too quickly.

As per Alex's request, I am posting about generating word-lists in Python. However, this is my FIRST attempt with Python, so please provide me with critiques and any and all comments. I really want to know what you think as there was a little bump here and there seeing as I am transitioning from C#.

Just removed an important gem from your weapon? Totally screw yourself over by restarting a bloodline instead of the battle you just lost? It sure would be great if you could backup your character so you can always have a safe copy ready to go at a moment's notice. Well, those smart folks over at the Infinity Blade forums have devised a clever way to do this.

Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server.

Welcome to the fifth Community Byte for coding in Python and beating the challenges given to us from HackThisSite. These sessions are created to bring our community together, to learn from each other, and essentially grow together. Everyone is welcome, from novice programmers to aspiring hackers—even people that are nearly computer illiterate.

When you first become interested in learning how to program, it can be difficult to find a place to start. A lot of questions come up, especially if you're new to the idea of programming entirely. After you pick which language you want to learn, you have to worry about how you're going to write the language.

With the rather large success of the Community Byte activities, both programming and HackThisSite, I have decided to continue to do both activities every session! With that said, when programming sessions occur, they will be lead by Sol Gates in Gobby. Also, the programming mission will no longer be to code a tool, we have changed it to be even more "noob friendly". This means that instead of coding a tool, you will be walked through puzzles and challenges that must be solved by coding a scri...

At Kaplan University, our main focus in developing our online MBA programs is career development. We believe the time and effort that is required to obtain a master’s degree online should be apparent the first day the student begins their new career. Earning an MBA could be a step in the right direction towards a fulfilling and satisfying career.*

Kaplan University master’s degree graduate Onica Browne obtained her Master of Business Administration (MBA) with a focus on international business. In her case, this Kaplan University online program offered a unique learning experience to collaborate with students in other countries, enriching the learning process.

Hideo Kojima is one of the biggest names in Japanese game design. He's the man behind every Metal Gear game, each of which has been beautiful but divisive. He's an auteur, a rarity in AAA game design, managing business, design, and programming for Kojima Productions. Last week he made a rare public appearance at the USC School of Cinematic Arts, which contains the school's video game programs, and gave a 90-minute talk about his career, influences, and the specifics of his new Fox game design...

Introduction In this post we will look at how to access a PosgreSQL database in your C/C++ application. It's not as hard as you might think, but you need to understand the procedure and the functions used.

Thanks Anonymous User For This Article, Not Bad Ok SoftzZz...!.!.!.: Step 1 Antivirus