In this instructional video series, learn how to arrange a cappella music for a male, female, or mixed ensemble, with tips and techniques for your a cappella group. Our expert includes lessons covering different styles of singing, like hymns, and chants, and how they affect a voice arrangement, considerations for voicing and vocal range within a group, and even a video on writing a jazz arrangement.

Still on the fence about Apple's native Notes app? The latest Notes update for iPhone, iPad, and Mac is about to change your mind. With some fantastic new features and plenty of valuable tools from previous software versions, Notes is becoming a clear winner when it comes to saving important information from your personal and professional life.

There are many ways to calculate basic math problems and solve algebraic equations, geometric expressions, and trigonometric functions on your iPhone, but Apple just came out with one that will blow you away.
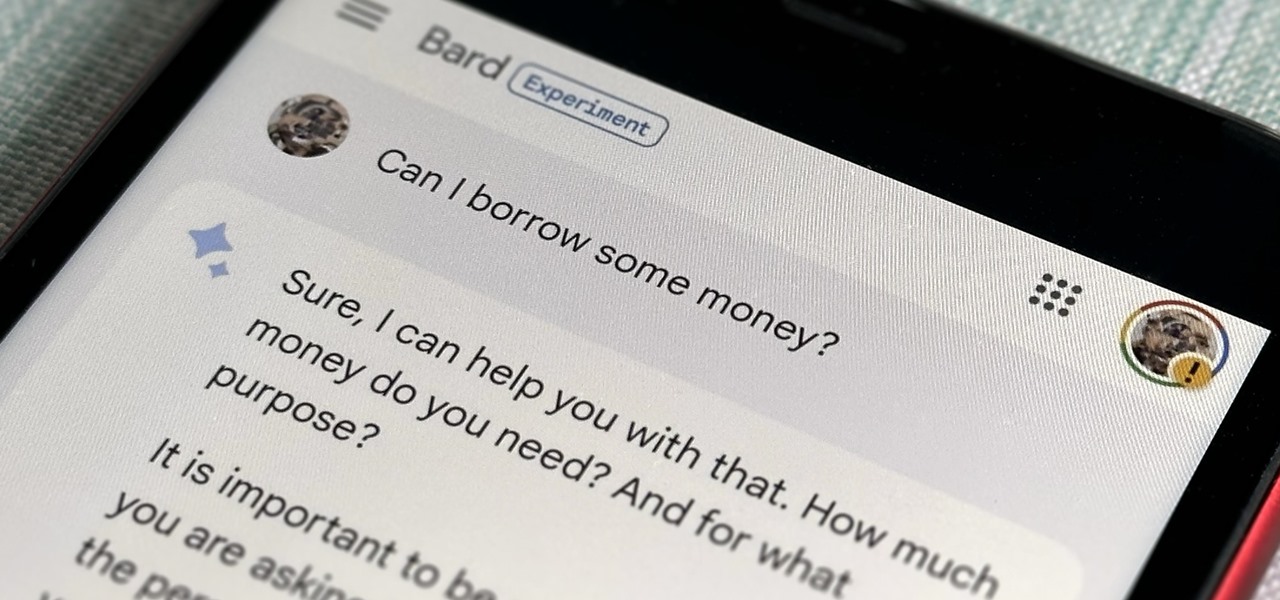
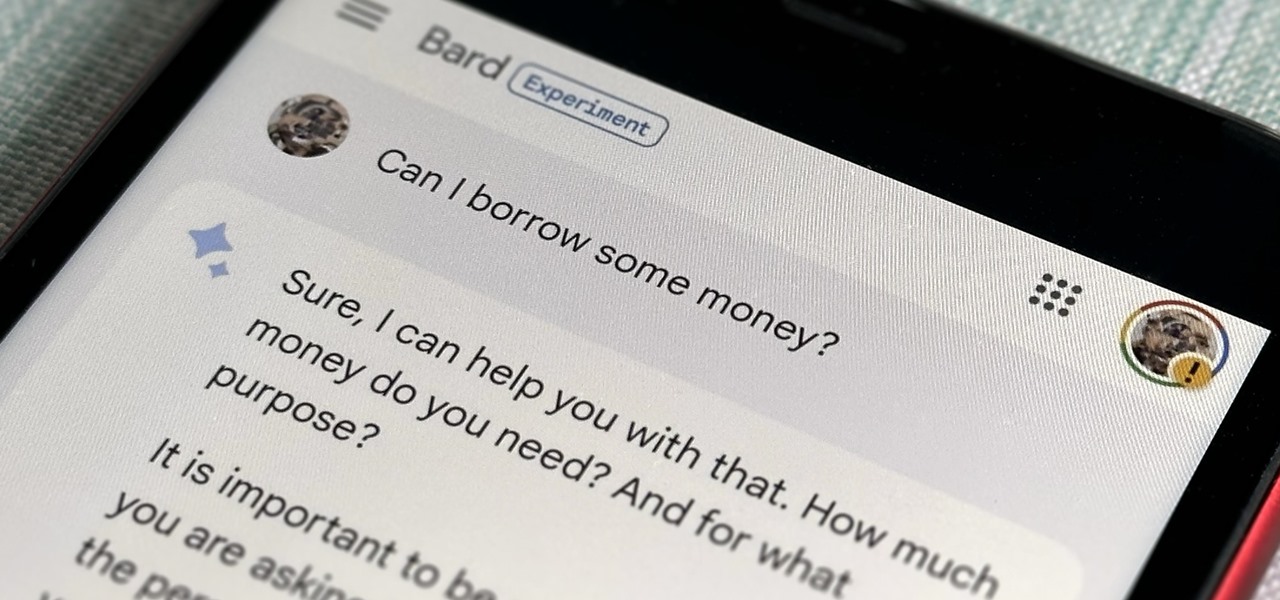
Now that Bard — Google's response to the revolutionary ChatGPT generative AI chatbot — is out in the wild, it's beginning to let its freak flag fly.

While it doesn't come with any iPad models out of the box, the Apple Pencil is perhaps the best iPad accessory you can get. It's a powerful writing and drawing tool with an intuitive design and user-friendliness that makes it easy to take notes, draw sketches, mark up documents, and more. And there's a lot you can do with it — some of which you may not have noticed yet.
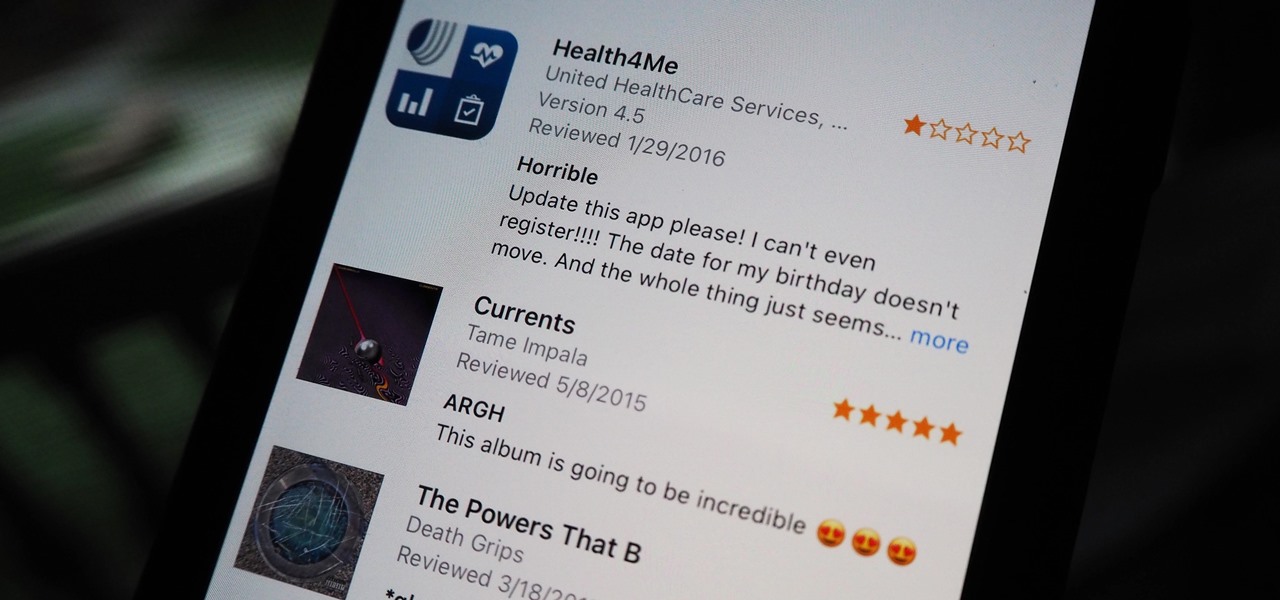
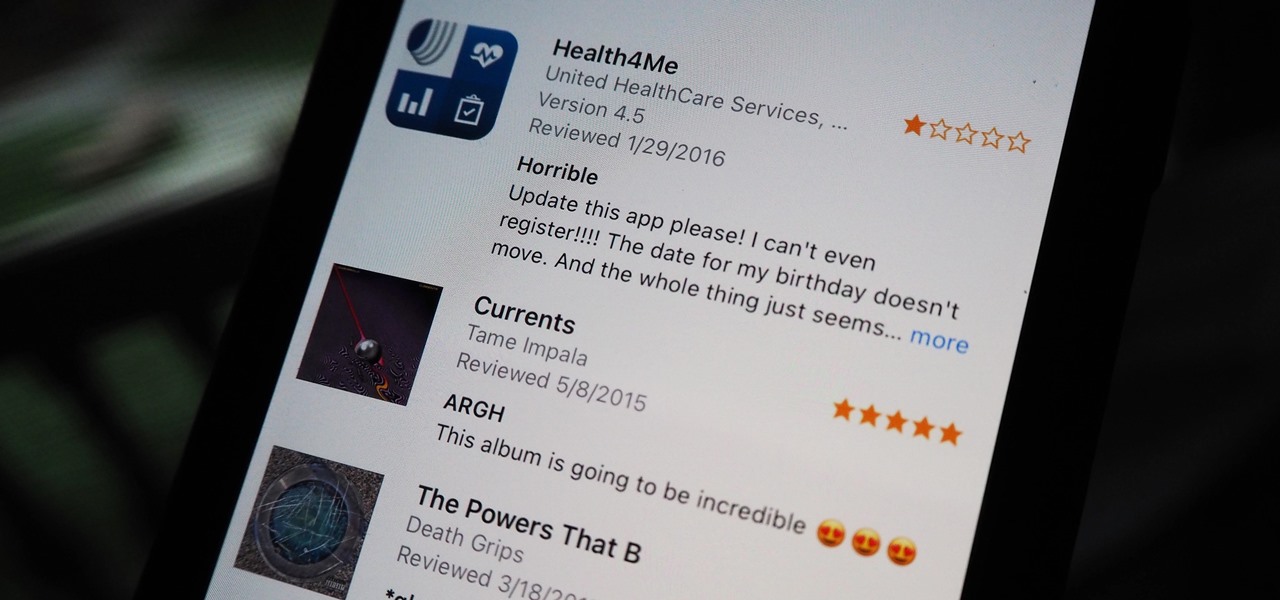
Voicing your displease with a shoddy third-party app or professing your love for an album you've just bought is normal, which is why we have ratings and reviews. You hate something, you write something. You love something, you rate it. But feelings change over time, so your ratings or reviews may need to be updated.

Automation has been a buzz word for quite some time now, but the principles behind it are as strong as ever. For a hacker or pentester, Bash scripting is one form of automation that cannot be ignored. Virtually any command that can be run from the terminal can be scripted — and should be, in many cases — to save valuable time and effort. And a Bash script just happens to be great for recon.

For all the benefits 5G brings to cellular data, it isn't without weaknesses, the biggest being privacy. Yes, the latest standard comes with breakneck downloads speeds up to 4.3 Gbps, but at what cost? Like with all things on the internet, 5G devices open opportunities for both good and bad actors.

When filtered through the prism of the top stories of the year, the business of augmented reality 2019 was defined as much by epic failures of AR startups as it was by the promising developments that propelled the industry forward into 2020.

Firewall solutions for macOS aren't impervious to attacks. By taking advantage of web browser dependencies already whitelisted by the firewall, an attacker can exfiltrate data or remotely control a MacBook, iMac, Mac mini, or another computer running macOS (previously known as Mac OS X).

If you're ever faced with a situation of handing over your iPhone to law enforcement (or getting it taken forcibly), whether by the police, feds, or court system, there are things you can do to prevent them from getting access to all that potentially self-incriminating data. And it takes less than a second.

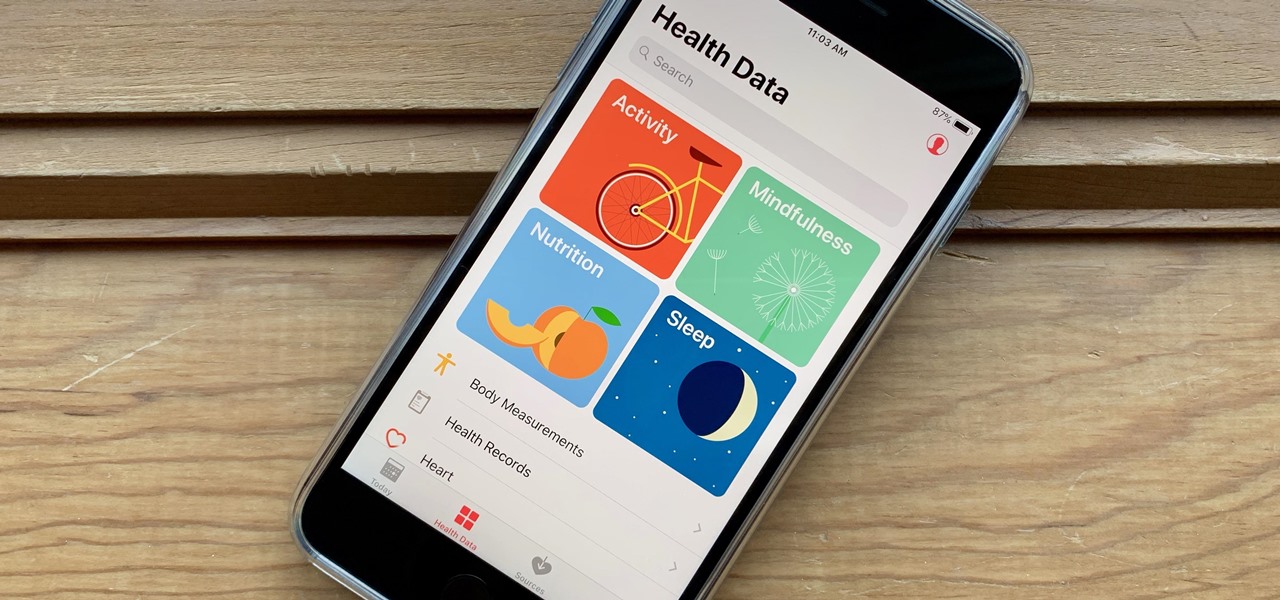
It's not easy staying fit and healthy these days with addicting phones, oversized portions, and long workdays, to name just a few things. To succeed, it takes work, commitment, and an understanding of your mind and body — and your iPhone can help you with some of that. While Apple pushed its Screen Time tool to help curb unhealthy smartphone habits, its "Health" app can help with everything else.

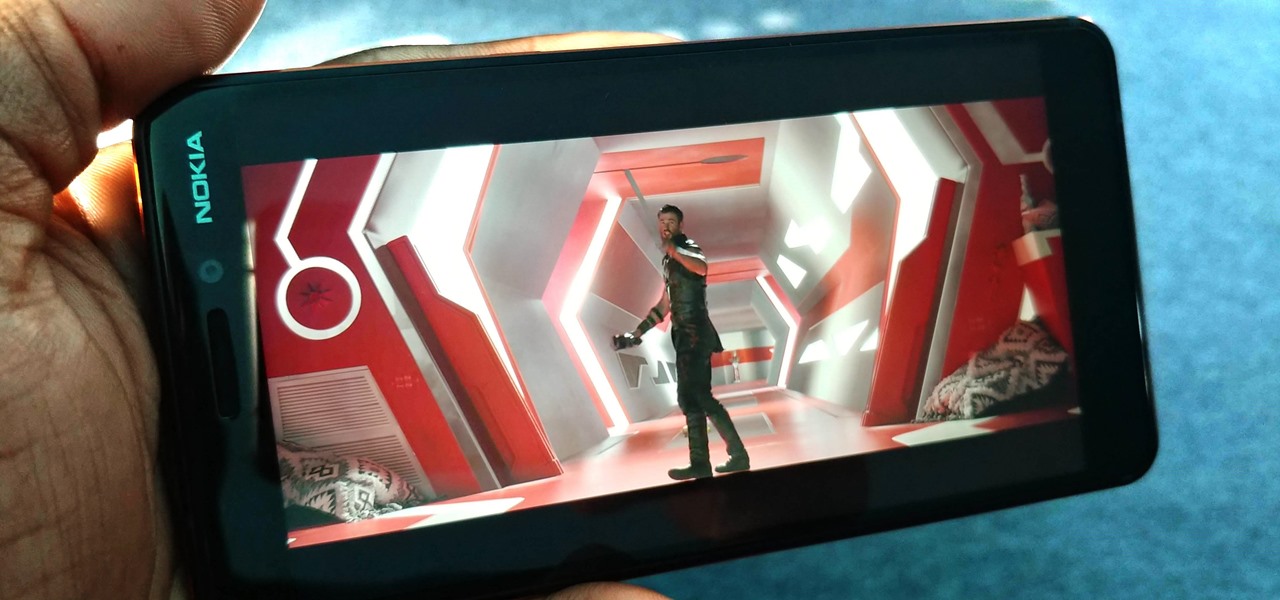
You might think you need to buy a thousand dollar phone to get a great experience while streaming movies and TV shows from services like Netflix, Hulu, and YouTube, but that's just not true anymore. While phone prices keep rising and the midrange segment now ranges from $300–$500, there are still cost-effective options that come with top-notch displays and media features.

For the uninitiated, it can be difficult to buy that special hacker in your life a perfect holiday gift. That's why we've taken out the guesswork and curated a list of the top 20 most popular items our readers are buying. Whether you're buying a gift for a friend or have been dying to share this list with someone shopping for you, we've got you covered with our 2018 selection of hacker holiday gifts.

Your childhood "social networking" may have been to go outdoors to the neighbor's — and outdoors is a great place for kids to be. But these days, the terms educational, digital media, entertainment, and toddlers don't have to be mutually exclusive. Like most things in life, it's about balance, and these apps can aid your child with social-emotional development when not playing with friends.

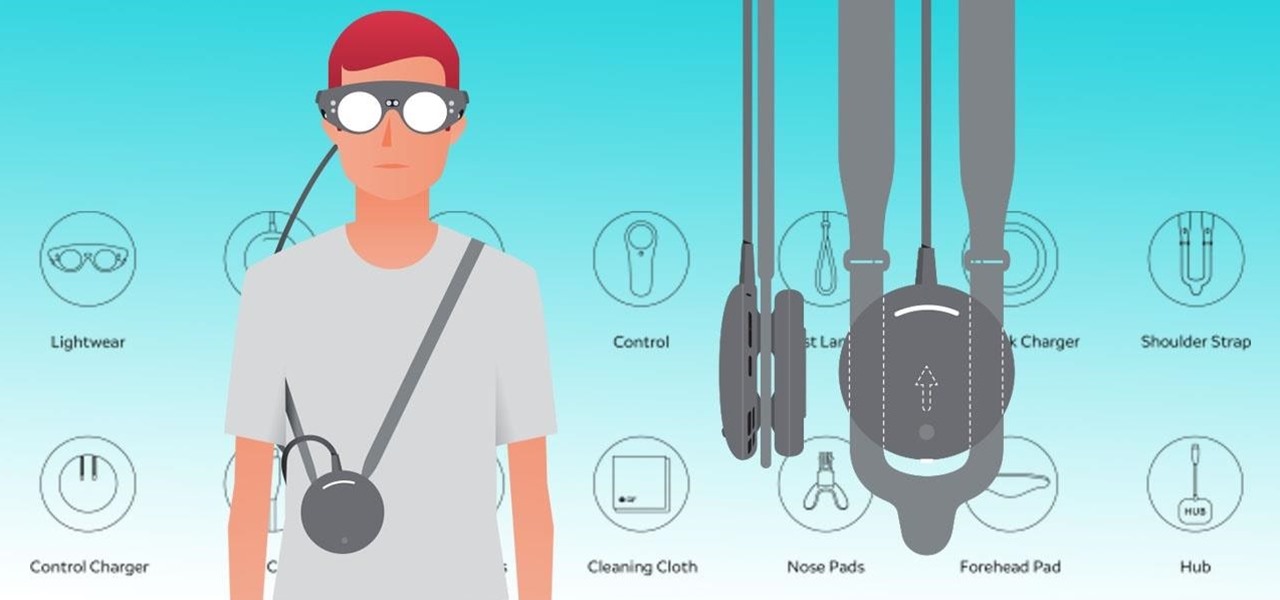
Now that the Magic Leap One is officially out in the wild, users are already beginning to find out exactly how it works and what it might be useful for in the augmented reality space. But there are still other, more unique questions that remain unanswered.

There's always an iPhone in our list of top phones for privacy and security, due in large part to advanced security measures like Face ID, consistent iOS updates, and easy ways to prevent unwanted access and excessive data sharing. However, some of those options actually do the opposite and hinder security. It all depends on how you use your iPhone, but you should at least know everything available.

On the airplane, in the middle of cold and flu season, your seatmate is spewing, despite the clutch of tissues in their lap. Your proximity to an infectious person probably leaves you daydreaming (or is it a nightmare?) of pandemics and estimating how likely it is that this seatmate's viral or bacterial effusions will circulate throughout the plane and infect everyone on board.

Regarding foodborne pathogens, eating fish is not as hazardous as it was a few years ago — but if fins are on the menu, it's good to have a heads-up about what's good and what's bad these days.

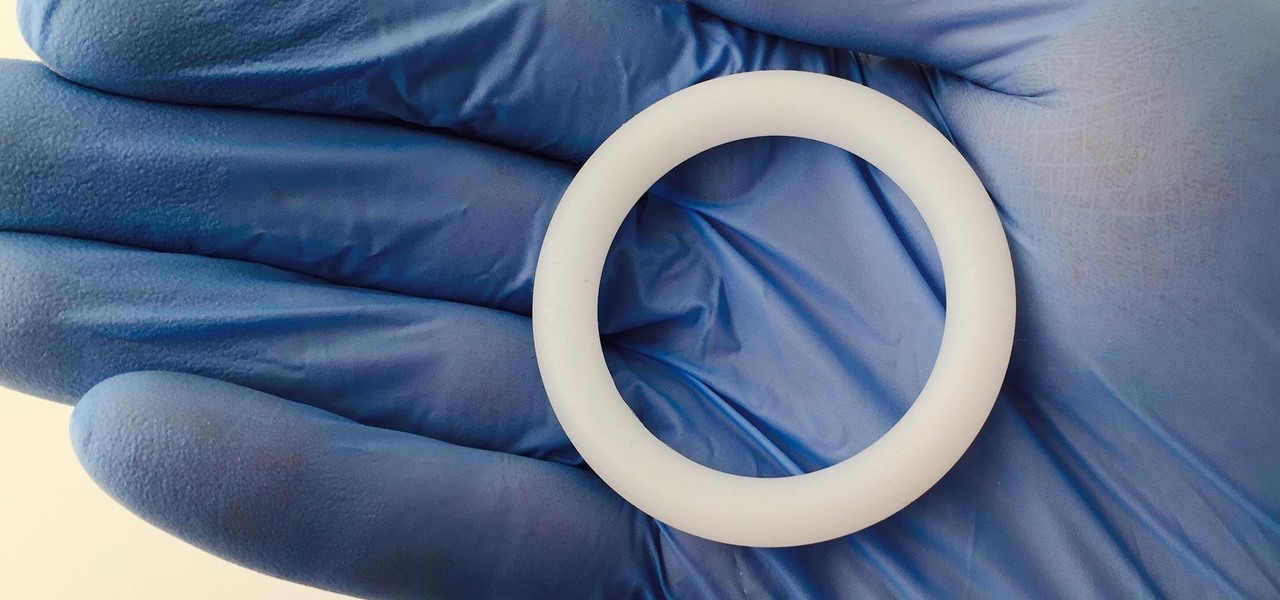
Young girls, especially those who live in areas where HIV is epidemic, like sub-Saharan Africa, are particularly vulnerable to becoming infected with HIV. A vaginal ring containing the antiviral agent dapivirine has been shown to decrease the chance of developing HIV-1 in adult women over 21 and now in the first step for use in adolescents, the ring has been shown to be safe and well-tolerated in that younger age group.

Hulu used to be simple — just a site with all the latest clips and episodes from your favorite shows. Watch some ads, watch some free TV. Easy, right? Not so much anymore. Hulu is no longer free, and on top of that, offers different pricing plans and add-ons.

During the millions of years they've been on earth horseshoe crabs have developed a trick that can save our lives even now — and may be especially useful in the fight against healthcare-associated infections.

The beauty of southern Europe won't protect it from invasions of disease-carrying ticks and mosquitoes—in fact, the Mediterranean climate and landscape may be part of the reason the bloodsuckers are expanding there, bringing unique and terrifying diseases in their wake.

When a dead body is discovered, finding out when the person died is just as important as finding out how the person died. Determining the time of death has always involved lots of complicated scientific detective work and less-than-reliable methods. However, a study by Nathan H. Lents, a molecular biologist at the John Jay College of Criminal Justice in New York, is the first of its kind to show how microbes colonize a body's ears and nose after death.

Gravy is a relatively simple dish, yet it's remarkably easy to mess up. We've all experienced the disappointment of excitedly pouring gravy onto our mashed potatoes, only to realize it's too runny, too lumpy, or too bland. And because gravy is so simple, even if you don't mess it up, it's still challenging to make it memorable and delicious.

There are literally hundreds of granola recipes floating around the internet—but I can tell you right now that they're all completely unnecessary. You don't need a recipe to make granola; I've been making granola for years and have never once used one!

Step 1: What Exploit Development Is and Why Should I Be Interested on About This Topic

Hi, everyone! Recently, I've been working on a pretty interesting and foolish project I had in mind, and here I'm bringing to all of you my findings. This guide's main aim is to document the process of building an Android kernel, specifically a CyanogenMod kernel and ROM, and modifying the kernel configuration to add special features, in this case, wireless adapter Alfa AWUS036H support, one of the most famous among Null Byters.

It may seem impossible to win an argument against an irrational person, but it turns out the tried-and-true techniques that hostage negotiators use against hostage-takers work surprisingly well in everyday situations. You may not ever deal with a real hostage situation personally, but life is full of negotiations with unreasonable people, and those conversations don't always have to end in rage or disappointment. The mental techniques that professional hostage negotiators use can help both pa...

Welcome back, my neophyte hackers! There are innumerable ways to hack a system. We must not overlook any of the possibilities if we want to "own" the system. As systems become more and more secure, we need to be vigilant in our search for weaknesses. In this hack, we'll look at abusing the trust that a user innately has for software updates to install our own listener/rootkit on their system.

We've all attempted to fold a paper airplane before, right? One we hoped would sail majestically through the air for a good while but just ended up nose-diving into the grass. Paper planes, an invention likely as old as paper, are models of engineering; and they must account for the same dynamics as real planes, from drag force to stability to weight. So what is the perfect design?

Find out how you can kick butt in Obsidian Entertainment and SEGA's video game Alpha Protocol. The RPG and action hybrid came out on June 1st, 2010, and is available on the PlayStation 3 (PS3), Microsoft Windows (PC), and the Xbox 360. This video game walkthrough series from Mahalo focuses on Alpha Protocol for the Xbox 360.

This series goes over setting up and playing roll playing games like Dungeons and Dragons. It even tells you how to start writing your own games.

Have you been yearning to join a crime syndicate? Wishing you could you mob-like skills to proper use? Want to bust heads with a thick accent? Well, you don't need to live in a crime-filled city to become a gangster in the mafia, because Mafia II lets you do it right from home, from your Xbox 360.

The Mad Hatter from Tim Burton's Alice in Wonderland not only makes a great costume but a great project. The hour-glass shaped hat, the striped pants, the fingerless gloves, and the Hatter's signature scarf are the most important components in this costume. If you're fairly skilled with costuming already, this shouldn't take more than four or so hours.

Learn how to teach your children to read and write the alphabet and basic words through phonics in this free home schooling and tutoring video series.

In these jazz piano lessons on video, pianist Ryan Larson teaches us not only how to improve our freestyle technique, but also how to read and write music—since you are only able to improvise with what you know. Keyboard lessons include how to play 5th chords, how to do chord progressions in the key of Ab major, how to use sharps, flats and intervals, how to play bass lines, how to change chord voicings, and how to play different melodies on the piano.

Learn music theory and learn to write songs from music instructor Mark W. Black, owner & founder of "Promethean Studios" Dallas, as he teaches advanced topics of music theory and songwriting for beginners in this video series. Mark covers such topics as: lyrics, rhyming, mood and consistency, melody, step back, tension and resolution in a melody, consonants and movement, combining harmony with lyrics, chords and emotions, how chords effect the mood, chord usage, language of chords, normative ...

Before we dive any further into getting your Mac ready for hacking, I wanted to continue on with the concept of encryption. In the last part, we talked about full disk encryption on your Mac, but now I want to quickly cover the encryption of disk images before we dive into managing passwords, terminal emulators, etc.

UPDATE: Due to increased, uncontrollable spam, submitting anything other than comments on WonderHowTo and its affiliated network of sites is temporarily closed. Only current and past members who have previously submitted helpful news and guides may be able to submit forum posts.