Uber has lost market share to Lyft, its main competitor. Uber's US market share dropped from 84% to 77% between January and the end of May this year, and the ride-sharing company has continued to run into legal, public-image, and internal trouble. Lyft, on the other hand, has been growing.

The list of HoloLens applications continues to grow as more companies discover ways to enhance their operations using augmented reality. Air New Zealand is the latest to show interest in the technology, demonstrating their vision for AR in a new concept video.

Apple staff will be put through their paces now that the company's "Automated System" for driverless cars is in motion.

Every party has a pooper, and that's why you're reading this article. We don't mean to be a downer on such a fun day as 4/20, but it's important to make sure you know about the source of your pot, especially if you're one of the 2,299,016 people who use medical marijuana in the US.

Google's Pixel smartphone is striking up some heated competition between phone makers HTC, LG, TCL, and Coolpad, as the Pixel 3 gets ready to release in 2018. Yep, you heard that right—not the Pixel, not the Pixel 2, but the Pixel 3—which shows that Google is really committed to the future of its new flagship line.

Pokémon Go takes the popular franchise and brings it into the real world through augmented reality, allowing us to play the game while exploring our physical environments at the same time. It doesn't just put pocket monsters into a more realistic context, but it changes the game in some major ways that may delight some players... and upset others.

In Minecraft 1.9 New Command Blocks can be used to make elevators. You types different commands to achieve controlling the elevator for movement you like. This tutorial tells in Minecraft 1.9 how to use command blocks to make elevator. Lets just have a look at it!

Get some tinfoil hats and make a time machine because we are about to go back to the 90s and learn about some phreaking.

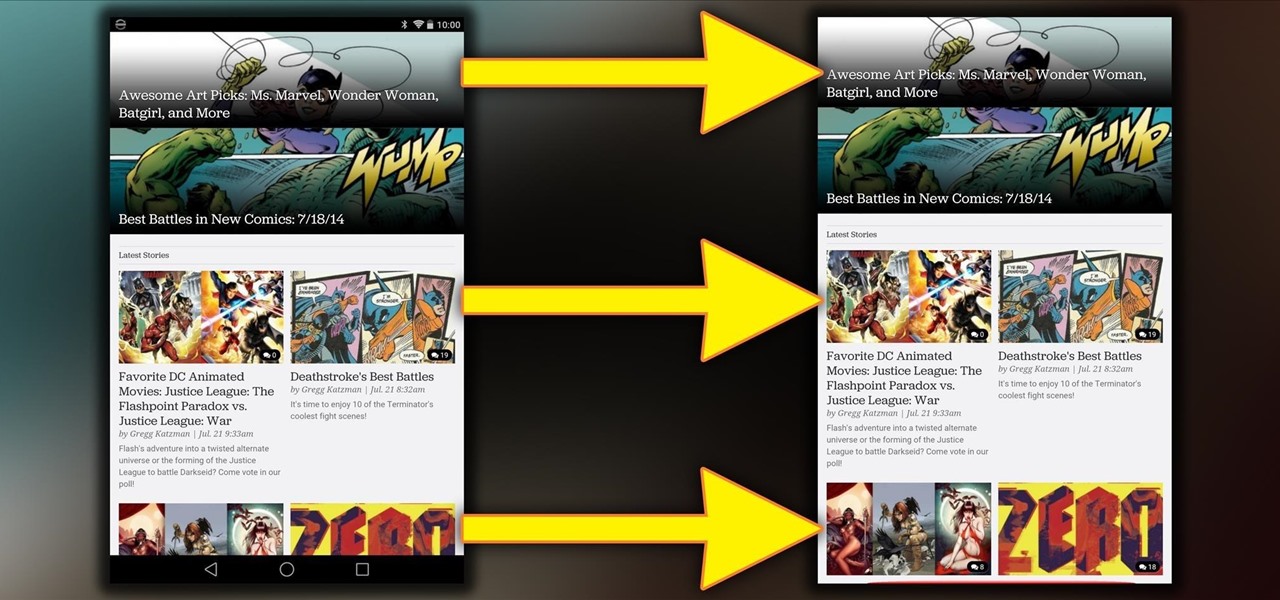
Rooting is a great way to unleash your device's full potential, but not everyone's comfortable with it. Rooting can void a warranty, cause issues with certain apps, and the process itself can be tricky for older devices. Alas, most of the great apps or mods out there require root access, like the ability to utilize a built-in KitKat feature known as Immersive Mode.

If you work at a large office or have a multi-story home, you're probably familiar with Wi-Fi range extenders. Since one hotspot isn't always enough to cover an entire area, Wi-Fi repeaters are generally set up in larger areas to capture and rebroadcast the original signal.

If mainstream media has taught us anything, it's that being beautiful can get you ahead in life. The notion isn't necessarily correct, but it's what the general consensus accepts and it seems to hold quite a bit of weight (no pun intended) in the western world.

I collect straight razors from the Victorian era and then add some steampunk style. Step 1: Remove the Old Scales

If you're a Breaking Bad junkie who can't wait for the next episode, satisfy your craving with a little at-home chemistry and make some blue DIY smash-glow crystals! No, this is not Walter White's so-called "Big Sky" or even the subpar cringe-worthy product of his competitors. It's not even the same kind of crystals, otherwise you wouldn't be reading this. This is totally legal, even kid-friendly if you play it safe, though it actually requires more safety precautions than the potassium nitra...

Earlier this week, Spiderlabs' vulnerability researcher Jonathan Claudius discovered a key in Windows 7 and 8 registries that makes it easy for anyone with physical or remote access to a computer get a hold of the user's password hints. When the "UserPasswordHint" key is read, the hints are displayed as a code that looks encrypted, but Claudius noticed a pattern of zeroes that could be easily translated back to plain text with a decoder he made in Ruby. He added this functionality to the Meta...

In the following video, I demonstrate how to create a device capable of charging the body of anyone who wears it with static electricity, allowing a powerful shock to be discharged into anything that is touched. This grants the wearer the ability to do some pretty amazing things, some of which are shown in the first segment of the video.

Backpacks are handy for camping, hiking, school and travel, but they can be difficult to pack properly. In this tutorial, learn how to pack your bag so that its light and efficient.

They say cheaters never prosper, but how will your know for sure if you don't give it a try? By a little repositioning of the blindfold and some spacial awareness you can be the master at this classic party game.

Nmap is more powerful than you know. With a few scripts, we can extend its functionality beyond a simple port scanner and start to identify details about target servers sysadmins don't want us to know.

When a headache strikes, I reach for the nearest painkiller. Forget closing my eyes, laying down, or even applying an ice pack—I seek the quickest and most immediate relief possible, and normally that comes in the form of pills. However, fast relief can be found from another, more natural source: herbal beverages. So if you're tired of popping pills when you have aches and pains, try some of these herbal drinks out instead.

Greetings my fellow aspiring hackers, It's still Christmas and we have a lot of things and hugs and kisses and ... to share ( you know the things that you do ). I have never done this before but I just felt to encourage you on the quest for knowledge, security and defence, skills and a whole lot more that comes out as a result of pursuing hacking. What we mean by hacking on this forum is White hat Hacking and OTW has great articles on it and I don't need to explain myself on that one.

Today's smartphones and tablets offer a great way for children to learn through interactive sight, sound, and touch, but they can also provide hours of genuine fun. If you have a spare tablet laying around—or at least a nice, durable case—the only thing you need to get your child started in this world of fun and learning is a handful of good apps.

Minor mishaps occur all the time in the kitchen, whether you cut your finger while dicing an onion, scorched your hand in a grease fire, or burned the roof of your mouth because you were to eager to taste-test your killer pasta sauce.

The best part about April Fool's Day is that everyone is fair game. Even big tech companies like Google and Twitter get in on the action every year. It encourages even the most uptight, unfunny party-poopers among us to have a little fun driving each other crazy with pranks — even at work.

If you've been to a convention of any sort before, you know that there are good and bad panels, and that their inherent goodness or badness often has little to do with the actual content being discussed. That's because giving a panel is a skill that not everyone has. However, it is a skill that everyone could have! In this article, I'll tell you how to give a good panel on practically any subject. Image by Shannon Cottrell

This video animation tutorial demonstrates the process of sculpting a human face out of polymer clay as part of an armature for stop motion animation. The demonstrator begins by molding a piece of polymer clay into the general shape of a human skull and neck, and impresses the more finite features with the aid of a flexible sculpting tool. Watch this instructional video and learn how to sculpt the face of a polymer clay stop motion armature.

A pyramid is a three-dimensional figure with a polygonal base and a vertex. The base can be a triangle, quadrilateral, pentagon, hexagon, or other type of polygon.

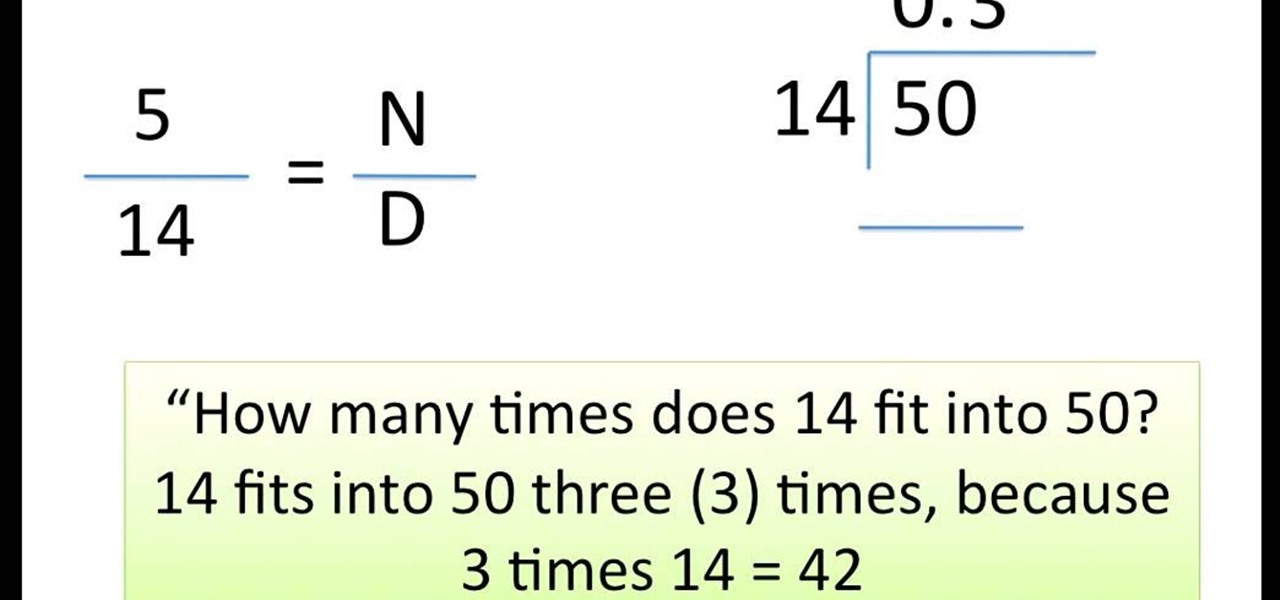
This video shows you how to easily divide proper fractions. In the first step, you have to calculate how many times does the denominator fit into the numerator. You need to divide the numerator by the denominator. If the denominator does not fit into the numerator, you have to write 0, followed with a point, at the top of the calculation ("0."). Next, you add a 0 next to the numerator (multiply it by 10). Now, you have to calculate how many times does the denominator fit into the numerator ag...

If you're an AirPods user, things are a lot better with iOS 18 and iPadOS 18. If you're not, it may finally be time to grab yourself a set of AirPods, especially if you're into privacy and gaming.

For all the benefits 5G brings to cellular data, it isn't without weaknesses, the biggest being privacy. Yes, the latest standard comes with breakneck downloads speeds up to 4.3 Gbps, but at what cost? Like with all things on the internet, 5G devices open opportunities for both good and bad actors.

Determining the antivirus and firewall software installed on a Windows computer is crucial to an attacker preparing to create a targeted stager or payload. With covert deep packet inspection, that information is easily identified.

Just as predicted (but perhaps with less fanfare than usual), Apple has made the move of adding a depth sensor to the rear camera of its latest edition of the iPad Pro.

As the demand for realistic volumetric video for AR experiences begins to grow (along with the available facilities and services for capturing it), researchers at Google have figured out how to improve upon the format.

It's no secret that Samsung is working on augmented reality hardware, as the company has been candid about its intentions. However, what we don't know is exactly how many AR projects the company is working on, as patent filings and reports revealed two more over the past week.

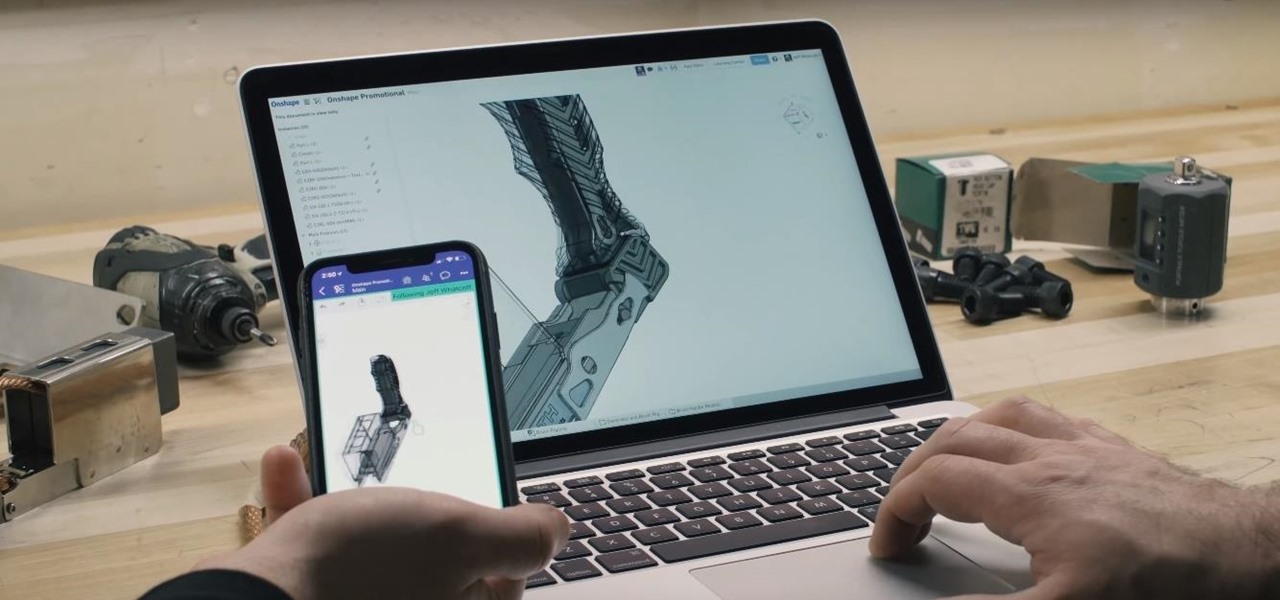
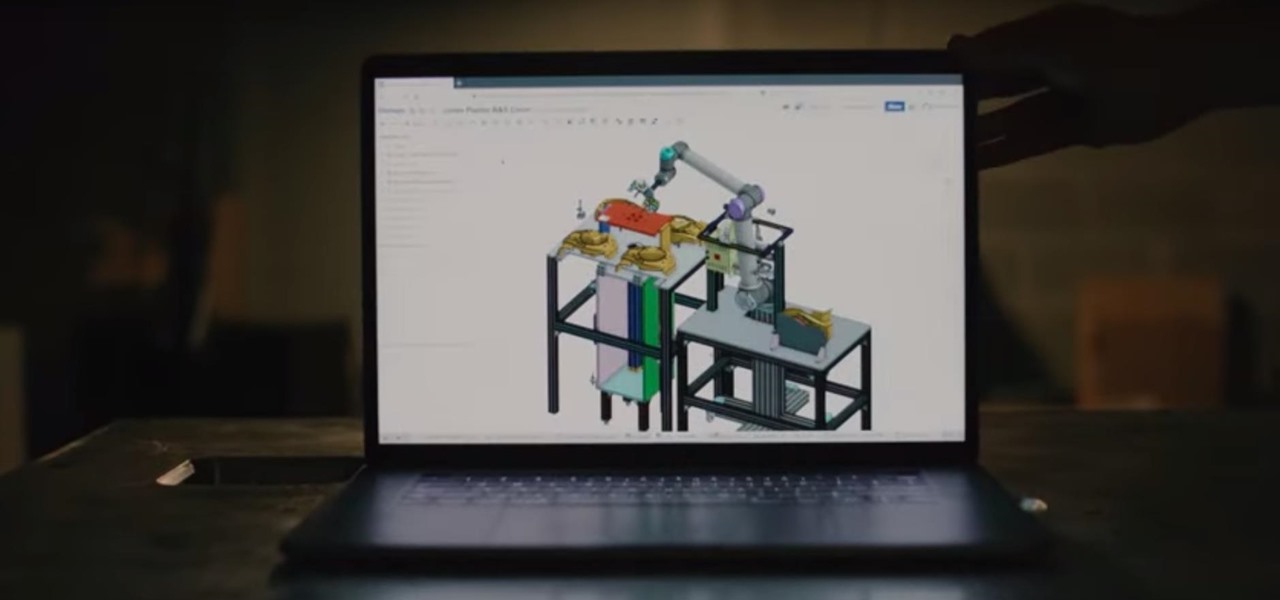
There's a direct correlation between the proliferation of augmented reality apps and the demand for 3D content, and PTC just quantified that in dollars.

The legal drama surrounding Chinese startup Nreal and Magic Leap continues, and now we finally have an update.

There's no denying that native Dark Mode in iOS 13 is awesome. Stock apps that were blindingly white for over a decade can now be comfortably used in the middle of the night. You might find, however, that some of your third-party apps aren't taking the hint. Why won't YouTube switch to dark mode when iOS as a whole does? We put together a troubleshooting checklist to get your apps cooperating.

There are a lot of songs out there, so it's tough to remember all of the words to every song you like. If you're like me and have a less-than-perfect memory, visual aids will ensure your Apple Music jams aren't interrupted with incorrect or forgotten lyrics. That's why Apple's update with time-synced lyrics is so cool, essentially turning your iPhone into a portable karaoke machine.

Passwords on Windows are stored as hashes, and sometimes they can be tough to crack. In certain situations, though, we can get around that by using the hash as is, with no need to know the plaintext password. It's especially interesting if we can manage to get the hash of an administrative user since we can then authenticate with higher privileges by performing an attack known as pass the hash.

Metadata contained in images and other files can give away a lot more information than the average user might think. By tricking a target into sending a photo containing GPS coordinates and additional information, a hacker can learn where a mark lives or works simply by extracting the Exif data hidden inside the image file.

The ability to shift between virtual reality and augmented reality seamlessly on one device is a dream of many AR fanatics, but the execution is usually fairly buggy or underwhelming.