Firefox Focus has been out for iOS for a while now, so it's about time Mozilla began porting the app over to Android. It's an amazingly private browser that protects you from trackers and ads when you're surfing the web. It blocks a wide range of online trackers, erases your browsing history, hides passwords, and deletes cookies. This essentially means ads won't be able to follow you around, in the sense that you won't see ads related to your last ten searches on Google.

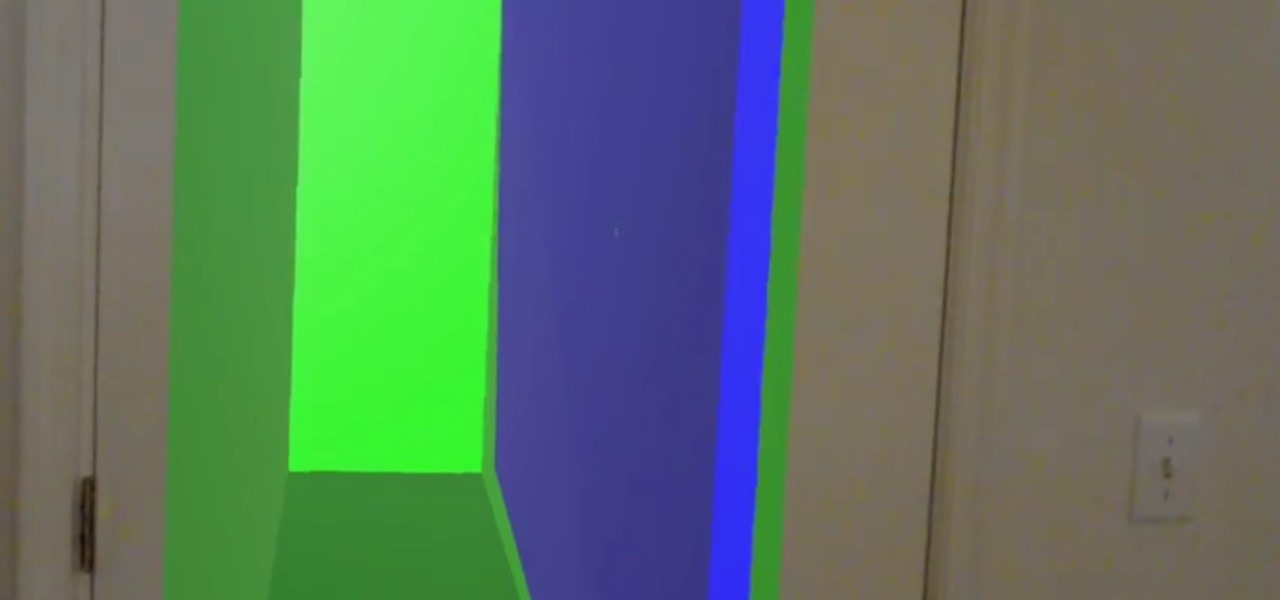
Google's working on a new mobile operating system called Fuchsia, and while we don't know much about how they intend to use it, we're now getting a glimpse at what the main interface will look like.
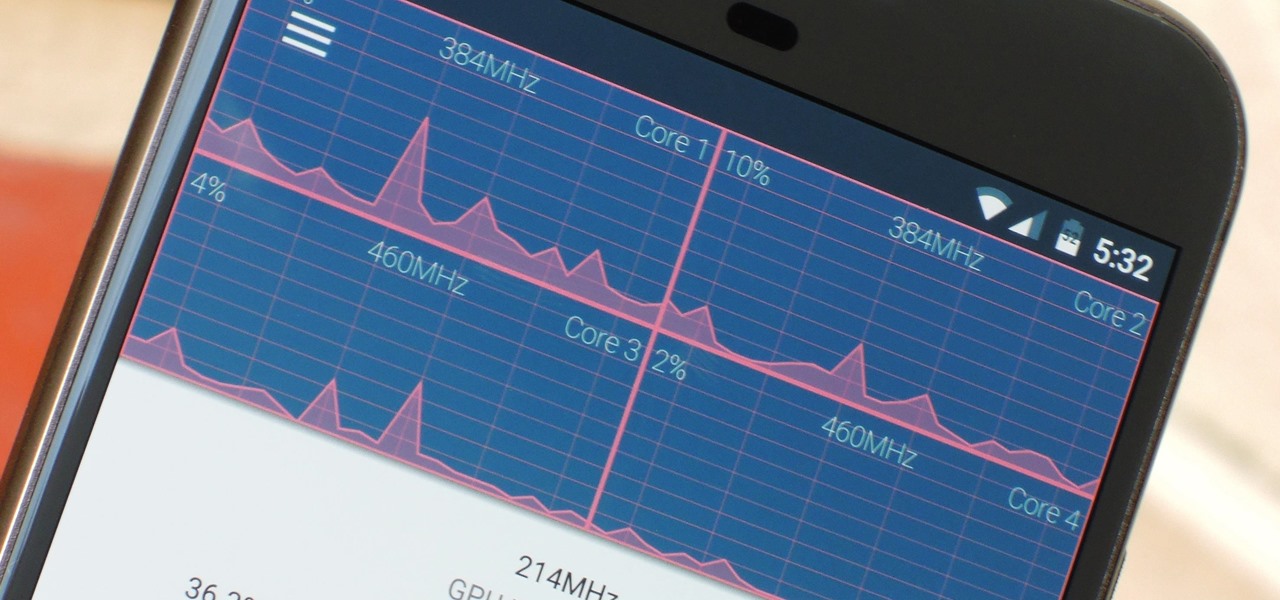
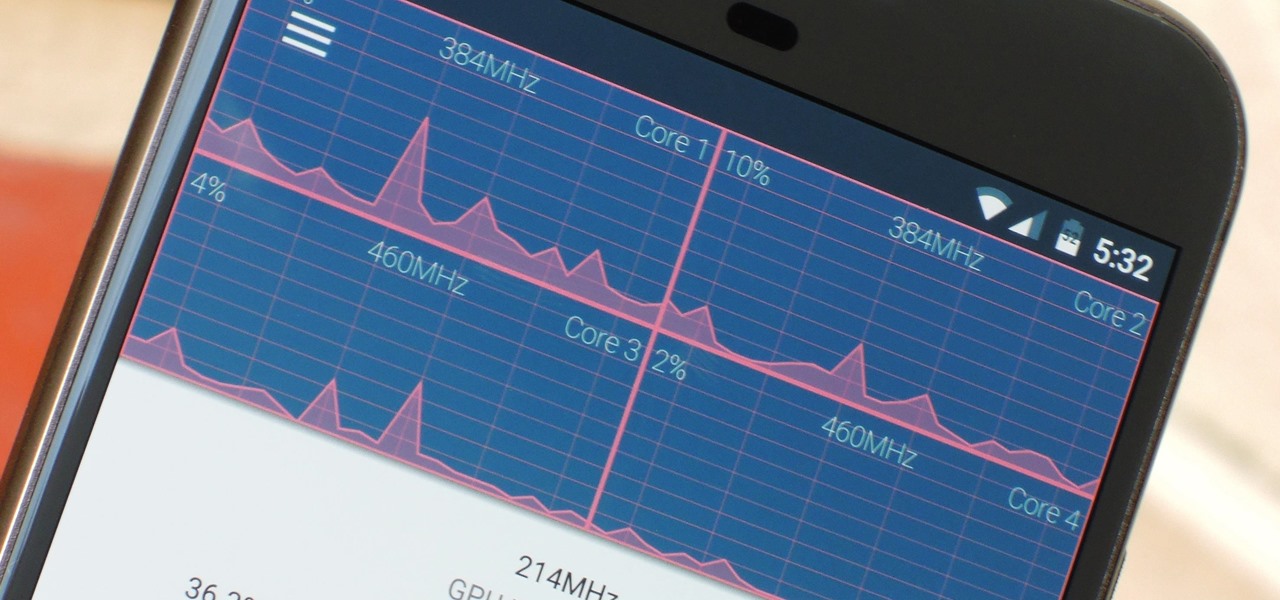
The Google Chrome browser does mostly everything well and integrates nicely with other Google services, but it's not exactly renowned for speed. With a rooted device and the aid of an app called Kernel Adiutor, however, you can make Chrome as nimble as some of the fastest browsers on the market.

Futurama: Worlds of Tomorrow has finally touched down as a soft launch for Android. Join Fry and his lovable band of interstellar misfits on a quest to rebuild New New York, traveling the stars, fighting aliens, and delivering packages while doing so. As with any city building and quest game, progressing through the game equals leveling up, which in turn unlocks new buildings and outfits to further beautify your characters and the city they live in. And the best part of all, Futurama's creato...

One thing you don't see often in the driverless industry are partnerships. When automakers are in the news together, it usually means drama. However, an important partnership between Nissan and Mobileye was announced today. One that has the potential to make driverless cars on the road better and safer.

Every Friday, Next Reality reviews the latest headlines from the financial side of augmented and mixed reality. This weekly Market Reality column covers funding announcements, mergers and acquisitions, market analysis, and the like. This week's column starts with a stock price that's performing well for one company — one that HoloLens developers should know quite well.

You may have heard that Samsung Push is an incredible service that all Android users absolutely love. For one, Push provides extremely useful notifications for Samsung apps to assist you in all aspects of your life.

Augmented reality seems to be the talk of the town lately, with everything from glasses to furniture stores prepping to implement exciting, new AR technology. Well now, it looks like even our food is getting a makeover for the augmented reality future.

Soy sauce is a sushi essential for most Americans and we don't often consider its exact origins whilst chowing down on that tuna roll.

In a race to make self-driven cars mainstream, Intel announced today that they've bought Israeli microchip technology company Mobileye for $15.3 billion, setting the stage for Intel to dominate a large portion of the driverless market.

Late last year, two surgeons from the Instituto de Ortopedia e Traumatologia de Jaraguá do Sul in Brazil started using a combination of 3D printing and the Microsoft HoloLens to help plan spinal surgeries. And now, with the rest of their team, they've successfully performed a surgical procedure on their first international patient using their 3D impression planning and augmented reality process.

Once mixed reality technology is more widely available and realistically priced for consumers, using the tech to create the illusion of a larger space, will likely be a favorite use for mixed reality in places where real-estate is expensive, people tend to live in smaller homes and work in tighter offices.

Visualization is one of the obvious commercial applications for technology such as Microsoft's HoloLens. The ability to see the assets of a project in different scales—from micro to larger-than-life—with a quick air tap will play a large part in the coming augmented reality revolution. Whether the assets are art for a game, interior design, raw financial data, or architecture, data visualization will play an important role in the future. This is due, in part, to our ability to absorb informat...

It seems that fans of the Android open-source operating system are a bit peeved by some of the choices Google has made regarding the new #MadeByGoogle Pixel phones. And with good reason. The new phones are expensive, the Nexus line is dead, and some Redditors are speculating on whether or not the Pixel bootloaders may not be unlockable at all.

When it comes to hacking guides, most are written from the perspective of a Linux user. There are a few outliers, but it's mainly Linux, which leads to the idea that Linux is the only OS that's viable for hacking. This couldn't be further from the truth. A properly set up Apple machine can do quite a bit of heavy lifting.

Autodesk offers some of the most popular software for computer-aided design (CAD) projects, which involve all sorts of 3D rendering. Their tools are clearly suited for use with the Microsoft HoloLens, but so far very little supports HoloLens development outside of Unity. Why is that?

The mighty toaster oven may be the most useful small appliance ever, whether you're a college student who needs to heat up your Bagel Bites or a professional looking for a quick way to warm up a frozen pizza after a long day. But that toaster oven is no one-hit wonder. With this smart hack, you can give it double-duty superpowers to heat up not one, but two frozen foods at the same time.

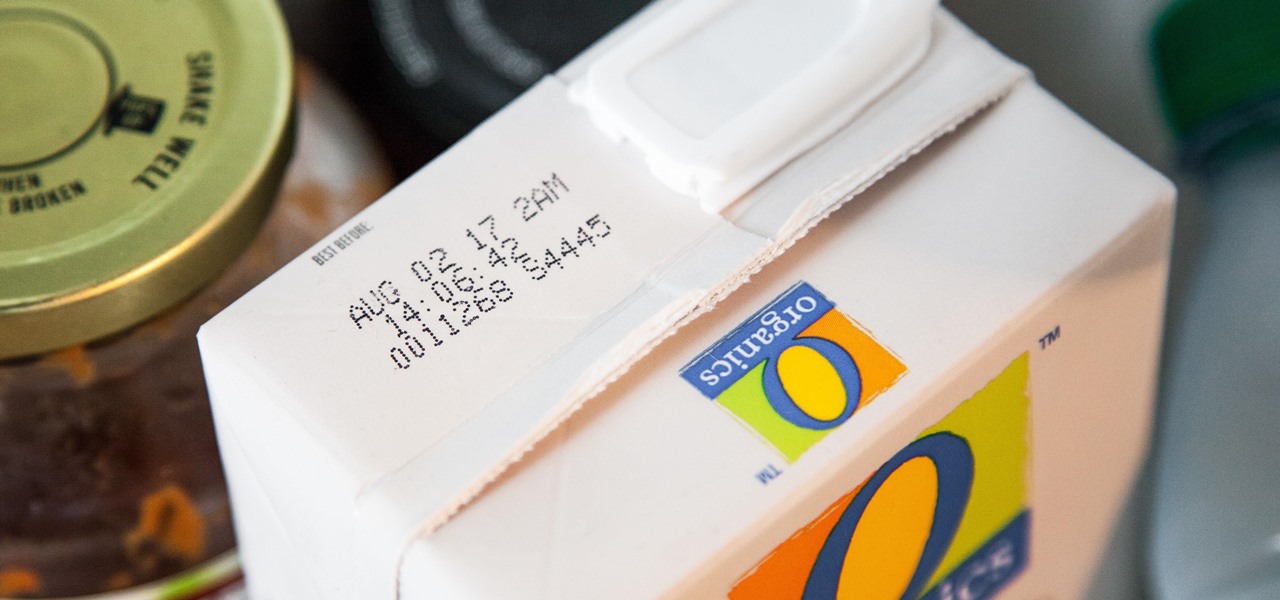
I'll admit it: I ignore expiration dates. No matter if it's a sell-by date, "best if used before" date, or even a use-by date, I don't care. I just check for signs of food decay and keep on eating.

Chris' Outrageous Cheesecake, a decedent combination of chocolate cake, brownies, cheesecake, and coconut-pecan frosting, is easily one of The Cheesecake Factory's most popular desserts. But, the price of fulfilling your cravings for this addictive treat can get up there (at about $8 a slice), and when you eat it at the restaurant you likely are limited to only one small piece.

We're already glimpsing the future when we look at mixed reality through a headset, but is the real evolution of this technology something that will exist as part of our bodies? As intense as that may sound, TechCrunch's Jay Donovan offers compelling reasons why it's not such a crazy idea:

Want to actually catch 'em all? Pokémon GO has long-teased the opportunity to hunt for Pokémon in the real world through augmented reality, but few have had the opportunity to actually see it in action.

With the FBI getting access to iPhones, and apps like Waze being used to track people's locations, you've got to wonder just how safe and secure your smartphone is... or isn't. When you consider everything you do on your phone, from taking and sharing pictures to mobile banking, keeping your information safe is a crucial step that may seem out of your hands.

Since Ive started to learn about nmap and metasploit and other tools I was learning well but I had one problem,

On Wednesday, Microsoft launched a chatbot on social media that learns from conversation, and trolls quickly taught it how to be a shameless, Nazi-loving bigot. Oh Internet, an opportunity for a Hitler joke never slips past you, does it? This Is Why We Can't Have Nice Things

In this video I'm going to teach you 5 pranks you can get away with at school or at home On April 1st.

A little less than a year after announcing "Project Astoria," Microsoft announced Thursday, February 25th, that it will end the "Bridge," which would have brought Android apps to the Windows Store.

Very often we have processes in Linux that we want to always run in the background at startup. These would be processes that we need to start at bootup and always be available to us.

Before we dive into the world of frustration, I first would like to thank whoever of the admins and mods made the folder for Raspberry Pi in the How-To's, thank you. Now with that outta the way, this article is about Metasploit on Raspberry Pi (hence the title). I should say that I ran into a error, but I think I figured what the problem is. First of all this is not on Kali Linux, but on a regular Linux OS. With that said let's open up a terminal and begin.

What's up, peeps? In this quick tutorial, we will be looking at structs, a special kind of data type.

Most people are familiar with the fact that vinegar adds sourness to a dish, in varying degrees from light acidity to puckering acid. However, vinegar can also be used in lieu of salt when seasoning the final touches to sauces, soups, and stews.

Hello fellow Null-Byters! In this "tutorial" we will be going basics of HTML. In the next tutorial, we will be going over CSS and then apply JavaScript.

Welcome back, my novice hackers! More and more, the world is turning to and adopting the smartphone platform as the digital device of choice. People are not only using smartphones for voice communication, but also web services, email, SMS, chatting, social networking, photography, payment services, and so on.

Hanukkah, also known as The Festival of Lights, commemorates the rededication of the temple in Jerusalem in 168 BCE. (Jews and secular publications, such as academic or scientific papers, use BCE—"before common era"—rather than the Jesus-centric BC, or "before Christ.")

Vegetables are perhaps the most important part of our diets, but often times they're an absolute pain to prepare. Cleaning every fleck of dirt off of dozens of leafy greens takes ages, and eliminating the more fibrous parts of certain veggies can be extremely tedious.

Hello everyone Today I will show a different way to exploit a windows machine with a reverse https payload..."wait...why https? Isn't tcp good anymore?"

T-Mobile's credit-checking system was recently hacked, and this one is about as bad as it gets. The names of 15 million customers, their date of birth and social security number, as well as driver's license numbers and additional information was illegally accessed, meaning the potential for identity theft here is huge.

Hello My Fellow Hackerzz.. This is my first How-to and i'll be updating the “Hacking Android Using Kali” to msfvenom and some FAQ about known problems from comments. So Here we GO!!

Ruby is a dynamic, general-purpose programming language created by Yukihiro "Matz" Matsumoto in Japan around the mid-90's. It has many uses but with it's flexibility, it makes a great language to write exploits in. In fact, the entire Metasploit Framework is written in Ruby! The sole purpose of this series is to teach hackers the basics of Ruby, along with some more advanced concepts that are important in hacking.

As Android's de facto virtual assistant, Google Now lets us speak directly to our phones in plain English to answer our questions and perform many basic tasks. With the app open, just say "Okay Google," then wait for the beep, and ask almost any question.

So, we all probably know that when you run a trojan made by Metasploit, nothing will appear to happen. This is a sign for me to immediately check my Task Manager, but for an unsuspecting victim, it will just seem like a broken file. It is likely that they will delete this "broken file" once they see that it "doesn't work." In order to prevent this, we need to disguise the trojan.