While privacy and security are cornerstones of Apple's ecosystem, your iPhone isn't bulletproof. Creating a strong passcode will protect you from most threats, but there exist tools that can break through even the toughest passcodes via the Lightning port. Luckily, Apple has implemented a new security feature to disable your Lightning port and keep your data safe and secure.

As with most social media platforms, Instagram can be a double-edged sword. On one hand, it's a great way to share and express yourself — but on the other, it can be just as effective at compromising your privacy. Thankfully, there are a few things you can do to protect yourself.

As the third-largest smartphone manufacturer in the world, Apple devices are a constant target for hackers everywhere. While iOS has seen fewer common vulnerabilities and exploits (CVEs) in recent years, iPhones still aren't hack-proof. Fortunately, you can strengthen your security with the help of a few apps.

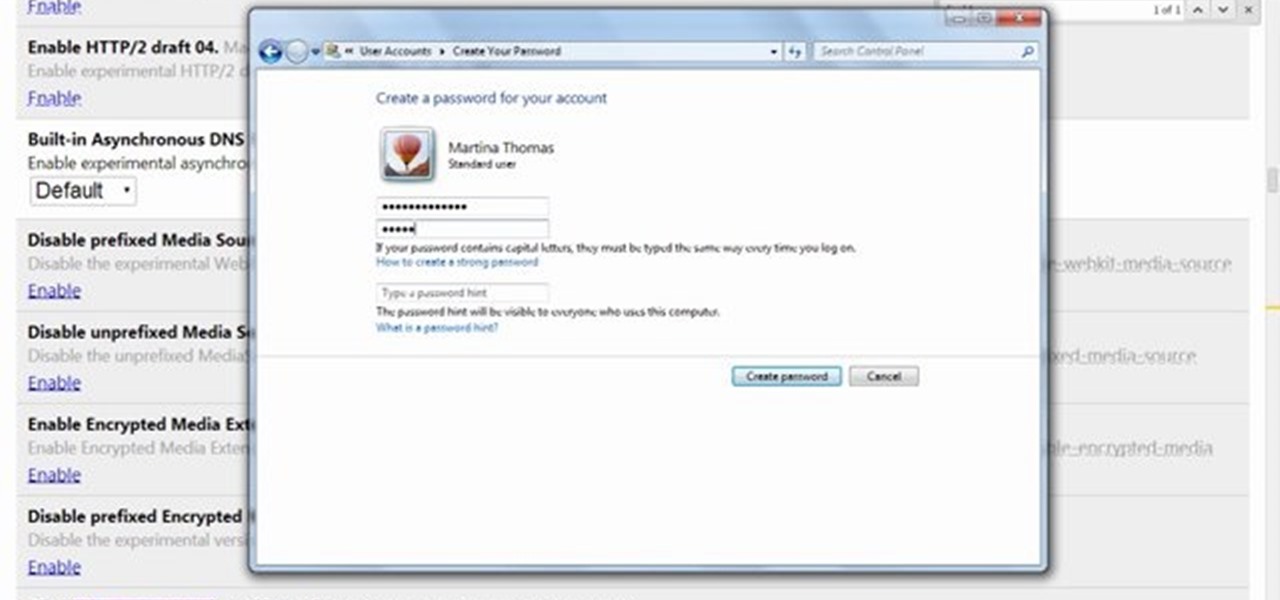
Over the years, the internet has become a dangerous place. As its popularity has increased, it has attracted more hackers looking to make a quick buck. However, as our dependency on the web grows, it becomes increasingly difficult to sever all ties. This means we have to protect one of our weakest points, the password.
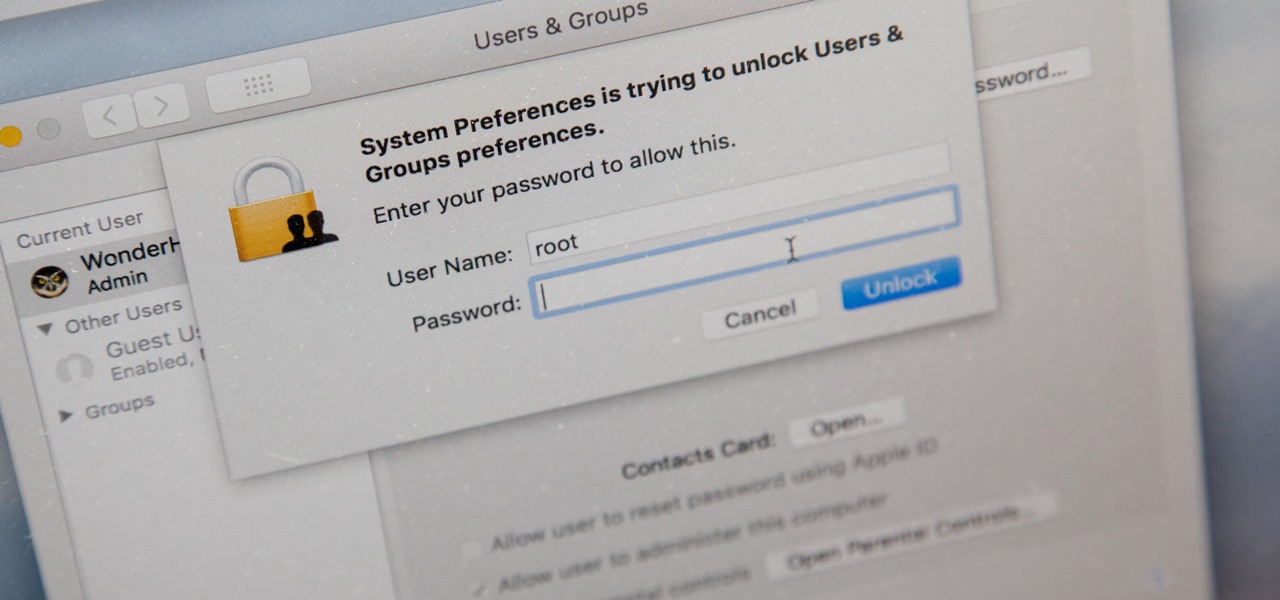
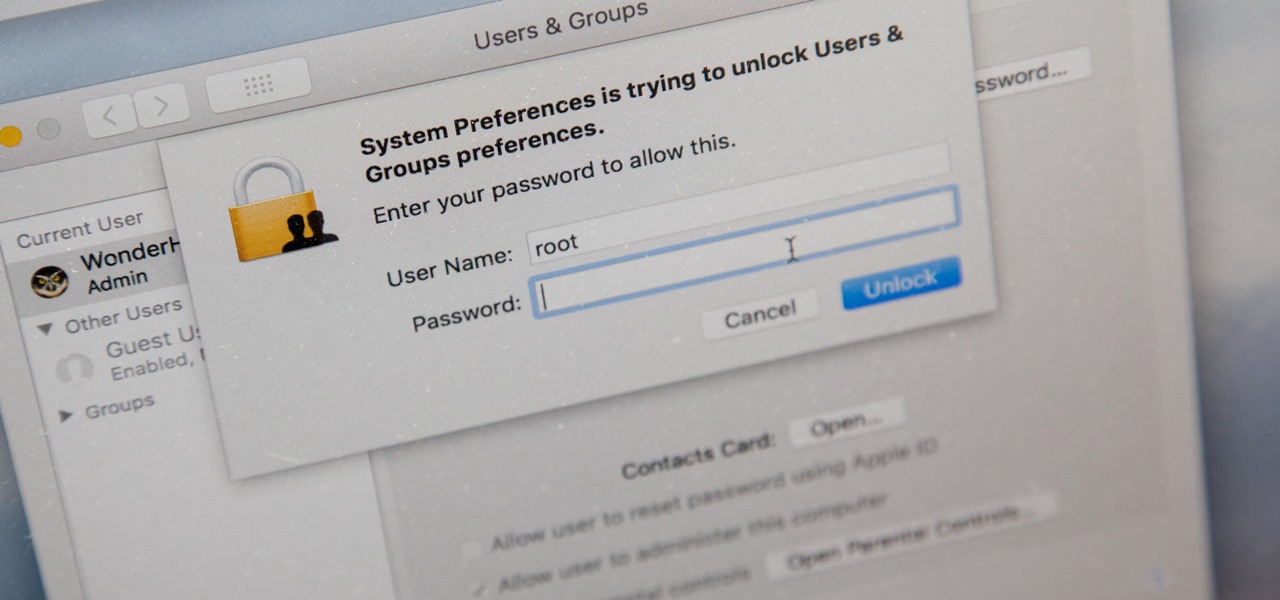
There's a new macOS vulnerability that hackers within physical reach of your computer can use to gain root access to your system and accounts. Just by using "root" as the username and a blank password on a privilege escalation prompt, someone can install malware on your computer, access hidden files, reset your passwords, and more. Root access gives them the ability to do anything they want.

Because of the way Google Play works, Android has a "bad app" problem. Google allows any developer to upload an app to the Play Store, regardless of if it works, how it looks, or whether or not it can harm users. Malware scanning happens primarily after apps are uploaded, and though Google has recently taken steps to safeguard users with its Play Protect program, you don't have to depend on them.

In my previous article, I discussed installing and configuring OpenVAS on Kali Linux. Now it's time to start using OpenVAS with the Greenbone Security Assistant to audit networks for security issues. This can be extremely helpful when you are looking for vulnerabilities or misconfigurations in a large number of hosts.

When you first set up an iPhone, you'll be prompted to create a six-digit passcode to unlock your screen and access certain system settings. If you skip this step, you can always go back and create one, which we highly recommend. Without a passcode, everything on your iPhone is accessible by anyone who gets their hands on it — nosey friends, hackers, thieves, local law enforcement, the FBI — and you don't want that, do you?

No one is safe anymore, it seems. Google's Project Zero has just uncovered how easy it is for attackers to target your phone's Wi-Fi chip, which is essentially a mini processor for Wi-Fi that detects and processes networks.

As it turns out, your Android apps are pairing together to share your data without asking for your permission first. Researchers from Virginia Tech developed a tool called DIALDroid to monitor exchanges of data between Android apps over the last three years, and what they've found is quite alarming.

If the recent "state sponsored" Yahoo hack wasn't enough motivation for users to stop using their services, the latest news about Yahoo should be. Joseph Menn, a reporter at Reuters, just revealed that Yahoo created a custom email wiretap service for the US government.

One of the best things about cold weather is soup, and there's nothing more comforting than a great chicken noodle soup. But I've often grabbed a can from the grocery store and found the chicken dried out and over-processed... and the noodles soggy and tasteless. What's worse: there's never enough of the stuff you like (such as the vegetables) and too much of what you don't (the nasty stuff I mentioned above).

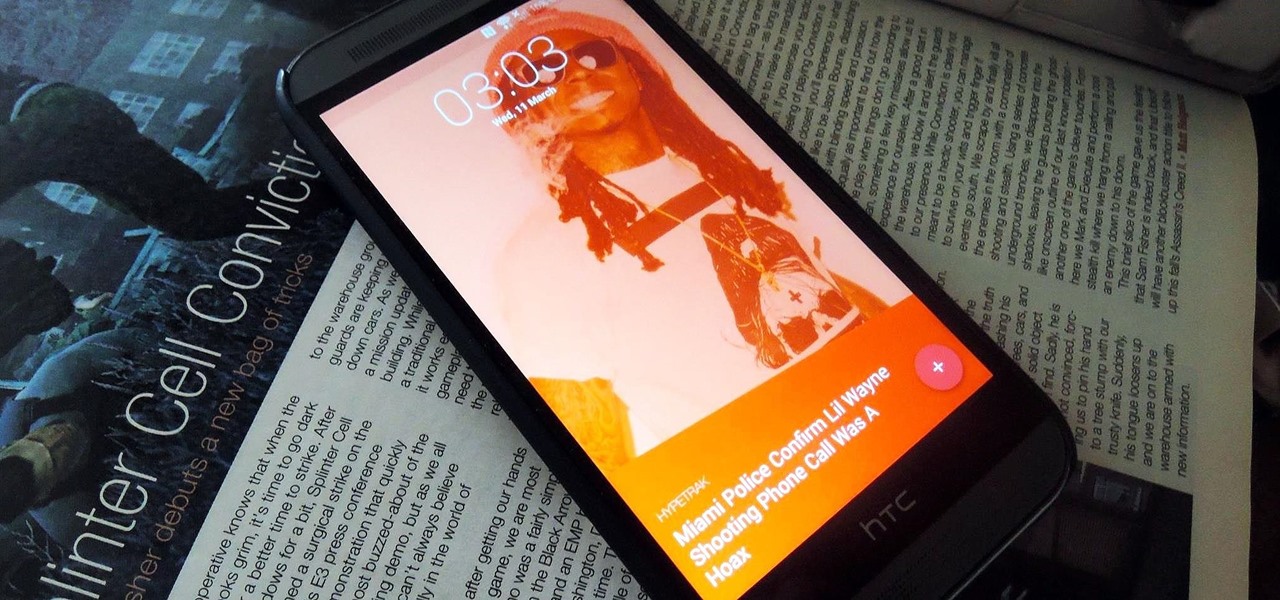
Android Lollipop still doesn't have a simple way to add a custom lock screen wallpaper, so when I came across Corgi For Feedly from developer Stan Dmitriev, I had to check it out. What sets Corgi apart from other lock screen replacements is that it connects directly to your Feedly account to display top stories from your favorite RSS feeds as your background.

The other day I was perusing my Instagram when I came upon a curious hashtag... #OnePotPasta. Intrigued, I investigated further and discovered a whole world that was previously unbeknownst to me.

This video will show you how to protect others from accessing saved password on Google Chrome. Saving account passwords in browsers are useful for time saving as well as threatening for malicious activity. This is dangerous for security. So you must protect your accounts detail from others to secure your browsing. Watch the video and follow all the steps carefully.

This video will guide you how to blur faces in YouTube video. Many times it’s needed to blur the faces of people in videos. In many sensitive cases faces are blur due to security or confidentiality reasons.

Yesterday, the Free Software Foundation published an article written by Paul Kocialkowski. A software developer for the the Android fork system Replicant, Paul stated that his organization discovered, and later patched, a "backdoor" vulnerability that existed in older Samsung Galaxy devices, including our beloved Galaxy S3s. Only problem is, it's kind of bullshit—but we'll get to that later.

David Blaine has made millions off his magic tricks and mind-bending illusions, so why shouldn't we get in on the action, too? Well, your Samsung Galaxy S3 can do all kinds of things, but magic isn't one of them...yet.

Add 1 Tablespoon chicken bouillon to the cold water in the pot. You may also add herbs/spices if you wish.

This video tutorial shows you how to make a delicious vegetarian penne pasta. Use a very large pan. Put two tablespoons of olive oil in the pan. Add four cloves of garlic chopped up. Heat the garlic over medium heat until it is golden brown. Next add one teaspoon of Italian seasoning and some crushed chilli flakes and stir for about thirty seconds. Add one sliced onion and mix the sliced onion with the other ingredients in the pan. Let the mixture cook for about one minute. Next add two bell ...

Learn Arabic in english step by step made simple with Yusuf Estes. This is a two part guide to the Arabic language.

People sometimes ask me about the IT industry here in the states. These folks are usually either trying to get into a certain field, or looking to switch or move into another one. Right now, you may currently be a Computer Science major that will be graduating shortly and are interested in the current state of IT security.
Swim Yes/ter/day /the/ tri/pod/ went/ to/ go/ swim A
24th Street Theatre Saturday Explorer Series 2012 Saturday Explorer Series 2012
Here are some words i grabbed from Porto Editora's 2011 dictionary: Dicionário da Língua Portuguesa Here they are:

I'm pretty sure every villain Batman has put away over the years makes an appearance in Batman: Arkham City. If that fact weren't so awesome, it'd be freaking ridiculous. To get the 'Sandstorm' achievement, you have to defeat Ra's al Ghul in some sort of magical sand land.

Photoshop Disasters presents their top 20 monstrosities of 2010. Wow. Take a lesson. Egyptian newspaper Al-Ahram doctors the above photo to put President Hosni Mubarak at the head of the procession. (Read more)

Or at the least, Sexy Has Been in Lisbon! There are definitely ladies (Kardashians, Hiltons, et al) that have made the journey to South Africa for more than the matches.....

Tommy and Al dive into discussing bellflowers with special guests Eli and Brian. Tommy, woodworking master, demonstrates how he made the lines on the table leg. He then reviews how to make the bellflowers and Eli cuts them. Afterwards, Tommy and Brian discuss their furniture work so far.

Racial Profiling at Boston Airport, Officials Say - NYTimes.com. Officers in an airport program intended to spot telltale mannerisms of potential terrorists say the operation has become a magnet for racial profiling. » The Next Election: High Stake Outcomes Based on Non-issues.

» Video Blogger Documents Expanding TSA expansion. The TSA is continuing its expansion from airports to train stations and other modes of transportation. On Monday, an independent journalist posted a video documenting TSA agents setting up shop at Union Station in Chicago. Obama Calls on Romney for More Transparency - What about himself?.

In this video tutorial, viewers learn how to password protect their files. This task can only be done on a Windows computer. Begin by creating a Microsoft Word document. Simply right-click on the desktop, go to New and select Microsoft Word Document. Then double-click on the document and create your text document. Now to save it, click on File and select Save As. Name the file. Now click on the Tools drop-down menu and select Security Options. Then type in a password, reconfirm the password a...

In this Computers & Programming video tutorial you will learn how to encrypt a D-Link router with WEP password protection. First you connect to your wireless network. Open your browser and type in http://192.168.0.1. Type in your base station username and password and press OK. Under the SETUP tab, select WIRELESS SETTINGS, scroll down to 'Wireless Security Mode' and select 'Enable WEP Wireless Security'. Scroll down to WEP. Under WEP Encryption pull down menu select 128Bit. Now create a pass...

In this video tutorial, viewers learn how to set and encrypt a NET-Gear router with WEP password protection. Begin by opening your web browser and go to the router website: Router Login.. When the Prompt window appears, type in your router user name and password, and click OK. In the sidebar, under Setup, click on Wireless Settings. Once again, type in your user name and password, and click OK. In the Security Options, check WEP (Wired Equivalent Privacy). Then select the Pass-phrase box, typ...

Amazing clip from Jeremy Clarkson's Motorworld television series, which aired on the BBC back in the mid '90s. Seikh Hamad bin Hamdan Al Nahyan of the United Arab Emirates created this incredible monster, which was modeled after the '50s era Dodge Power Wagon.

This video shows us how to make a traditional, true carbonara. First, the video points out that people often use bacon in their caronara, but you should really use guanciale, which is a cured pig's cheek. Put the pig's cheek in a nice and hot pan and get it crispy. The next step is to cook the pasta. Then, you put one whole egg and one egg yolk into a bowl and whisk it up. Mix about three tablespoons of Pecorino cheese as well as three tablespoons of parmigiano cheese with the eggs, plus some...

Not sure how to enable javascript on your computer? Follow these steps to enable all the functionality javascript provides.

Mmm... fettuccine alfredo. If you're a fan of cream sauces, one bite of this cheesy, decadent dish and you'll be hooked for life. Serve with a salad and tell yourself it's healthy! Enjoy!

Thanks to the Freedom of Information and Privacy acts, we’re all entitled to see what the FBI has on us. Learn how to get your hands on your FBI file.

This seafood recipe comes to us from Landersdorfer & Innerhofer in Munich. Follow along with this cooking how-to video to learn how to make skate fish with sauteed fennel and tomato. This is great recipe for incorporating fish and veggies into your diet.