Keeping prying eyes off your device isn't always the easiest thing to do, especially once you lend somebody your phone to make a call. Seems that whenever someone is scrolling through your pictures or checking out your new phone, they always end up somewhere you don't want them be. You could always hover over their shoulder to make sure they're not getting into your texts or photos, but that isn't always possible.
There are countless lock screens you can apply to your Android device, but very few offer more than just quick access to apps or advanced security functionality. Since you probably unlock your device a gazillion times every day, why not use this to your advantage and let it teach you something new?

Lock screen apps are a dime a dozen, but every now and then one pops up that defies expectations. We've already covered some good ones for the Samsung Galaxy S4, including Picture Password Lockscreen (which gives you secret unlock gestures), SlideLock (which improves notifications), and TimePIN (which gives you a more clever PIN).

Figuring out someone's password, pattern, or PIN isn't very difficult—simply watching over their shoulder or following the oil marks left across their screen is enough to figure them out and bypass whatever lock screen security they have.

Some of my favorites hacks are the ones that speed up the process of accessing my favorite and most-used apps. So, in this softModder guide, I'll be showing you a super fast way to open those apps straight from your Samsung Galaxy Note 3's lock screen.

With the the general computer users understanding of Information security rising (at least to the point of not clicking on unknown links), and operating system security getting better by default. We need to look for new and creative ways to gain a foothold in a system.

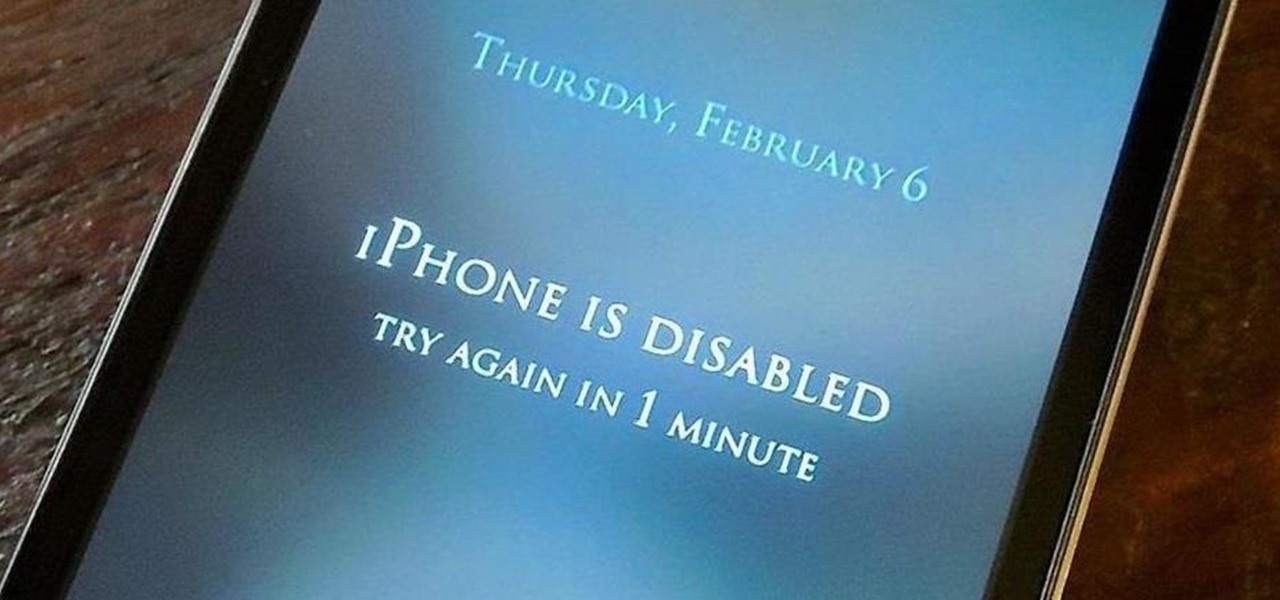
If somebody really wants to gain access to your iPhone, they'll get in. Phone thieves (and mischievous friends) can easily figure out your passcode just from looking over your shoulder or tracing over the oily smudges on the screen. And if you're using popular passcodes, birthdays, and addresses on your iPhone, you might as well disable lock screen security entirely.

The lockout feature in iOS 7, which securely locks your device after a few incorrect passcode entries, can be a real pain in the ass sometimes.

Let's be honest for a second; we all have sensitive material on our phones that we wouldn't want anyone else to ever see. Maybe it's to protect ourselves or someone else, or maybe it's none of your business why I don't want you to see pictures of my bachelor party. Regardless, sometimes we need to keep things hidden and safe.

If you haven't heard yet, Google made it possible a couple months ago for every Android user running 2.2 or higher to track his or her smartphone or tablet using their Android Device Manager service. It's a super easy way to track, lock, and secure erase your Android device from the web without ever having to download a third-party application, like Droid Finder, since it occurs in the background via Google Services.

#FOMO. If it bugs the living hell out of you that you don't know what that means, you're presently FOMO, as in you've got a Fear of Missing Out.

Samsung just concluded their live unveiling of the Samsung Galaxy S4! A more in-depth look can be found here.

Even though iOS 6.1 was only released a couple of weeks ago, hackers released evasi0n a couple days after. Evasi0n, the only iPhone 5 jailbreak currently on the market, is the most popular jailbreak in history—with nearly 7 million iOS devices already hacked in the mere four days after its release. Well, now it seems that iOS 6.1 is being taken advantage of again, this time with a simple exploit figured out by YouTube user S1riOS6, which lets you bypass the lock screen on an iPhone running iO...

Having all of your stuff in the cloud is super convenient if you want to access it on multiple devices, or if you want a backup in case it gets lost or wiped. The biggest downside with services like Dropbox, though, is security. With everything sitting there in one place, the last thing you want is for someone to break in.

UPDATE: A patch to fix the exploit has been released. Download it here.

Even though we all know it's a bad idea, a lot of people still use their browser's store password function to keep up with all their accounts. While convenient, this shortcut also makes their passwords very easy to find if you have access to the computer they're stored on.

If you use Ubisoft's uPlay browser extension, you should probably get rid of it right now. An Information Security Engineer at Google discovered that the plugin has a hole in it that allows programs to be installed through uPlay, essentially letting anyone who feels so inclined to take over your computer. How the Exploit Works

It used to be that you only had to worry about maids rummaging through your belongings in your locked hotel room. But now anyone with 50 bucks of hardware and some programming skills can hack their way in—as long as it's locked by keycard.

Most of the time, asking to borrow someone's car will elicit a really long string of excuses. But unlike letting your buddy use your car, which usually gets you nothing more than an empty tank, GM has found a way to make car sharing beneficial for everyone involved. If you're one of the 6 million people who have a GM vehicle that's connected to OnStar, you're in luck: according to an OnStar employee, you can make up to $1,000 a month just by letting other people rent out your car when you're ...

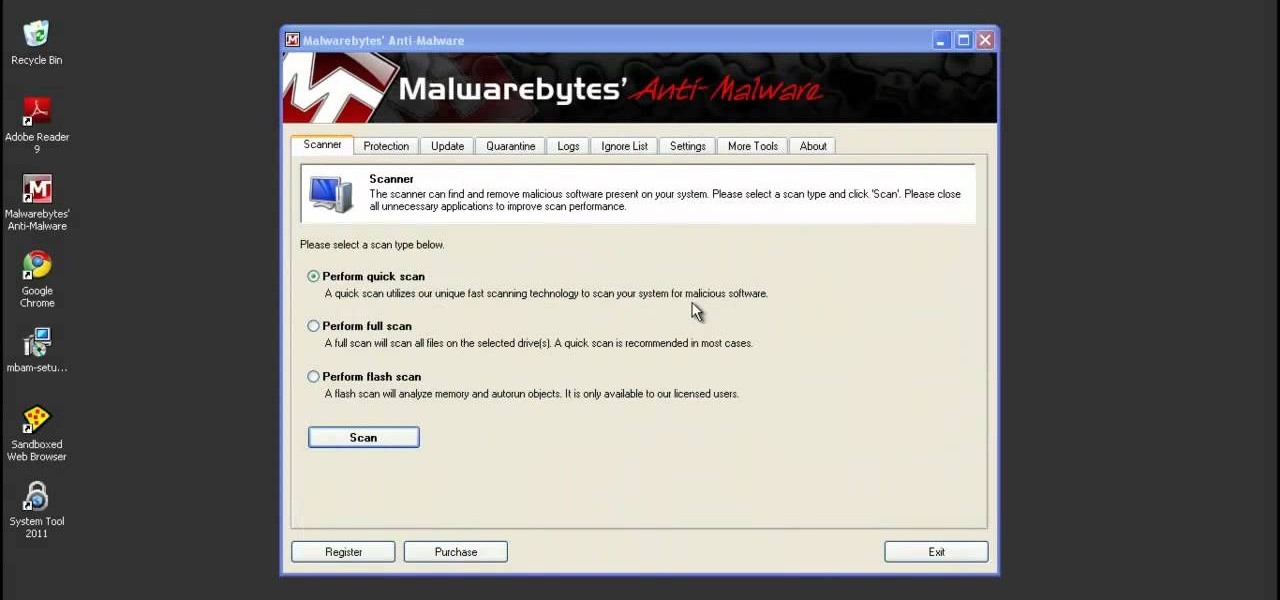
System Tool and System Tool 2011 are the most widespread fake-antivirus rogues on the internet today, infecting countless machines. This video will teach you how to uninstall both warez completely, returning your computer to blessed normalcy.

The iPad's got some stiff competition these days, especially from Android, who plans to invade the tablet market with their high-end mobile operating system. And they're off to a good start with the Samsung Galaxy Tab, available from AT&T, T-Mobile, Vodafone and Verizon Wireless, along with other carriers.

What's better than one prank? Five pranks! This video from the notorious Kipkay provides five fantastic, funny, and facile pranks to pull off on your friends and family… maybe even your enemies.

Do you remember "The Heist" from episode 21? Well, the sequel is even more unfair than the original! Check out this video if you want to stump people with a trick called "The Heist II." For this trick, you need only a few simple supplies: a match, a cup, and a nickel.

Systm is the Do-It-Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. They will help you avoid pitfalls and get your project up and running fast. In this DIY episode, see how to build a firewall from a junk PC to protect networks.

SQL injection is a common web application attack that focuses on the database backend. WebGoat is a deliberately insecure J2EE web application maintained by OWASP designed to teach web application security lessons. I plan to use WebGoat for a few future videos. This first WebGoat video will show the basics of installing WebGoat and doing two of its SQL injection lessons. Hack websites with SQL injection and WebGoat.
In a riveting interview on TruNews Radio, Wednesday, private investigator Doug Hagmann said high-level, reliable sources told him the U.S. Department of Homeland Security (DHS) is preparing for “massive civil war” in America.

As hard as you try to protect your valuable information with strong passwords and anti-doxing measures, there's nothing you can really do when someone else gives up your goods. And that is the case with the recent Global Payments breach.

US Secretary of State Hillary Clinton lashed out against Russia and China after a meeting in Tunis. The meeting aimed to increase pressure on Syria to stop its bloodshed. Hillary represents the US as an ally for the rebels.

Merry Christmas all! I hope you are all having a very wonderful day!

This article relates to changing the settings in Adobe Flash so that you can improve your overall computer security and privacy. Changing these settings might have a negative performance impact on your computer - but it is worth while.

Security awareness seems to be a hot topic these days on the web, with developers making apps and devices that can hack networks and machines with just a few clicks. But these applications aren't only exploiting security flaws in systems and networks, they're being used by amateur and wannabe hackers who want to have a little fun, but don't want to learn how to actually "hack" anything.

Social Profile Change the privacy settings on your social profile (Facebook, MySpace, Friendster, Twitter, etc.) so that the following information can't be found by a random person who you didn't accept you as a friend:

In the wealthy oil man's world of Arabian camel racing, the tradition of using child jockeys has been replaced with the use of small robo-jockeys in recent years. But after finally ridding the game of the mistreatment of children, the sport is now under scrutiny again. The Dubai police have discovered a new feature illegally added to the torturous, whip-endowed robots: hidden stun guns.

So the cooking of the bird doesn't lie on your shoulders this Thanksgiving. Lucky. But before you relax too much, there is a wild card- you never know who will be handed the carving knife. Below, five handy infographics for carving a turkey like a pro.

In January of this year, I went to Kuwait with director Fawaz Al-Matrouk to complete photography for the film "To Rest In Peace". We shot the majority of the film in Southern California, duping air force bases, homes, and beaches for authentic Kuwaiti locations. Because traveling was a significant theme for the film, we went to the small, nearly deserted island of Failaka (about 20km off the mainland). Captured by the Iraqi army and deserted by its citizens almost 20 years ago, this island wa...

Wired posts a gallery of the original models of now iconic devices, with some fun tech-fetish facts. Did you know the first cell phone weighed a whopping 4.4 pounds? Or that the world's first super soaker was invented completely by accident? Examples below; click through for Wired's complete gallery.

As sports fanatics, we know how central instant replay is in professional sports. The NFL proved it to any non-believer many years ago. Now the rest of the world is playing catch up. Yes, I am pointing my fingers at the FIFA idiots who run the World Cup. (UK was robbed against Germany). And baseball... Selig should apologize to Armando.

So, as if it wasn't obvious enough, money is playing a big role in this World Cup, not just by how much will be injected into the South African economy (also dubbed as the "World Cup Bump"). Here's a brief look at what some teams stand to make depending on how far the make it.

When your opponent throws down "AA", you tell them no abbreviations, but alas... it's not. They build "ZA" on the board for 64 points, and you say it's slang, but it's in the dictionary. Next is "EF", and you let them know that spelling out letters is not allowed and ridiculous... but it's totally legit.

In this video tutorial, viewers learn how to change the default password on a NET-GEAR router. Begin by opening your web browser and go to this site: Router Login. When the Prompt window opens, type in your router's user name and password, and click OK. In the sidebar, under Maintenance, click on Set Password. Now type in the old password, new password and re-type the new password once again to confirm. Finish by clicking Apply. This video will benefit those viewers who use a NET-Gear router,...