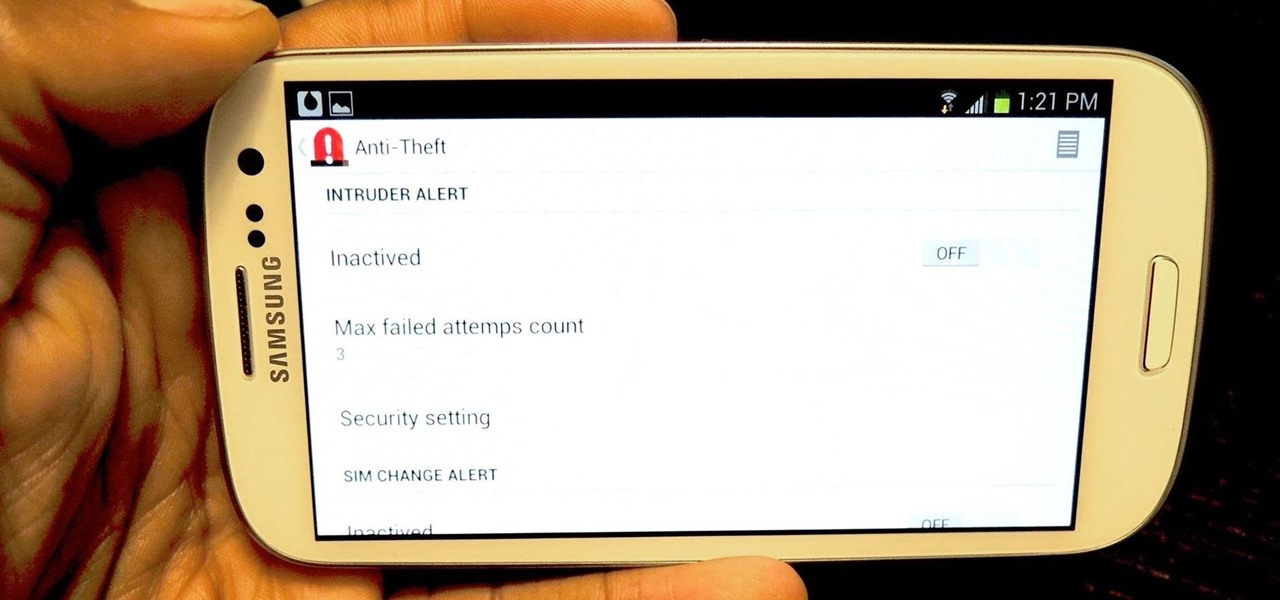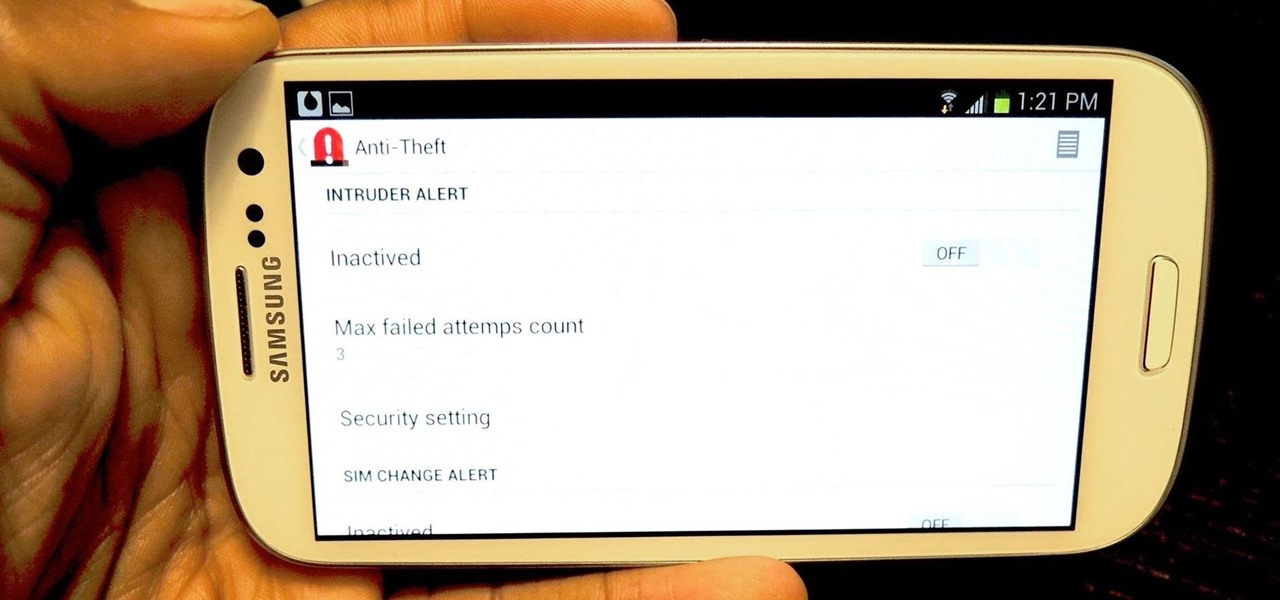
I love surprises. Surprise parties, surprise visits, surprise Patrick... But there are times when a surprise is the last thing you want, like reaching into your pocket to find that your Samsung Galaxy S3 is not where it should be.

Welcome back, my nascent Hackers! In my last blog, we looked at a passive way to gather information necessary for a hack. The advantage of using passive recon is that it's totally undetectable, meaning that the target never knows you're scouting them and you leave no tracks. The disadvantage, of course, is that it's limited to only some websites and not entirely reliable.

Welcome back, my hacker novitiates! Many of you have written me that you're having difficulty installing and running Metasploit on a variety of platforms. No matter if you're using Mac, Linux, or Windows, I strongly recommend you install BackTrack as your secondary OS, a virtaulization system, or on an external drive. This particular Linux distribution has many hacking and security tools integrated—including Metasploit.

I recently had my iPhone stolen at public park and did everything I could to locate it, but with Find My iPhone disabled (I know, what an idiot) and no exact address to give to the police, I had about a .00000001 percent chance of getting it back.

Last weekend, some unlucky Gmail users inadvertently had their email accounts wiped out. Actually, it was 0.02 percent of all Gmail users—or roughly 40,000 of the 200 million who use the email service, due to an "unexpected bug" which affected copies of the data. Gmail does make backup files of everything, so eventually everyone will reclaim their email history. In fact, as of yesterday, Google has successfully restored all information from their backup tapes and has started returning everyon...

Outdoor lighting is an important part of your landscape. It's serves multiple purposes, but wouldn't you want to make sure you're getting the right lights, for both daytime and nighttime use? Lowe's has the answers to help you plan and install outdoor lighting in your yard.

Quickly turn a profit during a combat mission by ratting - killing NPC enemies who spawn in asteroid belts. The difficulty of rats depends on how secure your system is - the lower security, the harder the rats are to kill. This tutorial shows you the best way, as a new player, to earn money by ratting.

In order to set up a secure wireless router, you will need to use the security that is available with your wireless routing. You will need to change the default ID names and password on your computer. Try to make sure that your passwords are difficult. Also, turn on the encryption: e.g. WEP.

You don't want anybody to have access to your cell phone. Nobody. Well, instead of the standard unlock mechanism, the one anybody can unlock your cell phone with, the Motorola DROID, and Android enable mobile device, allows you to create your own unlock pattern, secret to anyone else, which wakes it from sleep mode. Best Buy has answers. The Best Buy Mobile team explains how simple it is to set up a secure lock on a Motorola DROID cell phone.

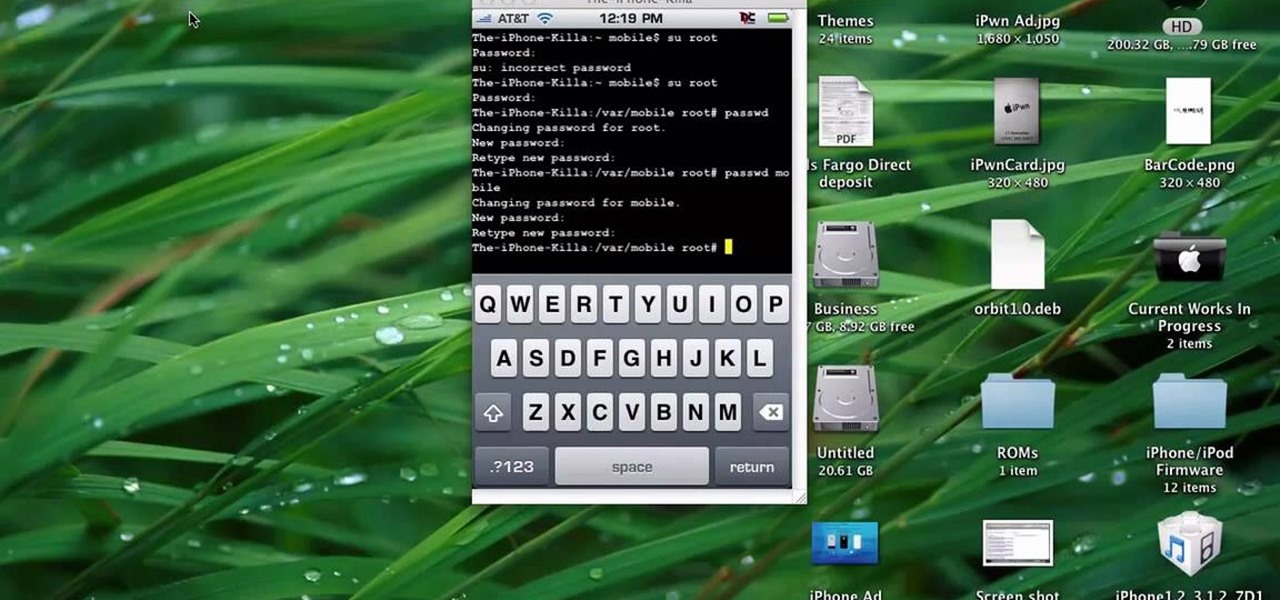
This quick tutorial runs you through a fast and easy way to make your iPhone or iPod Touch more secure. However the best security is abstinence. Just don't run the programs that leave your devices vulnerable unless you need them.

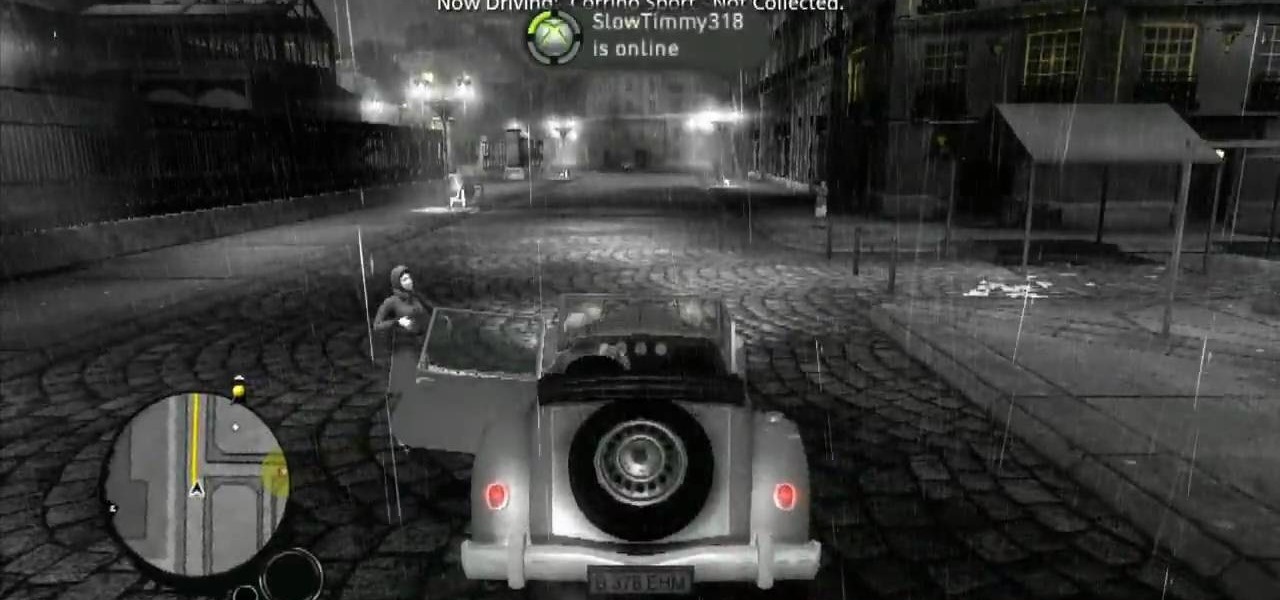
Make your way through The Saboteur for the Xbox 360. In the eighth mission in Act 1: Doppelganger, the ambassador will rendezvous with a German official near the Place des Vosges. Security will be tight around the ground level, but you should be able to find a vantage point among the rooftops. For more info, watch the whole gameplay.

So you want to party with celebrities. Whatever you do, don’t cry. You won’t just look silly—you’ll look unstable. Follow these steps to get you one step closer to hanging with the stars.

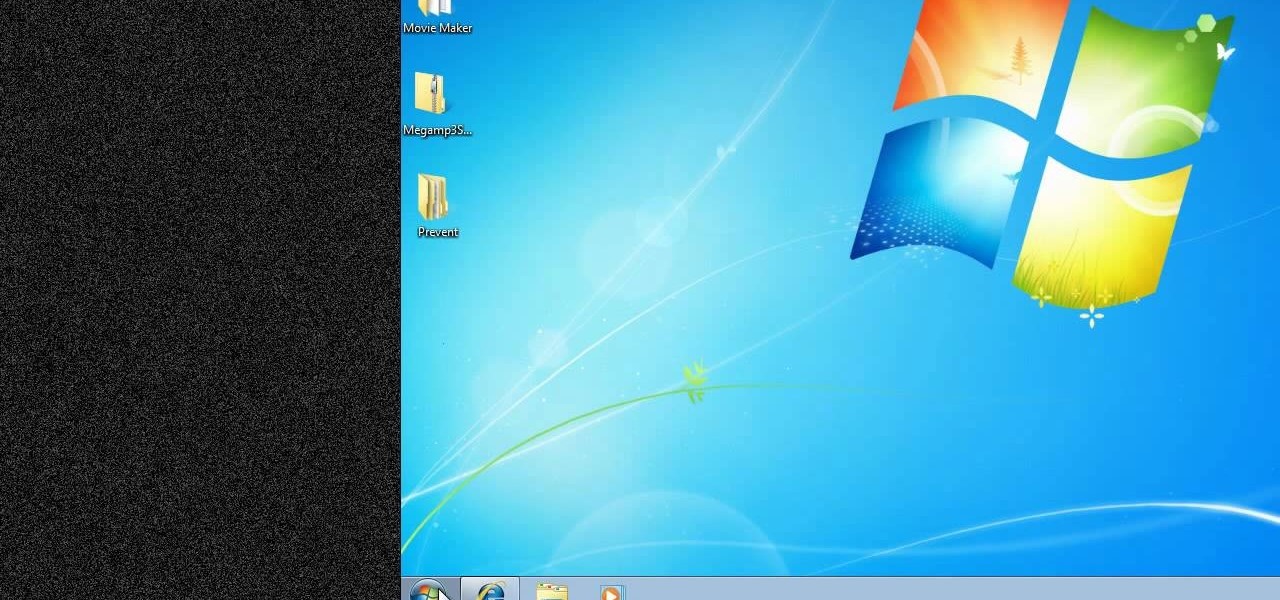
New to Windows? No problem... here's a beginner's video tutorial that will teach you how to prevent cut, paste, copy, and delete on Windows files.

Check out this 2 part walkthrough of RE 5 Chapter 2-3 Savanna. This Resident Evil 5 Walkthrough is being played on Veterans Difficulty in Co-Op mode with Chris Redfield being played by Reule and Sheva Alomar being played by RavenVanHelsing.

Resident Evil 5 (RE 5) is the sequel to 2005's Resident Evil 4. This game guide shows you BSAA emblem locations, treasures, and includes strategies for all 6 missions and boss fights.

Check out this walkthrough of Residential Evil 5, Chapter 6-2: Main Deck. Resident Evil 5 (RE 5) is the sequel to 2005's Resident Evil 4. This game guide shows you BSAA emblem locations, treasures, and includes strategies for all 6 missions and boss fights.

The HP 2710p business notebook has a number of innovative security tools to make sure your data stays where you want it.

Chicago cops, the FBI, Homeland Security, Secret Service and a large number of unnamed others have established a high-tech secret command center to surveil people exercising their First Amendment right in Chicago as the NATO war council unfolds this weekend.
Soon, Americans may find every private email they write could be opened, copied and inspected by government snoopers. The latest cyber security bill – called CISPA – has passed the House of Representatives, coming a step closer to becoming law. President Barack Obama has threatened to veto the act, if it goes through in the Senate. He cited civil liberty concerns as the reason for his threat. CISPA has raised a massive outcry with internet users and freedom activists, who say it’s a hard hit ...
National Security Agency whistleblower William Binney reveals he believes domestic surveillance has become more expansive under President Obama than President George W. Bush. He estimates the NSA has assembled 20 trillion "transactions" — phone calls, emails and other forms of data — from Americans. This likely includes copies of almost all of the emails sent and received from most people living in the United States. Binney talks about Section 215 of the USA PATRIOT Act and challenges NSA Dir...
Monday 27 February, WikiLeaks began publishing The Global Intelligence Files – more than five million emails from the Texas-headquartered "global intelligence" company Stratfor. The emails date from between July 2004 and late December 2011. They reveal the inner workings of a company that fronts as an intelligence publisher, but provides confidential intelligence services to large corporations, such as Bhopal’s Dow Chemical Co., Lockheed Martin, Northrop Grumman, Raytheon and government agenc...

Here's a trophy guide for Payday: The Heist that requires excellent teamwork. To get the 'No Photos' trophy, you'll need to take out all of the security cameras in the level First World Bank within ten seconds of drawing your weapon.

About two months ago, the massive Gawker Media hack was a wake up call for many web denizens on the importance of proper password security. Data analyzed by the Wall Street Journal revealed the three most popular passwords recovered from the hack were downright idiotic—123456, password, and 12345678. If past events weren't motivation enough for crafting a strong password, then maybe a racy 8-bit stripper is. Naked Password is a jQuery plugin by Platform45 that rewards you with an accelerating...

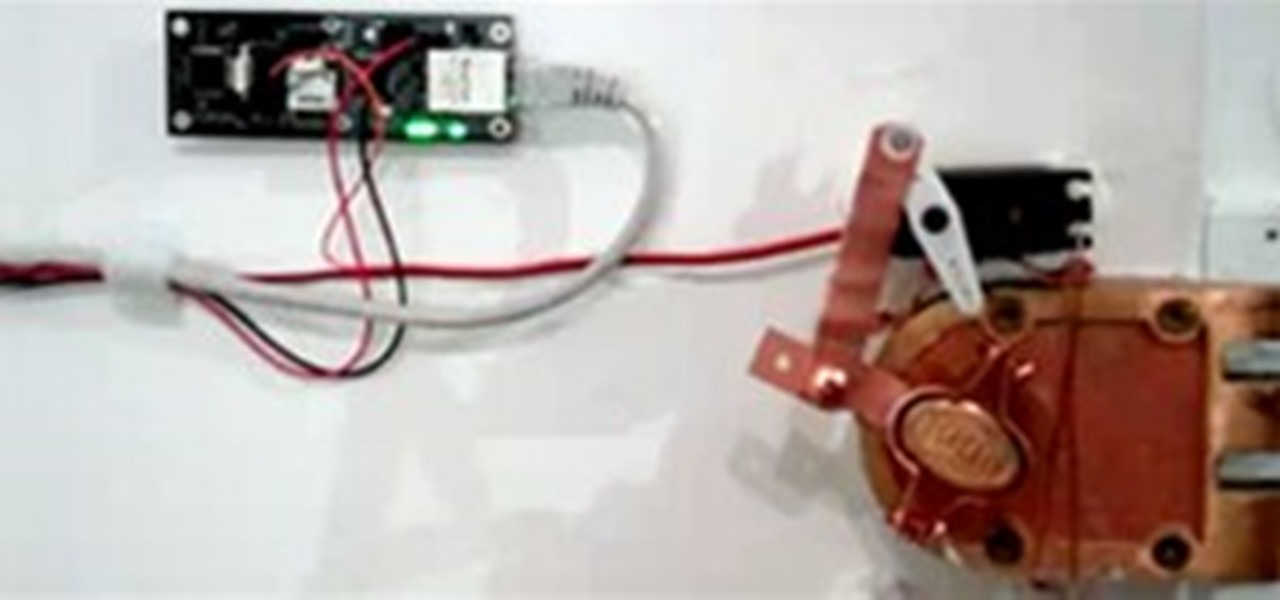
When choosing a security system for the office, Billy Chasen decided to ditch the traditional lock & key barricade for something a little more 21st century. He hacked together a device that uses a web server, servo motor and some parts from Home Depot to enable locking & unlocking via text message. Chasen maintains a list which gives access to green lit office workers, who enter by simply texting "lock" or "unlock"... and voilà, open sesame.

The German police have their panties in a bunch over a highly inflammatory sculpture of a urinating policewoman by artist Marcel Walldorf. Entitled "Petra", the hyperrealistic figure depicts a female officer crouched, peeing with buttocks exposed. The most chilling detail is her riot baton casually propped on the wall next to her.

Up for auction at Heritage, JFK's crusty old birthday cake, presented to him at his 45th birthday party in Madison Square Garden back in 1962. Marilyn Monroe performed her legendary “Happy Birthday, Mr. President” at this very event.

WonderHowTo loves paper artillery. More sophisticated in construction than Box Wars, plus tense on-camera drama to boot, Cardboard Warfare is a tight homage to the paper gun. Not completely sold on the acting, but I'm really digging the mise-en-scène. Says creator Clinton Jones, aka, pwnisher:

In this tutorial, we learn how to find an IP address in Hotmail. First, open up your Hotmail in box and right click on the email you want the IP address of. Now, select "view source" and find where it says "received: from" or "X-Originating IP". This will give you the exact IP of where this email was sent from. You can use this for any email you receive and the best part is that it only takes a few simple clicks of the mouse and a few seconds out of your day! This can help you bump up securit...

Congrats to MuscleNerd, the first to jailbreak the almighty iPad. Via DVICE:

Welcome, everyone! While Linux distributions are almost always used for exploits, security, pentesting and other stuff covered in Null Byte, knowing the Windows Command Line (or Command Prompt) is a useful skill that can help you in various ways, such as using exploit programs made for Windows or using the command line on someone else's Windows computer.

Hey Everyone! Welcome to my post. We have seen a numerous GUI Tool in kali linux. Armitage, wireshark, Burpsuite etc,. Lets see an another GUI tool.

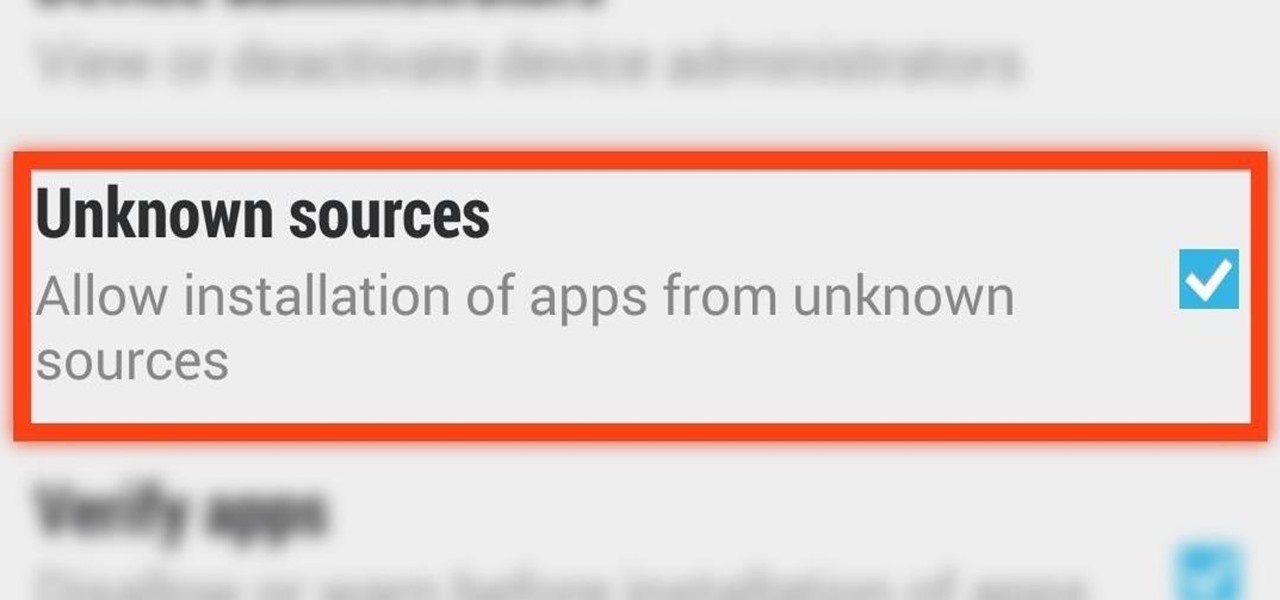
When you try to install third-party applications (meaning apps not found in the Google Play Store) you'll be met with a warning that notifies you that your device currently blocks installations not obtained from the Play Store. Enable Unknown Sources

Installing applications that are not on Google Play requires you to enable a certain permission in the settings so that the whole process goes down smoothly. If you're downloading one of these third-party applications (in the form of an APK), you'll need to enable Unknown sources.

There are plenty of times where you'd want to install an app, but either the developer or Google has taken the app off the Play Store (like with Flappy Bird). To bypass the need for Google Play, you can just download the app's APK from a reliable source on the internet and install it manually.

Here's one of those modding must-haves that's basic, yet easy enough to forget about. If you're going to install apps that don't live in the Google Play Store, like the Google Experience Launcher, the OnePlus One lock screen, or something that needs root privileges like the Xposed Framework, you need to turn on this setting.

When i went to class today, a good friend asked me a question. He wanted to know what the best hacking software was to basically do everything. What i told him was this: Well there isn't an "Ultimate" tool boot there are a number of tools which deserve a "Medal." So what i'm trying to say here... What are some of the best hacking tools available right now? For starters i created a list with some of the tools.

Do you have a junk drawer full of expired gift cards, membership cards, school ID cards, debit and credit cards, and other sturdy rectangular pieces of plastic you no longer use?

When you really think about it, registering for any website is a little scary. Not only do they now have your name, email address, and a username/password combination you might've used elsewhere, but certain sites and services ask for quite a bit more private information. From phone numbers to addresses to birth dates and more, that company now has all of your information stored.

Prank is played on Ehren: Have Johnny knoxville and Danger Ehren on Jimmy Kimmel with the premise that Johnny is going to do some trick with a gun. When Johhny and Ehren are on the set, have a reason for Johnny to give the gun over to Ehren and have Johnny tell Ehren to shoot it at Jimmy with the idea that the gun isn't loaded. The gun will fire a blank and Jimmy will have a blood packet in his chest go off and will pretend to have really been shot and then die. Soon as this happens, Ehren is...

Papercraft guns are the new origami. The new origami for boys, that is. WonderHowto and YouTube are chock full of paper gun tutorials. Many models are simple, but some are impressively realistic, not to mention functional. My personal favorite (unfortunately no tutorial) is the homemade Desert Eagle .50 cal by YouTube user Changmobile.