Ann Arnoult explains why making Pilates exercises with exercise bands is good for your body. It adds resistance, that increases your flexibility and motion. You can work your al body using it. There are demonstrations of exercises, using the band. For working your legs and back, lie down, put the band on your feet and start exercising, by bending the knees. The seconds exercise is by sitting on the floor, straightening your legs. The third exercise: you have to kneel on the floor, put the ban...

Chef Keith Floyd is in Cornwall to cook a portuguese dish al-fresco at a Naval Base. Delicious meal idea using pork, bacon, mussels, scallops, prawns, and cockles from BBC vintage cookery show 'Floyd on Food'.

Check out this video tutorial on the very basics of a chess game. In chess the very first thing you need to know is how to move your pieces. That's what this chess video is all about.

Tommy and Al dedicate this podcast to answering the question of the week: What is the best way to attach legs to a column? With explicit instructions, they demonstrate how to use dovetails to get the legs and columns to fit together “nice and tight.”

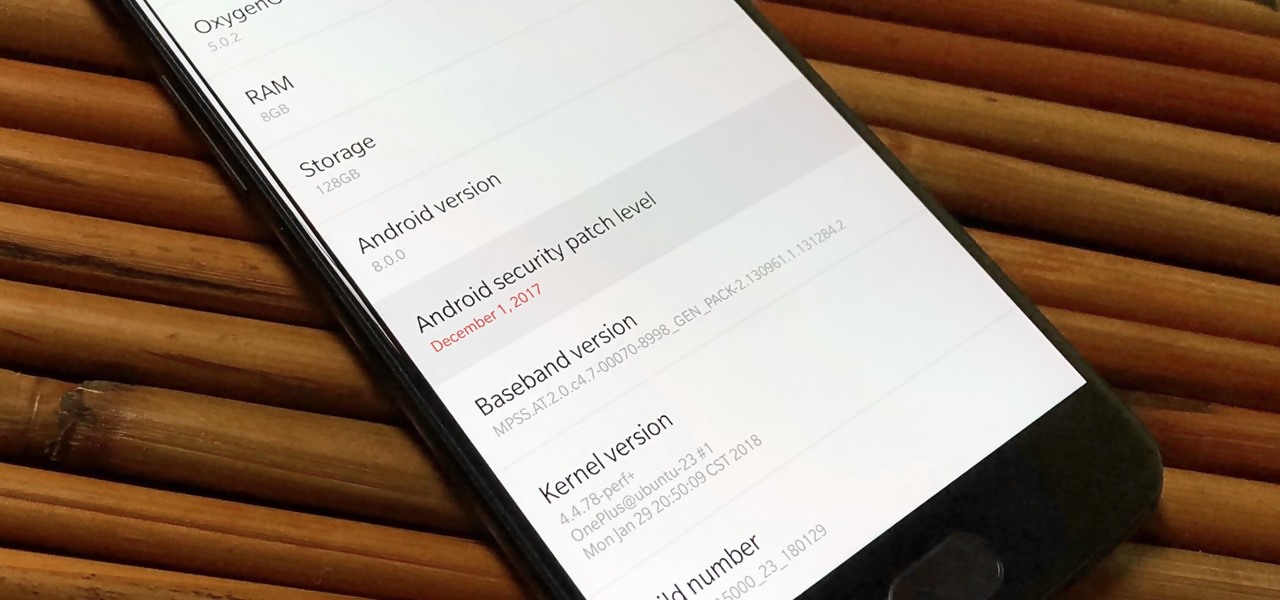
Samsung just began rolling out the Oreo Beta 2 to registered users of the Galaxy S8 and S8+. The update's changelog promises the inclusion of the October 2017 security patch. Unfortunately, after downloading the update, we've noticed this is not the case. Omission of the more recent security patch is notable in that it leaves devices vulnerable to several known exploits, such as KRACK.

The Cloud Security Alliance (CSA), a leading IT trade association, has published its first report on risks and recommendations for connected-vehicle security, ahead of when driverless cars are about to see volume production in the near future.

Google released its "Android Security: 2016 Year in Review" report last month, and to no one's surprise, included its own flagship phones. However, one surprise on the list was the BlackBerry PRIV, which Google named one of the best Android devices for privacy.

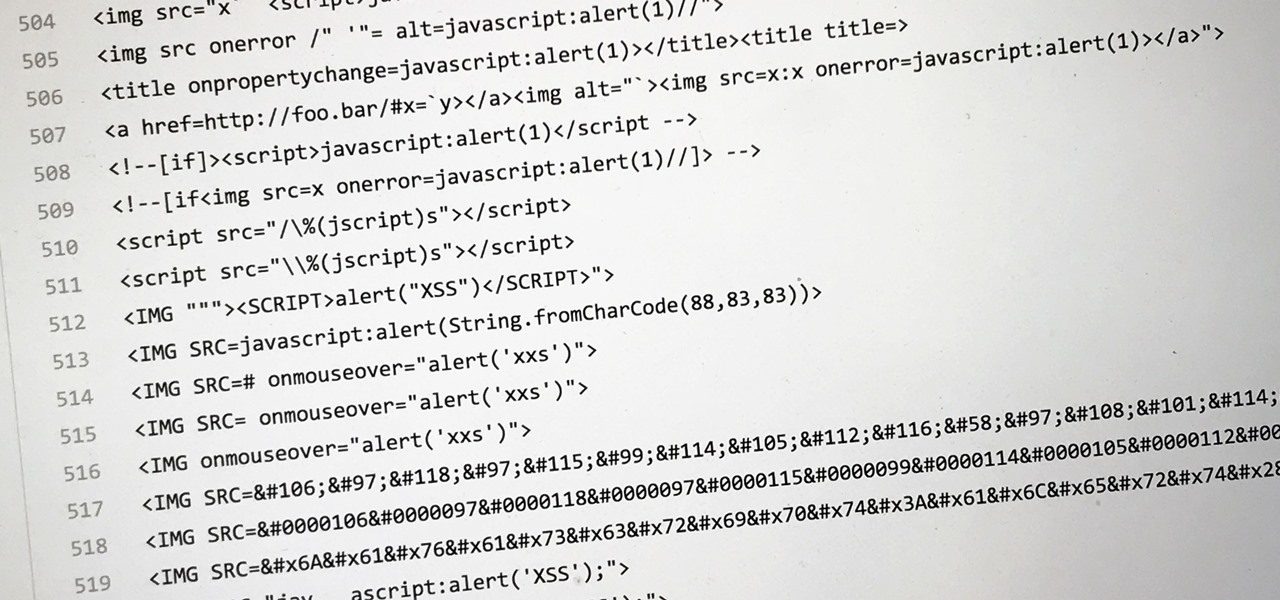
Dirty, malformed, and outright mischievous text strings have long been the enemy of interactive website developers. Strings contain any combination of letters, numbers, spaces, and punctuation, and are entered into text boxes on websites by users. These strings in particular can do everything from highlighting XSS vulnerabilities to soliciting 404 error pages.

A human rights activist from the United Arab Emirates recently stumbled upon three gaping security loopholes in iOS that work by enticing you to tap a link sent to your iPhone. Ahmed Mansoor received a text message from an unknown number roughly two weeks ago, but instead of following the link it included, he sent the message over to a security researcher at Citizen Lab.

With all of the personal data that's stored on our smartphones, it's of vital importance that we have some sort of lock screen security enabled. One of the Galaxy S5's killer features is obviously the fingerprint scanner. It makes the process of dealing with a secure lock screen a bit easier than typing in a password or PIN.
Just in the nick of time. The TSA has come under a lot of scrutiny lately as outrage grows around the country over goons in gloves touching the junk of everybody from toddlers to grandmas. Then there was a suspicious if not improbable al-Qaeda underwear bomber threat to get things back on track. Now we have a French woman with a “surgically implanted device” on transatlantic flight.

In this video, we learn how to remove Security Tool the simple way. Most ways will not remove this from your computer, but this way will. To start, you will need to restart your computer. After this, press ctrl+alt+del the moment Windows shows up. Then, go to the Task Manager and look through the programs that are open. When your security tool opens, press the same buttons to get the mouse free. Then close the security tool from the Task Manager. Now, go to your desktop and press on the icon ...

How to make some delicious and creamy fettuccine alfredo. Ever try and make some that just doesn't turn out quite right? Well here we show you how to make it with perfection. You will need, Fettuccine noodles, cook these to 'al dente' which means soft and fully cooked. Also, you will need heavy cream, milk, parmesan cheese, ground black pepper, shredded Romano cheese, egg yokes, and salt. Bacon is optional, and if you use it, make sure it is fully cooked. Watch the video to observe how to pro...

Chef Michael Smith on Food Network Canada tells you how to avoid serving up a solid mass of pasta with sauce sticking to it.

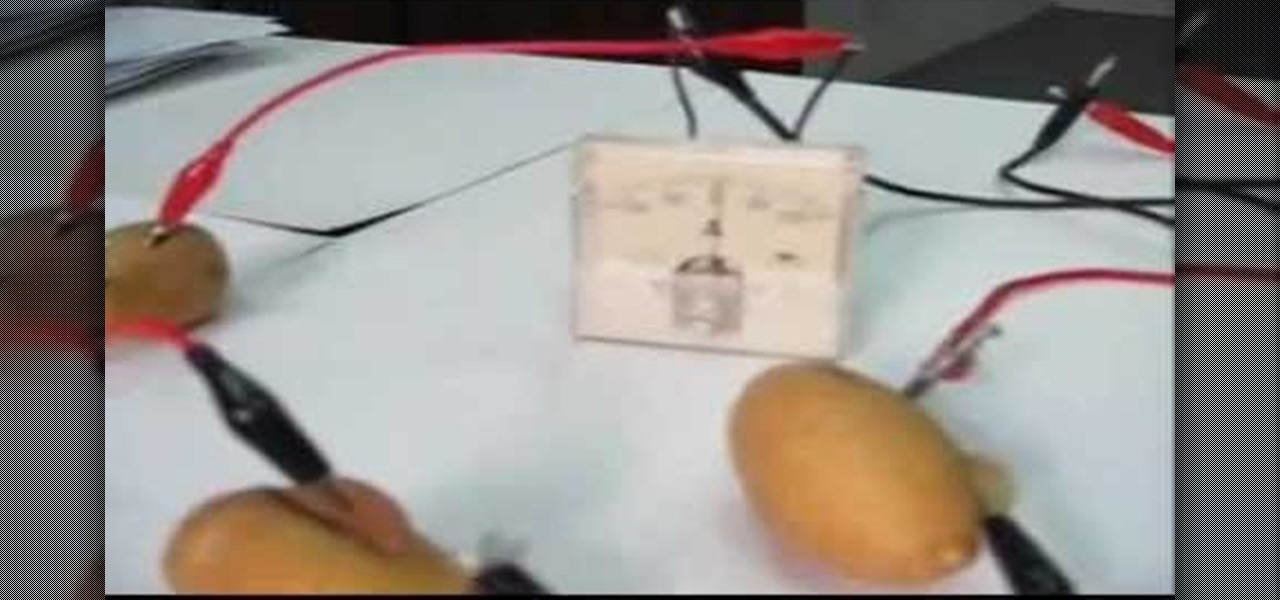
Like a lemon, a potato can produce electricity. This science experiment was prepared by Ebtisam Al Anzoor and demonstrated by Mustafa Daif. The electricity is proven using an analog micro ameter. The positive is copper from a penny or copper coin while the negative is a galavanized nail. The potato releases a charge and is further proven when it is connected to a calculator. You can daisy chain the potatoes for a greater charge.

The term "Thermite" refers to the mixture of aluminum and ferric oxide used in this experiment. It is sold commercially and is used for such applications as railroad welding and incendiary bombs.

When it comes to your security, you want the best of the best. Why settle for mediocre service with something as valuable as your protection? Malware continues to make its way onto the Play Store, leaving millions of devices vulnerable. You need an app that will shield your devices from both the latest malware threats and threats nearby. And when it comes to antivirus apps, there is only one choice.

Kali Linux is the obvious first choice of an operating system for most new hackers, coming bundled with a curated collection of tools organized into easy-to-navigate menus and a live boot option that is very newbie-friendly. But Kali isn't the only distribution targeted at pentesters, and many exciting alternatives may better fit your use-case. We've already covered BlackArch Linux, now it's time to talk about Parrot Security OS.

In an article published in early-2015 by Peninsula Press, it was reported that the demand and the salaries for cyber security professionals are exploding! They cite that 209,000 cyber security jobs were unfilled last year, and that job postings have increased over 74% in the last 5 years. Job opening are expected to grow by another 53% over the next 3 years. You are definitely in the right field, my tenderfoot hackers! Some researchers are expecting information security jobs to continue to gr...

While most of us don't think twice about dragging a pattern or using Touch ID to open our phones, or entering a password in for our email and bank accounts, these features are there to protect some of our most private information. Only problem is, they don't do a good job of it.

While we now know that iCloud was not exploited by hackers to steal private celebrity photos, Apple did admit that guessed (aka brute-forced) passwords and/or iCloud security questions were to blame for the breach.

Watch Al, Bobby, and Tommy discuss (with big words) some table saw safety tips and demo the Saw Stop table saw. Tommy breaks down the process of setting the saw up, engaging the safety systems, firing the blade break and resetting the saw.

Tommy (with Al asking the tough questions) walks you through the process of making simple dovetails and some classic "George Washington wooden teeth".

In this video tutorial you will learn to use the rounded rectangle tools. Al Ward will teach you tricks to make smoother selections. You might find this video useful especially if you are looking for ways to create round-cornered buttons. Make a rounded rectangle selection in Photoshop CS2.

This is one of Al Ward's favorite tricks - how to create a Glass Sphere using a single photo in Photoshop CS2. Learn to use Polar Coordinates to turn a photo into a sphere. You will also need tools like Dodge and Burn to adjust the overall effect. Create a glass sphere using a photo in Photoshop CS2.

Google recently released a new mesh router known as Nest Wifi. The updated and rebranded Google Wifi brought many improvements, such as faster processing power and an increased level of wireless security called WPA3. But while it's not enabled by default, you can still get the new WPA3 security on your original Google Wifi.

If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.

Hundreds of Windows 10, macOS, and Linux vulnerabilities are disclosed every single week, many of which elude mainstream attention. Most users aren't even aware that newly found exploits and vulnerabilities exist, nor that CVEs can be located by anyone in just a few clicks from a selection of websites online.

As far as overall security updates are concerned, we all know that iOS reigns supreme over Android. But just how bad do Android devices fare against Apple in general? A recent report will have you second guessing some companies the next time you're in the market for a handset.

You may have seen news reports over the last two days detailing a major security flaw in virtually all smartphones. The devices that are at risk are not limited to either iPhone or Android — all of us are affected. If you want to make sure your smartphone and its data stay secure, there are a few steps you can take.

Many people think antivirus apps are useless — why pay a subscription fee when most malware can be avoided with common sense? But the thing is, there were an estimated 3.5 million malicious Android apps discovered last year, with many of them making their way onto the Play Store. As this number continues to rise, can you truly depend on common sense to protect you?

Samsung's 2016 line of smartphones has a new update, at least for the devices on AT&T. The update brings the Galaxy S7 to version G930AUCS4BQL1 and the Galaxy S7 Edge to version G935AUCS4BQL1. Here's what's on the table.

The Play Store hasn't been the most secure place for apps lately. A quick Google search for "Play Store malware" will give you a taste of some of the malicious apps that snuck their way onto Android's official app store. Google is aware of the problem and they're tying to fix it, but their new Play Protect program doesn't have a great track record, so you might want to look elsewhere.

WhatsApp sneakily made some security changes to iCloud backups without your knowledge, ladies and gents. Not that strengthening security is a bad thing, but still!

Who likes security? I like security. I lock my doors at night, and so should you! That's why it's exciting to me that Samsung has just announced its May security update. It's like getting a brand new, top-of-the-line lock for free, but for your phone.

In previous posts here, I have pointed out that hackers are in high demand around the world and in nearly every industry. Every military and espionage unit of every country is trying to hire high-quality, experienced hackers as fast as they can to hack their adversaries' computer systems in order to gain a strategic advantage and to spy.

Macaroni and cheese is one of those dishes that automatically make me feel all is right with the world. I even like the boxed kind in a pinch. However, real macaroni and cheese is pretty easy to make and is worlds better than the boxed kind. It's also pretty easy to make really, really good macaroni and cheese once you know some essential pointers.

These days, our smartphones carry some very sensitive data. From banking app passwords to personal photos, there are many things on your Nexus 5 that you might not want other people to have access to.

Snapchat has had more than its fair share of security failures and mishaps. The photo-sharing company is looking to better address some of these security gaps by adding new features, and today its most recent addition is live: the Captcha. New users will be asked to verify their "humanness" by selecting the infamous Snapchat ghost out of a selection of images. The feature is supposed to help block hacker-made bots from creating fake accounts or accessing existing ones. But rather than using t...

There's nothing more tedious, yet exciting, than watching surveillance cameras at work. They prey on the innocent and the unknowing. They protect businesses, workplaces, and homes. They catch criminals in the act, find hilarious anomalies, and are just darn cool when you're not the one that's supposed to be eavesdropping with them.