You're lost. You're cold, thirsty— you're hungry. What if you're not much of a hunter? Maybe you're a gatherer. So, then you'll eat plants. But what if you eat something poisonous? What if you're allergic to it?

During pregnancy, women will end up carrying a good amount of extra weight. While a third of the weight gained will come from the baby, the other two thirds come from the changes that happen in your body while you're pregnant.

Tired of seeing large pores on your face? Need to take care of this problem before it gets out of hand? Below, you will see steps that you can take to rid yourself of this problem.

General Electric isn't known for their Christmas lights, but maybe they should be, because their GE Color Effects are pretty awesome. Especially the LED Color Effects G-35 String sets. And especially when someone named Darco hacks them.

Moving a 2000 pound safe isn't easy... I was working as manager for a construction company that was performing an up fit on a century old building in downtown Concord, N.C. The owners wanted us to move a two thousand pound (that's a ton!) safe up to the second story so that it could be displayed in their new office. The safe was located between the first and second floors in a small office that was used for accounting purposes in the old days when said building had been a hardware store.

Thermal cooking saves energy costs and preparation time, so why not try out this delicious recipe using a thermal cooker? You'll learn how to make a fruit cake inside a thermal portable cooker, which could get you addicted. Give it a try, see if you're a thermal cooker.

In this video clip series, our expert, Brian Nowasky, will demonstrate a variety of shapes, animals and toys made with balloons. Follow along at home as he explains the basic techniques for creating balloon art and helps you learn, step by step, how to re-create his exciting creatures at home for your own kids, or for entertainment purposes.

Don’t be fooled by the use of a vegetable, carrot cake is a delicious dessert that seems to go hand-in-hand with Easter and spring bakes sales. If you’ve made them before or this is your fist time start out the season with this classic cake.

The purpose of this stunt is be a dumbass while 4WDing and purposly get bogged. When someone helps you it is funny to annoy them as you don't know what you are doing, trying to anger person.

Minecart rides primarily serve two different functions—transportation or entertainment. We rarely see minecart-based transportation systems in Minecraft these days because most servers support warps or allow users to set multiple homes that they can simply teleport to. That leaves the primary purpose of entertainment.

There are many impressive accomplishments in Minecraft, too many to name in fact. Sprawling builds, complex machines, and massive servers are the hallmark of Minecraft and things keep getting bigger and better. No one doubts the epic scale Minecraft has reached, but every once in a while something grand comes along that sets a new benchmark in awesomeness. By far the most recent step in this long line of big ideas was an innovation pushed forward by YouTube user Kimundi2. The premise of this ...

You have four guys portraying the typical chicken fight game which is usually played in a swimming pool (example image attached). Only, this fight isn't inside a pool of water, but a pool of sewage or animal waste. Two guys are attached to stilts. Two other guys are placed on top of their shoulders without shirts. They have rooster wings attached to their backs and rooster combs on their heads (for costume purposes of the skit). They rub each other down with baby oil to make themselves very s...

We’ve all been there before. Relentlessly refreshing Ticketmaster and filling in those CAPTCHA codes only to receive the miserable “No tickets are available at this time” message. That’s because ticket brokers with a dozen screens and God knows how many browsers snatch up anything and everything.

Outside the realm of politics, where opposing sides are quite passionate and quite disagreeable, there are few areas in our society quite as divisive as Twitter. People who like Twitter love Twitter and are relentless in trying to co-opt the people they know into joining (this is both altruistic and an unsubtle attempt to boost followers).

The purpose of this stunt is to have the Jackass guys dress up in nothing but speedos and shoot each other with paintballs in an all out paintball battle. Then, Preston Lacy comes over in a tank-like vehicle that assaults all of the guys in speedos with a barrage of paintballs.

The purpose of this prank is for the poor janiter to clean this poo after. Find a place where there is a broken/unavailable toilet e.G A Shopping Mall, McDonalds, KFC, public place etc.

Fire. It’s everywhere— always has been. From the Ordovician Period where the first fossil record of fire appears to the present day everyday uses of the Holocene. Today, we abundantly create flames (intentionally or unintentionally) in power plants, extractive metallurgy, incendiary bombs, combustion engines, controlled burns, wildfires, fireplaces, campfires, grills, candles, gas stoves and ovens, matches, cigarettes, and the list goes on... Yet with our societies' prodigal use of fire, t...

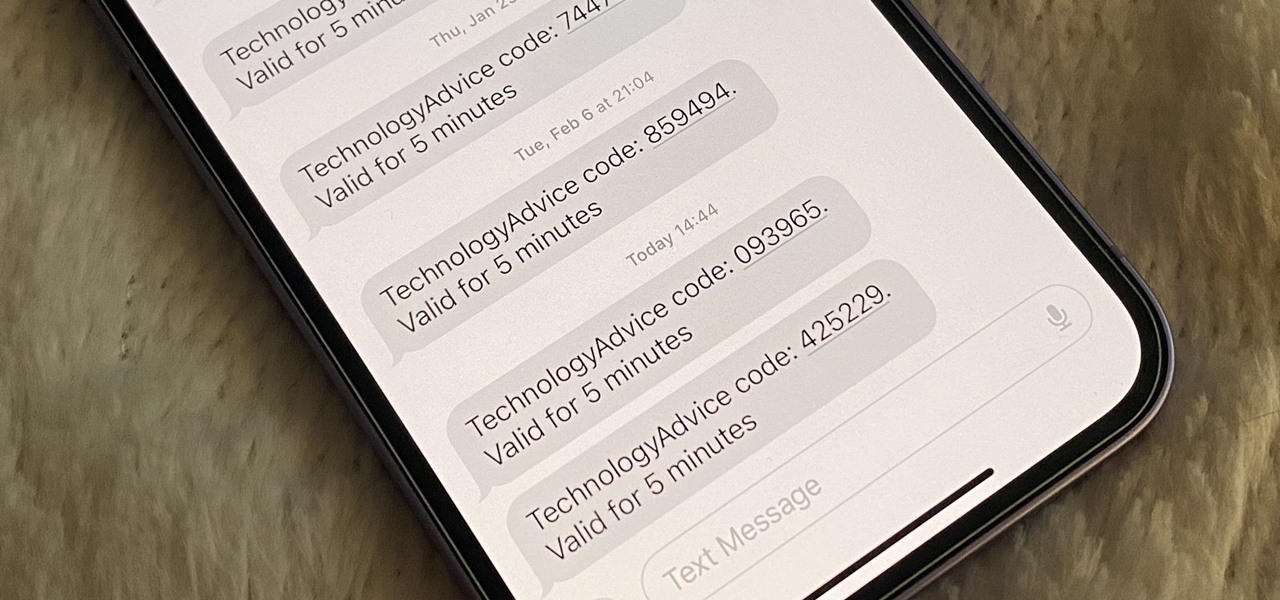
Many of your accounts online likely require two-factor authentication (2FA) or two-step verification (2SV) to confirm your identity when logging in, and there's a good chance the second factor or step for each is a one-time email or SMS verification code. If you get a lot of email and SMS codes, it can clutter your Mail and Messages apps with junk if you don't delete the messages after signing in.

It's nearly impossible to comfortably lay down on your bed or couch with headphones on. Sure, you can position yourself so that your headphones don't touch anything, but that usually means facing up at the ceiling, which is a huge no if you're watching something on Netflix or listening to music on your side.

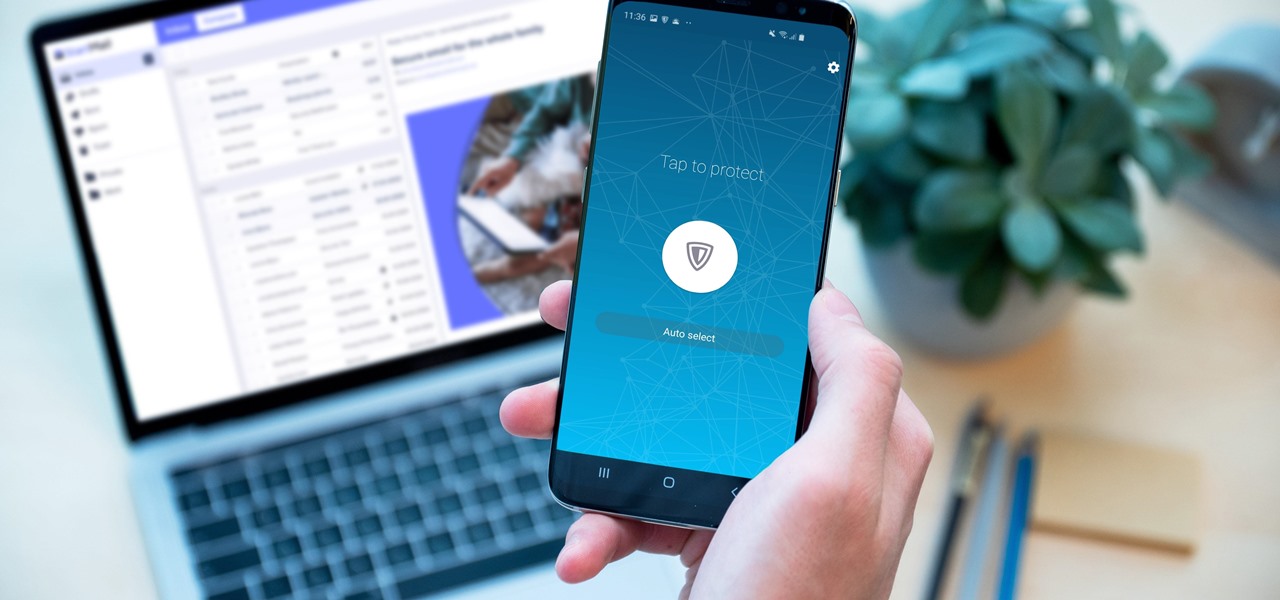
Your sensitive personal data should be strongly protected, and it's never more vulnerable than when you are online. The internet connection is a prime avenue of exposure, and email is one of the least secure forms of communication. Fortunately, there is an easy solution to both of those problems.

The iOS 14.4 developer beta was pushed out a day ago, and now the iOS 14.4 public beta is out and ready for your iPhone. At first glance, there's not much to look at in the new beta release, and it's not yet known if it lays out the groundwork for missing features such as 5G data with dual SIMs, shared third-party app subscriptions, and Xbox Core Controller.

The next big phase of iOS 14 has started with the release of the iOS 14.4 beta. Right now, the developer-only beta features only one known item. Apple introduced the ability to scan App Clip Codes in iOS 14.3 with the Code Scanner control, and now in iOS 14.4, you can launch a local App Clip experience via Camera, NFC, Safari Smart App Banner, or iMessage.

Android's status bar is ever-present. It sits at the top of almost every screen in every app, making it the most prominent part of your Pixel's theme. So it only makes sense that Google would give you a way to change the icons it uses.

Yes, that's right: Instagram has a sneaky, inconspicuous, cryptic, hush-hush way to change its iconic, colorful icon on your Android's or iPhone's home screen and anywhere else it shows up throughout iOS. The app really outdid itself too, with 12 alternative icon designs from its classic look to new themes, all located in an impossible-to-find preferences menu — unless you know the trick.

Apple just released iOS 14.0.1 for iPhone today, Thursday, Sept. 24. The update features bug fixes for the News widget, default browser and mail apps, and more. In iOS 14, default apps suffer from a bug where iOS reverts back to Safari or Apple Mail when rebooting your iPhone, which defeats the purpose of the feature entirely.

Since its release in 1991, Python has become one of the world's most popular general-purpose programming languages. From data mining and web programming to cybersecurity and game design, Python can be used for virtually everything online.

In the coming years, artificial intelligence (AI) will revolutionize every facet of technology and business. AI researchers are in high demand. Salaries in this field are regularly in the hundreds of thousands of dollars.

If you keep your iPhone's home screen obsessively tidy, new apps are the bane of your existence. Hyperbole aside, they automatically fill the first available space on your home screen, starting on the second page, which can wreak havoc on your carefully planned layouts. With iOS 14, however, you can auto-hide new apps so that you never see them until you want to.

Not all 5G is equal. Even if you dropped the cash on a true 5G phone and you see it's connected to 5G in the status bar, that doesn't mean you're surfing the web, streaming Spotify, and binging Netflix faster than your friends with LTE phones.

With all the talk about privacy concerns recently, Google's name keeps coming up because they are a very data-driven company. As an Android user, they know basically everything about you based on your device usage. That can easily scare some people off who are worried about their privacy and security. You do have some say in what personal data Google controls, but what if you want total control?

It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploit contains a variety of modules that can be used to enumerate MySQL databases, making it easy to gather valuable information.

Are you thinking about upgrading your iPhone this year? Apple sure wants you to. Of course, that's no different than any other year, but Apple really wants you to upgrade this year. How do we know this? The rumors point to not three, not four, but five brand new iPhones in 2020, with two very different release schedules. All this begs the question what the hell is Apple thinking?

Router gateways are responsible for protecting every aspect of a network's configuration. With unfettered access to these privileged configurations, an attacker on a compromised Wi-Fi network can perform a wide variety of advanced attacks.

When filtered through the prism of the top stories of the year, the business of augmented reality 2019 was defined as much by epic failures of AR startups as it was by the promising developments that propelled the industry forward into 2020.

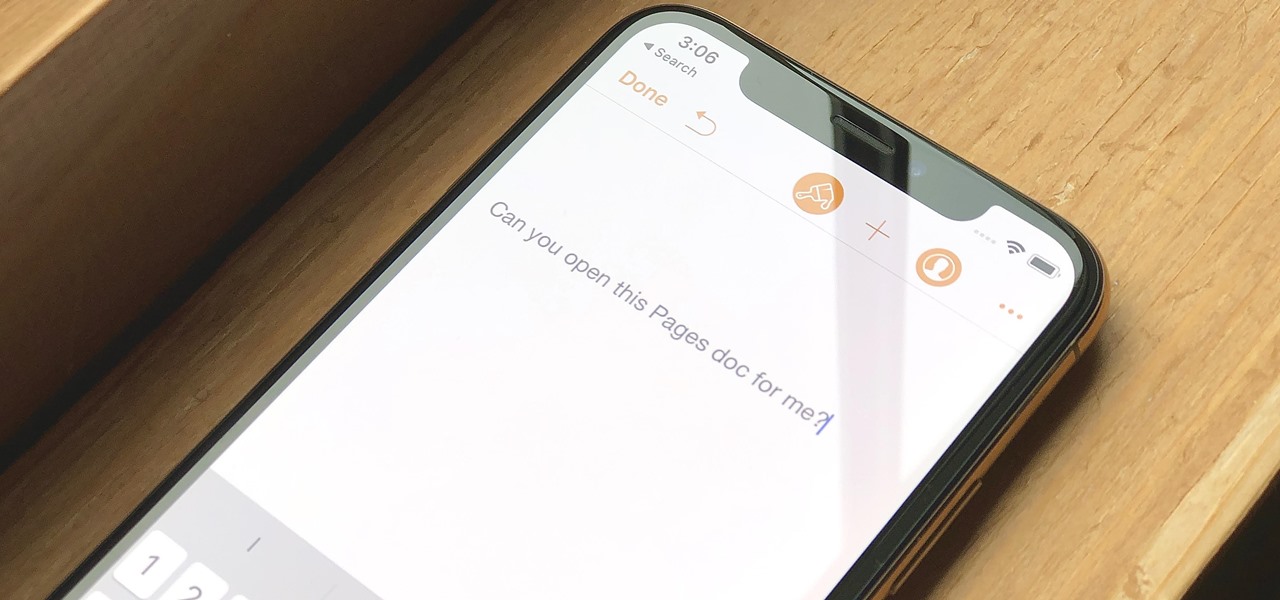
Let's say you have an important report to submit, but you want to check it over for any last-minute edits or changes. Times running out, and you simply can't find this Pages document anywhere. Wouldn't it be great if you could just ask your iPhone to open the report for you, so you could stop wasting time searching and finish the paper? Well, thankfully, Siri can help you out with that.

In Apple Music, loving and disliking songs is a great way to teach Apple's subscription service what type of tunes you like and which you don't. While it also seems like it should be an excellent way to keep track of songs you enjoy in the wild, there's no clear way to view all of your loved tracks in one convenient list. There is a way, however, but easy it is not.

The idea of squeezing your phone might have sounded a bit out there when it was new, but it's now a hallmark feature on Pixel devices. As useful as it is for summoning the Google Assistant, however, it certainly would be nice to be able pick and choose what action is triggered by squeezing the phone. Well, now you can.

When I first found out about Nreal, back in the spring of 2018, the most interesting thing about the company's story was the founder's background. Chi Xu, the CEO and founder of Nreal, previously worked at Magic Leap as a software engineer.

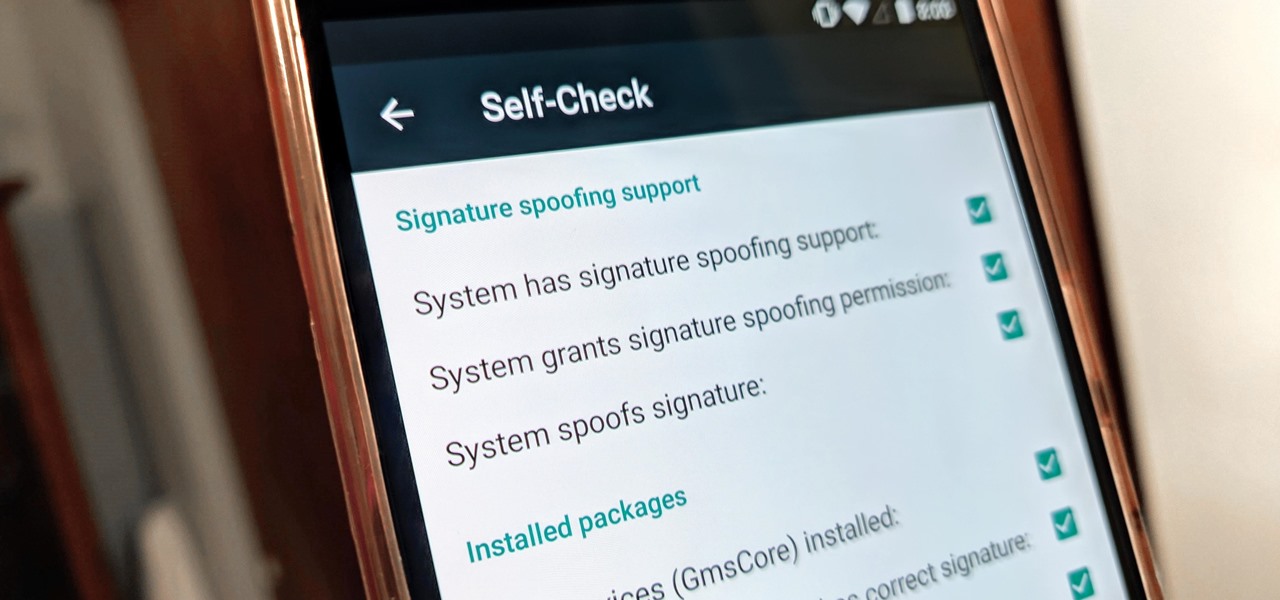
KeePassX, 1Password, and LastPass are effective against keyloggers, phishing, and database breaches, but passwords managers rely on the operating system's clipboard to securely move credentials from the password vault to the web browser. It's within these few seconds that an attacker can dump the clipboard contents and exfiltrate passwords.

UAC is something we've all dealt with on Windows, either as a user, administrator, or attacker. It's a core feature of the Windows security model, and for the most part, it does what it's supposed to. But it can be frustrating as a hacker when attempting privilege escalation, but it's easy enough to bypass UAC and obtain System access with Metasploit.