The status of Uber's driverless program remains a big unknown amid the company's recent woes, but a reported multibillion-dollar shot in the arm by Japanese tech giant Softbank could change all that.
Lyft officially laid its stake in the ground to develop driverless fleets following its Friday announcement, but how fast it is catching up to ride-hailing competitor Uber's driverless initiative remains to be seen.

Is there anything Amazon doesn't do? Whether it's video streaming, creating a brick-and-mortar bookstore, or even purchasing Whole Foods, you name it, and Amazon's probably doing it — well.

Dogmented reality might be coming to Apple's ARKit, so get ready to play with your new (AR) pups! Don't Miss: A Breakdown of the What Apple's New ARKit Can Do for iPhones & iPads

Update: Twitter user Benjamin Geskin (@VenyaGeskin1), known for his iPhone renders, tweeted on Monday alleging that the leaks are fake:

A new leak by frequent tipster Roland Quandt appears to reveal the renders of Motorola's next budget smartphones, the Moto E4 and E4 Plus.

Uber's legal team may have finally sold their engineering golden boy down the river as their war with Waymo continues. Anthony Levandowski isn't your average sacrificial lamb either — given the alleged stealing and all that — but Uber seems set on distancing themselves from this whole fiasco as fast as they can.

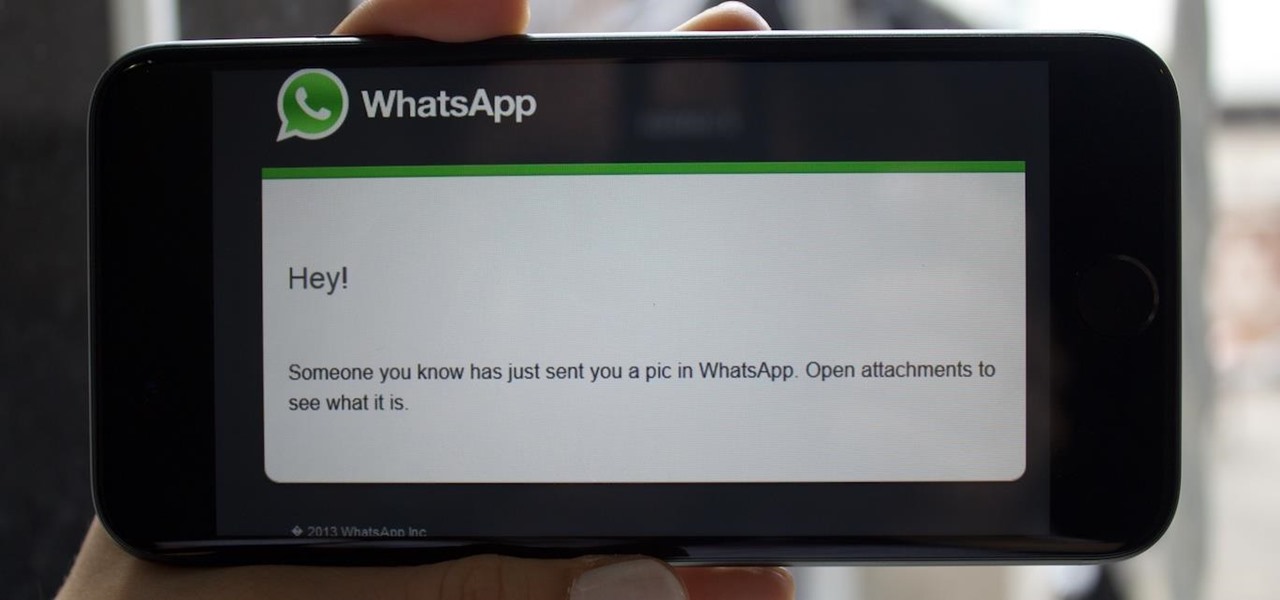
If you ever get asked to update your WhatsApp to your favorite color, don't. It's probably spam. According to Reddit user Yuexist, a new WhatsApp adware is going around disguised as an update.

Uber's chance at driverless domination may be ripped away as its legal battle with Waymo escalates. The company's self-driving program is now under threat of closure if the allegations of premeditated theft are proven

When will the drama end? The lawsuit between Waymo and Uber is back in the news with no signs of stopping. Today the court denied yet another request from Uber to shield itself with the fifth amendemnent, securing a small victory for Waymo.

The rumor mill surrounding the iPhone 8 is churning this week, and not necessarily in a good way. Yesterday, we learned Apple may be leaving the 3D camera out of the next big iPhone to keep the phone on schedule. Today, rumors allege the 10th-anniversary edition of Apple's smartphone may not ship with Touch ID embedded under its display.

Google's former driverless car boss Chris Urmson raised considerable funds to get his new startup company Aurora Innovation up and running. Axios initially reported that Urmson raised over $3 million to fund his brainchild in the wake of his Alphabet exit, according to an SEC filing.

It's no secret Uber has had a pretty rough year, in no small part to being sued by Google. But Google doesn't seem to have intended a full lawsuit against Uber from the get-go, as news today shows Waymo pushed for arbitration against their former employee last fall, months before the news broke that they were suing Uber.

While everyone was marveling at the latest drama over at Magic Leap involving employees last week, a major rumor listed in one of the reports, related to the company's flagship device, was mostly overlooked.

Ride-hailing services are everywhere nowadays and with new companies developing all the time, it is one of the most convenient ways for people to get around. Companies like Uber make it easy for passengers to call a car to pick them up and drive them to their desired location. These services have been especially helpful for commuters as well as those who might need a ride home after a night at the bar. However, ride-hailing services require driving with a total stranger, which means the safet...

For some people, a costume is just a necessary prerequisite to get into Halloween parties. If you're female and you're going the sexy route, it's not too hard to find something to wear, but transforming yourself into something terrifying takes a little more work.

Every year the fine folks at Row Three do a post-TIFF mega-wrap up, collecting the micro-blurbs of a bunch of attendees into a giant meta-analysis of what everyone liked, loved, hated, etc. etc.. We'll link to that post when it goes up on the weekend, but in the mean time, here's my contribution:

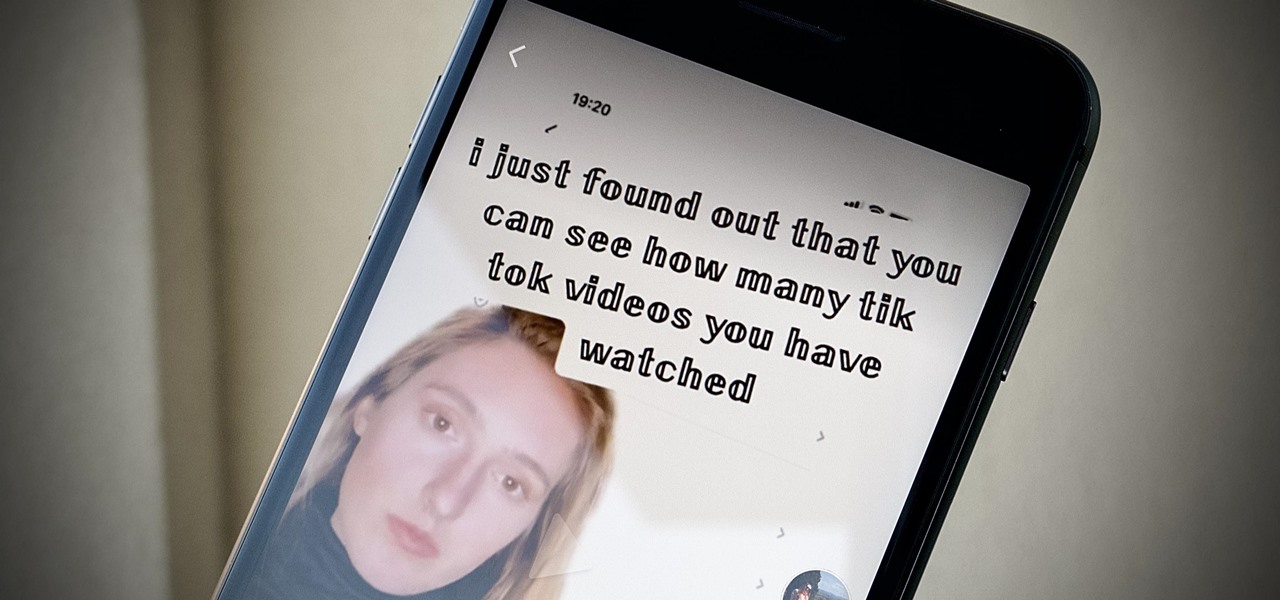
If you're as addicted to TikTok as much as I am, you probably heard about the app's alleged, hidden views counter, which can show you how many TikToks you've watched on your account. Most people who look at their counters are horrified to see that they've watched hundreds of millions of TikToks so far. Can that be right?

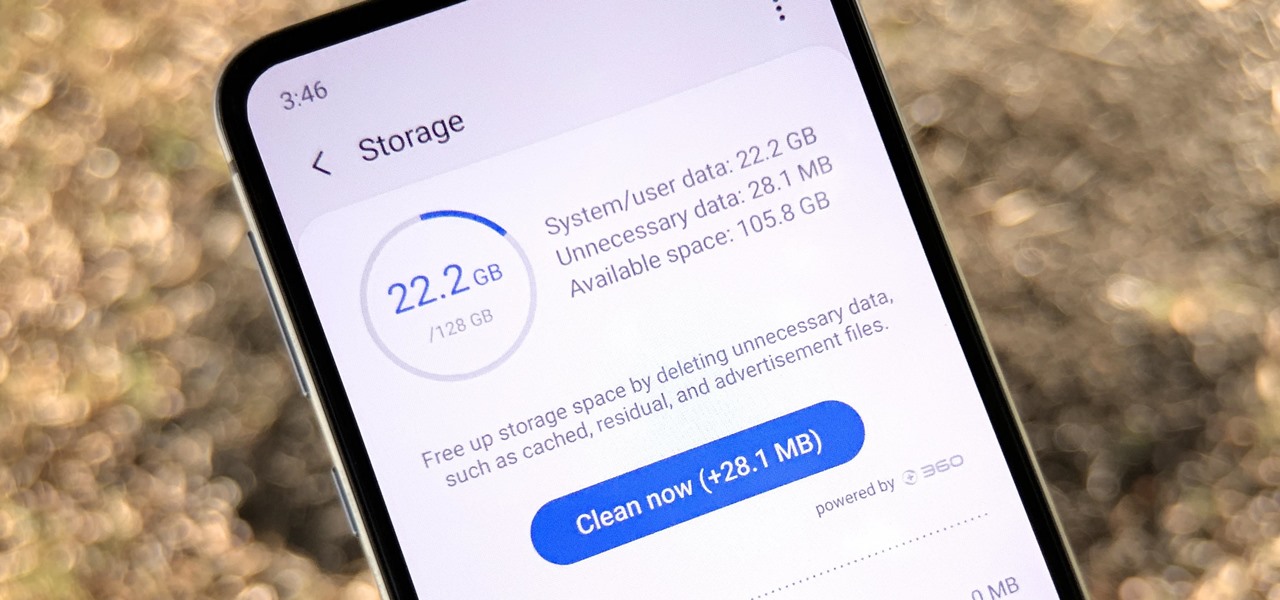
Samsung, like other OEMs, partners with third-party companies to include their apps on Galaxy devices. For example, Microsoft pays Samsung millions to pre-install certain Office apps. But one of these partners might not be on the up and up.

In the midst of fending off legal challenges from Magic Leap and Epic Games, startup Nreal isn't retreating. Instead, the company is digging in its heels and pushing forward with its launch plan for its Nreal Light smartglasses.

Months after Next Reality broke the story surrounding the financial troubles at Meta Company, there's a new update in the company's ongoing patent lawsuit.

This week's Game Developers Conference came at just the right time for Magic Leap, a company that was riding a wave of bad news from legal troubles and rumors regarding Magic Leap One.

Noted poet T.S. Elliot once wrote that "April is the cruelest month." But Magic Leap might argue that March is the most miserable, as the Ides of March brought more legal woes to augmented reality startup. Elsewhere, its closely-held branding secrets have been spilled by way of the US Patent and Trademark Office (USPTO).

Augmented reality business followers, we've got good news and bad news. First, the good news: Upskill closed another round of funding, this time led by strategic investors Cisco and Accenture. (Well, this is probably bad news if you're competing with them on the enterprise AR front.)

While Meta Company has agreed to a settlement in its lawsuit against a former employee and his company, they find the tables have now turned on them in the form of patent infringement allegations from another entity.

Former Google and Uber engineer Anthony Levandowski's scathing accusations challenging the physics behind Tesla CEO and founder Elon Musk's claims about Autopilot should force Musk to make his case that self-drive cars don't need LiDAR in the next few months.

General Motors (GM) seems to have gone to great lengths to avoid lawsuits as it launches its first hands-off driving system in its soon-to-be-launched Cadillac CT6.

Waymo claims in court documents filed yesterday in its lawsuit against Uber that ex-Uber CEO Travis Kalanick knew that former Google engineer Anthony Levandowski was in the possession of stolen documents while employed at the troubled ride-sharing firm.

At this point, I'm ready to give Apple CEO Tim Cook a piece of my mind. The hype surrounding the iPhone 8 is crazy, and rumors are circulating constantly. So many different things have been said about its release date that no one can even keep track anymore. If Cook could throw us all a bone and give us a hint, it would quiet the speculation. Unfortunately, it doesn't look like that'll happen anytime soon, but — in the meantime — a new report allegedly has the inside scoop. Recent rumors surr...

Magic Leap has always been intensely secretive about its work on its augmented reality headset, so it's interesting that they're now publicly recruiting developers to build software for the device before its launch.

The drama continues! In the latest installment of the feud that has rocked the driverless vehicle industry, Waymo is now accusing Uber of withholding a secret LiDAR device.

A federal judge wants answers after an Uber engineer accused of data theft pleaded the Fifth in the ongoing Waymo versus Uber battle. This privilege would protect the accused, Anthony Levandowski, of self-incrimination and handing over specific documents demanded in a previous subpoena and forthcoming deposition.

It's no secret that there's a lot of surveillance going on these days. It's easier than ever to end up in a database, and even former government agents are speaking out about the atrocious amount of spying being done against our own citizens. They've targeted our laptops, cars, IP addresses, and now they're coming for our iPhones. AntiSec hackers managed to get their hands on a list of over 12 million Apple UDIDs (Universal Device IDs) from an FBI computer, and they published 1,000,001 of the...

This Naruto character is a very sinister and evil one: Orochimaru. At one point in time, he was considered a prodigy and was one of Konohagakure's Sannin. The Sannin is a group of three students of Hiruzen Sarutobi. The three members were a part of Team Sarutobi and they were Jiraiya, Tsunade, and Orochimaru. If you want to learn how to draw this dismal Orochimaru anime/manga character, it's really quite simple. DragoArt has this video tutorial on how to draw Orochimaru from Naruto. Get more ...

Welcome to the Part 2 of the series 'Cryptocurrency'. It has been late because of some errors, where all I typed was lost.

Sometimes, doing the right thing is way more difficult than it should be, like trying to return a lost smartphone. Despite having the best intentions, it's often hard to track down the rightful owner, especially if the device is armed with a passcode. On the other hand, there are plenty of people who see an unattended iPhone or Samsung Galaxy S3 as a chance for profit. In 2011 alone, the number of lost and stolen cell phones in America was worth over 30 billion dollars. That's right, billion....

In a stunning end-of-year twist to the Magic Leap versus Nreal legal saga, the China-based startup is now filing a motion against Magic Leap.

Six people have died from fungal infections in Pittsburgh hospitals since 2014—that fact is indisputable. The rest of the situation is much vaguer. A lawsuit has been filed against the hospitals on behalf of some of the deceased patients, alleging that moldy hospital linens are to blame. While the lawyers argue over who's at fault, let's look at how this could have happened.

Samsung and Apple are back in court, but this time it's not just money at stake. The Supreme Court's decision could have a far reaching effect on patent law and innovation in design.

Welcome back, my fledgling hackers! Let's continue to expand our knowledge of digital forensics, to provide you the skills necessary to be a digital forensic analyst or investigator, as well make you a better hacker overall. In your attempts to enter a system or network undetected, it is key to understand what a skilled forensic investigator can learn about you, the alleged hacker.