After you've tried out Nextraker's pillow prank, move onto the medicine cabinet with this deodorant stick prank. All you need is your victim's stick of deodorant (white) and some Kool-Aid (or in this case Flavor Aid).

Matches may not be the ubiquitous part of every person's going-out equipment that they once were, but they are still useful both for lighting fire if you don't have a lighter and for pulling these two hilarious bar pranks. The first is a simple counting game where you manipulate your victim into making piles of matches of sizes you guess correctly, because you rigged the game. The second involves challenging the victim to make six equal half of eleven using a pile of matches. Both are funny, ...

Office pranks have a long and distinguished history. You've probably seen this one before, but in case you haven't, this video will show you how to do the upside-down coffee cup prank. Simply take a full cup of coffee, place it on the desk of your victim, place a piece of paper flat on top, then carefully flip the cup onto the desk and remove the paper. The cup will be upside-down, full, on the desk. The only way to remove it is to soak oneself with coffee, as your victim will most likely do.
It looks like there is a fatal flaw in the current macOS High Sierra 10.13.1, even straight from the login menu when you first start up the computer. This severe vulnerability lets hackers — or anyone with malicious intentions — do anything they want as root users as long as they have physical access to the computer.

Hello Friends … My name is Suresh Senarathna and this is my first “How-To” post,
Hey everyone, this will be a quick post. Facebook does not use HTTP Strict Transport Security (A header that tells the browser to only use HTTPS when communicating with the server) on subdomains of facebook.com. That means, if someone uses facebook in a different language, the browser will attempt to connect using HTTP first. An attacker can intercept that request and serve a different page, including a fake login one.

There are a lot of great tutorials on Null Byte using Python to create backdoors, reverse shells etc, so I thought it might be worthwhile making a tutorial on how to convert these python scripts to exe files for Windows victim machines.

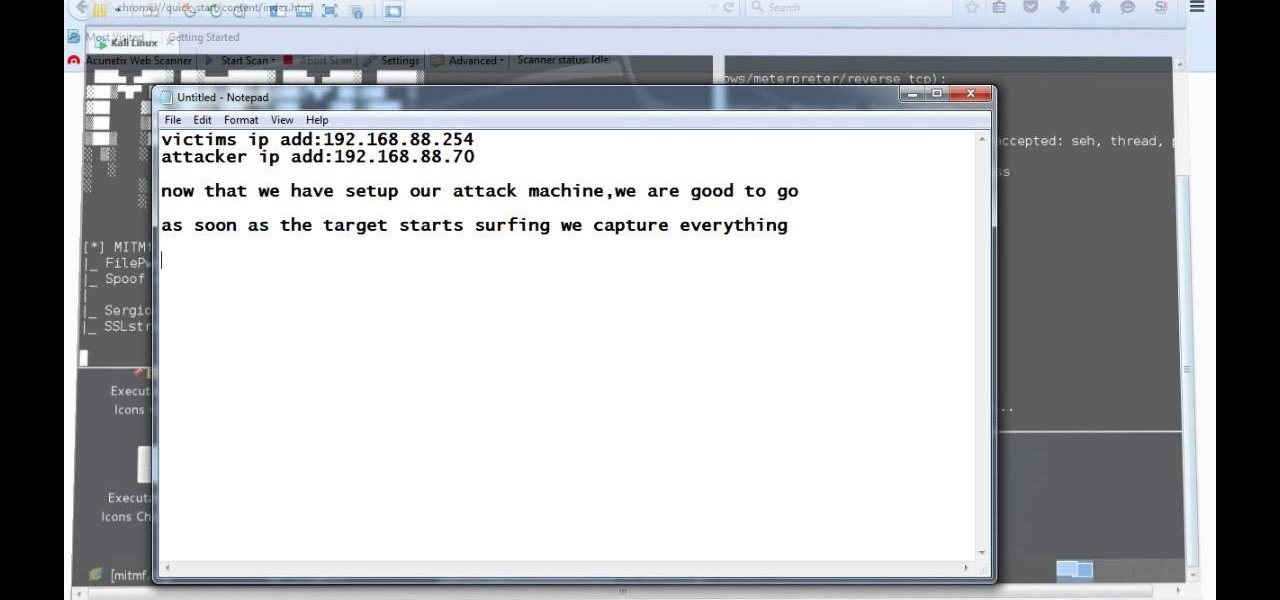
Video: . Hi, this is a quick demo about how to backdoor executables (software) sent over HTTP using MITMF, backdoor factory

One of the worst messes to clean up is raw eggs, well use that to annoy anyone you want by setting up this practical joke.

Are you looking for a mean April Fool's Day Prank, Check this out! Basically you take your victim's hairbrush and tamper with it.

Welcome back, my tenderfoot hackers! In some of my past articles, I've shown numerous ways of embedding a listener/rootkit on a remote system, including buffer overflows of the operating system, getting the victim to click on a link to our malicious website, and sending a malicious Microsoft Office and Adobe Acrobat file.

If you want to prank a friend or family member, this next tutorial is one that is really easy to perform. This is called the exploding soda can prank.

This water bottle prank is really ingenious. You split two water bottles and recombine them to form a new, weaker frankenwwaterbottle. You fill this with water and superglue the cap on. Now, when your victim tries to open the water bottle they'll push so hard on the unopenable cap that the weak bottle will break in two, soaking them and their friends. Brilliant, devious, and hilarious.

Good Housekeeping Magazine has teamed with the American Heart Association to bring this life-saving video to you. In the event of a sudden cardiac arrest, call 911 and begin chest compressions immediately. Place your hands on the center of the chest and push hard and fast until help arrives. Compressions help deliver oxygenated blood to the brain and heart. This hands only approach to delivering CPR can greatly alleviate fear, and can double or quadruple a victim's chance of survival.

Know someone that's terrified of rats? This twitching dead rat prank is perfect for you then. Great for Halloween or April Fool's Day. You just need a stuffed rat, a rattrap, vibration motor, AAA battery holder with batteries, and a piece of straw. Oh, and fake blood, too!

All you need is you, a friend and a victim and it's as simple as that! Just make sure your friend isn't THAT heavy. Brian Brushwood of Revision3's Scam School shows you this bar trick and how to fool your friends into thinking you have magical super hero strength.

The legal travails of Magic Leap appear to have no end in sight, as a lawsuit filed by an ex-employee further threatens to dampen the startup's 2018 launch.

Patent holder Genedics, LLC has filed a legal complaint alleging that hand-tracking startup Leap Motion is infringing on its intellectual property.

Video: . For the first prank you're going to need an empty container, preferably black, a smoke bomb and a lighter. I gotta say though this prank is not for just anybody so prank at your own risk. Let me show you how its done, first apply some hot glue on the bottom of the smoke bomb, then stick it inside the container.

Good day people, today we will examine some basic, for some people well-known attacks, also we will take a look at some advanced attacks.

A video showing what is alleged to be the new Apple iPhone 7 has appeared online. The uploader of the video claims that it was shot on one of Foxconn's assembly lines.

Recently, I've been experimenting with BeEF (Browser Exploitation Framework), and to say the least, I'm hooked. When using BeEF, you must "hook" the victims browser. This means that you must run the script provided by BeEF, which is titled "hook.js", in the victims browser. Once you've done that, you can run commands against the victims browser and cause all kinds of mayhem. Among these commands, there is an option to use the victims webcam. This is what we'll be doing here today, so, let's g...

Welcome back, my tenderfoot hackers! Recently, Microsoft released a new patch (September 8, 2015) to close another vulnerability in their Windows Vista, 7, 8, and 8.1 operating systems. The vulnerability in question (MS15-100) enabled an attacker to gain remote access to any of these systems using a well-crafted Media Center link (MCL) file.

This is evil and it destroys people. Let's just get that out of the way. Nonetheless, suppose you need to make someone distrust their own memory and perception of reality. Suppose you want someone to believe in you more than they believe in themselves.

Kipkay is at it again with his pranks. In this video, he shares four fun and easy pranks that anyone can do to drive their friends (or victims) crazy! Their all very simple. They include a cell phone prank, a floss prank, and more!

Pranks are the world's favorite pastime. Everyone loves a good prank, and there's nothing better than keeping someones stomach empty. Imagine the pain and suffering one would endure if he or she could not eat because the fridge will not open. Most refrigerators allow for reversing the door swing. Normally you also switch the handle. But not if you want to thoroughly confuse the victim of this practical joke.

Video: . ?The following are 5 practical jokes you can set up on your friends and family, All these pranks involve sodas so make sure you have a few handy if you want to try out these pranks. Just a little warning, 4 out of the 5 pranks showcased in this intractable are pretty messy so prank at your own risk.
According to security firm Kaspersky Lab, CoinVault and Bitcryptor ransomware are officially dead.

Welcome back, my greenhorn hackers! After the disaster that was Windows Vista and the limited and reluctant adoption of Windows 8 and 8.1, Windows 7 has become the de facto standard operating system on the desktop/client.

Welcome back, my rookie hackers! Many newbie hackers focus upon the technical aspects of hacking and fail to give enough attention to social engineering. In fact, I would say that technical hacks should ONLY be attempted if social engineering attacks fail. Why bother spending hours or days trying to hack a password if someone will simply give it to you?

The perfect way to avoid boredom at work or in the classroom is with a good old-fashioned prank, and this one is for tech-minded. In the video below, you'll see how to change your coworker's (or classmate's) computer screen to be display upside-down, which will totally freak them out when they return from lunch or the restroom. The best part is watching them try to revert it back to normal!

Now that we have control over a victim's browser, we need to use some attacks to maintain the connection, or even better: upload a shell.

For the dedicated prankster, April Fool's Day is no joke. Nothing will stop them from coming up with the cleverest, most elaborate prank the world has ever seen. Or at least—their victim.

Toilets are some of the best prank aides, and this video will teach you a novel way to use them. All you do is connect the hose that fills the tank with water to another longer hose, then run it to under the sink and attach it in a position to spray outward. Then wait for your victim to flush.

Icy-Hot has relieved and caused intense pain for decades, and this is one of the best Icy-Hot pranks we've ever seen. All you need is a victim who uses body wash regularly, some Icy-Hot, and a desire to cause someone intense but not long-term harmful pain.

This tutorial makes you look like you just stepped off the set of the Terminator movie. You can also use these techniques to make yourself look like a burn victim, an undead or any other creature which has dark, mottled skin.

Card magic is generally done to amuse the elderly and to scam the gullible. This video will show you a great way to do the latter and get yourself free drinks at a bar. The outcome of the trick is that you and your victim both cut to the same card in a deck after you bet them that it will happen. Watch the video, then get out there and pull the prank.

Are you using the Queen too much, or attacking with one piece at a time, or making mostly pawn moves, or that tricky Knight obsession, or "freeing" the Rook with a side pawn, or are you being a victim of a back row checkmate? Well, watch this video to to avoid these common chess mistakes.

Len's flare is more than little star-shaped rectangles appearing in backlit pictures. Even when you don’t see a starburst, you may be the victim of lens flare if you use inexpensive lenses. In this video tutorial you will learn to use the patch and sponge tools to remove lens flare from your images.

Maybe you thought sitting behind a Mac gives you special protection when it comes to getting hacked. Thanks to a a new report from Check Point, you can kiss that theory goodbye. The cyber security company just uncovered the latest strain of malware — OSX/Dok — infecting all versions of macOS (previously Mac OS X).