Welcome back, my tenderfoot hackers! I recently began a new series on digital forensics to help tenderfoot hackers from being detected and ultimately, incarcerated. In this installment of that series, we will look at recovering deleted files. This is important to hackers because you need to know that even when you delete files on your computer or on the victim's computer, a forensic investigator can usually recover them.

The My Computer section of most PC computers is an absolute mess, especially if you're trying to navigate someone else's computer. Why not take advantage of this fact by pulling this awesome prank on one of your data-loving friends? The video above will show you how to make a folder invisible and then hide it on their computer, making the chances of them finding it without knowing that you've pranked them slim to none. Just make sure you're there to watch you victim freak out afterwards! That...

Sharks. The first thing that comes to mind is "Jaws", Steven Spielberg's horrifying shark film that scared generations of young adults from entering the ocean waters. But not all sharks are as violent (and hungry) as "Jaws", so jump in the water and know a few guidelines to stay safe. Escape a shark’s jaws of death with these lifesaving strategies.

Neck pain can be the worst. Be aware of daily habits that may be causing your chronic neck pain and replace them with healthy choices. In this tutorial, learn how to soothe chronic neck pain.

Looking to up the ante in the home secuirty department? If you are concerned about the safety of your family and home, consider purchasing a burglar alarm system by following these helpful tips.

There's nothing worse than stalker, or someone who you just want to avoid. Fortunately, there are ways of dealing with it! This video shows you some of them.

Put yourself in the shoes of a burglar so you can anticipate where they'd look for your valuables. You Will Need

Learn how to play "Womanizer" by Britney Spears, an acoustic guitar tutorial. Follow along with this demonstration, tabs and lyrics here:

Learn how to identify a stroke victim, what a stroke is, how it affects your body, how to test someone who might be suffering from a stroke, and tips for stroke prevention with expert medical tips in this free online health care video series.

If you're as addicted to TikTok as much as I am, you probably heard about the app's alleged, hidden views counter, which can show you how many TikToks you've watched on your account. Most people who look at their counters are horrified to see that they've watched hundreds of millions of TikToks so far. Can that be right?

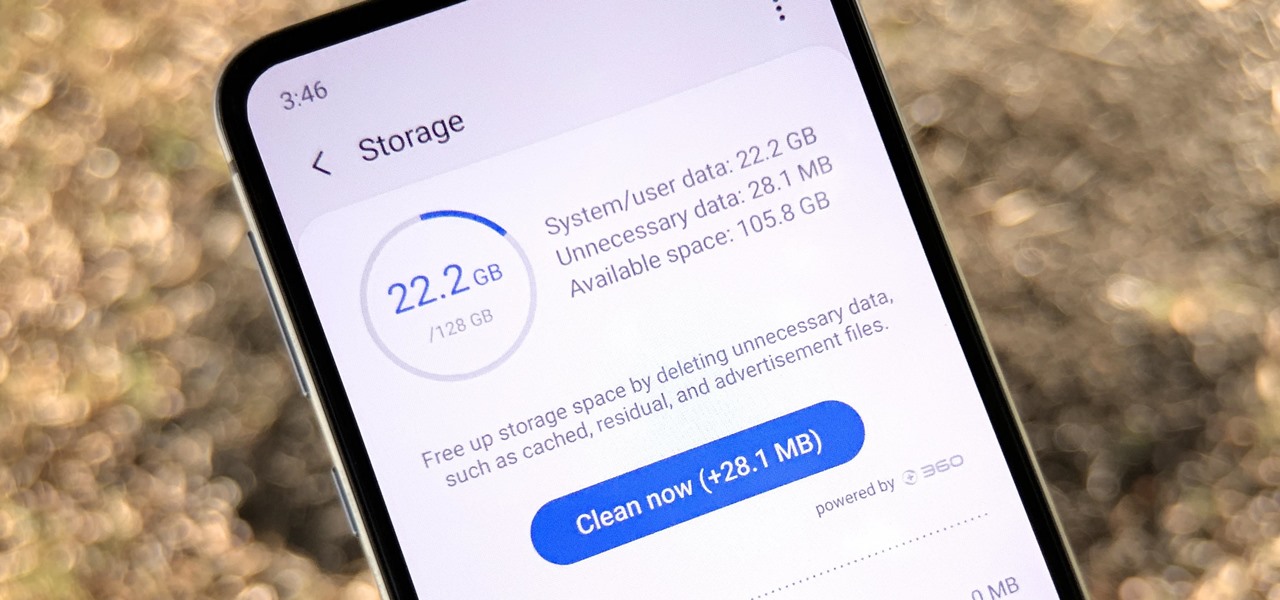
Samsung, like other OEMs, partners with third-party companies to include their apps on Galaxy devices. For example, Microsoft pays Samsung millions to pre-install certain Office apps. But one of these partners might not be on the up and up.

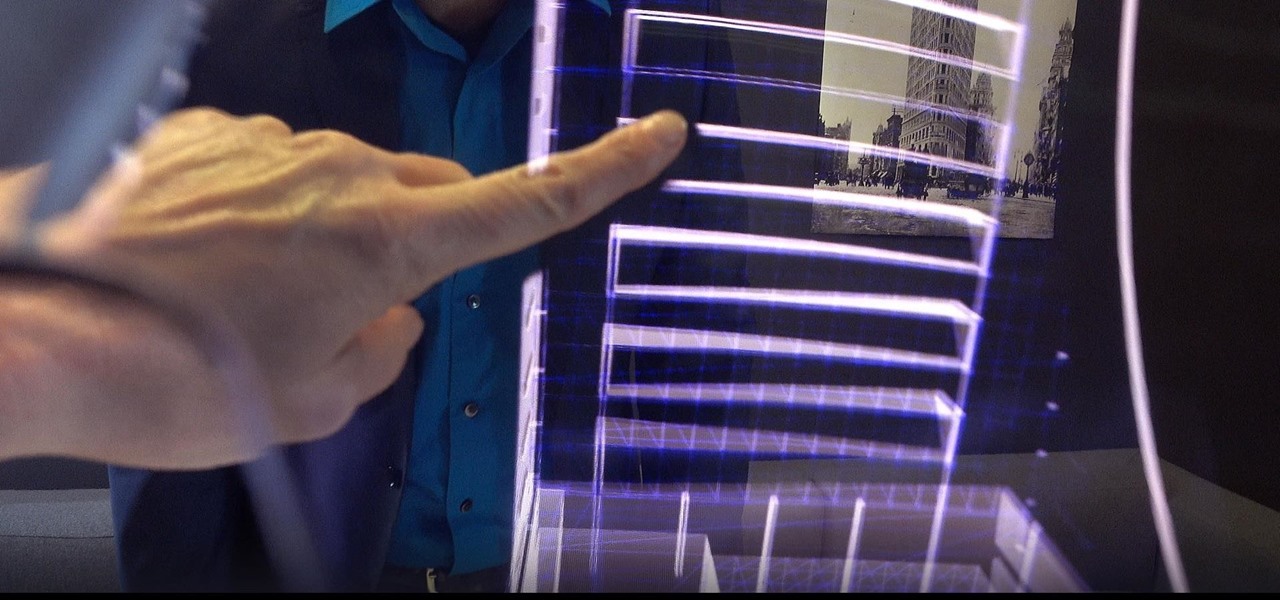
In the midst of fending off legal challenges from Magic Leap and Epic Games, startup Nreal isn't retreating. Instead, the company is digging in its heels and pushing forward with its launch plan for its Nreal Light smartglasses.

Months after Next Reality broke the story surrounding the financial troubles at Meta Company, there's a new update in the company's ongoing patent lawsuit.

Smartphones and laptops are constantly sending Wi-Fi radio signals, and many of these signals can be used to track us. In this guide, we'll program a cheap IoT device in Arduino to create hundreds of fake networks with common names; This will cause nearby devices to reveal their real trackable MAC address, and it can even let an attacker take over the phone's data connection with no warning.

This week's Game Developers Conference came at just the right time for Magic Leap, a company that was riding a wave of bad news from legal troubles and rumors regarding Magic Leap One.

Noted poet T.S. Elliot once wrote that "April is the cruelest month." But Magic Leap might argue that March is the most miserable, as the Ides of March brought more legal woes to augmented reality startup. Elsewhere, its closely-held branding secrets have been spilled by way of the US Patent and Trademark Office (USPTO).

Augmented reality business followers, we've got good news and bad news. First, the good news: Upskill closed another round of funding, this time led by strategic investors Cisco and Accenture. (Well, this is probably bad news if you're competing with them on the enterprise AR front.)

While Meta Company has agreed to a settlement in its lawsuit against a former employee and his company, they find the tables have now turned on them in the form of patent infringement allegations from another entity.

Former Google and Uber engineer Anthony Levandowski's scathing accusations challenging the physics behind Tesla CEO and founder Elon Musk's claims about Autopilot should force Musk to make his case that self-drive cars don't need LiDAR in the next few months.

General Motors (GM) seems to have gone to great lengths to avoid lawsuits as it launches its first hands-off driving system in its soon-to-be-launched Cadillac CT6.

In late June, the biggest measles outbreak to strike Minnesota since 1990 seemed to be winding down. Today, public health officials announced a new confirmed measles case in the area.

Waymo claims in court documents filed yesterday in its lawsuit against Uber that ex-Uber CEO Travis Kalanick knew that former Google engineer Anthony Levandowski was in the possession of stolen documents while employed at the troubled ride-sharing firm.

Ride-hailing services are everywhere nowadays and with new companies developing all the time, it is one of the most convenient ways for people to get around. Companies like Uber make it easy for passengers to call a car to pick them up and drive them to their desired location. These services have been especially helpful for commuters as well as those who might need a ride home after a night at the bar. However, ride-hailing services require driving with a total stranger, which means the safet...

We all know the internet isn't exactly a safe place. While plenty of its users are innocent and kind, you won't last long unless you treat every new screen name like a criminal (we're all this cynical while surfing the web, right?). Well, that cynicism is proven correct today, a post on Medium uncovered a group of scammers on the iOS App Store that are costing victims up to $400 a month.

At this point, I'm ready to give Apple CEO Tim Cook a piece of my mind. The hype surrounding the iPhone 8 is crazy, and rumors are circulating constantly. So many different things have been said about its release date that no one can even keep track anymore. If Cook could throw us all a bone and give us a hint, it would quiet the speculation. Unfortunately, it doesn't look like that'll happen anytime soon, but — in the meantime — a new report allegedly has the inside scoop. Recent rumors surr...

Magic Leap has always been intensely secretive about its work on its augmented reality headset, so it's interesting that they're now publicly recruiting developers to build software for the device before its launch.

The drama continues! In the latest installment of the feud that has rocked the driverless vehicle industry, Waymo is now accusing Uber of withholding a secret LiDAR device.

A federal judge wants answers after an Uber engineer accused of data theft pleaded the Fifth in the ongoing Waymo versus Uber battle. This privilege would protect the accused, Anthony Levandowski, of self-incrimination and handing over specific documents demanded in a previous subpoena and forthcoming deposition.

Download a popular, legit app from the Google Play Store. Decompile it. Add malicious code. Repackage the app. Distribute the now trojan-ized app through third-party Android app sites. This is how advertising malware Ewind, what Palo Alto Networks calls "adware in applications' clothing," infects Android users.

A human rights activist from the United Arab Emirates recently stumbled upon three gaping security loopholes in iOS that work by enticing you to tap a link sent to your iPhone. Ahmed Mansoor received a text message from an unknown number roughly two weeks ago, but instead of following the link it included, he sent the message over to a security researcher at Citizen Lab.

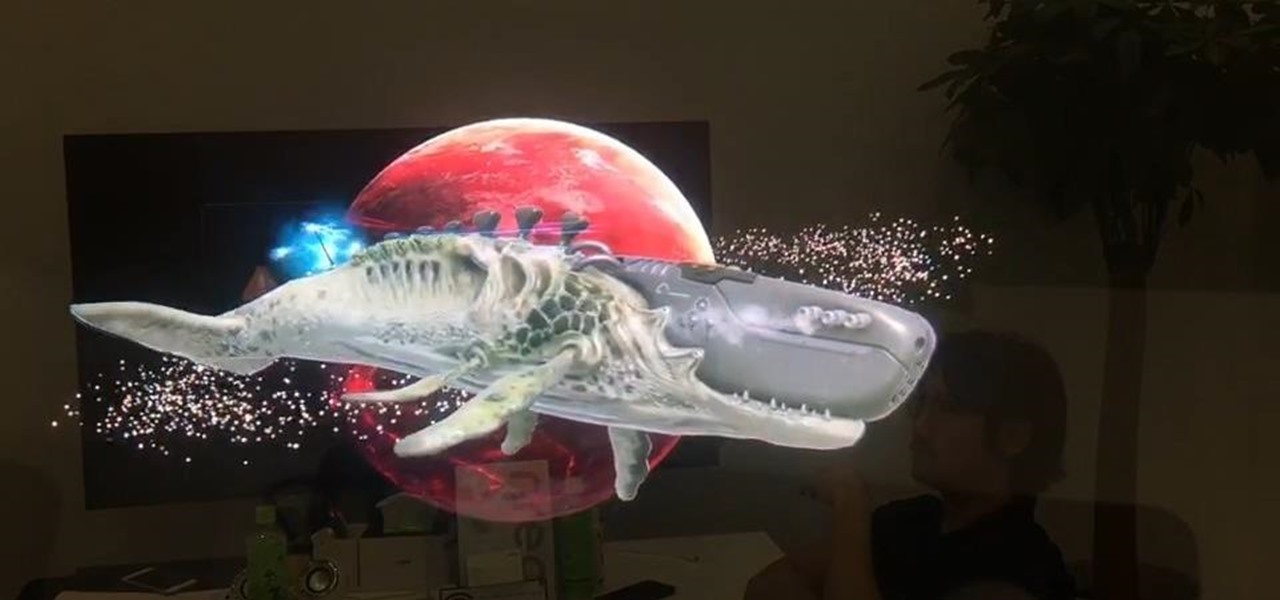
Our brains do a magnificent amount of work to process visual stimuli, but they aren't difficult to fool. Optical illusions can trick our minds into believing what we're seeing is real, even if it's not—and virtual and mixed reality technologies take advantage of this little loophole in our brain to help us accept the unreal.

This tutorial follows the same idea as my original tutorial for windows, but I've redone it to work with Mac OS X. Here's how to get a meterpreter session from your victim opening a malicious word document:

I saw many people asking for a Tutorial about writing their own Remote Administration Tool, so I now introduce you in a basic kind of RAT. This program is not for real use, but for learning how you could write this kind of tool. It will be basicly coded and not very refined. I used Python 3, so you have to install it if you want to use this program unchanged. Also this RAT is for Windows and almost all features won't work under Linux.

First of all, Merry Christmas and Happy New Year to all Null-Byters that learn and teach in this wonderful site. In this article we will explore the basics of the meterpreter's IRB (Interactive Ruby Shell).

Roughly four years ago, Adobe decided to abandon development of the mobile version of their popular Flash Player browser plugin. Their excuse at the time was that this move would enable them to focus more on HTML5 development for mobile devices and allow them to put more effort into maintaining the fluidity and security of their desktop Flash plugin.

If you read my last tutorial on using SEToolkit, you probably know that SEToolkit is an effective way to make malicious actions look legitimate. But, that was only the beginning... the truth is, Metasploit and SEToolkit belong together, and help each other very well.

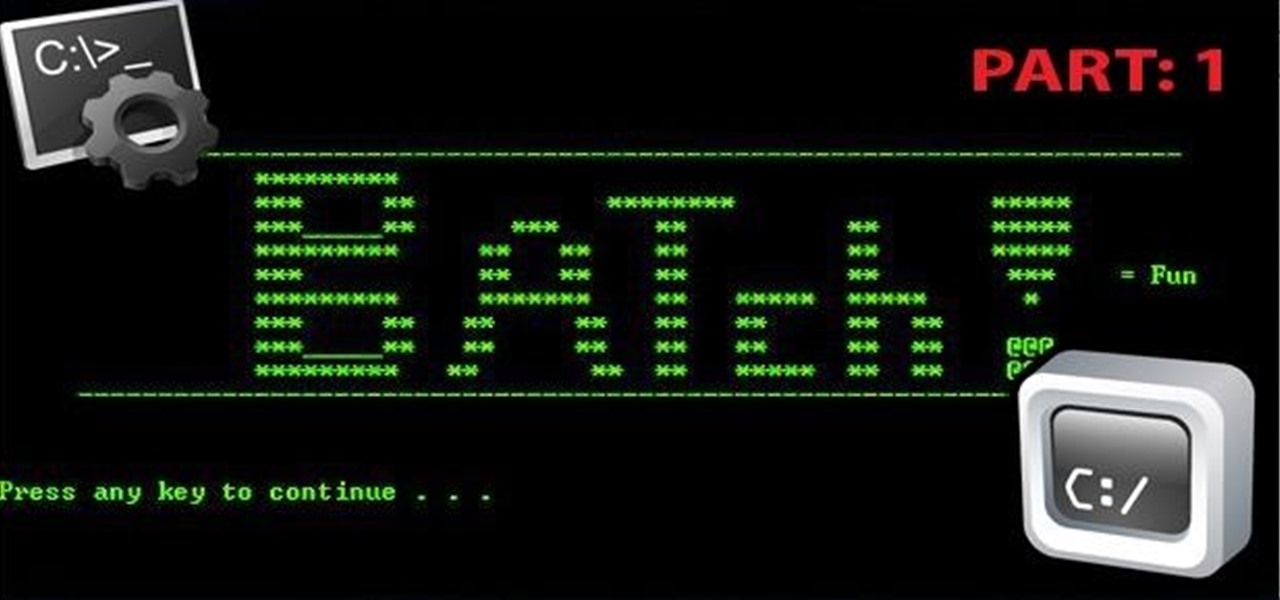
Hi there, Crackers, Welcome to my 7th post (Part-1), this tutorial will explain about the basics of Batch Scripting.

Apple scrubbed the floor clean of all existing text-bombing apps in the iOS App Store, and even though there were once a ton of these apps in Cydia, the go-to store for jailbroken devices, there few and far between these days. If they do exist, they either cost money or don't work as advertised.

All of my hacks up to this point have been operating system hacks. In other words, we have exploited a vulnerability usually in an operating system service (SMB, RPC, etc.) that all allow us to install a command shell or other code in the target system.

Tripwires are a new mechanic released in Minecraft 1.3, and people are still trying to figure out how best to use them. Minecart returns are a great idea, but what about traps?