PDF is a convenient format for documents that can embed text and pictures and can be read by almost any device—personal computers, laptops, smartphones, etc. However, PDFs are mostly read-only files, so sometimes it's necessary to convert them to JPG images, a universal format for pictures. JPGs can be modified by software such as Adobe Photoshop or posted on Facebook.

Some of you may stick with your iPads, but for those looking for a similar Android version, you finally have a winner.

A lot of different places have computers with controls on them for several things; some have controls for installing software, some for running software, blocking websites, opening certain file formats, etc.
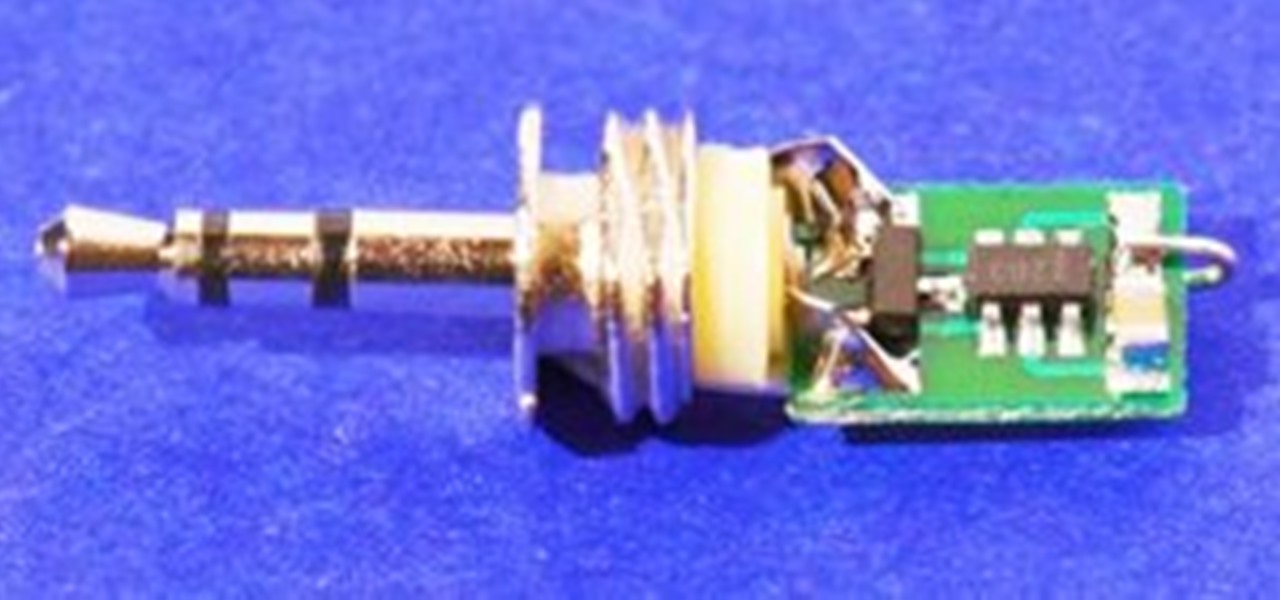
This morning, I received a message from a friend who was reading a hack log, and she had some questions about the commands used. This got me thinking, as Linux has a ton of commands and some can be archaic, yet useful. We are going to go over everything you need to know to read a hack log and hopefully implant the steps in your head for future use.

A few days ago, CloudOn released their free mobile app that brought Microsoft Office directly to your Apple iPad. The cloud-based service effectively runs Office on their end, allowing you to use apps like Word and PowerPoint to edit your documents, which you would house in Dropbox. But after overwhelming demand, they removed the free app yesterday from the iTunes App Store.
Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server. You may know that Minecraft is an excellent creative tool, but perhaps less well known are the fascinating array of redstone powered games that have been made by players like you.

If you're a lucky owner of the iPhone 4, you know that the upgrade to its camera app includes a front-facing camera feature which acts like a video cam on your computer. Apple, of course, intends the front-facing feature to be mainly used for the FaceTime application which enables you to hold video phone conferences with other iPhone 4 and Mac users who have FaceTime installed on their device. This is all well and good, but there several other ways the front-facing camera can be used.

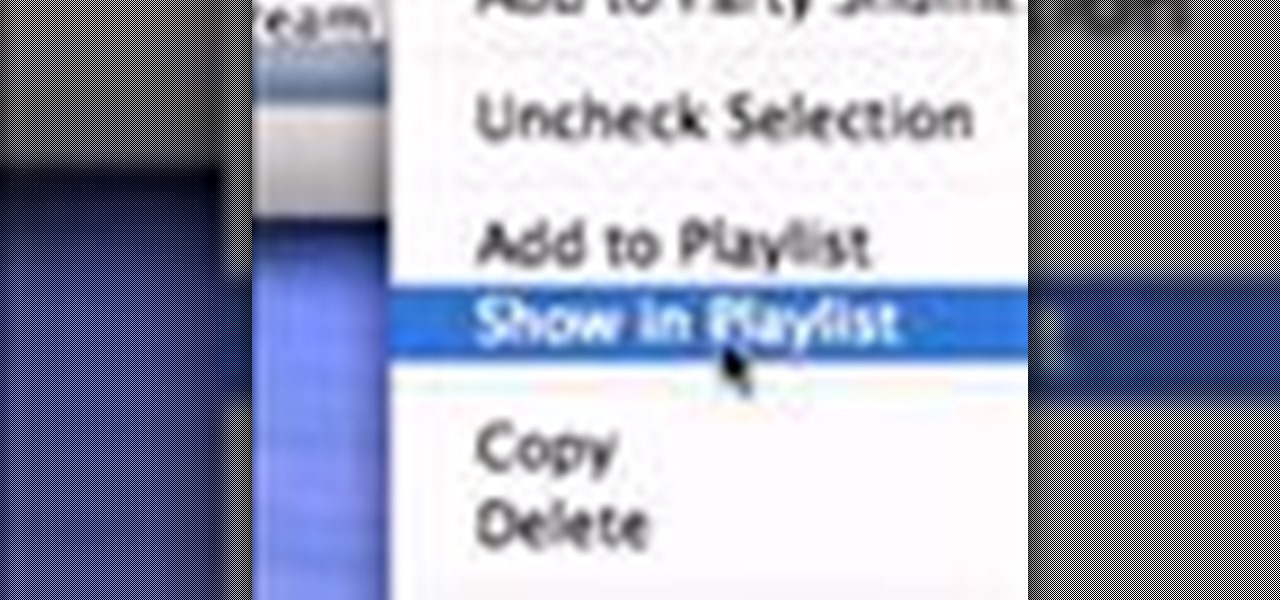
This video explains how to display in iTunes the playlists a certain song appears in, focusing on Macs. All you have to do is open itunes, and select show in playlist. Find out the number of playlists a song appears in.

A man in a Hawaiian shirt shows how to arrange a parallel flower arrangement. No verbal instruction, but video clearly displays the techniques in accomplishing this arrangement. Create a parallel flower arrangement.

We've provided Google insiders, Google's community managers, authors, and celebrities for you to add to your circles. This week, we've discovered over 100 brilliant photographers for you to follow.

Decorating With Entertainment in Mind Sure, when you're throwing a party it's easy to put up balloons and streamers, but it's easy to forget one of the most important things: memories. You know all that money you spent on entertainment? The clown? The magician? You're naturally going to want to snap some photos, but if you don't decorate properly, the photos will be bland. And that's just one of the potential problems.

Get ready to learn a cool trick where a ribbon is cut in half and then magically fused back together! You will need some ribbon, an envelope, and some scissors. Sometimes we use materials that require adult supervision... like scissors, so make sure you have friends and family around whenever you do magic tricks. 1. Preparation: Cut the ends off of both sides of the envelope.

Propaganda and indoctrination at it's peak. My friends, today, when I was browsing through the net for news, I noticed something on MSNBC. It was a very short article, with a title that just wasen't true. Before talking about it, let me tell you why this is important.

Today, we are going to combine what we learned from the Introduction to Cryptography article with our Java programming skills. If you are new to Java, check out Matthew's Learn Java: Part One for a quick beginner's lesson, or check out some of the Java tutorials directly on Oracle.

Looks like Minecraft is getting some cool new features, including editable books and colorful wooden half slabs. Check out the video below to see the newest Minecraft Snapshot 12w17a in action. Warning: This release is for experienced users only! It may corrupt your world or mess up things badly otherwise. Only download and use this if you know what to do with a minecraft.jar file!

In my opinion, Isaac Newton is definitely the number two astronomer, right below Galileo Galilei. His discoveries were very important to uncovering the secrets of space, and he deserves to be remembered.

Here's another delicious Byte. Ucha Gobejishvili, a Georgian Security Researcher under the handle of longrifle0x, discovered two cross site scripting (XSS) vulnerabilities on the official website of Forbes. He discovered the hole in two different locations on the site, and has already informed the website of the vulnerability.

Null Byte is looking for forum moderators! Last Friday's mission was to accomplish solving HackThisSite, basic mission 9. This mission delves a little further into Unix commands and remote directory traversal (which is just a fancy term for going through folders blindly).

Your BIOS, or Basic Input Output System, is the firmware on your motherboard responsible for initializing your computer's hardware when it is first powered on. It probes for video adapters, RAM, the whole works. The BIOS provides a small library of basic input/output functions used to operate and control the peripherals such as the keyboard, text display functions and so forth, and these software library functions are callable by external software such as the OS and system software within sai...

Null Byte is looking for moderators. More threats to computers exist every day. Not only do we have computer viruses and malware, but we have rootkits and other nasty pieces of code that can log your keyboard strokes or even add your computer to a botnet to attack other websites. Your computer can be infected even if you have anti-virus software installed. I can't stress enough how easy it is for a hacker to write a piece of code that gets around every piece of anti-virus software.

Users of the latest AMD 6xxx series graphics cards may have noticed that when they are playing Skyrim, their framerate isn't anywhere near what it is supposed to be with dual GPUs in Crossfire. AMD is working on releasing drivers with these issues fixed, but it has been too long since Skyrim has come out to just sit and wait.

Anonymity is something that doesn't exist today. Everything you do in the world is tracked, from the purchases you make to surfing the internet—even taking pictures on your iPhone. Everything you have ever said and done on the internet is still there—somewhere. This is called caching. For example, when a site is down, you can view its cached page on Google.

With the plethora of programming that we promote at Null Byte, I figured a lot of you newbies that stop by IRC will need a big boost in the right direction to make your dive into programming a lot easier. A hot question that has been thrown around in IRC a lot when making the initial dive is, "How do I write code?". People who do not know much about computers can't understand how code is written. Code that we write here is usually scripted and written in Python, so we will use it as our examp...

Password strength and encryption are important things when it comes to computers. A password is the entire security of your computer, and OS passwords are not hard to break. Most users believe that if you have a password on your computer via the OS, that you are safe. This is not true at all, sadly.

Social networks like Facebook and Google+ are great for staying connected with family, friends and coworkers—even fans. But sharing and communicating with practically anyone in the digital realm has alienated us from most of the flesh-and-blood beings we see everyday—our neighbors. How well do you know your neighbors?

VERONICA n pl. -S a handkerchief bearing the image of Christ's face 63 points (13 points without the bingo)

One of the biggest video games events of the year is about to happen in Japan tomorrow, when the Tokyo Game Show (TGS) kicks off. If you've never heard of it, just think of it as the E3 of the East—a video game extravaganza open to both businesses (Thursday and Friday) and the public (Saturday and Sunday). And even though it hasn't officially started, TGS has already released some grand announcements, specifically about Nintendo's future lineup and a precipitous drop in their share prices.

You may not know him by name, but Eric Leebow is the man we can all thank for inventing social networking. At least, that's what he thinks.

You may not do it in public, and you might not admit to it among your friends, but you do it. We all do it... sing. We sing when we're alone in our cars, at home when no one's listening, and when we've had a little too much to drink and don't care anymore, all inhibitions aside. We love to croon and belt out lyrics to our favorite songs because it makes us feel good, no matter how good or how awful we are, or how well we know the words. Well... now you can at least be proud of one of those th...

Mozilla is scheduled to release their updated Firefox browser on Tuesday, bringing the popular web browser up to version 6. Lately, the Mozilla team has been releasing newer versions of Firefox without a slew of new features, focusing on fixing bugs and getting the improved product out as quickly as possible, in order to compete more rapidly with other browsers like Google Chrome.

If you're lucky, your digital camera has a built-in intervalometer that lets you operate the shutter regularly at set intervals over a period of time. Why would you be lucky? Because you can create some very awesome time-lapse videos, like the horribly beautiful eruption of a volcano or vivid star trails in the night sky. You can capture the stunning display of the northern lights or even document the rotting of your favorite fruit.

Tower defense games have covered a lot of creative ground over the last five years. They've gone from simple desktop amusements to a staple of the indie game scene, having been integreated into nearly every other type of game and released on every platform. They have taken place in ancient times, the far future, and on alien planets. But one place they (and most other types of video games) have never taken place is the real world. Not a virtual recreation of the world, but on the very terra f...

Video games are the most prevalent type of interactive media, but certainly not the only one. The interactive music video for the song "3 Dreams of Black" by supergroup ROME and digital artist Chris Milk utilizes the latest web design technology, video game influenced art and interactivity, and large crowd-sourced elements to form a compelling work of art. ROME is composed of producer extraordinaire Danger Mouse, Italian film composer Daniele Luppi, Norah Jones, and Jack White. Their recent e...

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

With give or take 250 million cars in America, odds are most city dwellers waste time hunting for parking spots. And while a smartphone app can't make free parking spots magically appear, it can aid in the searching process.

I've always wanted a gigantic saltwater aquarium, but maintaining a big, beautiful fish tank is not only time consuming—it's expensive. Also, it's a potential hazard if you have children, pets or any other uncontrollable elements around the house.

Introduction In this post we will look at how to access a PosgreSQL database in your C/C++ application. It's not as hard as you might think, but you need to understand the procedure and the functions used.

Whether it's the new iPad Killer or not, one thing's for sure—the Motorola XOOM is hackable. Just hours after its release last week, Verizon's new Android-based tablet (running Honeycomb) was rooted by hacker Koushik Dutta, which seems easy enough.

Immigration is a serious political issue in the United States, and those who oppose or support stricter immigration laws are often outspoken and candid about their beliefs, imposing their will on future legislation to not only politicians, but the general public—the voters. And what's the best way to reach the public? Entertainment.