One of the best things about Android is the ability to customize every aspect of your device to make it your own. However, unless you have prior knowledge or experience with every single setting available to you, you might have missed a few critical features without even knowing it. Some settings are easy to find, while others might be tucked away in another menu of their own.
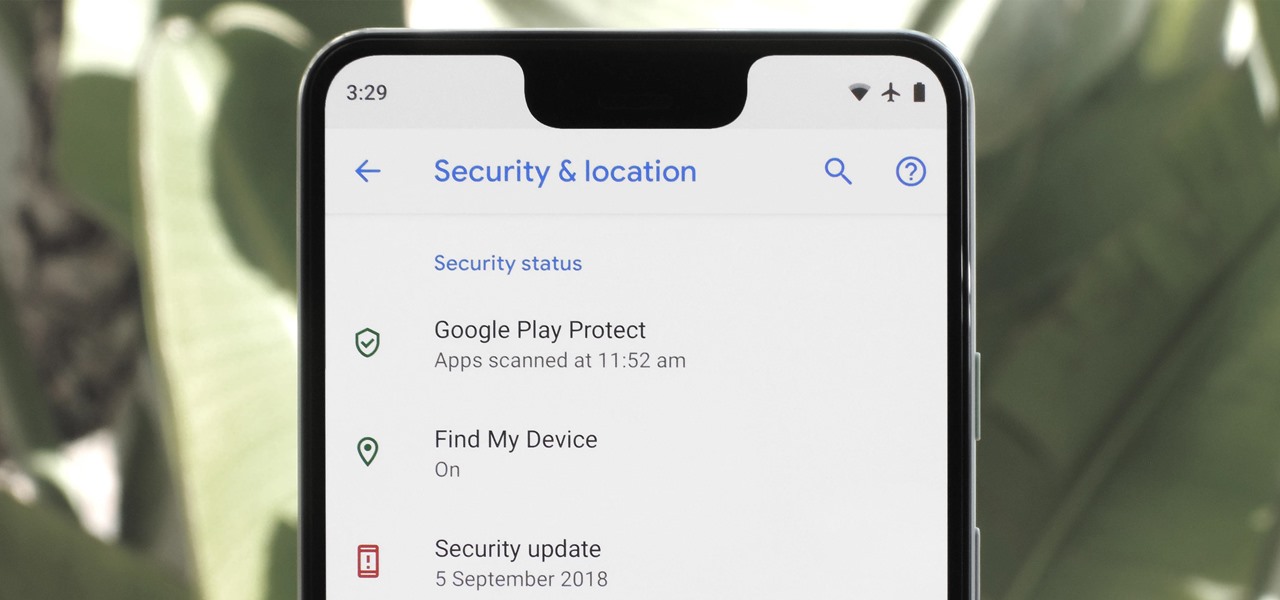
Android's settings menu is actually pretty daunting. There are options for nearly everything, so in the sea of various menus and submenus, it's easy to overlook important privacy and security settings. On Google's Pixel phones in particular, there are 20 such settings that you should double check.
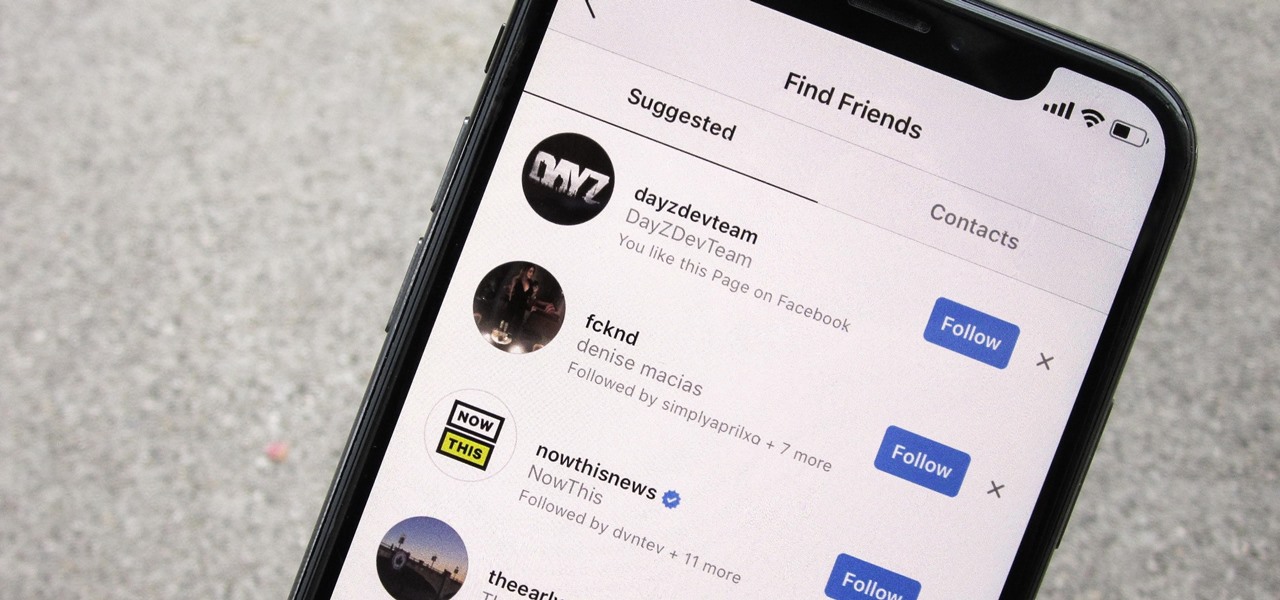
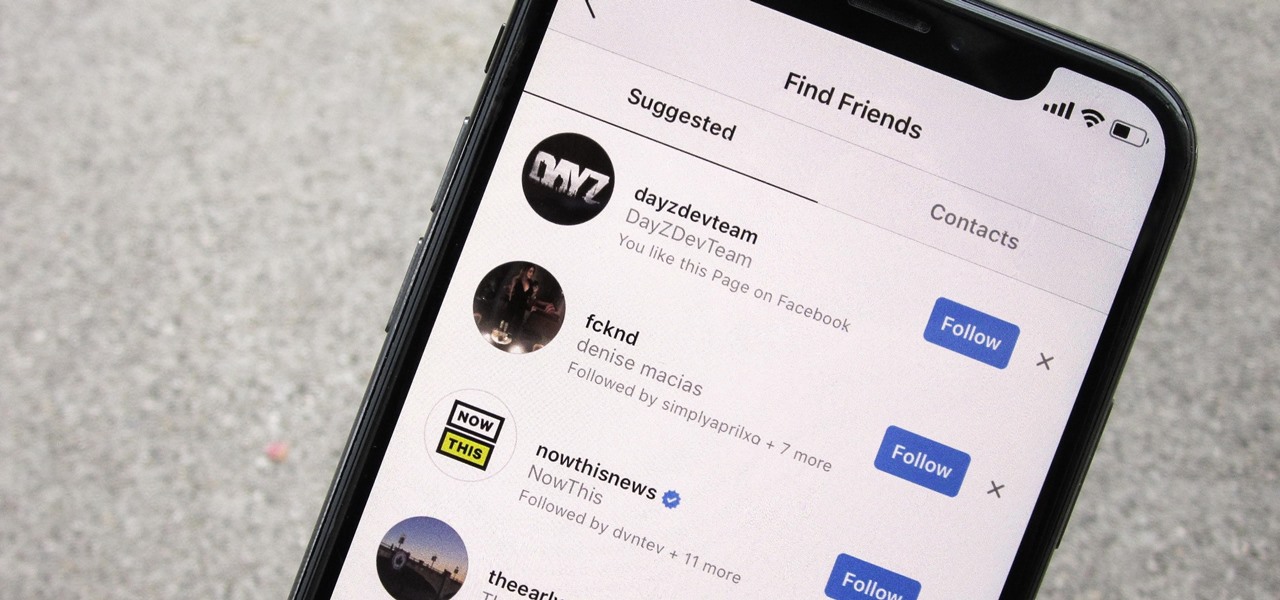
Sharing your personal information can come up for any number of reasons: you may want to get in touch with a colleague after work or you've been involved in a car accident and need to stay in contact with the other driver. Unfortunately, giving out information can be the key for others to find your social media accounts, such as Instagram, whether you want it to happen or not.

For the uninitiated, it can be difficult to buy that special hacker in your life a perfect holiday gift. That's why we've taken out the guesswork and curated a list of the top 20 most popular items our readers are buying. Whether you're buying a gift for a friend or have been dying to share this list with someone shopping for you, we've got you covered with our 2018 selection of hacker holiday gifts.

Contrary to popular belief, augmented reality apps have been available for a while now. I remember using the Layar app (still available for iOS and Android) to explore nearby businesses and landmarks with varying success via an early-generation Android handset.

Dark mode is simply a way of life these days now that both Android and iOS officially support it. Most major apps now use the system-wide setting on Android and iOS, and many had their own dark themes in-app before Google and Apple got with the program. But the social media giant Facebook took forever to implement a night theme, and some of you still may not be able to access it.

Privacy and security go hand in hand, especially for smartphones. When it comes to privacy, you decide what personal information about yourself is out there to discover. Security, on the other hand, is all about enforcing those privacy decisions.

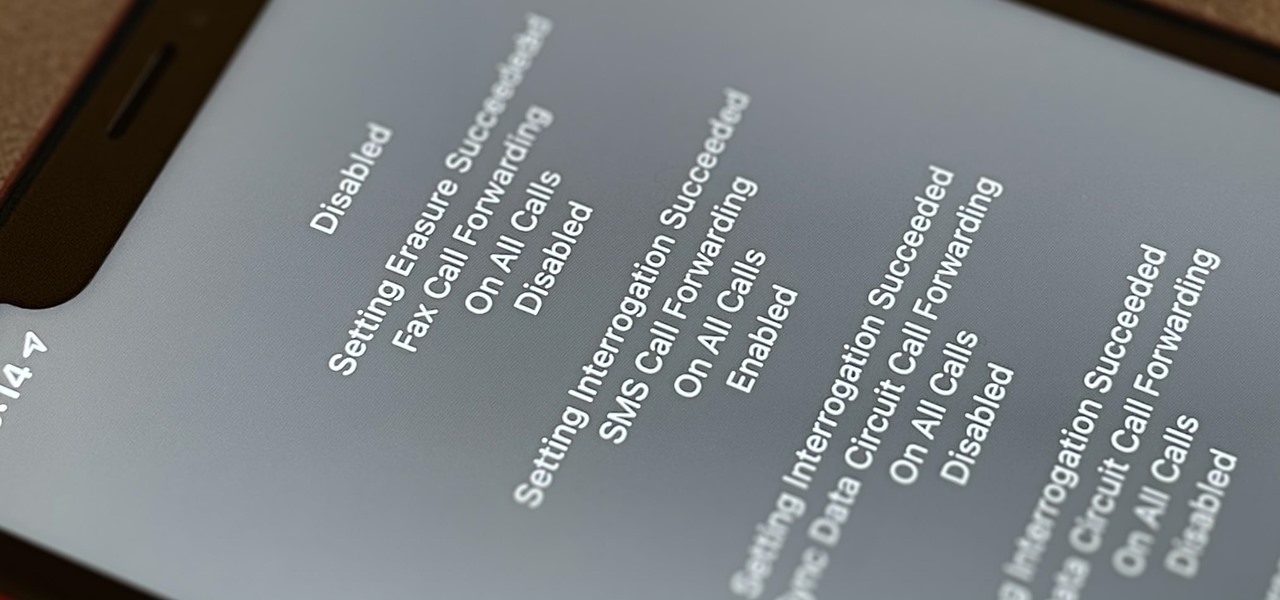
Malevolent hackers can divert your incoming calls and texts to any number they want, and they don't need to be a criminal mastermind to do it. Even friends and family members can reroute your incoming calls and messages so that they know exactly who's trying to reach you, and all it takes is seconds of access to your iPhone or wireless account. These secret codes can help uncover them.

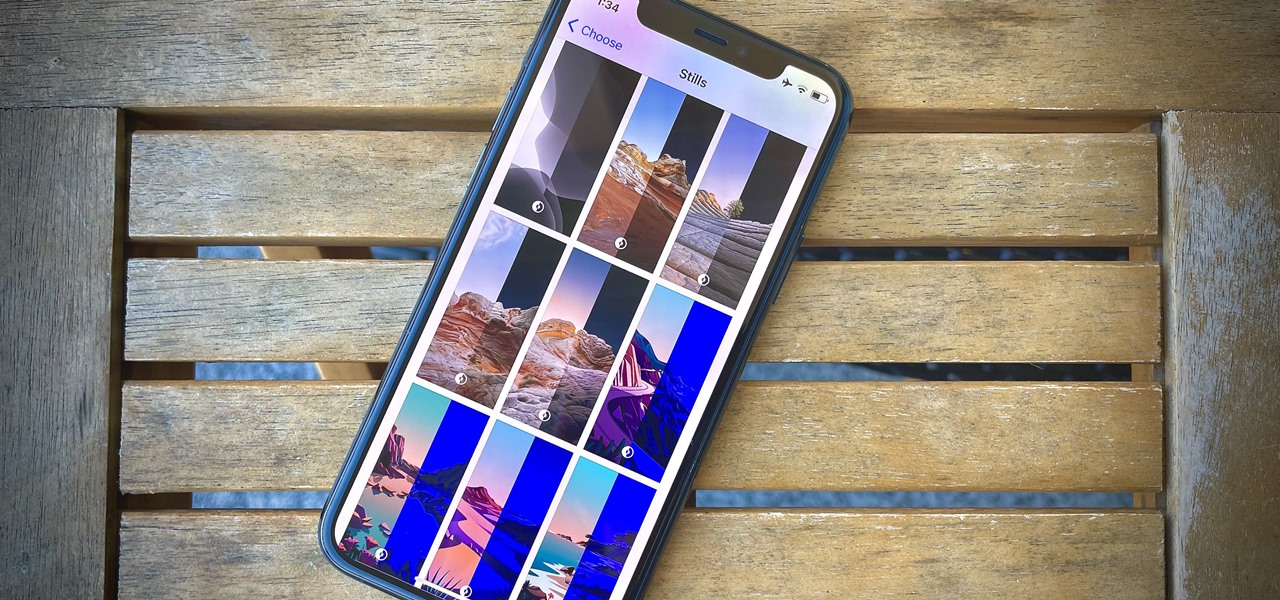
Apple's latest update, iOS 14.2, is finally here. As the name implies, it's the second major update to hit iPhones since Apple released iOS 14 in the fall. The update brings at least 13 new features and changes to all compatible iPhones, including over 100 new emoji and eight new wallpapers.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

Siri has long relied on basic sources like Google and Wikipedia for answers, but with iOS 18.2 and iPadOS 18.2, Apple is taking its virtual assistant to a new level by integrating ChatGPT. Now, you can use Siri to generate text and images with ChatGPT — and that's not all. ChatGPT is deeply integrated into Apple Intelligence and goes beyond just Siri.

Apple AirTags are super helpful for keeping track of your keys, backpack, and other frequently misplaced items, but there are some pretty clever things you can do with them beyond finding regularly used stuff.

An invaluable button on your iPhone can do hundreds, even thousands, of amazing things, but most iPhone users don't even know it exists. You can't push it. You can't click it. You can't press it. But it's the largest button on your iPhone, more powerful than the versatile Side button, and it's hiding in plain sight.

Apple's iOS 13 has been available for beta testing since June, and the stable release pushed out to everyone on Thursday, Sept. 19. To help you make the most out of iOS 13 for iPhone, we've rounded up everything you'll want to know, whether a colossal feature, small settings change, interface update, or hidden improvement.

Besside-ng is the hidden gem of the Aircrack-ng suite of Wi-Fi hacking tools. When run with a wireless network adapter capable of packet injection, Besside-ng can harvest WPA handshakes from any network with an active user — and crack WEP passwords outright. Unlike many tools, it requires no special dependencies and can be run via SSH, making it easy to deploy remotely.

Making anonymous prank calls got a little difficult for a while there in the early 2000's. Not anymore though! Between Skype and PrankDialer there are very few people that you can't prank call anymore without having to worry about them finding you. This video will show you how to use Prank Dialer to make prerecorded prank calls to whomever you want for free. Good times.

It might not be on the top of your to-do list but activating your Windows XP is simple and only takes a moment. No need to put it off any longer. You just need your product key and your computer and your ready to go.

So you just upgraded your Mac to OS X Lion and it greeted you, not with a friendly welcome video as Snow Leopard did, but instead with a tiny clip informing you that the Apple powers that be, have decided to reverse the 2-finger scroll direction, without even asking if you'd like to!

WikiLeaks. In recent weeks, it's been the hottest topic on the web. It's been attacked on a multinational level by political influence peddling.

Introduction The 3 major anonymity networks on the Internet are Tor/Onionland, I2P and Freenet. If you feel confused on which one is the "best" one to use the answer is simple. Use all three!

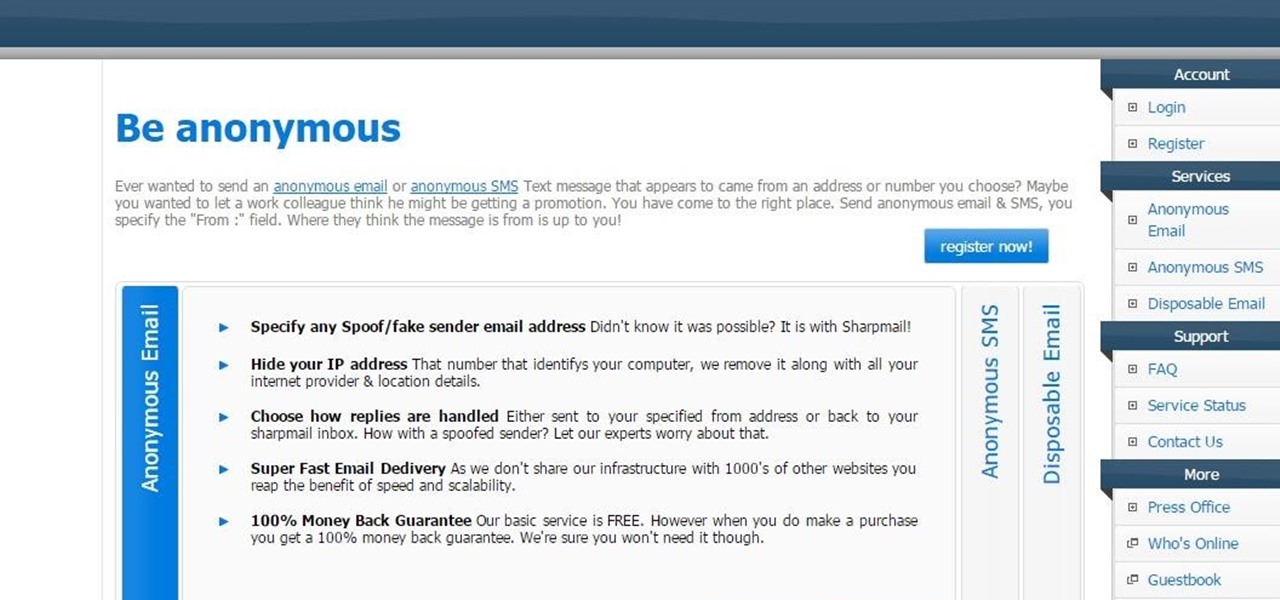
Anonymity is something that doesn't exist today. Everything you do in the world is tracked, from the purchases you make to surfing the internet—even taking pictures on your iPhone. Everything you have ever said and done on the internet is still there—somewhere. This is called caching. For example, when a site is down, you can view its cached page on Google.

IP Hider masks the real IP of a user, allowing him to browse all kind of pages without ever worrying that the ISPs or any other marketing tool is monitoring your surfing habits or spammers are attacking your computer. The simplest way to do this is to have traffic redirected through anonymous proxies.

A hacker from Anonymous broke off communication with an FBI agent posing as a Symanec employee after being offered $50,000 to not publish the Symantec pcAnywhere code online. And in a not surprising turn of events... the code was released today on peer-to-peer networks.
A cool link I found on Twitter that Anonymous tweeted. Get involved, this effects everyone.

A DIY most worthy of the archives: a magnificent skull constructed entirely of Mickey D's fries. Now if only it weren't just some anonymous web image, but a real DIY project complete with instructions. Anyone wanna step up to the plate?

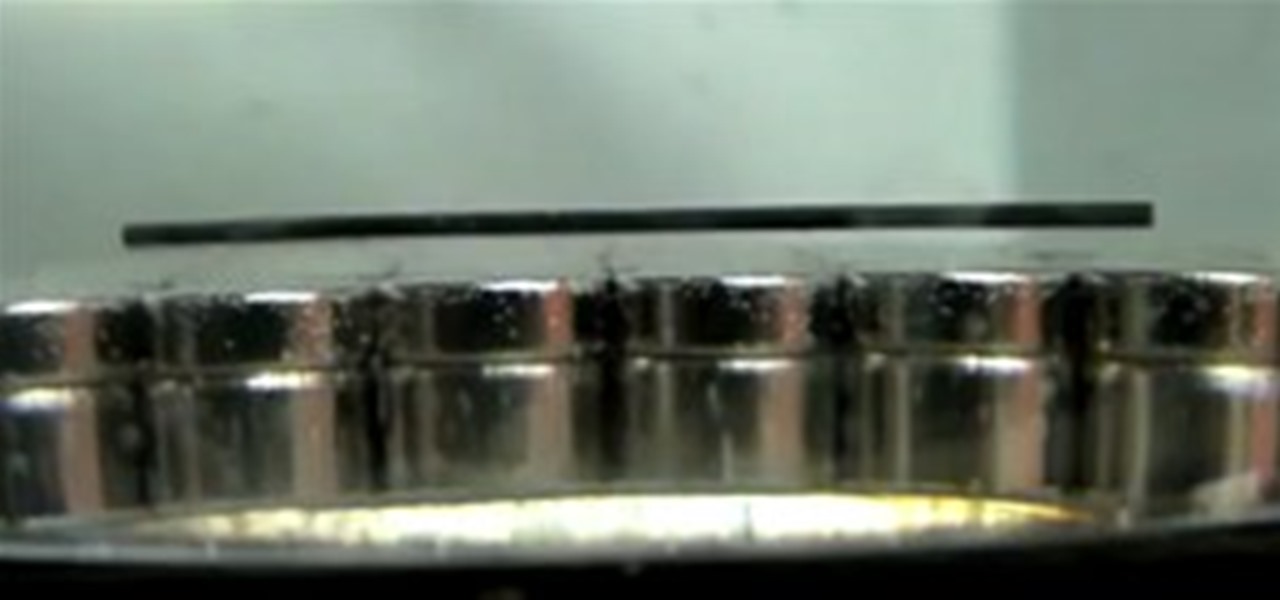
The anonymous doctorate of science, Nurdrage, is back with another fascinating HowTo (previously featured, glow sticks). Dr. Lithium's latest video demonstrates how to practice diamagnetic levitation using common household pencil lead and magnets.

A super cool anonymous woman rocks at playing the guitar... upside-down. I don't know about you, but I have yet to see a style quite this unique. That hand rolling move is awesome. Previously, 13-Year-Old Guitarist Wows Guitar Pros... and Yoko Ono.

Cinematographer Anna Foerster shot tests for Roland Emmerich's new period film "Anonymous". It's nice to actually see a test shot by a legit DP under controlled circumstances.

Welcome, The Geeks!! This is my first article on email spoofing and hope everyone likes it.

If Null Byte had a large Batman-like spotlight calling for help, we would definitely be using it right now. However, we don't, so this is my digital equivalent. Information security is a huge field, far too much for one man to cover adequately, so I need your help!

File Transfer Protocol, or FTP, is a network protocol made for transferring files in a client and host fashion over a Transmission Control Protocol (TCP) network, such as the internet. FTP is integrated into most browsers, and you have probably used it before. It is a common way to host files and transfer them easily. To access an FTP, a login is required, unless the server is configured to use anonymous logins (like the Arch Linux mirrors).

Most indie game developers will never see a million dollars in their bank accounts, and I certainly doubt that Eul, the anonymous developer responsible for the original version of Defense of the Ancients (DotA), expected to. But now even the fans can earn a little green. Some lucky and talented DotA players are about to win $1,000,000 for playing the unreleased sequel to the free unsupported Warcraft III mod from 2003.

Anybody who spends most of their day on the internet should know all about lulz. Lulz are most often jokes made at the expense of web users, as popularized on 4Chan. Today, a consortium of hackers called LulzSec is attempting (and in some cases succeeding) in efforts to shut down some of the games that offer web users a giant share of their online fun. World of Warcraft, League of Legends, EVE Online, and Bethesda Softworks have all been targeted by LulzSec's hacking efforts in the last week,...
We all know that VPNs may or may not keep logs, and may or may not tell the whole truth when asked about what records they do keep. With this in mind, here's the latest review of VPN services from those lovely folks at Torrentfreak. https://torrentfreak.com/vpn-anonymous-review-160220/

We've talked about the deep web before, but we never really covered the details of what's out there. It occurred to me that a nice list of resources would be very helpful to all of you anons out there. Think of this like a helpful brochure to the hidden web.

For a moment, picture a situation where you want to host some files or images, but you do not want it traced back to you. Perhaps you're working on a project with others and need secure data storage. Anonymity is the new shield of the 21st century—and you best protect yourself. As always here at Null Byte, we are trying to make that happen. Before someone can learn how to root a box, they need to learn how not to be found. I can not stress that point enough.

You've probably seen those deep-web images floating around on the Internet. Usually, it goes something like this: There is a towering iceberg and the deeper the underwater portion extends, the more “hidden” and “exotic” the content is described to be. Sometimes these images are accurate to a point, but most are just making things up.

Luxirare is a site of mystery; the genius behind the intricate and painstakingly photographed projects remains somewhat anonymous, despite her culinary mastery, fashion pieces and e-shop being featured in the likes of Vogue, Lucky Mag, ABC, NBC, and the New York Times. Insanely stylish and original, Luxirare has been blogged about all over the web.

...this anonymous dude for keeping it ingeniously simple. Who is he? No idea, but John Doe is now web famous. No need to spend all that time modifying pens and Coke labels. A coat sleeve will do just fine.

Calling all alchemists, it's time to make magic. Here's another lesson from our favorite mad scientist, Nurdrage (previously, DIY glow sticks & pencil lead levitaton).