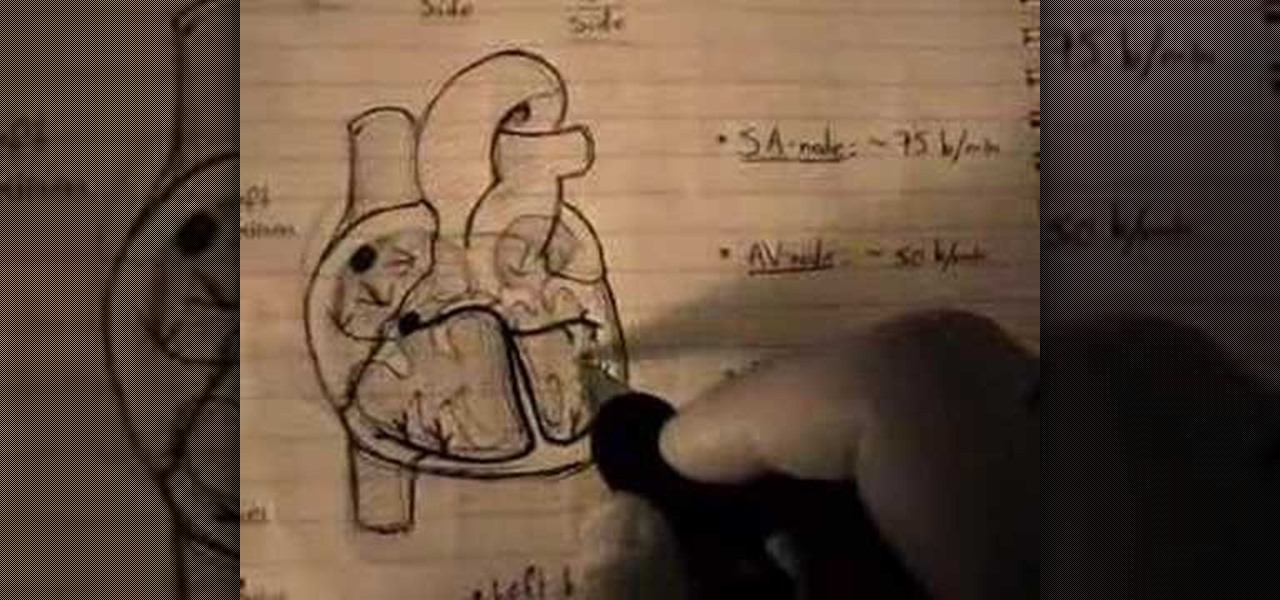
Attentions all science nuts: Check out this video tutorial on human cardiac action potential. If you are interested in anatomy, biology, and especially physiology, then you have to watch these educational videos.

Arduino is a language that's easy to learn and supported on many incredibly low-cost devices, two of which are the $2 Digispark and a $3 ESP8266-based board. We can program these devices in Arduino to hijack the Wi-Fi data connection of any unlocked macOS computer in seconds, and we can even have it send data from the target device to our low-cost evil access point.

If you like homemade light shows, this is one hell of a way to do it. AP Digital light shows you how you can hack a small fan into a special mirror used to create a poor man's PIC-based laser show. It's an experimental method of balancing a fan-mounted acrylic mirror for spirograph project.
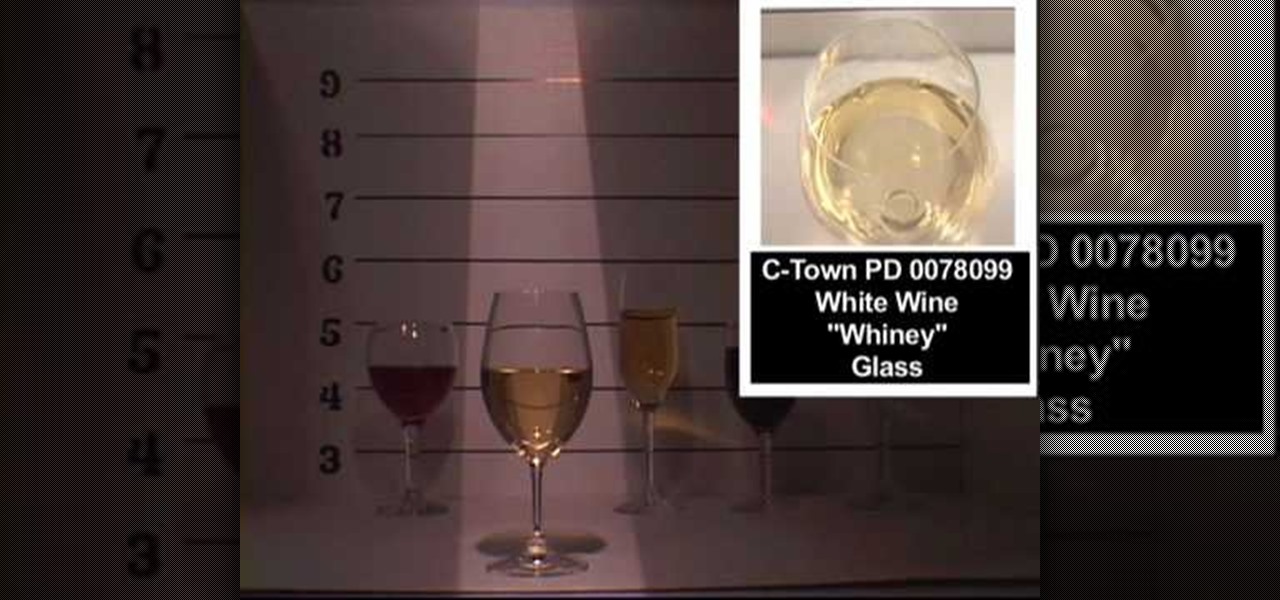
Don't know much about the dinner table? You know the basics: you eat from a plate, you use silverware to shovel it in and you drink from glassware. But what about if you're at a fancy dinner? Would you be able to distinguish a juice cup from a champagne glass? A white wine glass from a martini glass? If not, these two videos will show you which ones are which.
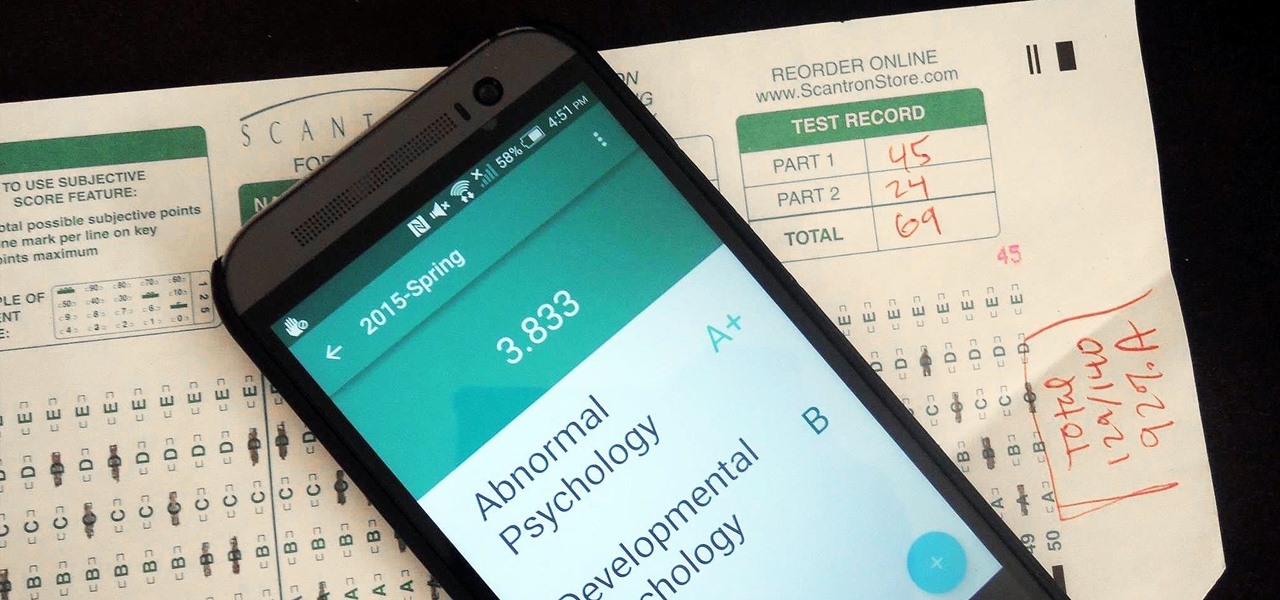
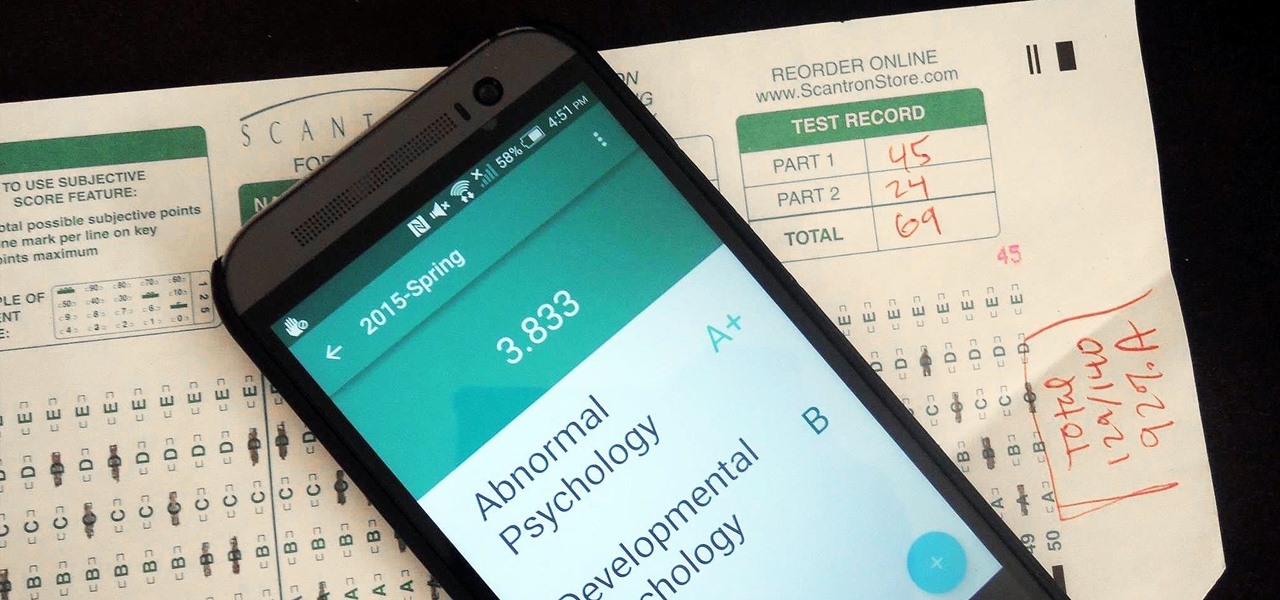
Even though my high school days are long behind me, I still find myself waking up in a cold sweat worrying about what my GPA is and what college I'm going to be able to get into. During those days I had to rely on coming up with my own equations to figure out my GPA between grading periods—including AP and honors course, as well as weights for pluses and minuses—but now there are smartphones to do all that thinking for me.

Welcome back, my tenderfoot hackers! We have looked at a number of ways that we sniff traffic on the network with such tools as Wireshark, tcpdump, dnsiff, and others, but each of these tools is only capable of pulling packets off the wire.

Unless you're a music theory buff or taking AP Music Theory in school (forced or otherwise), then the only word in "diatonic circle chord progressions" that makes sense to you is "circle." But the fancy schmancy term is just an elaborate way of saying you're playing chord progressions based on the circle of fifths.

After establishing itself as a leader among media companies in augmented reality in journalism over the course of 2018, The New York Times pulled back from the technology this year.

A flaw in WPS, or WiFi Protected Setup, known about for over a year by TNS, was finally exploited with proof of concept code. Both TNS, the discoverers of the exploit and Stefan at .braindump have created their respective "reaver" and "wpscrack" programs to exploit the WPS vulnerability. From this exploit, the WPA password can be recovered almost instantly in plain-text once the attack on the access point WPS is initiated, which normally takes 2-10 hours (depending on which program you use).

If you're trying to learn a new skill, you wouldn't want to waste your time learning from someone with sub-par experience. No, you'd want to learn from the very best of the best to ensure you're getting a quality education.

The augmented reality team at USA Today closed out a prolific year of immersive storytelling with a hard-hitting companion piece exploring the controversial conflict in Afghanistan.

While a new museum to house the original torch of the Statue of Liberty is under construction on Liberty Island and scheduled to open in May 2019, New York Times readers can now view the sculpture in their own space through augmented reality.

You've got some free time, so you decide to try out that new puzzle game on the App Store. After a half hour of fun, the game stops. It seems you've run out of lives, and have to wait until tomorrow to play ... unless you drop $0.99 on extra lives. What are you going to do, wait until tomorrow? Some of us might, but others ... not so much. If you dropped some cash to keep playing for the day, you, I'm sorry to say, were played. And this video shows you why.

With tools such as Reaver becoming less viable options for pen-testers as ISPs replace vulnerable routers, there become fewer certainties about which tools will work against a particular target. If you don't have time to crack the WPA password or it's unusually strong, it can be hard to figure out your next step. Luckily, nearly all systems have one common vulnerability you can count on — users!

Welcome back, my aspiring hackers! As I mentioned in earlier posts, the best hackers (or at least those not behind bars) have a keen understanding of digital forensics. If I am tasked to intrude upon an enemy's file server to retrieve war plans, such as in this tutorial, it is essential to my country's (and my own) well-being that it not be traced back to me. Understanding digital forensics helps us to leave without a trace and never have a trail back to us or our employer.

Welcome, my hacker novitiates! As part of my series on hacking Wi-Fi, I want to demonstrate another excellent piece of hacking software for cracking WPA2-PSK passwords. In my last post, we cracked WPA2 using aircrack-ng. In this tutorial, we'll use a piece of software developed by wireless security researcher Joshua Wright called cowpatty (often stylized as coWPAtty). This app simplifies and speeds up the dictionary/hybrid attack against WPA2 passwords, so let's get to it!

MacOS isn't known as an ideal operating system for hacking without customization, but it includes native tools that allow easy control of the Wi-Fi radio for packet sniffing. Changing channels, scanning for access points, and even capturing packets all can be done from the command line. We'll use aliasing to set some simple commands for easy native packet capture on a macOS system.

When hacking Wi-Fi networks, having the right wireless adapter is essential. But hunting online for one can be a frustrating experience. To see how the handful of Kali-compatible adapters on the market measure up, I ran a series of tests to benchmark and compare their range, signal strength, and ability to enter monitor mode and perform packet injection. This should help you determine which adapter is right for your own hacking needs.

Greetings aspiring hackers. I have observed an increasing number of questions, both here on Null-Byte and on other forums, regarding the decision of which USB wireless network adapter to pick from when performing Wi-Fi hacks. So in today's guide I will be tackling this dilemma. First I will explain the ideal requirements, then I will cover chipsets, and lastly I will talk about examples of wireless cards and my personal recommendations. Without further ado, let's cut to the chase.

Android 5.0 "Lollipop" has only existed for a few months, but a leaked version of Samsung's take on the firmware has already been spotted in the wild. This update came straight from Samsung, and brings with it a plethora of new features, including greatly improved performance and a revamped TouchWiz UI.

Welcome back, my fledgling hackers! In the first part of my series on Wi-Fi hacking, we discussed the basic terms and technologies associated with Wi-Fi. Now that you have a firm grip on what Wi-Fi is exactly and how it works, we can start diving into more advance topics on how to hack Wi-Fi.

You know YouTube is able to host high-defintion video content online now, right? Well, how do you watch it, or make it, or embed it? Well, this video tutorial will show you how to upload, embed and watch 720p HD video on YouTube. This YouTube hack will let you watch and embed videos in true 1280x720 high definition.

Thanks to modern "smart phones" and the internet, media by the people, for the people is finally a reality. Here's how to use your phone to be a mobile journalist.

It's no secret that devices leak data, but sometimes they do so in ways you may not expect. Your phone, laptop, printer, and IOT devices leak Wi-Fi information that can (and is) used to track you.

WPA Enterprise is widely used in large corporations as it offers individual and centralized control through a server that authenticate the users (RADIUS server). In this tutorial I will show you how to break the barrier and obtain the user credentials.

Welcome back, my greenhorn hackers! In previous Wi-Fi hacking tutorials, I have shown you ways to create an Evil Twin, to DoS a wireless AP, and to crack WEP and WPA2 passwords, but in this tutorial, I will show you something a little bit different.

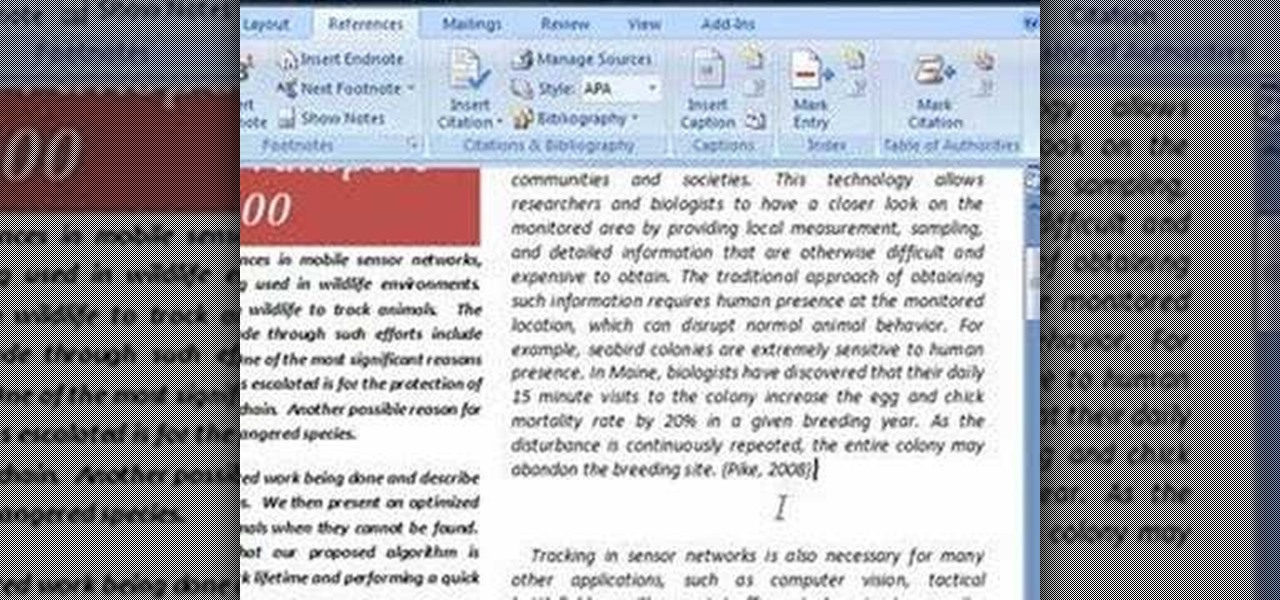
In order to use the bibliography feature in Microsoft Word 2007, you will need to begin by opening your document in Word. Find the place where you would like to add a reference. Place your cursor in that spot. Then, go to the tool bar. Click on "Insert Citation". Click on "Add New Source". When the pop-up opens, enter the information about the periodical or book that you are citing. Fill it in completely. Make sure you choose the type of material you are referencing in the top drop down menu....

Augmented reality's status as a new storytelling medium has already led to the reinvention of filmmaking and journalism.

In an effort to raise awareness regarding the impact of emissions on the environment, Snap has partnered with the United Nations Environment Programme to use augmented reality to show how much ocean levels will rise over the next 80 years.

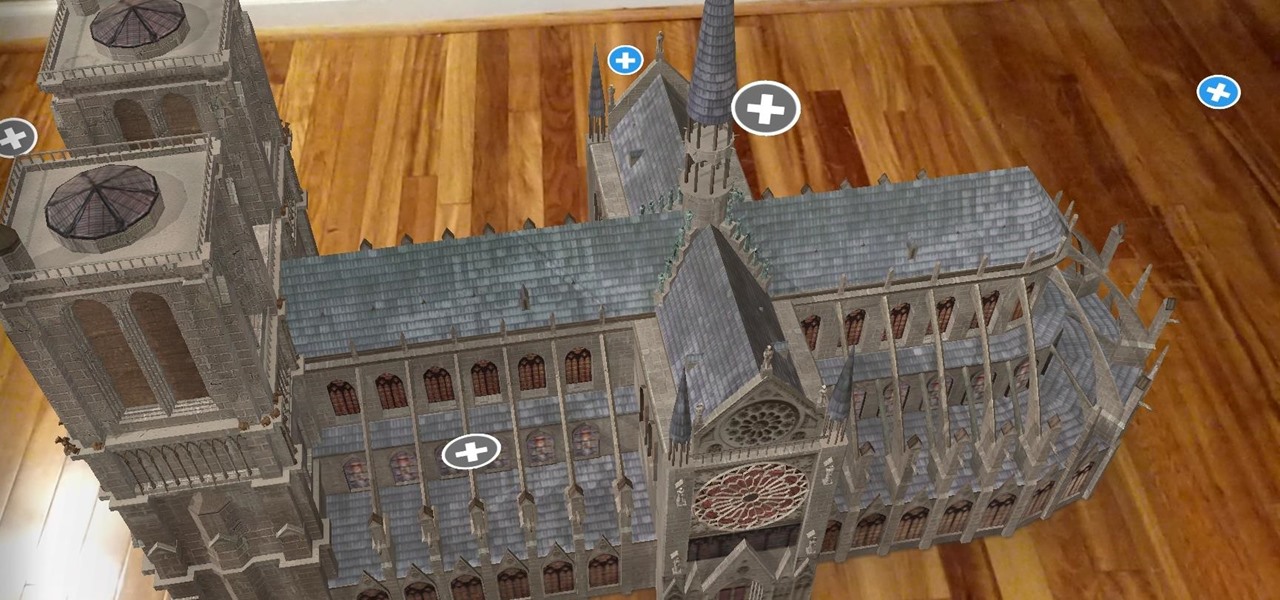
On Monday, the world watched in horror as the historic Notre Dame Cathedral went up in flames in Paris.

To punch up the launch of its new podcast, USA Today has created an augmented reality experience to introduce listeners to the story of corruption in Chicago.

Although The New York Times may have won the race in terms of presenting coverage of the 2018 Winter Olympics through augmented reality first, The Washington Post is nevertheless working to compete in AR in a different way—via gaming.

After devoting a number of resources toward developing VR content to modernize the delivery of its news content in recent years, The New York Times is expanding its capabilities to include augmented reality as well, a mission outlined in a manifesto published on Thursday.
Most of you lot would be aware what WPA/WPA2 is so I won't bang on about the encryption or protocols a great deal. In short WPA and WPA2 both have a maximum of 256bit encrypted with a maximum of 64 characters in the password. The encryption is really only 64bit but x 4 because of the way the authentication functions as a 4 way handshake.

Welcome back, my budding hackers. So many of you are interested in hacking Wi-Fi that I have decided to revisit my Wi-Fi Hacking series with some updated and more in-depth material. I strongly suggest that you look at some of my earlier posts, such as "Getting Started with Terms and Technologies" and "Getting Started with the Aircrack-ng Suite of Wi-Fi Hacking Tools," before continuing here. If you're ready, you can also check out our updated 2017 buying guide here.

Written news was first delivered by an elaborate courier service used by the Pharaohs nearly 4,500 years ago. About 2,300 years later, Romans would post public announcements via bulletins carved in metal or stone. Fast forward 1,600 years to the first monthly handwritten gazette published in Venice, the forefather of modern newspapers, which didn't become commonplace until the early 17th century.

Welcome back, my neophyte hackers! Have you ever had a neighbor that you're certain is up to no good? Maybe you've seen him moving packages in and out at all hours of the night? Maybe you've seen people go into his home and never come out? He seems like a creep and sometimes you hear strange sounds coming from his home? You know he's up to no good, but you aren't sure what it is exactly.

It's not an official app, but for fans of Rick and Morty, it's a welcome piece of the series' universe until the recently renewed animated show returns to Adult Swim.

The Android 4.4.2 KitKat update is available via firmware upgrade for the international GT-N7100 variant of the Samsung Galaxy Note 2, about a month after we saw its first leak. The update is available via Kies in France, with and OTA update soon to follow. Details courtesy of SamMobile are as follows:

A macOS computer can reveal a lot of information about the owner, including which Wi-Fi network they have permission to access. With an Arduino-based attack, we'll use a five-dollar setup to inject a rogue Wi-Fi network and steal the list of trusted Wi-Fi networks, allowing us to see where the computer has been.