As Microsoft unveiled their new Windows Phone 8.1 software update yesterday, undoubtedly the most memorable takeaway was their showcase of Cortana. Competing directly against Apple's Siri and Google's Now, Cortana is Microsoft's entry into the digital voice assistant fray, and the official replacement to their search app.

Whether you've been fully converted or just want a little Apple with your Android, adding your iCloud email to your Galaxy Note 3 is a fairly simple task. Usually, Apple and Android don't play nice, but your iCloud address can be added to your stock email app just like any other email account.
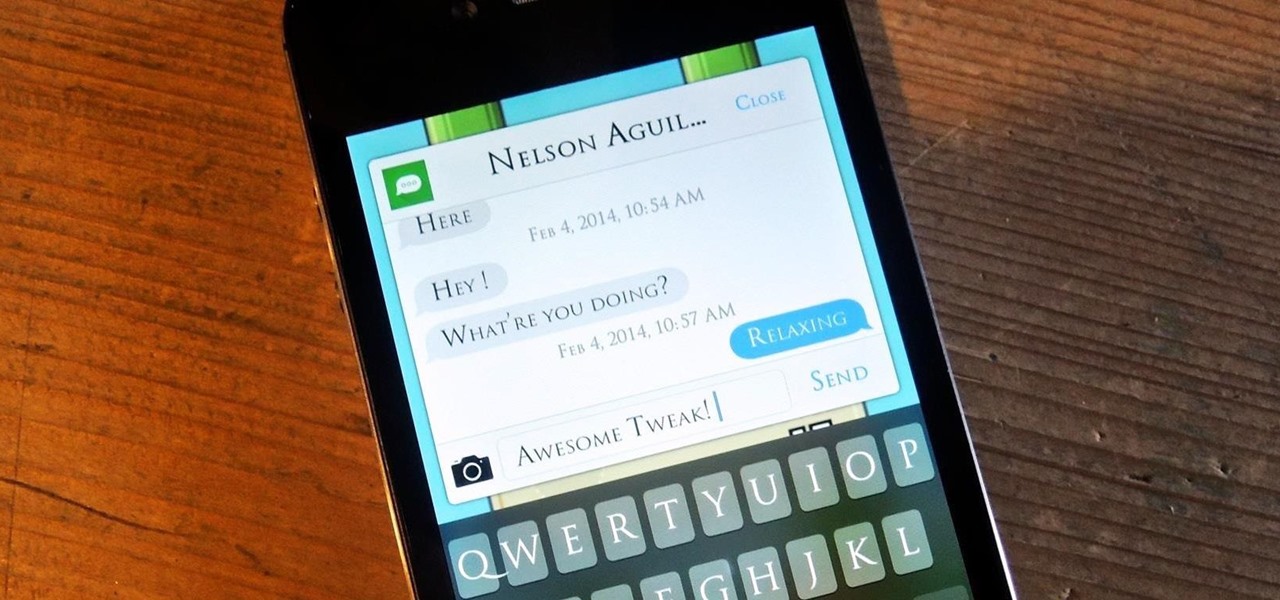
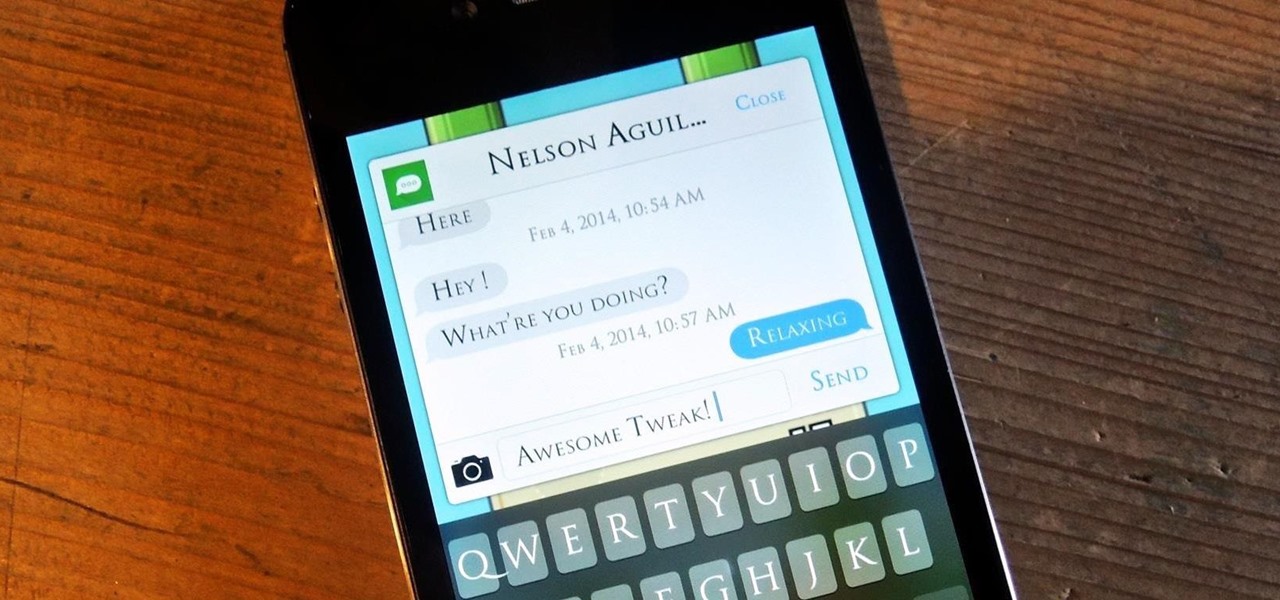
Texting can be difficult sometimes. When you're browsing the web or playing a game on your iPhone and need to respond to text message real quick, you have to exit your current app to do so. Not exactly efficient, especially if a quick "K" is all you need to say.
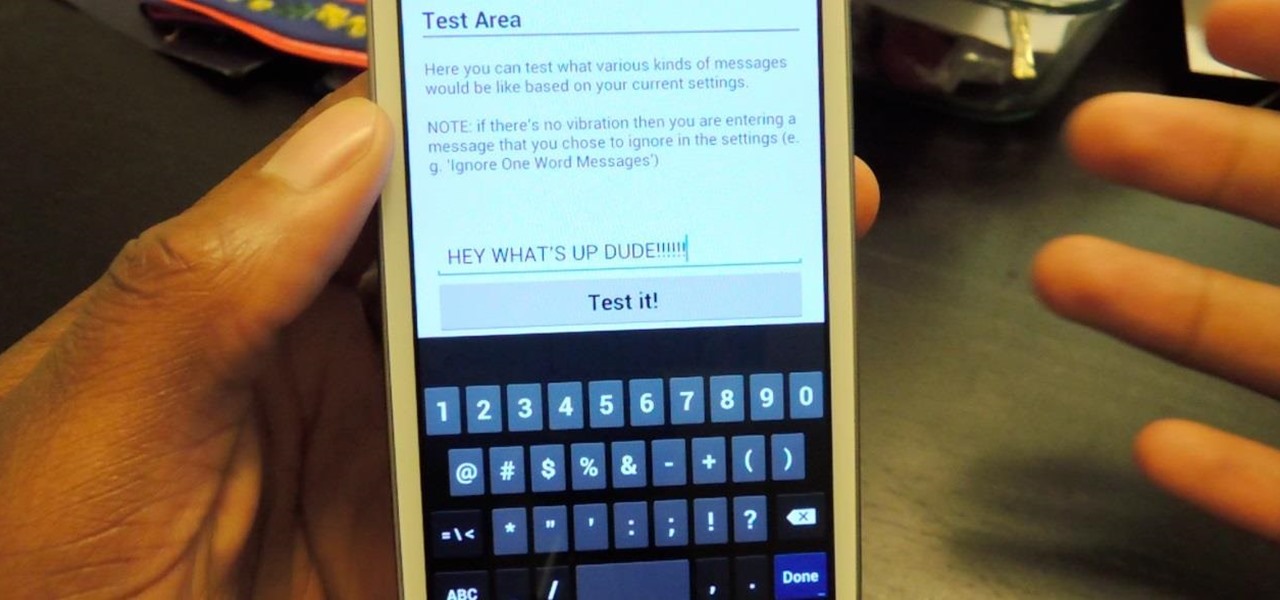
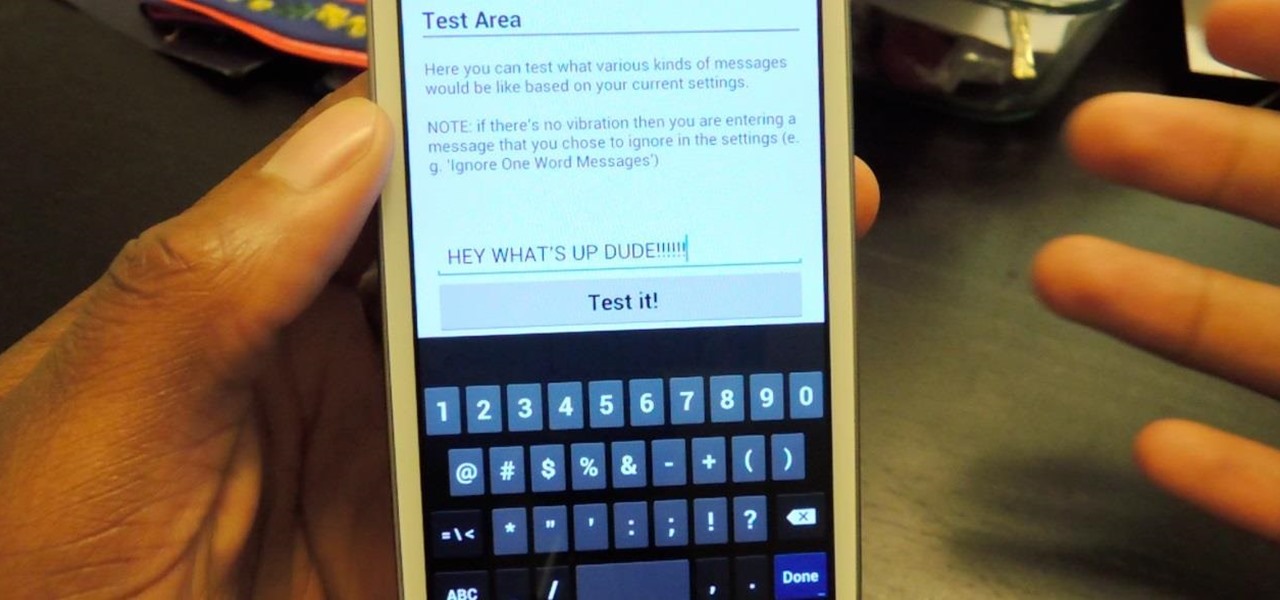
The constant stream of beeps and the buzzes coming from your Samsung Galaxy S3 can soon begin to fade into the background and remain forgotten. With smartphones vibrating for email alerts, Candy Crush notifications, phone calls, and text messages it can become difficult to tell which alert is which.

The holiday season wouldn't be the same without decorations. Ornaments and fancy lighting brightens up a neighborhood and helps spread the holiday cheer. While decorations and Christmas lights are fantastic, why not get a little more creative and some fun in the process?

For over 20 years, a tiny but mighty tool has been used by hackers for a wide range of activities. Although well known in hacking circles, Netcat is virtually unknown outside. It's so simple, powerful, and useful that many people within the IT community refer to it as the "Swiss Army knife of hacking tools." We'll look at the capabilities of Netcat and how the aspiring hacker can use it.

Welcome back, my greenhorn hackers. When Wi-Fi was first developed in the late 1990s, Wired Equivalent Privacy was created to give wireless communications confidentiality. WEP, as it became known, proved terribly flawed and easily cracked. You can read more about that in my beginner's guide to hacking Wi-Fi.

Welcome back, my greenhorn hackers! Now that we're familiar with the technologies, terminology, and the aircrack-ng suite, we can finally start hacking Wi-Fi. Our first task will be to creating an evil twin access point. Many new hackers are anxious to crack Wi-Fi passwords to gain some free bandwidth (don't worry, we'll get to that), but there are so many other Wi-Fi hacks that are far more powerful and put so much more at risk than a bit of bandwidth.

Welcome back, my fledgling hackers! In the first part of my series on Wi-Fi hacking, we discussed the basic terms and technologies associated with Wi-Fi. Now that you have a firm grip on what Wi-Fi is exactly and how it works, we can start diving into more advance topics on how to hack Wi-Fi.

Can't decide between the Galaxy S4 or the Galaxy Note 2? There are advantages to both the Galaxy S4 or the Note 2, it all boils down to what your needs are such as screen size, battery life, and more.

We'll show you how to use an attachment for a power washer called a "Foamer" - you'll never hand wash a car or boat again!

Welcome back, my newbie hackers! Hackers often are associated with clandestine and illegal activity, but that is not necessarily always the case. Hackers are increasingly being used and employed for law enforcement, national security, and other legitimate purposes. In this installment, we will look at how a single hacker could save the world from nuclear annihilation.

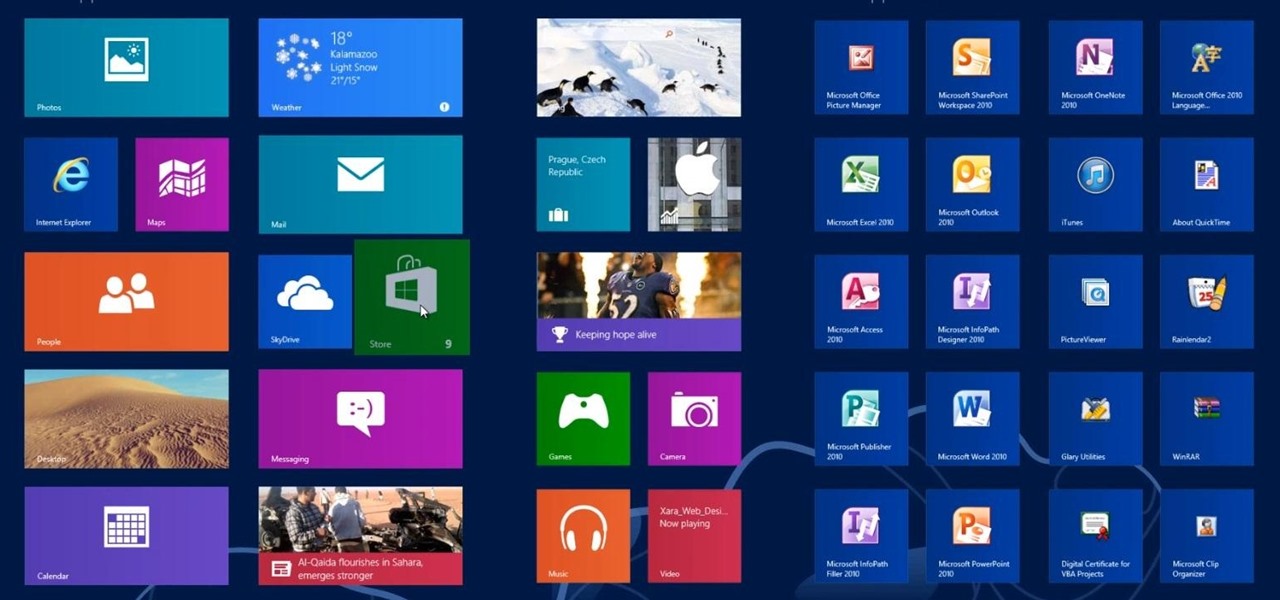
In this Windows 8 Tutorial you will learn how to search for application in the Windows 8 store. I know it can be a bit confusing for those who have just moved to the Windows 8 store on how to search for store applications in fact it took me like an hour to figure out how to search because all the visual cues were hidden away. However when you finish watching this Windows 8 tutorial you will see it is as easy as being able type on your keyboard to find applications in the Windows 8 store.

This Windows 8 tutorial, I will show you how to change the name of groups, and rearrange groups and applications in the Windows 8 start menu metro interface.

In my last hack blog on crashing your roommates Win7 system, we started looking at client- side attacks. As promised, we will be looking at some more client-side attacks.

Automator is a built-in Mac utility found in Mac 10.4+ and can be used to convert a PDF file to text format.

Programs that run automatically every time you start your computer can slow down your boot time—or just be plain annoying. Many of these programs are rarely used and don't even need to be running for your computer to function properly. So, if you want to disable these auto-run programs and increase your computer's startup speed, here are a few ways you can do it in the new Windows 8.

Here's a video on how to deal with pedestrian crossings in England. It's to help all of you taking driving lessons in Nottingham and the surrounding area, and can be used before or in-between your training.

Gardening school is in session and Shirley is teaching the absolute basics, such as: what to wear, what tools to use, what is the difference between an annual, perennial, and biennial? What is a garden zone, and which one is yours? Class is in session, so spit out your gum and listen up. Time to learn Gardening 101.

In my first few articles, we focused on operating system hacks. These hacks have been primarily on older operating systems such as Windows XP, Windows Vista, and Windows Server 2003.

Until recently, brainwave-reading devices have pretty much only existed in science fiction. Sure, electroencephalography (EEG), the technology that powers these devices, has been used in medicine and psychiatry since the late 1800s, but diagnosing people's brains and reading their minds are two totally different things. The first EEG headsets available to the public were used mostly in gaming and even in fashion, but in the last few years, they've gotten a little more sophisticated.

As an adult you will come a cross a point in time when you need to make the right impression by writing a formal letter. Follow the format and you will be able to be most effective at conveying the information in your letter.

When interviewing for a job, it is important to stay calm and answer the questions honestly. Answer interview questions with applicable information to the position, and be clear and concise with the answers with tips from a career adviser in this free video on job guidance.

Take a look at this video and learn how to hack into a wireless Linksys router. This hack isn't applicable for all security enabled networks, only ones that use generic passwords.

Mens jeans come in a ridiculously broad range of styles and sizes, from form-fitting to huge and baggy. Different body types look better in different types of jeans, and this video will teach you how to determine what types of jeans are best for you body type.

There are countless types of drum beats for every musical style and genre. Learn a few basic beats for different types of music with tips from a drumming instructor in this free music lesson video series.

Watch this video to put your Eee PC in advanced mode, which makes it look like XP. The steps are as follows

Our expert, Xi Chen, will show you how to say many different types of fruits names in Chinese. She will walk you step by step through each name and explain each one at a time. Since there is a lot of important detail in each these lessons are invaluable to the serious student!

In this how-to video series, learn how to type on a computer from expert typist and administrative assistant Jenifer Cononico. Jenifer will teach you how to type with tips and techniques such as proper computer typing posture, where to put your fingers on the keyboard.

In this series, learn about the different types of Native American flutes. You will be amazed by the various sounds and pitches that these instruments can produce. Let Werner John show you some different styles of Native American flutes. He also plays these flutes so that you can hear their distinctive sounds and pitches. So, start learning about wondrous world of Native American flutes today!

Let TutVid teach you how to make metallic text is Adobe Illustrator CS3. This video shows you how to do it step by step. You only need basic knowledge of Adobe Illustrator CS3 to do this.

This is my first contribution in an ongoing series on detailing the best free, open source hacking and penetration tools available. My goal is to show you some of the quality tools that IT security experts are using every day in their jobs as network security and pen-testing professionals. There are hundreds of tools out there, but I will focus and those that meet four key criteria:

There are a lot of things on your computer that can reveal information about you when you are surfing the Internet. If you are like me, then you will do anything to maintain your privacy and prevent those little leaks of information from happening. Here's a list of a few of the "threats" that can reveal information about you:

Update: this article is referring to the 1.9 pre-release beta version, which is now commonly referred to as 0.1.9, released in October of 2011.

mIQ? What is it exactly? It's a handy web service that helps you manage your mobile life, with free and easy online access to all of the content and information stored on your mobile device. How does it work? Best Buy has answers. The Best Buy Mobile team explains how simple it is to use mIQ to backup all the data on your cell phone, including messages, photos and contacts.

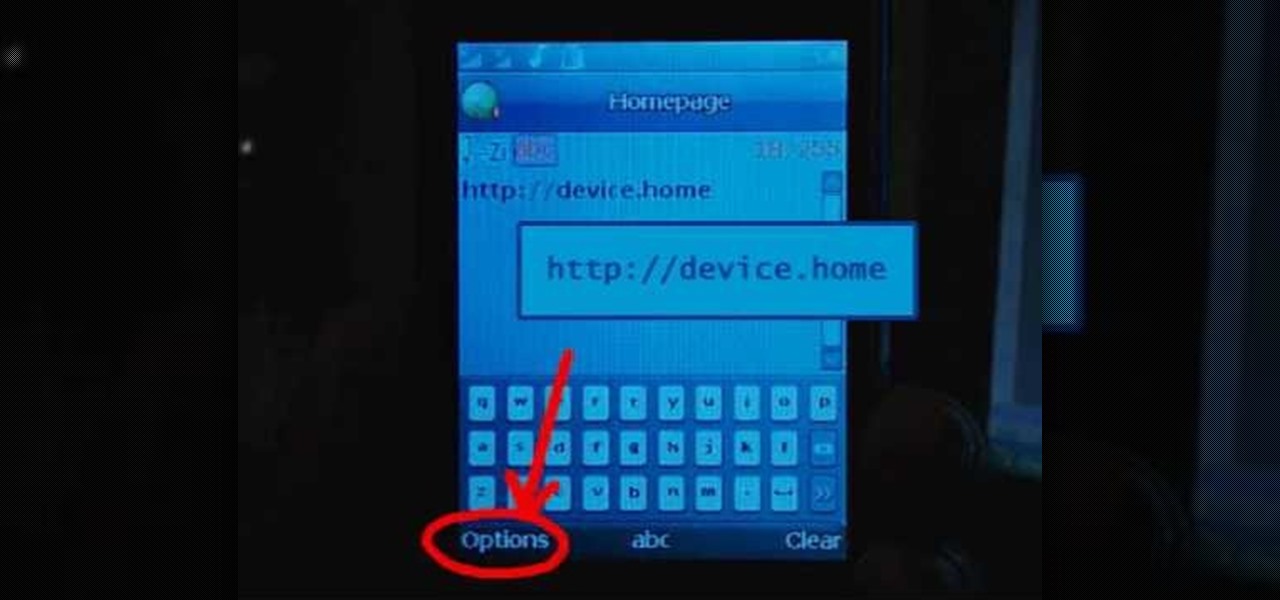
Learn how to set up Internet on iPhone clones with this video. *First thing you need to do is to make an AT&T GPRS data account.

Everybody has a blood type. There are four types of blood in the ABO system: A, B, AB, and O. In this medical how-to video, learn how easy and important it is to find out what your blood type is. The procedure is very watch and find out.