Welcome back, my budding hackers! When we are looking for ways to hack a system, we need a specific exploit to take advantage of a certain vulnerability in the operating system, service, or application. Although I have shown you multiple ways to exploit systems here in Null Byte, there are still many more exploits available that I have not yet shown you.
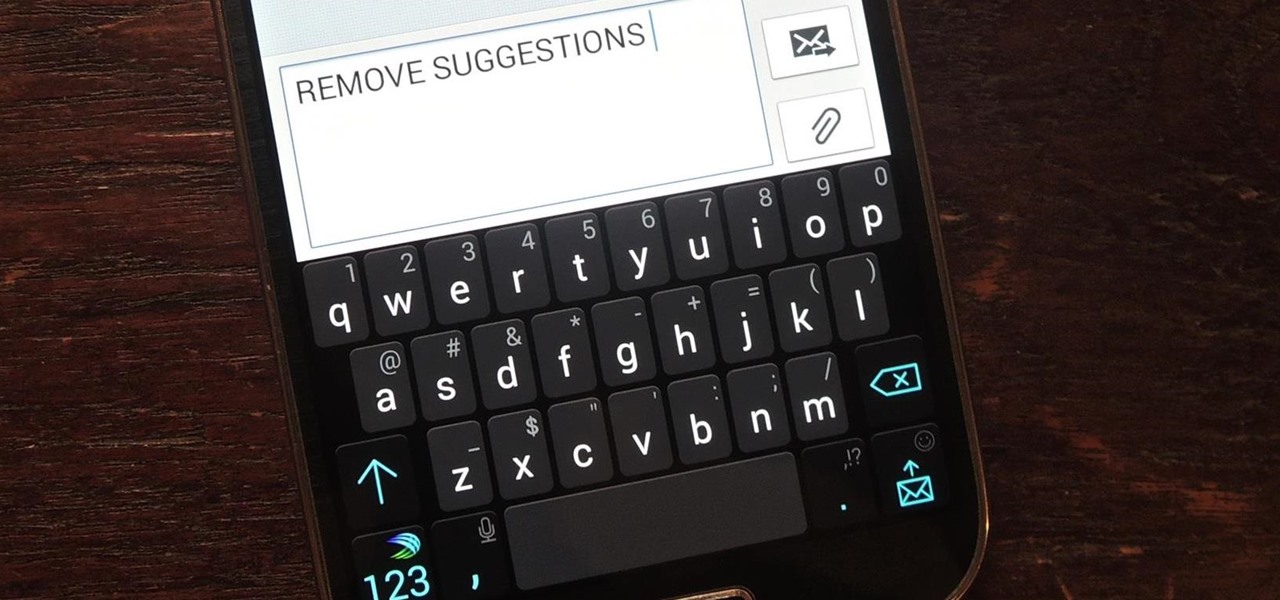
Auto-correction is a double-edged sword if I ever saw one. It's great because I'd have an abundance of typos without it, yet it's extremely frustrating (and embarrassing) when it doesn't actually work. Just take a look at the very recent example below from Breaking Bad star Aaron Paul. Funny for us, embarrassing for him. I have a particularly difficult time typing on small keyboards (i.e. fat-finger syndrome), so disabling auto-correction on my Samsung Galaxy S4 is a no-go. I'm willing to ris...
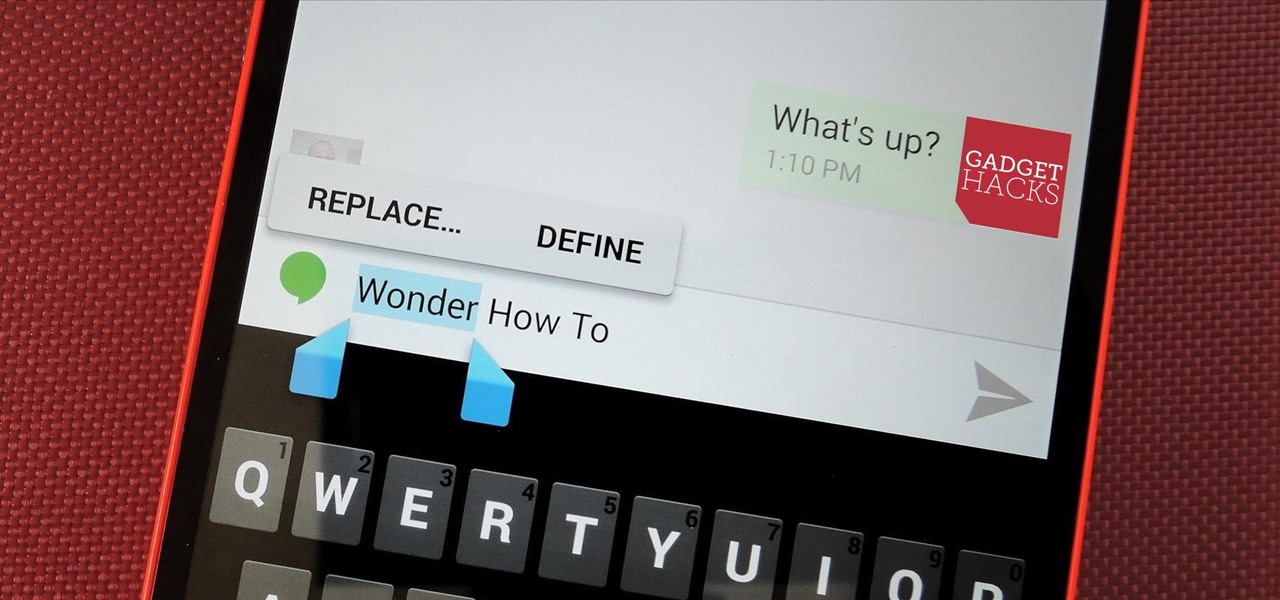
Even as a writer by trade, I'm not intimately familiar with every word in the English language. When you're typing something out on your Nexus, sometimes you think to yourself, "Is that right? Am I using the correct word here?" Then, you have no choice but to bring up Google Now and do a search for that word to make sure you're using it correctly.
Copy and paste keyboard shortcuts are beautiful gifts from the gods, and any website that blocks such an offering can burn in hell. But really, Cmd+C and Cmd+V (Ctrl+C and Ctrl+V for Windows folks) are second nature to most of us, so it's very frustrating when sites like PayPal don't let us use them.

Having an open-source platform like Android is great, allowing manufacturers and developers the ability to make their own skins and apps to truly customize the end-user experience. The only downside is that when an update comes to vanilla Android, many of us are left in the cold, unless you have a Google Play Edition HTC One.

HTC pulled out all the stops when designing the HTC One M8. From it's sleek body, to it's incredible sound quality, this thing just oozes sophistication. While all of these add-ons are great, they can be incredibly taxing on the CPU, in turn causing some serious lag.

Welcome back, my hacker apprentices! To enter the upper echelons of hackerdom, you MUST develop scripting skills. It's all great and well to use other hacker's tools, but to get and maintain the upper hand, you must develop your own unique tools, and you can only do that by developing your scripting skills.

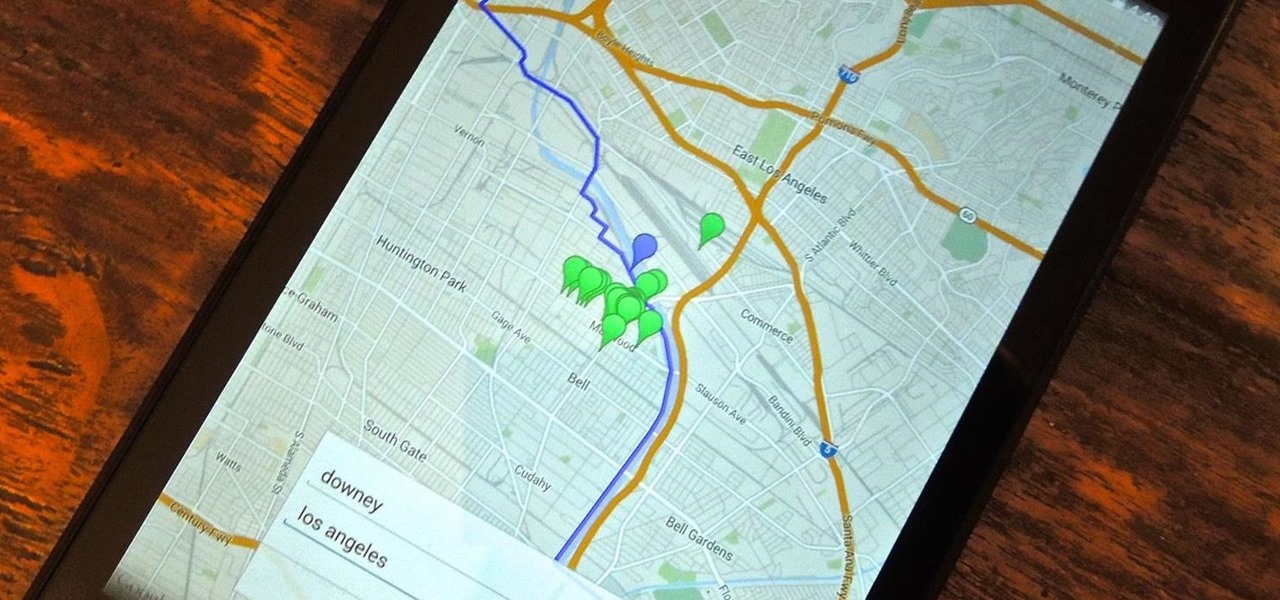
Back in college, there were many instances where I'd have to meet up with a partner that I was randomly paired with in order to work on a project or to study for an exam. Besides the awkward interactions, the most difficult part was always figuring out where we would meet off-campus. I live here and they live there, so what's reasonably halfway?

Welcome back, my hacker apprentices! Several of you have written asking me how you can check on whether your boyfriend, girlfriend, or spouse is cheating on you, so I dedicate this tutorial to all of you with doubts about the fidelity of your spouse, girlfriend, or boyfriend.
What is Programming? Why need to learn? How to get started? Which language to choose? While surfing web, you must be encountering various softwares, games, etc. and might be thinking to make one, but don't know where to start. Here, I am starting series in Programming.

We all have our favorite cooking oils, but not everyone knows that they're not all interchangeable. Each type of oil is best for certain jobs, and they all have different smoke points and flavor profiles, which are the two most important criteria in determining which one to use.

Welcome back, my hackers novitiates! As you read my various hacking tutorials, you're probably asking yourself, "What are the chances that this hack will be detected and that I'll land behind bars, disappointing my dear mother who already thinks I'm a loser?"

Texting something as simple as "What up, bruh?" can be transformed into something way more baller by adding emojis, emoticons, GIFs, and textspeak. Some people would even argue that texting is a form of art, similar to Shakespearean sonnets, but it still has a ways to go if you ask me.

Are you tired of your snoopy coworkers and friends lingering over your shoulder as you type in your security passcode? Unless you have the newer iPhone 5S with Touch ID that scans your fingerprint, you've only got a couple of security options—either a 4-digit numeric passcode or a cumbersome password.

In the midst of furious finger typing on a small non-tactile screen, you're sure to make mistakes—so the majority of keyboards have autocorrect. Generally it works pretty well and is a welcomed feature.

Like insurance, it's always better to have a computer mouse and not need it than to need it and not have it. Honestly, I don't want to carry around a clunky mouse with my laptop, so I don't. I do something else, something more convenient. I use my Nexus 7. If you want to give it a try, I'll show you how it's done right now. All you need to is a Wi-Fi network and a specific Android app to control your computer with your Android tablet.

Using fresh herbs can make a huge difference in almost any dish, but they're not always available everywhere. Depending on where you live, you can't always get them during the colder months. Personally, the problem I run into the most is not being able to use fresh herbs before they go bad.

A lot of people hate chopping onions, and understandably so. Their shape and layers make them difficult to handle if you don't have much practice, and even if you know exactly what you're doing, it's a task that usually ends in tears.

Welcome back, my fledgling hackers! One of the first issues any hacker has to address is reconnaissance. Before we even begin to hack, we need to know quite a bit about the target systems. We should know their IP address, what ports are open, what services are running, and what operating system the target is using. Only after gathering this information can we begin to plan our attack. Most hackers spend far more time doing reconnaissance than exploiting.

Welcome back, my hacker trainees! A number of you have written me regarding which operating system is best for hacking. I'll start by saying that nearly every professional and expert hacker uses Linux or Unix. Although some hacks can be done with Windows and Mac OS, nearly all of the hacking tools are developed specifically for Linux. There are some exceptions, though, including software like Cain and Abel, Havij, Zenmap, and Metasploit that are developed or ported for Windows.

Video: . How To Use a Tampon

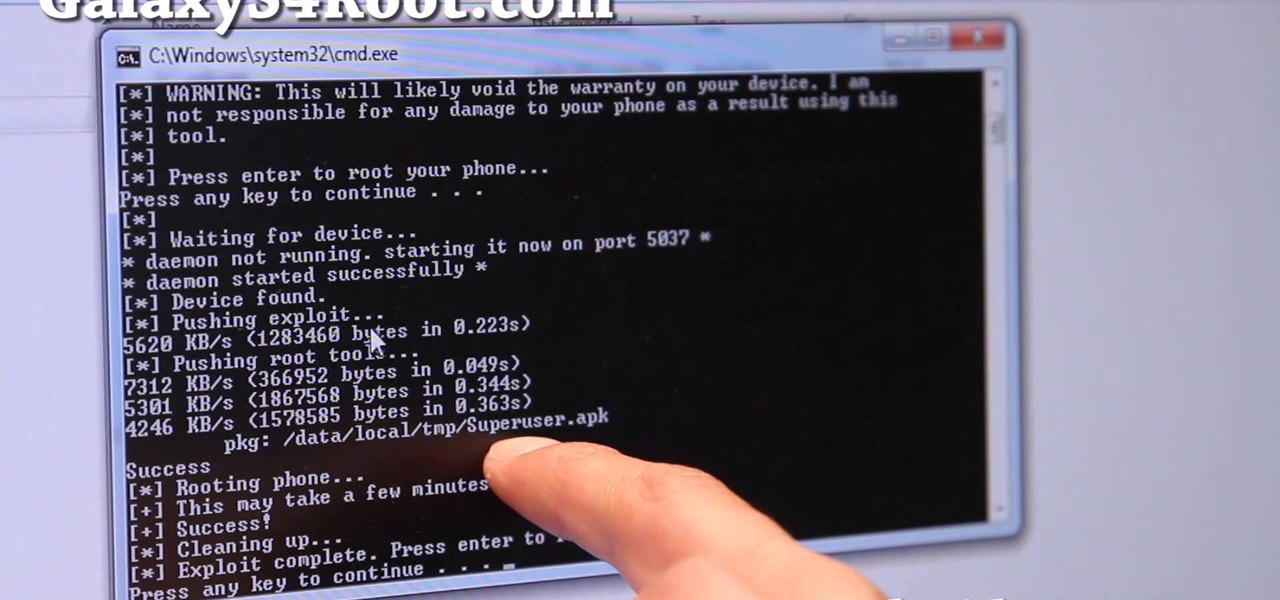
Here's a quick and easy video tutorial on how to root any Qualcomm-based U.S. or Canadian Galaxy S4 Android smartphone.

There are some really talented graffiti artists out there. Some of them are good enough that businesses hire them to paint advertisements, rather than hiring someone to scrub their work off the side of the building.

Love or hate 'em, you've got to admit that cupcakes really had their moment. They started rising in popularity back in 2003 with the opening of Crumbs Bake Shop in Manhattan, and quickly became one of the most annoyingly ubiquitous food trends to date. Seriously. Type "cupcake" into Google. While I wouldn't turn it down if you put one in front of me (red velvet, please), I can't say that I was particularly disappointed to hear that the cupcake trend is coming to an end. I'm more of a cheeseca...

Plastic red cups are synonymous with college parties, beer pong, and generally a good time. The reason these cups are so rampant in the party scene is because they're cheap, easily disposable, and, well... who wants to drink out of a blue cup?!? Oh, to be young and in debt.

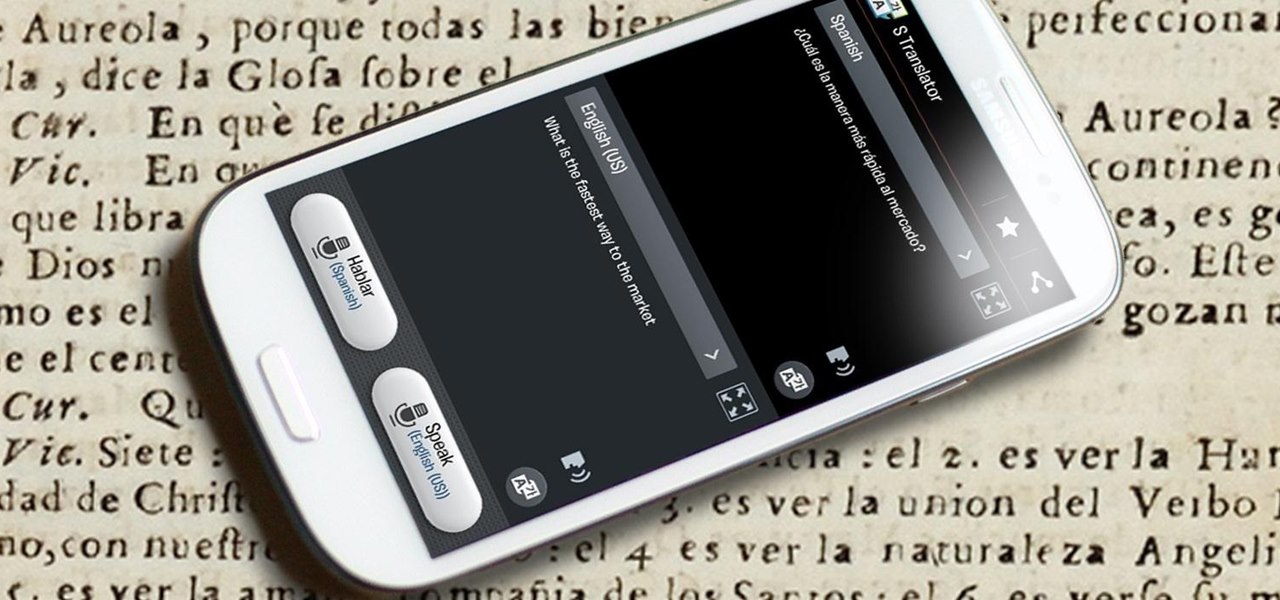
If you watched Samsung's Unpacked 2013 live last month, where they announced the new Galaxy S4, you probably sat through this awkward skit: This was Samsung's way of introducing their new translation software, dubbed S Translator. In the skit, the backbacking American traveler in Shanghai typed his question in English, and the phone spoke it aloud in Chinese. The other man replied in Chinese, and the app translated the message back into English. Live conversation translation aside, the app ca...

PRL, or Preferred Roaming List, basically tells your phone which towers to connect to first. Changing PRLs can improve reception and data speeds, and in some cases even give you access to corporate/test towers.

At a time when virtually everyone has a cell phone, it's almost inconceivable to think of a time when we're without them. At work, in bed, and even in the bathroom; we're always with our smartphones. I mean, hell, someone even designed a way to bring your smartphone into the freaking shower. It's not THAT serious.

Welcome back , my fledgling hackers! Lately, I've been focusing more on client-side hacks. While web servers, database servers, and file servers have garnered increased protection, the client-side remains extremely vulnerable, and there is much to teach. This time, we'll look at inserting a listener (rootkit) inside a PDF file, exploiting a vulnerability in Adobe's Reader.

For the most part, keyboard shortcuts are great. They save you some time and make it easier to do everything right from the push of a button. But like most things in life, there is always a caveat, and in this case, for me—it's a huge one.

Remember the 1960's American television series Batman, with Adam West as Bruce Wayne? It was waaaaay before my time. The caped crusader that I'm more familiar with is actually this one... When I first heard of Adam West, it was him doing the Batusi on The Simpsons. I had no idea what was going on, so I looked up Adam West and his sensual dance and found myself face to face with the 1960's Batman.

What time is it? It's a question that you'll find yourself asking a million more times throughout your life, but one that hardly goes unanswered. When you're on your phone or at your desktop, there is almost always some type of clock available to immediately give you the time.

Keeping your operating system up to date is essential to keeping it bug-free and running properly. Windows regularly pushes out patches and security fixes through Windows Update, so making sure to turn on Automatic Updates or checking at least once a week is strongly advised.

Archive files are great for portability and saving space, but a lot of people don't know they can also be encrypted. There are a lot of archiver programs out there, but most of them can open a file that's been encrypted using other software, as long as you're using a recent version.

So a little while ago we covered BUD switches, but there's only so much you can show in one tutorial.

If you use Ubisoft's uPlay browser extension, you should probably get rid of it right now. An Information Security Engineer at Google discovered that the plugin has a hole in it that allows programs to be installed through uPlay, essentially letting anyone who feels so inclined to take over your computer. How the Exploit Works

Wish your home wireless network was faster? You can always buy a signal booster, but if you'd rather not spend the money, here are a few tips and tricks to speed up your wireless connection, including how to make a homemade signal booster with things you probably already have lying around.

In this software video tutorial you will learn how to create a column line graph in Microsoft Excel 2007. First you type in the data in to the work sheet. Then highlight the data and click 'insert' on the menu bar. Here you select the 'column' option and go down and click on the type of column that you want. And the graph is automatically presented. Now click on 'move chart' and select a sheet where you want the graph to be moved to and click OK. To change any field in the chart in to a line ...

Check out this video iPhone tutorial and learn how to enable MMS pciture messaging on your 3G/GS. Windows XP/Vista 32 Bit Tutorial