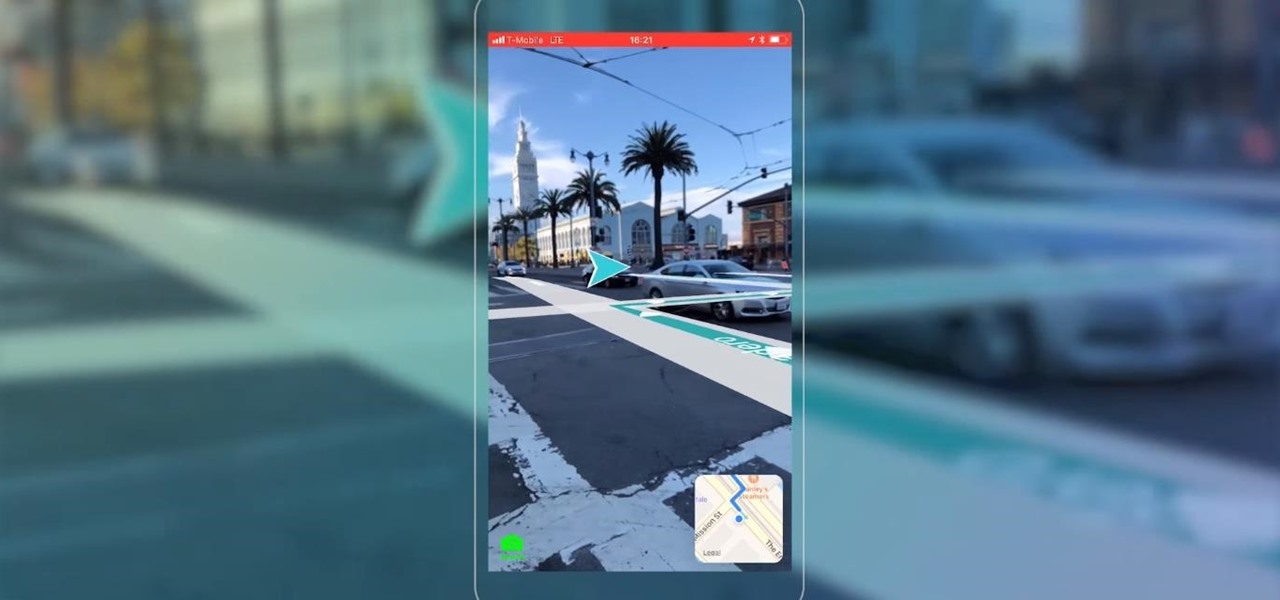
Apple AR: Blippar Charts New Territory with Launch of First AR Navigation App for iPhones & iPads
Mobile AR developer Blippar has achieved a breakthrough by releasing what appears to be the first commercially-available AR navigation app.

Mobile AR developer Blippar has achieved a breakthrough by releasing what appears to be the first commercially-available AR navigation app.
To revise a line from the Blues Brothers, when it comes to ARKit apps, we've got both kinds — home utilities and games. As such, two more candidates for each category have made their way to the app store.
A survey by ABI Research revealed that only 25 percent of businesses have implemented augmented reality technology in some form or fashion.

There's never an Apple announcement without some good ol' anger and backlash. To be fair, Apple received some really positive feedback from parts of the iOS 11 presentation at WWDC back in June. Fans had been waiting for years to customize the Control Center, as well as for native screen recording. But if there was one thing that got fanboys and Apple haters raging about in unison, it's that weird, incomprehensible notification system.
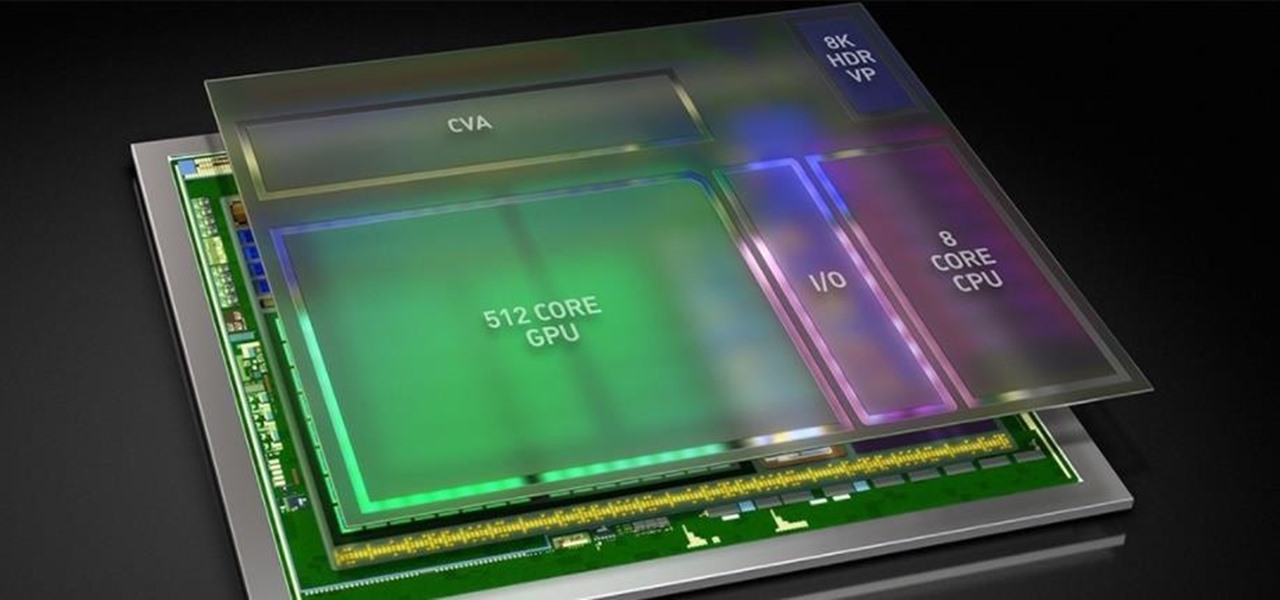
As Intel steps up their investment in driverless technology with a $15 billion acquisition of Mobileye, so have automotive supplier Bosch and NVIDIA teamed up to manufacturer driverless car systems with the much-awaited Xavier chip.

Cinemagraphs are basically artistic photos that have been turned into a GIF to showcase a bit of subtle motion and give them life. Unlike regular GIFs, which can sometimes loop with a jarring cut at the end, cinemagraphs give the illusion of perpetual motion, like water drops off a flower's petal or clouds moving over a scenic sky.

Metasploit is an extremely popular pentesting tool capable of enumeration, exploitation, and injecting shell code, and is a part of almost every hacking toolkit. So there's no way I could leave this out of our series on getting your Mac set up for hacking.

Google's new cross-platform video chat app, Duo, is finally making its debut today, following a long waiting period that began in late May. The app was heavily teased during the keynote speech at Google I/O, but was not made available for download until now, so any early hype Google managed to whip up has died down quite a bit.

First of all, Merry Christmas and Happy New Year to all Null-Byters that learn and teach in this wonderful site. In this article we will explore the basics of the meterpreter's IRB (Interactive Ruby Shell).

In this article, we will explore the basics of radare2, a powerful package that comes with Kali. We are going to write a simple program, and then disassemble it, to see what is really doing in the processor.

Let's say that we want to see what someone is doing on their computer? In this tutorial, we'll be hijacking cookie sessions to do just that!

It's already that time of year again—LG has unveiled its latest high-end smartphone, dubbed the G4. In past iterations, LG released its flagship devices in the fall. But slowly over the course of the past 2 years, the release schedule has been bumped up to be more in line with HTC and Samsung's springtime releases, and further away from the sales-sucking iPhone event each fall.

Hello my fellow hackers, Welcome to my republished revision of the ruby programming language, Part 1.

In last Saturday's workshop, the tutorial was on the ABBA switch, so named because it fires redstone pulses in A-B-B-A order. While the turnout was low, it was a really productive workshop! We experimented with a lot of things and had a great time. Hopefully you'll consider joining us next time!
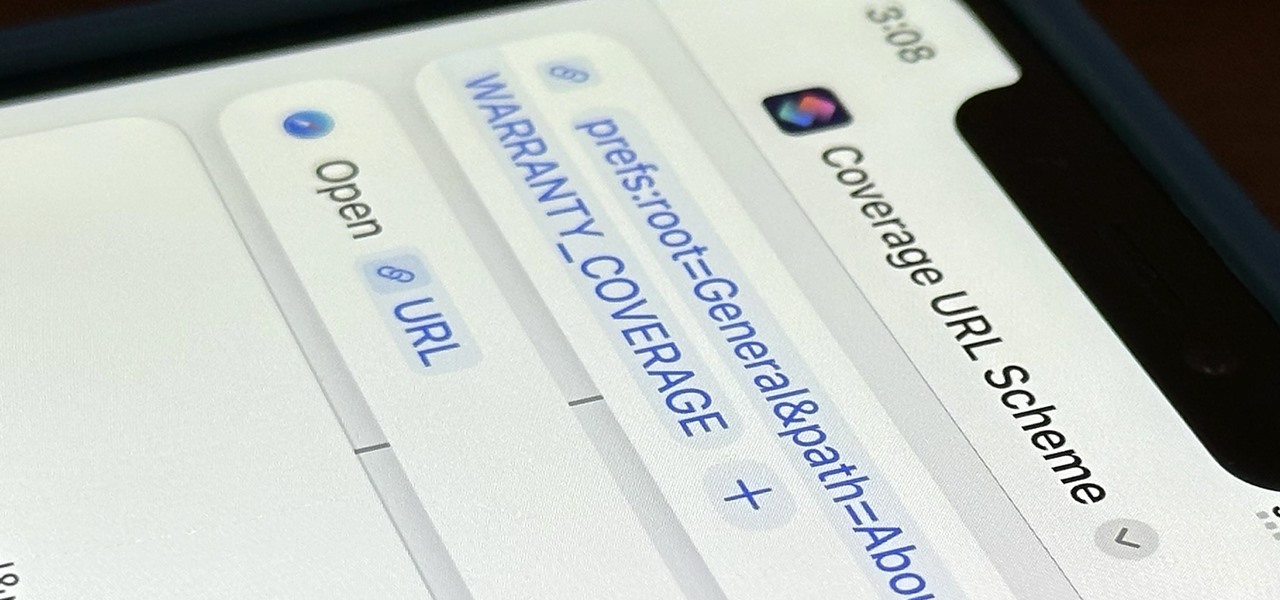
Apple just released its iOS 16.6 update for iPhone on July 24. When you install the new software, it may look like there's not much to it since Apple doesn't include any features in the release notes beyond "important bug fixes and security updates," but a few new features are hiding within.
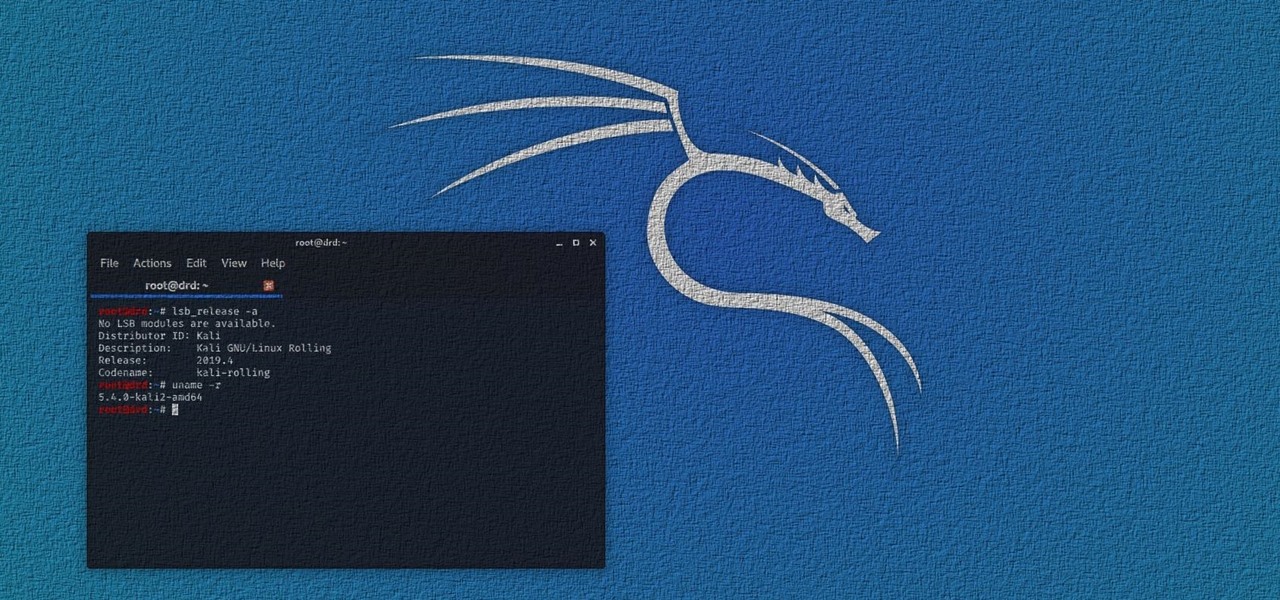
Kali Linux has come a long way since its BackTrack days, and it's still widely considered the ultimate Linux distribution for penetration testing. The system has undergone quite the transformation since its old days and includes an updated look, improved performance, and some significant changes to how it's used.

Do you want to know some quick tricks for improving tech processes at your company? How about equipping yourself with skills that will land you a new job or promotion this year? Becoming a cloud computing expert will make it happen, and right now, The 2021 Cloud Computing Architect Certification Bundle is on sale for just $29.99. That's an amazing 98% off the regular price of $1,800.

Microsoft has plenty of products that you're likely familiar with, especially if you work or dream of working in IT. One of the most important now and in the future will be Azure, the company's cloud computing service. You might not know it, but a significant portion of the internet runs on Azure, and that share of the web is projected to keep growing in the coming years.

Netflix has offered its beta program officially through the Play Store for some time now. Still, the issue most of us face — the beta availability is always scarce. Without getting lucky and landing a beta spot early on when the gates were open, there wasn't much you could do about it. However, there's now a brand new method you can use to sideload the Netflix beta app and join in on the fun.

Determining the antivirus and firewall software installed on a Windows computer is crucial to an attacker preparing to create a targeted stager or payload. With covert deep packet inspection, that information is easily identified.
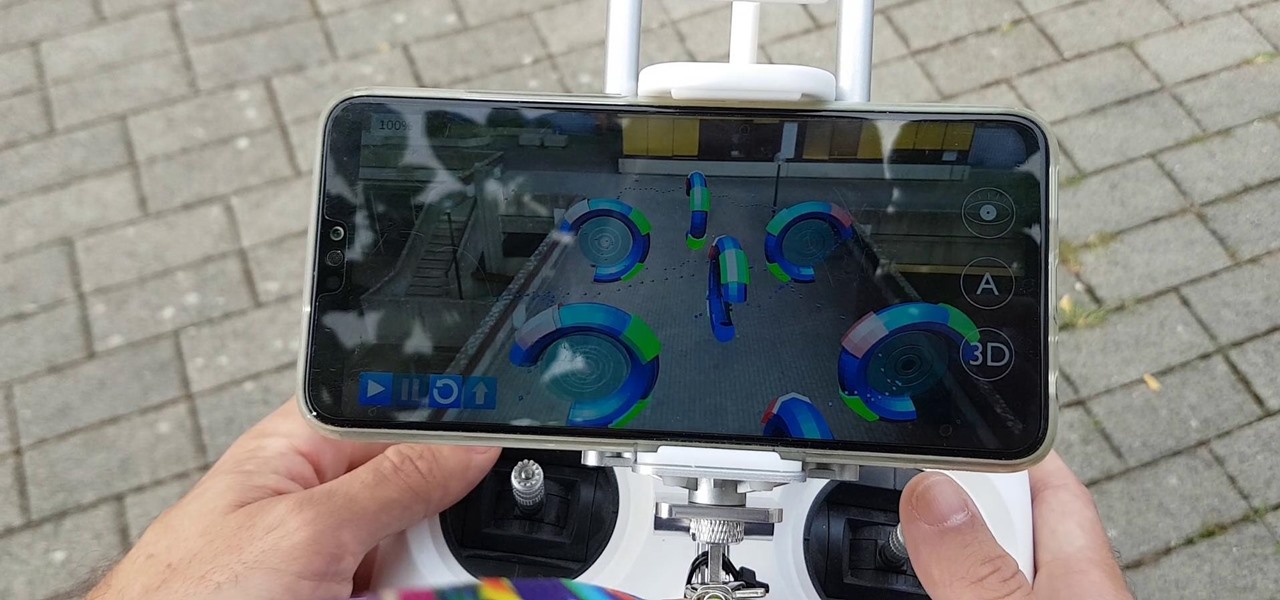
Drone mishaps, such as the collision that scratched a military helicopter in New York, are becoming something of an everyday hazard.

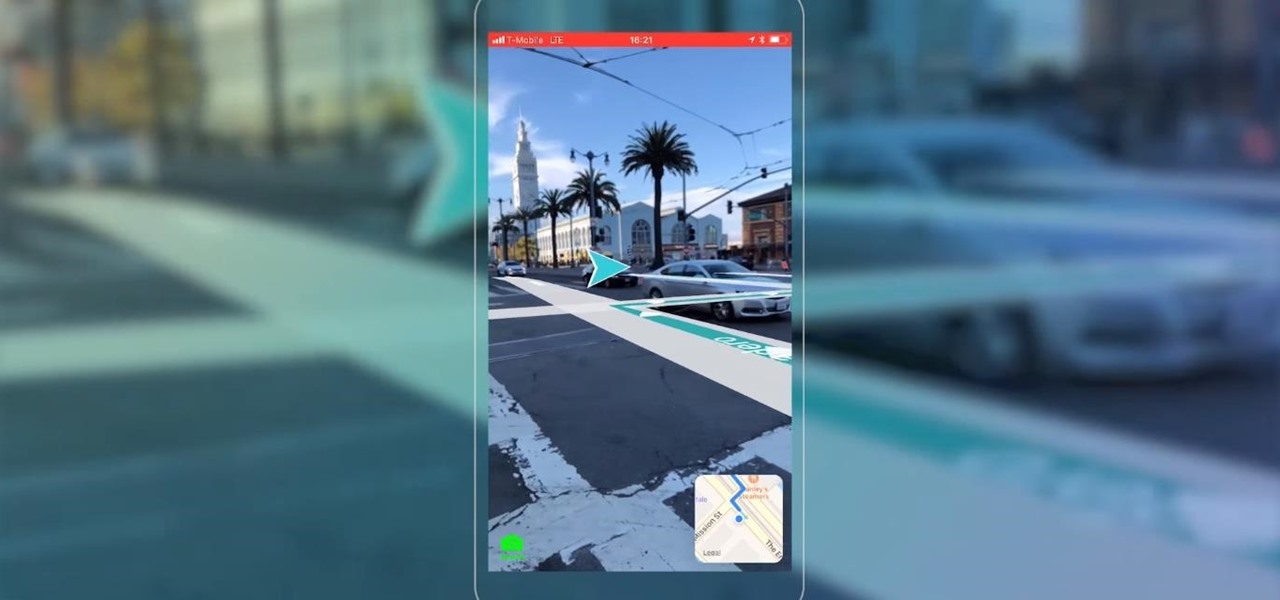
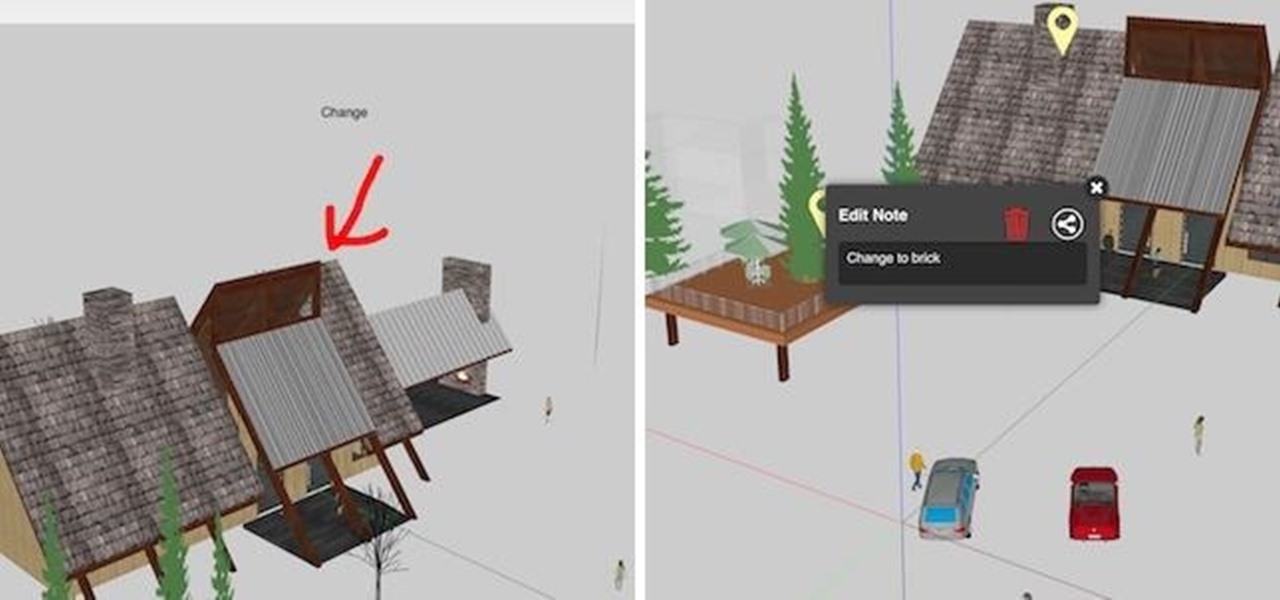
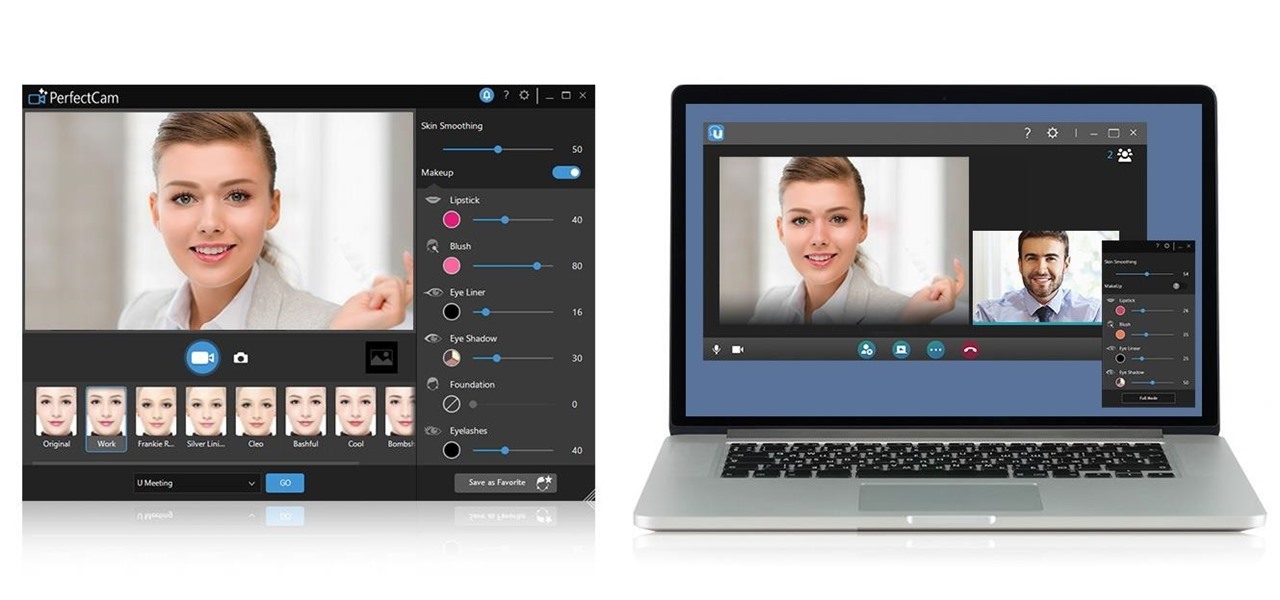
Developers in the augmented reality industry got a lot of love this week.

Just when we thought the AT&T partnership with Magic Leap wouldn't really take off until the latter launched a true consumer edition of the Magic Leap One, the dynamic duo jumped into action this week to offer the current generation headset to customers.

Augmented reality startup Nreal was a hit at this month's CES event, with some even calling the device a worthy challenger to the Magic Leap One.

In the world of technology, there's often a trade-off between convenience and security. The Java Remote Method Invocation is a system where that trade-off is all too real. The ability for a program written in Java to communicate with another program remotely can greatly extend the usability of an app, but it can also open up critical vulnerabilities that allow it to be compromised by an attacker.

Despite the launch of ARKit a year ago, and ARCore this year, a true killer app has not arrived for either platform, that's according to the head honcho for one of the leading development environments for 3D applications.

In its latest feature with an assist from augmented reality in storytelling, the New York Times shows readers the virtual crime scene it constructed to prove that the Syrian military conducted chemical warfare against its citizens.
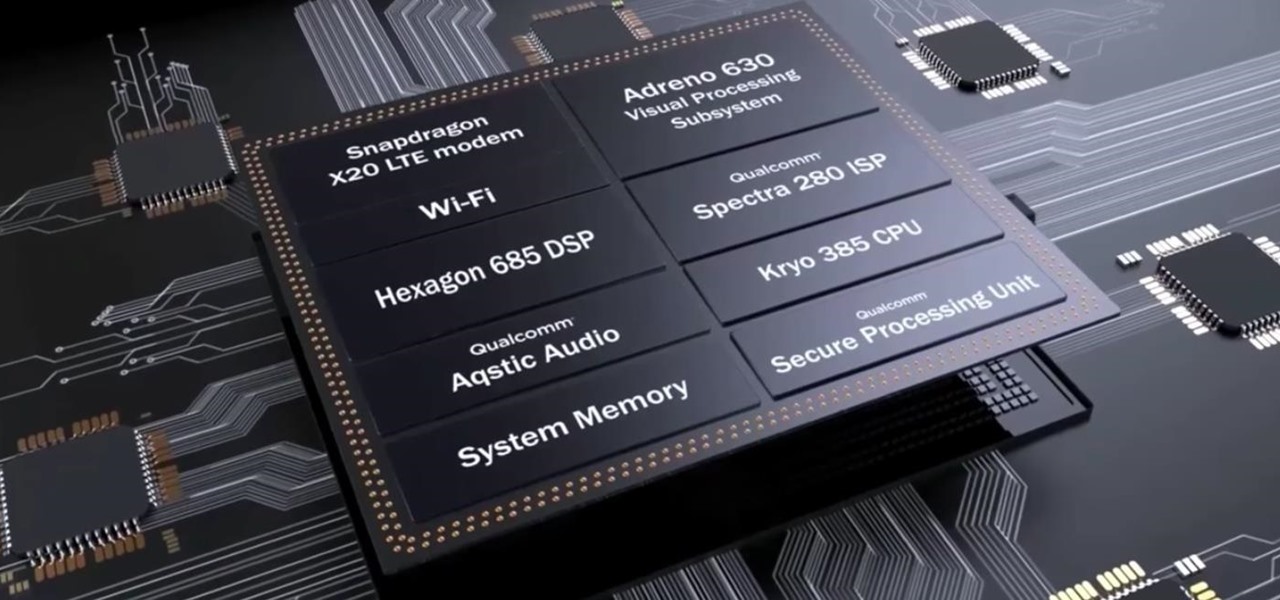
After the success of the Snapdragon 835, Qualcomm now has its eyes set towards the future with the arrival of its next-generation SoC, the Snapdragon 845. Debuting alongside the Samsung Galaxy S9, the 845 is now set to take over the market for flagship Android phones in 2018.

While ARKit and ARCore are poised to bring AR experiences to millions of mobile devices, one company is poised to anchor those experiences anywhere in the world with just a set of geographic coordinates.

The next-generation Audi A8 to launch in July is expected to be the world's first Level 3-capable production car to go on sale in retail channels.

In the ongoing search to find better ways to use antibiotics, an extract made from maple syrup has some surprisingly important medical benefits.

A group of researchers from Stanford University and Princeton University has put together the largest RGB-D video dataset to date with over 1,500 scans of over 700 different locations across the world, for a total of 2.5 million views.

As drug-resistant bacteria become more commonplace, researchers are looking for new antibacterial strategies to disrupt disease-causing microbes. Some scientists are working to create new drugs, while others are trying out drug combinations. Another group, however, are ditching pharmaceuticals altogether and experimenting with non-drug alternatives.

The iconic, lovable gummy bear originated in Germany, where it goes by the name Gummibär— but that's not what makes it so much fun. The base of gummy bears is made up of gelatin, which gives them the signature elasticity that makes you feel like a kid again. But the fun doesn't have to stop there.

Welcome back, my budding hackers! Digital forensics is one of IT's most rapid-growing disciplines. All hackers should be familiar with digital forensics if for no other reason than to protect themselves. More than one hacker has been apprehended because they were unaware of the evidence trail they left behind.
If your company has already released some popular and addictive game and you're thinking about creation a sequel, this article is just what you need. We gathered the main tips and advices that will be useful for the building a strategy and a sequel itself. Check out the following instructions and recommendations that can lend you a hand in making a sequel for your game.

In this article, we will build a parallel password cracker using the techniques explained in the previous part. As SHA-512 is the digest function that Kali (and most modern Linux distributions) use to store our passwords, we will make a SHA-512 password cracker.

As many of you know, processor's clock frequency improvement got stuck in about 2003, causing the origin of multicore CPU (and other technologies). In this article I'll introduce you on how to run code simultaneously in various processors (I suppose that all of you have a multicore CPU). When you write code without any parallel directive, it only executes in one CPU at the same time (see it below). OpenMP make simple to work with various cores (if not with all of them) , without so much heada...

In response to the success of Apple Pay and an attempt to stave off the appealing Samsung Pay service, Google is completely revamping Android's mobile payments system. Instead of just using Google Wallet as an app to make payments with your phone, a new service called Android Pay, with an extensive underlying framework and API, will soon make its debut—and maybe even sooner than you'd think.

Welcome back, my hacker novitiates! Eluding and evading antivirus software and intrusion detection systems is one of the most critical tasks of the hacker. As soon as a new exploit is developed and discovered, the AV and IDS developers build a signature for the attack, which is then likely to be detected and prevented.