How far can young people go in petting and still stay within the bounds of personal standards and social mores? Watch this how to video to find out. Show your date an appropriate amount of affection.

This nifty tutorial will tell you how to create a buffet supper, a classic American tradition. This video will teach you what foods to offer, how to arrange them, and more. Arrange a buffet supper.

This tutorial is for new Blender 3D users. All you need to do is have the software installed and this video will get you started. Start using Blender.
According to Amazon.com, Kindle was their best-selling item this year, which means many, if not all of you are playing with a brand new Kindle on Christmas Day. Of all of Amazon's Kindle models, the Kindle 3 (6") will be the most common eReader in everyone's hands, either the Wi-Fi version or the 3G model.

You can take a bajillion photos on your smartphone or digital camera, but they'll eventually end up lost on your computer hiding within folders within folders within folders... you get the picture. To bring them to the physical world, you've got to print them, but you don't have to settle on a boring ol' picture frame.
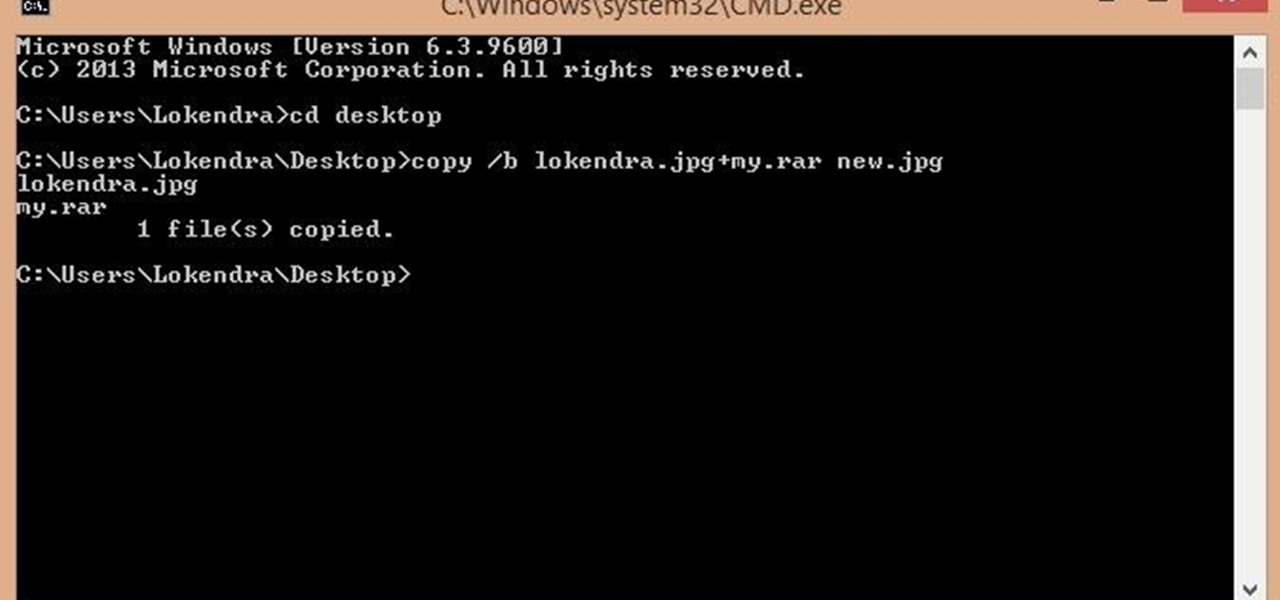
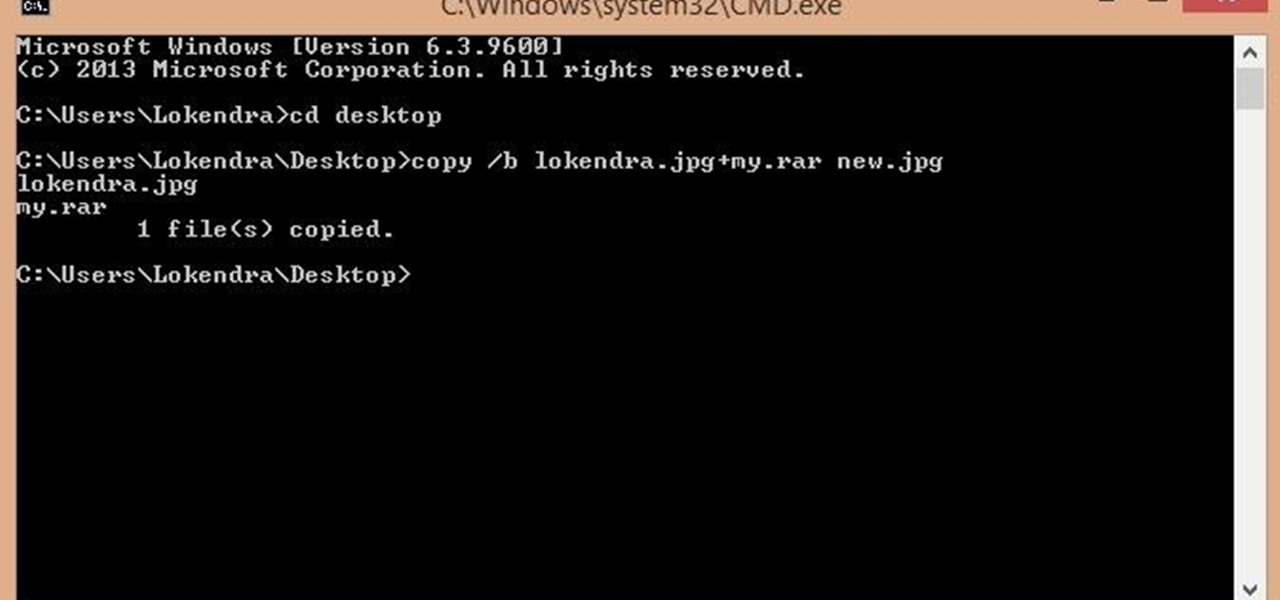
First of all you should make a folder and rename it as 'my'. Move all your files on that folder and place it on desktop.

Dan Osman was a real life Spiderman. This wild man did not die recklessly, but due to unfortunate equipment failure in Yosemite in 1998. This week is the tenth anniversary of his death.

On sports teams, especially youth sports teams, the players are never one and the same. Young athletes are all different, which means they all have different skills and abilities out on the field or in the arena. As a coach, you can't treat them as a whole, but you need to treat these young players as individuals of a whole. This video covers some practices and techniques, as well as gives advice for better coaching skills for teaching a "team". This is coach psychology.

I've been watching my Bocas del Toro, Panama weather for the last several months and the reports are correct. It rains a lot!

Look left. Can your garbage take photos like that? With a few tweaks it will! The pinhole camera is photography in its most basic form. Using a light-proof container, the 35mm will capture the image when the pinhole is opened. The resulting photographs have a distinctly démodé look, like this shot from Kodak's archive.

File recovery on Linux is a bit different than Windows. It requires different software than the Windows counterparts because every OS has their own file system. Windows uses NTFS, or FAT file systems, while on the other hand, Linux uses ext-based file systems. I personally use ext4 file system because it's the latest and greatest ext-journaling system and supports a large level of directory recursion and file sizes, but most installations still use ext2 or ext3. When files are deleted from a ...

Yale University has opened up its museum archives to the public in digital form, providing free online access to high-resolution images from its cultural collections, making it the first Ivy League school to do so in this fashion. Currently, there's over 250,000 "open access" images available from their new online collective catalog, with the goal of providing scholars, artists, students and all other worldly citizens royalty-free, no-license access to images of public domain collections with...

The Ubuntu experience has improved greatly with version 10.04, providing an easy-to-use interface. Especially when it comes to installing programs. However, it still relies on an online internet connection for installing additional software.

At some point, we all go from organized to disorganized. Let's assume you are a business executive working in a busy corporate building. Chances are you are going to get a heavy workload and it will impact how clean your workspace is. However, this article is about keeping your desktop clean and clutter free, along with the use of software to find documents you have misplaced.

Welcome to Part 3 in my series on protecting your computer from prying eyes (Part 1, Part 2). In today's segment, we will be going over drive encryption using the TrueCrypt program on Windows OS. Drive encryption is a technique that masks your data with a cryptographic function. The encryption header stores the password that you have entered for the archive, which allows the data to be reversed and read from. Encrypted data is safe from anyone who wants to read it, other than people with the ...

Encryped traffic and tunneling is a must when away from home to keep you and your information safe. SSH tunnels can be slow, and are heavily encrypted. VPNs are an all port solution, and proxies are just not what we need in most cases. Then, there is Tor.

While we're waiting for Google to sort out the mess over suspended Google+ accounts, it's a good reminder that you have the option to download much of your Google+ data with Google Takeout. Google Takeout, created by an internal Google engineering team marketed as the Data Liberation Front, is a free service that provides a handy and easy way to download data from your Google+ stream, your contacts and circles, and other information in a zip file.

On the same day that Google launched their new social network, Google +, a team of Google engineers calling themselves the Data Liberation Front announced their first service on Tuesday—Google Takeout, a product that allows users to easily move their data in and out of Google products, including Buzz, Contacts and Circles, Picasa Web Albums, Profile and Stream (the equivalent of Facebook’s newsfeed).

Human anatomy is something every physician must undergo as a medical student. Some move on to become great doctors, some move on to become great artists, helping to better educate students and improve upon many illustrated representations of the human body since the days of medieval medicine. But thankfully, you don't have to be in the medical profession to enjoy the beautiful art of the human body created for teaching purposes.

First, I have to apologize—this is really old news. But when it comes to Nele Azevedo's Minimum Monument project, it's well worth digging into the archives. It's one of the most amazing street art installations I've ever seen.

A Parisian street artist anonymously known as JR—his pervasive works feature massive photographs of poor urban residents plastered across the cityscape—was awarded the 2011 TED prize some months ago.

P.S.- I Made This offers resourceful, crafty tutorials that stretch the imagination. With projects ranging from jewelry to accessories to clothing, founder and creator, Erica Domesek has been featured in Teen Vogue, Glamour, Vogue Nippon, Domino, GQ, InStyle, and Marie Claire. Her brief tutorials also include collaborations with both Helmut Lang and Who What Wear.

Android 6.0 Marshmallow is due out later this fall, but Google has already released three preview builds of the upcoming version. So if you really wanted to give Marshmallow a try, you could install the preview on your Nexus device right now. But if you just wanted to get a little taste of what's to come, we went ahead and pulled all of the brand new wallpapers out of the latest release.

If you're looking to spruce up your iPhone's home screen, look no further than Aerial Wallpapers, a Tumblr blog that specializes in bringing you the most unique and breathtaking aerial photographs from across our planet, filled with both natural and artificial scenery.

Do you want to know what's better than a bouquet of a dozen red roses? How about a bouquet of bacon roses? Or, if you aren't a meat-eater, a bouquet of hand-crafted origami roses or ones made of duct tape that won't wither away within a couple of days?

One of the most annoying things about the PlayStation 3 is its lack of backward compatibility on some models. There are several hacks out there to do this, but most of them involve extra hardware, like the Cobra-USB Dongle, or downgrading, which can cause all sorts of problems. Photo by borisvolodnikov

Stuck behind bars? Held hostage by a guy with a flamethrower? Thanks to the wise and resourceful 80s secret agent MacGyver, these problems can be resolved by a car battery, two coins and some jumper cable.

How to transfer iTunes from PC to Mac You want to switch from PC to Mac and you want to take your iTunes library with you? There are several ways to move iTunes from your Windows PC to your new Mac. You can manually move all your iTunes contents to an external hard drive and from it to your Mac, or you can use a software like CopyTrans TuneSwift that does the job for you. Let's start with the easier way!

Do you have an old-timey typewriter sitting at home? This video will show you the history of it, as well as teach you how to type with it. Type with an old fashioned typewriter - Part 1 of 2.

The last few months of WikiLeaks controversy has surely peaked your interest, but when viewing the WikiLeaks site, finding what you want is quite a hard task.

You're probably already impressed at some of the photos amateur astrophotographers can capture with their 16-megapixel digital cameras. I know I am. That's why I'm beefing up my camera skills, so I can also take some amazing pictures of our skies above. But if you can take photos this good with a 16-megapixel camera, imagine what you could do with something a little bigger, say, 3.2 billion pixels! That's a whopping 200 times more pixels!

The already robust and ingenious Nmap tool has received a whole slew of new scanning scripts that can be used to do all sorts of naughty endeavors. Notably, the SQLi module, since it is a necessary evil that we must cover here at Null Byte. This major update is going to fuel today's lesson.

Your BIOS, or Basic Input Output System, is the firmware on your motherboard responsible for initializing your computer's hardware when it is first powered on. It probes for video adapters, RAM, the whole works. The BIOS provides a small library of basic input/output functions used to operate and control the peripherals such as the keyboard, text display functions and so forth, and these software library functions are callable by external software such as the OS and system software within sai...

Here at Null Byte, we've spoken a lot about securing and anonymizing traffic. This is a big deal. With all of today's business taking place electronically via computers, we need to be secure when on-the-go. A lot of businesses don't even train their employees to secure their computers to protect from various threats. Here are a few things that should always happen when doing business on computers:

This is the first of a multi-part series on steganography techniques. Steganography, the art of hiding things in plain sight, has existed for a long time, and in many forms. When you manipulate the alphabet to have your own cipher and decipher, this is considered steganography.

Often times when staying at a hotel or anywhere for that matter, you'll whip out your laptop and check the local area for Wi-Fi. I know you've all been in my shoes when you find an unsecured network that appears to be public Wi-Fi belonging to the hotel or airport, and you connect to it. You connect fast and perfectly, only to find that when you open your browser, it says you don't have an account, and are filtered from accessing the web. This is because the owners of the network want to keep...

National Geographic recently published a retrospective of the lovely Jane Goodall, one of the world's most accomplished conservationists. The feature includes every image of Goodall to ever appear in the magazine for the past fifty years.

If you have a group of large files that need to be sent to a client, you might want to compress it into one single file for easy access or even protect its content from outsiders with a password. This video will teach you how to create password-protected zip files with WinRAR. WinRAR provides full RAR and ZIP file support, and can decompress CAB, GZIP, ACE and other archive formats. Make sure to hit "play tutorial" in the top left corner of the video to start the video. There is no sound, so ...

Note: The article assumes that the reader has a fundamental understanding of at least one other programming language and Perl. This is intended serve as a quick reference for Perl's input/output of data to databases.

Some people are what is labeled a power user. I am one of these people. No matter how fast I get my system, or how quick of programs I have, it is never good enough. There is always at least one program that I could swap out for a more advanced, text-based counterpart that increases performance just a bit. Luckily, you don't have to use text-based programs without graphical user interfaces to get blazing fast speeds on Linux. There are tons of open source alternatives to the mainstream progra...