Solar panels are an amazing invention. Catching energy from the Sun before it even enters Earth's food chain, photovoltaics are like an all-natural nuclear power plant. Unfortunately, the constituted parts of a solar panel are rare, valuable, and subject to the coercive forces of market competition.

Did you know there is hidden data in your digital pictures? Well, there is, and that data might be a security risk to you. Think back at all of those pictures you're in and are connected with. I'm sure some of those you'd like to distance yourself from. And surely you wouldn't mind checking out the metadata in a few of those images. In this article, we'll be going over how to do just that.

Today's guide is on creating a password protected folder on Windows 7 without any additional software. Yes, you heard that right. No extra software at all! This guide is intended for beginners. But please note, this method should not be used to store financial or otherwise highly confidential material. It might be a good place to hide a planning document for a family member's birthday party or similar occasion where you need to keep something secret temporarily.

Grab your thinking caps and get your hack on. Null Byte is officially seeking contributors on a weekly basis who are willing to take the time to educate the Null Byte community on anything, from hardware hacks to life hacks. Contributors that write tutorials will be featured on the Null Byte blog, as well as the front page of WonderHowTo (providing it's up to par, of course).

We had a blast during last week's social engineering calls. One of our attending social engineers was so clever that she convinced several people on Craigslist that lost items were hers, even if it seemed she couldn't be trusted. But females are better social engineers, naturally. Some say that females have a special knack for manipulating men, but I think that's preposterous. I can't see why that would be true in a million years (note my sarcasm).

Eventually, we plan on doing some root the box competitions here at Null Byte, but we're still looking for a server to play on. Anyone want to donate one? You won't regret it. Root the box is like 'king of the hill', except you have to hack a server and maintain access. Each server will have numerous known security holes, but until then, let's get back to the regular weekly coding sessions and realistic hacking missions on HackThisSite.

We're officially seeking Null Byters on a weekly basis who are willing to take the time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (IF up to par, of course). There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials on any skill level, and about anything you feel like sharing that...

We'd like this to be one of the last HTS mission announcements, at least for now. As soon as Null Byte finds a server to play with (anyone want to donate one?), we are going to start doing root the box competitions, which is like king of the hill, except you have to hack a server and maintain access. Each server will have numerous known security holes. But for now, back to the normal flow of things...

We're officially seeking Null Byters on a weekly basis who are willing to take the time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (IF up to par, of course). There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials on any skill level, and about anything you feel like sharing that...

Technology in computers these days are very favorable to the semi-knowledgeable hacker. We have TOR for anonymity online, we have SSDs to protect and securely delete our data—we can even boot an OS from a thumb drive or SD card. With a little tunneling and MAC spoofing, a decent hacker can easily go undetected and even make it look like someone else did the hack job.

We're aiming for this to be one of the last HTS mission announcements, at least for now. As soon as Null Byte finds a server to play with, we are going to start doing root the box competitions, which is like king of the hill, except you have to hack a server and maintain access. Each server will have numerous known security holes. But, for now, back to the normal flow of things...

The community tore up the first realistic mission last week. You've applied the techniques learned in the basic missions to a real scenario, so I'm pretty content. The realistic missions are where the learning gets intense and where we can apply real knowledge to extremely realistic situations. We will also be continuing the normal Python coding and hacking sessions. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, f...

Community byters, it's time to get serious. We are finally moving on to the realistic missions in HackThisSite. This is where the learning gets intense and where we can apply real knowledge to extremely realistic situations. We will also be continuing the normal Python coding and hacking sessions. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, from novice programmers to aspiring hackers.

We're officially seeking Null Byters on a weekly basis who would enjoy taking their time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (if up to par, of course). This is a job meant for anyone with the will to share knowledge. There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials...

What is Google Dorking? Well, simply put, "Google Dorking" is just an efficient way to utilise keywords in order to perform very specific searches on a given subject. In this case, one would look for websites/servers that are vulnerable to attacks or are configured improperly by using specific search criteria that should yeild results, should it find matches to known mistakes/errors in a website or webserver.

We're officially seeking Null Byters interested in teaching others! Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (if up to par, of course). This is a job meant for anyone with the will to share knowledge. There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials of any skill level, and anything you feel like...

When you buy computer parts, it can be a tough decision where you want to put all of your hard earned dollars into. Not only that, but when you buy a top of the line component, 3 months later (at most), your hardware will likely be outdated. This puts consumers like us in a bit of a pickle when it comes to purchasing, especially on a tight budget.

Having an SSH or Secure SHell to tunnel your traffic through is something we have talked about many times at Null Byte. As we know, it allows us to securely route and encrypt our traffic through a remote server, effectively anonymizing us and protecting our traffic from all forms of analysis—simultaneously. We have gone over how to make a home SSH tunnel. However, the question has come up, "How can I get an SSH tunnel to somewhere other than my computer?" This would be useful in a situation w...

There’s nothing like a great horror movie to really get the adrenaline pumping during the Halloween season. I don't know about you, but the sight of blood dripping into a pool of even more blood creeps me out, so you can imagine my reaction to harrowing creatures that go bump in the night and rip people's faces off. It's intense, but I love it.

COLOSSUS n pl. COLOSSUSES or COLOSSI a gigantic statue 60 points (10 points without the bingo)

JavaScript is one of the main programming languages that the Web is built on. It talks directly to your browser and exchanges information with it in ways that HTML simply cannot. With JavaScript, you are able to access browser cookies, website preferences, real-time actions, slideshows, popup dialogs and calculators, or you create entire web-based apps. The list goes on nearly forever.

PVC isn't something you want to send to the landfill. It's not going to do anything good for the ground when it's buried. It is also something you really, REALLY don't want to send to an incinerator. When burned, PVC releases some really nasty chemicals, including hydrochloric acid and dioxin.

You'll see a lot of Linux action going down here at Null Byte. We use Linux for hacking-related stuff because it provides a more relaxed programming environment, making it easy to write exploits and tools. Linux has many features Windows is lacking, such as full control over the OS right down to the Kernel and massive availability of mature, open source (read: free & tweakable) tools & projects.

It may not seem like it, but it's been less than 90 days since Google+ was introduced to the world. Since then, we've seen many great features that have made Google+ one of the most attractive social networks around. Today, we've received even better news: major improvements and feature updates that are truly innovative.

This week has been pretty exciting for both Facebook and Google. Facebook announced a slew of features that seem on the surface to copy Google+. For Google+ users, a lot of improvements, updates and features were implemented, and they're seeing a lot more overall integration with their Google account.

For this week's review round-up, we bring you two games from opposite sides of the indie world. One is a free online hybrid shooter/platformer combining elements of Team Fortress 2 and Minecraft. The other involves driving jeeps around and shooting things as fast as possible. Both are great.

Camera manufacturers release new versions of the same cameras, mostly point-and-shoot models, as frequently as Detroit's auto industry upgrades minivans. They also add new lenses regularly, upgrading previous models with adjusted zoom ranges or the image stabilization feature. The same goes for tripods, portable flashes and even camera bags.

It's a hell of a lot easier to make money selling an indie game now than it was four years ago. But it's still a rough game.

It's only been a few weeks, and already there are a lot of misconceptions and myths floating around Google+. Let's take a deep breath, and tackle some of the more prominent ones.

Although circles are Google+'s answer to the problem of social network relationship management, that's not the only thing it's good for. People on Google+ are using circles for all sorts of creative activities, some of which aren't obvious as first glance.

Introduction to the Basics of Off-Camera Flash

Nobody could predict the success of Microsoft's Kinect, not even Microsoft themselves. So, it was quite a surprise when it ended up earning a Guinness World Record for fastest-selling consumer electronics device, and an even bigger surprise to see people buying one that didn't even own an Xbox 360.

Yesterday's installment of a Gamer's Guide to Video Game Software featured Unity 3D; today we'll be covering one of the oldest consumer game making engines, RPG Maker.

There are a few different types of Apple iPhone and iPad users: general household users who largely consume media—e.g. surfing the web, watching movies, listening to music. Other iPhone and iPad owners use their device(s) to produce stuff—written documents, edited movies, blog posts, music tracks, and the like. And then there are those who are very mobile with their devices. They commute to and from work on a regular basis with their iPhone or iPad. Some users may travel a lot on business, or...

Do you ever really know someone? I mean really really? Super really? Sometimes we can talk and be with people normally for years and then bam: five people dead, house on fire, dog missing. All the while people shake their heads and regret that if they had just put the little clues together all of this could have been averted.

Making bread from scratch is extremely difficult. Painstakingly following instructions does not necessarily guarantee successful results. Baking delicious homemade bread takes practice, skill, and frankly, a level of real culinary artistry.

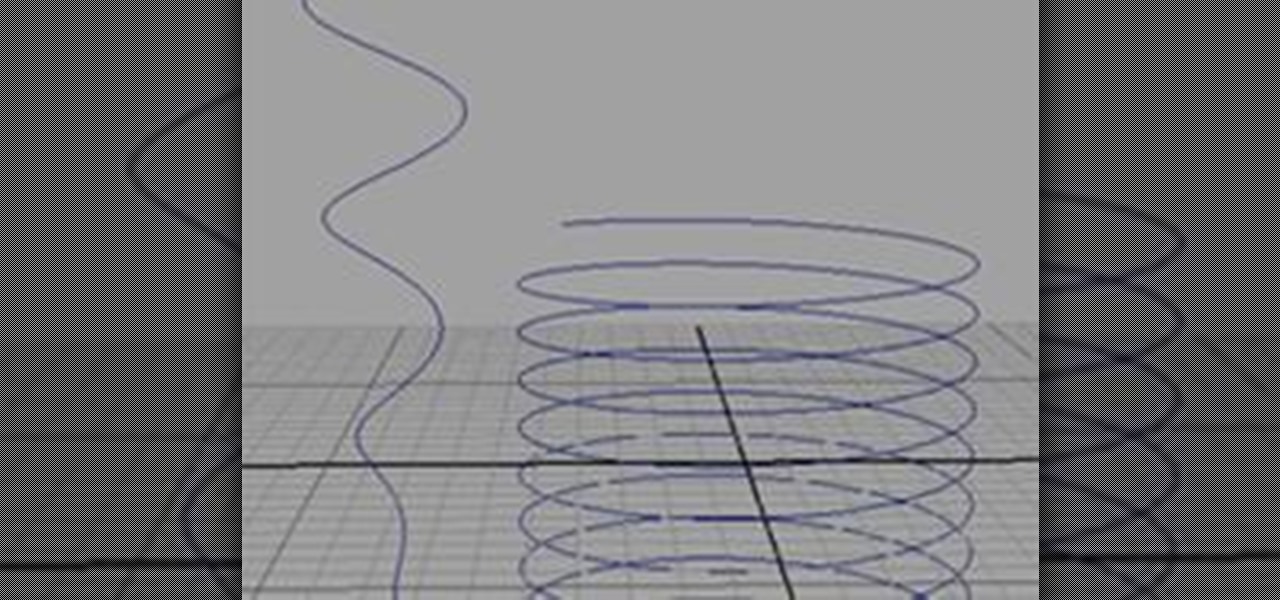
There are several ways you can go about creating your NURBS helix curve in Maya; I will demonstrate the two easiest ones.

Sure, you go online to email and shop and do research. But have you ever been curious about how the internet actually works? Don't worry, you don't need a degree in computer science to get a handle on how your info gets from point A to point B. Learning the basics of the internet will give you a whole new appreciation for all those emails and chat messages that seem to magically appear. Get ready, because we're about to enter the wonderful world of digital data!

Where were you in 1993? Thinking about starting a tech company? Starting elementary school? Awaiting a 1996 Daft Punk party after which you would be conceived? It's been eighteen years, but the game that solidified my dorkdom for good is still coming out with new sets, still fun as hell to play, and deserves some love dammit. To that end, I have started this World: A Magic: The Gathering Spot.

Huzzah! My sentences have been recorded! This is normally the most exciting part of beginning a language with this method, because you actually had another person do something for you that is really of great value. I remember receiving my first recording in Japanese. I listened to that thing about 100 times. I shadowed it, repeated it to my family multiple times and still hear it in my head from time to time.