
News: Minecraft World's Ultimate Survival Guide, Part 1
Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server.


Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server.

It's Monday, and once again it's time to highlight some of the community submissions posted to the Math Craft corkboard. In addition, I thought we'd take a look at having fun with the geometrical properties of polygons and circles by using one of the best circles I know, the penny.

Here is an alternative method to run Ubuntu 10.04 on a Mac without actually installing it on your internal hard disk.

Let's face it, not every logophile is addicted to Scrabble. Without the use of a timer, Scrabble can be a pretty slow game. Even in clubs and tournaments where the standard time limit is 25 minutes per person for a two-player game. Now, take away time restrictions and add two other players and you've got a game that could take up to 2 hours! It all really depends on who the competition is.
In this article I am going to show you how to quickly and easily make a professional looking trailer.

Banksy, Cope2, Invader, Retna, Mr.cartoon, They all have a few things in common. Firstly, they are all extremely talented and well known urban artists. Secondly, they all have very memorable and very, very cool names.

Do you do last minute cramming before you go to the dentist? No, I don't mean reading up on orthodontia in hopes of having an intellectual conversation about crowns with your dentist (how you can talk at all with all those tools in your mouth is beyond me, though dentists always ridiculously try).

Been hacked once? Twice? Maybe more? You thought abc123 was the only password that is both 6 characters wide and easy to remember? I have some suggestions in store for you. Just read on...

Blackbirds are NOT singing in the dead of night. At least, not in Arkansas.
Inception may not be the lead contender for the 68th Golden Globe Awards, honoring the best movies and television from 2010, but Christopher Nolan's film still collected four nominations— Best Motion Picture, Best Director, Best Screenplay and Best Original Score.

Intro To use the information in this article you need a jailbroken iPhone or iPod Touch of any generation. It doesn't matter what version of the IOS you jailbroke it with - just make sure it is jailbroken. If you need help jailbreaking your iPhone WonderHowTo has plenty of tutorials. Otherwise, leave a comment and I'll help you out!

Willow Smith has what it takes to be a star, just like her parents, Will and Jada Smith, and her brother, Jaden Smith. But this Smith, at the tender age of 9, is quickly becoming a pop superstar and preteen trendsetter, thanks to her music video "Whip My Hair".

We are embarking upon a new year. As usual, some of us will make "resolutions." There isn't anything wrong with setting goals for the year. It's actually a good idea. It may help focus the energy we bring to life.

Traditional Aboriginal didgeridoos are made from trees that have been hollowed out by termites. Finishing work to smooth out surfaces and decorate the didgeridoo would soon follow. Lucky for you, you don't have to spend lots of money or find a hollowed out tree to create a didgeridoo!

PDF is a convenient format for documents that can embed text and pictures and can be read by almost any device—personal computers, laptops, smartphones, etc. However, PDFs are mostly read-only files, so sometimes it's necessary to convert them to JPG images, a universal format for pictures. JPGs can be modified by software such as Adobe Photoshop or posted on Facebook.
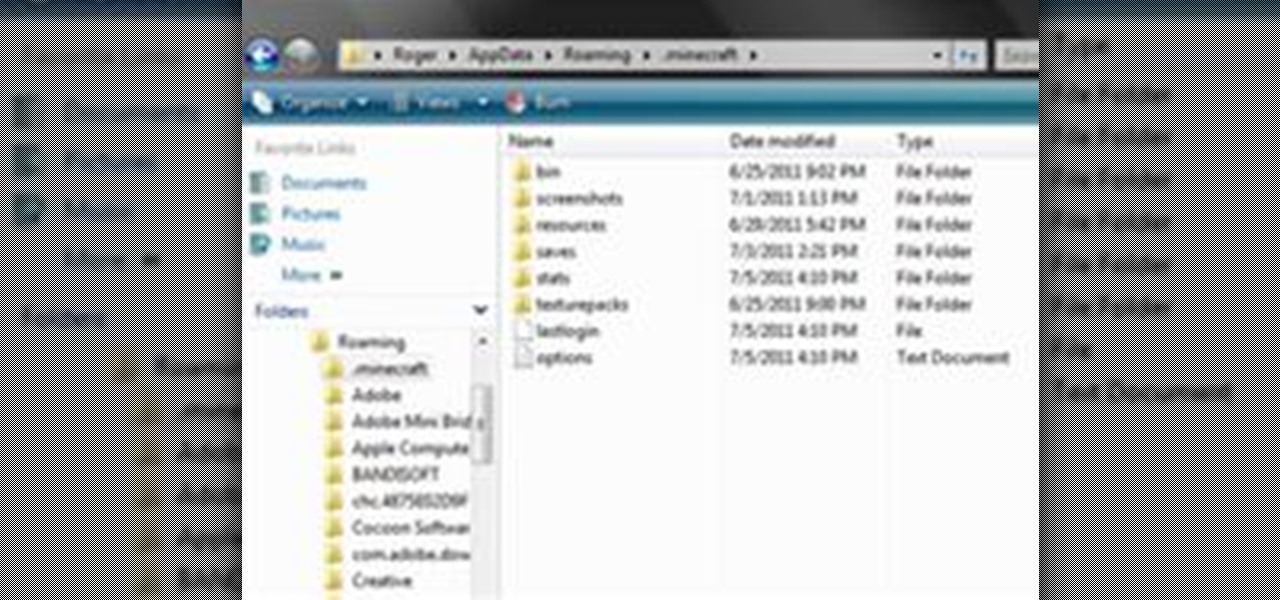
In this article, you will learn how to move your Minecraft save files. This knowledge is very useful if you want to give your friends a copy of your offline world, or play on one of theirs. You can also make backups, or move your offline world to your server folder to play online.

Some of you may stick with your iPads, but for those looking for a similar Android version, you finally have a winner.

Christmas is almost over— all of the presents are unwrapped, all of the prime ribs have been eaten, the whole family's drunk off eggnog— and soon it will be time to forget about Christmas until next year.

Google's much anticipated eBook Store has finally opened. As of today, the digital bookselling enterprise is awaiting your needs, with over 3 million eBooks to read directly on the web or on other platforms, like Android, iPhone, iPad, Sony and Nook devices.
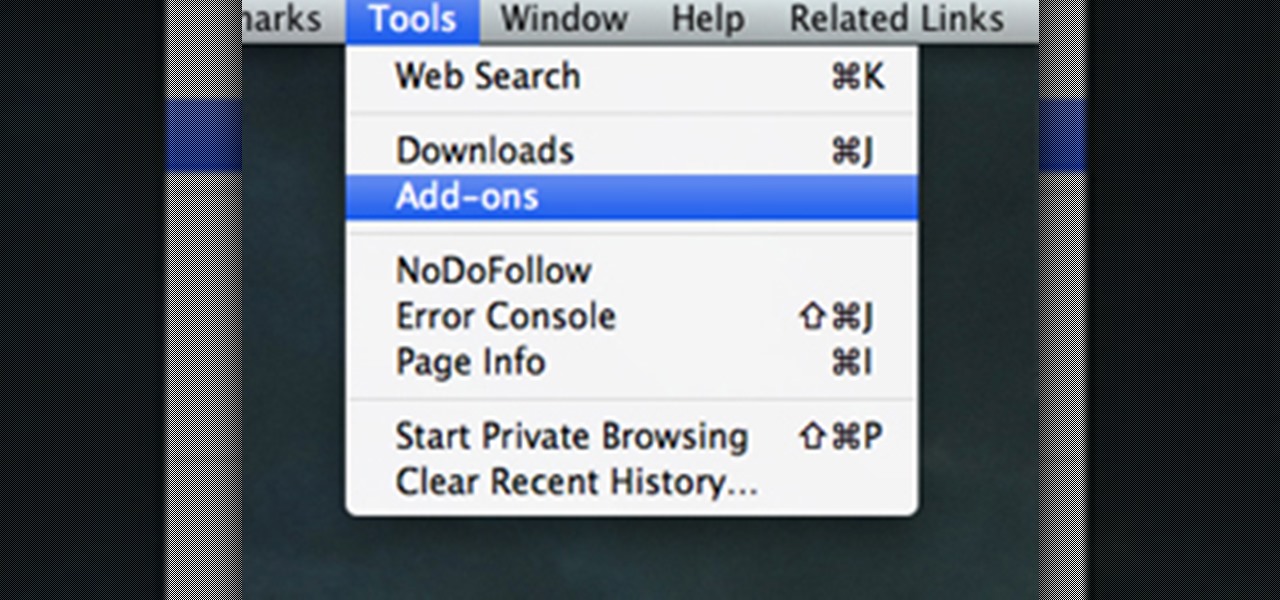
There's a whole lot of brouhaha going on right now about the hidden plug-ins being installed unknowingly in the Mozilla Firefox web browser, with companies like Apple, Microsoft and even Google being named top offenders.
Ever wonder how all of those tiny chips and components can fit inside your laptop or smartphone? If you tried to squeeze them in there yourself, your laptop would quickly become too heavy for your lap, and your mobile phone would need wheels to stay mobile.

Hey, hackers! Now that you've hacked/owned your first "box" in my last article, let's look a little closer at another great feature of Metasploit, the Meterpreter, and then let’s move on to hacking a Linux system and using the Meterpreter to control and own it.

We've talked about the deep web before, but we never really covered the details of what's out there. It occurred to me that a nice list of resources would be very helpful to all of you anons out there. Think of this like a helpful brochure to the hidden web.

In my Wireshark article, we talked a little bit about packet sniffing, but we focused more on the underlying protocols and models. Now, I'd like to dive right back into Wireshark and start stealing packets.

Today isn't actually Pi Day, but I was unable to get this article out in time. Pi Day was actually yesterday, March 14th (3.14), so let's call this a post-Pi Day treat!

Pull up outside any construction site and you'll see tools scattered about—hammers, jigsaws, nail guns, hydraulic pipe benders—these are the tools of the trade. You would be hard-pressed to build a home or office building with just your hands! On that same page, security professionals also have their own go-to tools that they use on the job site, only their job site is your server.

WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects.

Okay, so what are we going to make our videos about? I’ve written before about creating articles, and what kind of content we are going to put in our articles. So what are we going to put into our videos? Let me give you a few ideas that I have. These are some things that I would do if I had a service business.

You've probably seen those deep-web images floating around on the Internet. Usually, it goes something like this: There is a towering iceberg and the deeper the underwater portion extends, the more “hidden” and “exotic” the content is described to be. Sometimes these images are accurate to a point, but most are just making things up.

As you progress in the world of information security, you'll find yourself in situations where data protection is paramount. No doubt you will have files to hide and secrets to share, so I'm going to show you how to use the GNU Privacy Guard (GnuPG or GPG for short) to encrypt and decrypt as you need. GPG is a great open-source version of Pretty Good Privacy (PGP), a similar application used for encryption, but licensing and patent problems led to the development of GPG in its wake.

In this article, I'll show you how to built a Wireless Transfer of Energy Transmitter. Simply put, this device will send electricity to a florescent light bulb and light it up, from up to three feet. The idea originally (at least, prominently) came from Nikola Tesla (read more about this amazing inventor here), who used his Tesla coils to transfer wireless energy to light bulbs in demonstrations (photo below). However, the circuit described in this article consists of a flyback transformer, n...

In this article, I'll show you how to create a simple yet effective way of scaring off intruders. Of course, there are methods around this approach, but it's great for office pranks and general fun. The project requires a little background knowledge in electronics and circuitry, like reading schematics and using a soldering iron.

This is the third part of my electromagnetic pulse series (see Part One and Part Two). By now, I've covered the hardware and general concept of electromagnetic pulse generators, but how exactly do they disable electronics? How can an invisible field of energy have such a catastrophic effect on computers, cell phones, and most any other electronics? I'll be answering all these questions in part three of Making Electromagnetic Weapons.

WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects.

WonderHowTo is made up niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects.

Welcome to WonderHowTo's first Weekly Community Roundup! Each week we will be featuring the best projects from the community, as well as ongoing challenges and activities you can partake in. WonderHowTo is made up niche communities called Worlds, so if you've yet to join one, get a taste of what's been happening this week in the highlighted Worlds below...

Now that Google+ is open to everyone, there are a lot of new people who aren't techies trying out the service. When you first sign on, it can be overwhelming. I've decided to round up a bunch of resources to help you get started, and recommend some people for you to follow, if you want to stay on top of tips and new announcements.

If you haven't noticed yet, I've started dishing out some "Scrabble Bingo of the Day" articles that showcase interesting and somewhat unusual seven-letter words (or longer) that could give you an extra 50-point bonus on the board, as long as you empty your rack. So, for this week's Scrabble Challenge you'll have to get your brain in gear, because it's a tough one based of high-scoring bingo plays.
I've struggled for a long time trying to set up a virtual network between my KVM virtual machines. I tried several forums and tutorials on the web, but still on my system it just wouldn't work. I eventually got it owrking, so I've decided to make some notes of my own. Hopefully it will be helpful to you as a reader as well.
Dropbox continues to make headlines with their recent programming blunder which left the accounts of its 25 million customers wide open during a four-hour time span. During the duration, anyone in the world could access any Dropbox profile by typing in any password. And seeing as this wasn't the first security failure, everyone, including the most loyal users are considering dropping the Dropbox.