We recently covered a set of ported apps from the new cloud-based smartphone, the Nextbit Robin. These ported APKs brought two of the Robin's slick new stock apps—Camera and Gallery—to any other device, but the launcher was conspicuously absent.

The sprouts, they're alive! Alive, I tell you—aaaaaaliiiiiive! (Cue dramatic music.) It's true: sprouts are a living food, and they're packed with more nutritional benefits than some raw vegetables. It's easy and fun to grow your own sprouts from seeds, legumes, and grains. Plus, watching them grow is incredibly satisfying—you're bringing new life into the world (and onto your plate)!
The iPhone's pinch-to-zoom feature lets you easily enlarge photos to focus in on one particular area a little better, but after you've zoomed in to a certain degree, the image quickly snaps back and prevents you from zooming in any further. This is mostly meant to keep you from zooming in too far and getting lost, but a lot of times, the max zoom level just isn't close enough.

HTC's newest flagship smartphone, the HTC 10, has been met with nearly universal acclaim despite a weak amount of sales over the last few months. Most reviewers point to the device's gorgeous hardware as its main attraction, but at the same time, it certainly has some nice software to match, as this year's Sense 8 may be one of the best manufacturer skins ever.

Verizon customers who use the Samsung Galaxy S7, beware: a recent update installs new bloatware over your existing bloatware that installs new bloatware. Confused or pissed off? You should be, as this app can install new apps onto your phone without you knowing.

The only knock on Samsung's last round of flagship devices is that TouchWiz is still alive and kicking. Aside from this overbearing skin that's been applied on top of Android, the Galaxy S6, S6 edge, Note 5, and this year's Galaxy S7 models are some of the best phones money can buy.

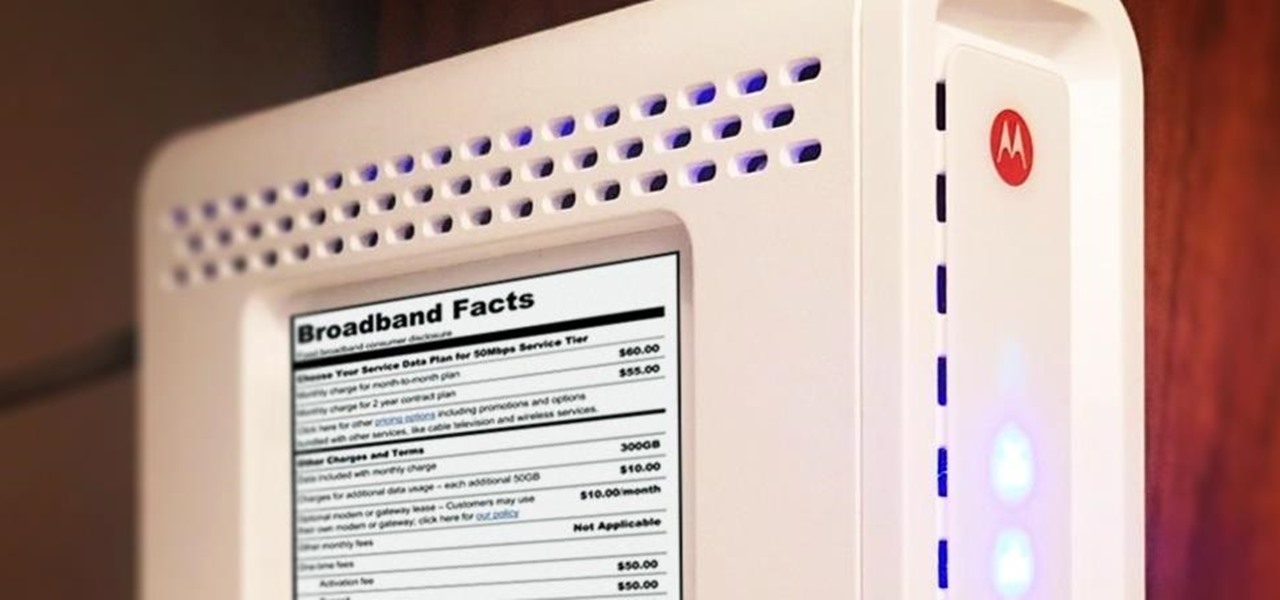
Shopping around for a good broadband company or mobile carrier may soon be as easy as shopping for cereal, thanks to the introduction of broadband consumer labels by the FCC for both fixed and mobile broadband.

When Android N is officially released sometime later this year, it will bring a lot of cool new features along with it. We've already had the chance to play around with some of these, thanks to a preview build available to Android beta testers, and one change that we like in particular is a revamped Settings menu. Among other things, each settings entry now has subtext beneath it that shows relevant info at a glance.

Sourdough is a delightful twist on your traditional bread, but creating and maintaining a sourdough starter can be a headache for many home bakers.

On Wednesday, Microsoft launched a chatbot on social media that learns from conversation, and trolls quickly taught it how to be a shameless, Nazi-loving bigot. Oh Internet, an opportunity for a Hitler joke never slips past you, does it? This Is Why We Can't Have Nice Things

When you delete a file, Android doesn't actually remove it from your storage drive—instead, it simply marks that space as empty and pretends the file doesn't exist anymore. But deep down inside, the file that you originally wrote to that location is still physically there, at least until you randomly happen to save another file on top of that same spot.

Video: . The following are 5 Simple household pranks you can pull off on friends and family this upcoming April Fools' Day! All the material needed you already have at home so lets get started! Check out the video tutorial for further instruction.

Google's YouTube Red is an awesome service, particularly in the United States where it comes bundled with a subscription to Google Play Music. You don't have to worry about ever seeing ads again on any videos, you can continue playback after you exit the YouTube app or even when you turn your screen off, you can download videos for offline playback, and you'll have access to YouTube Music.

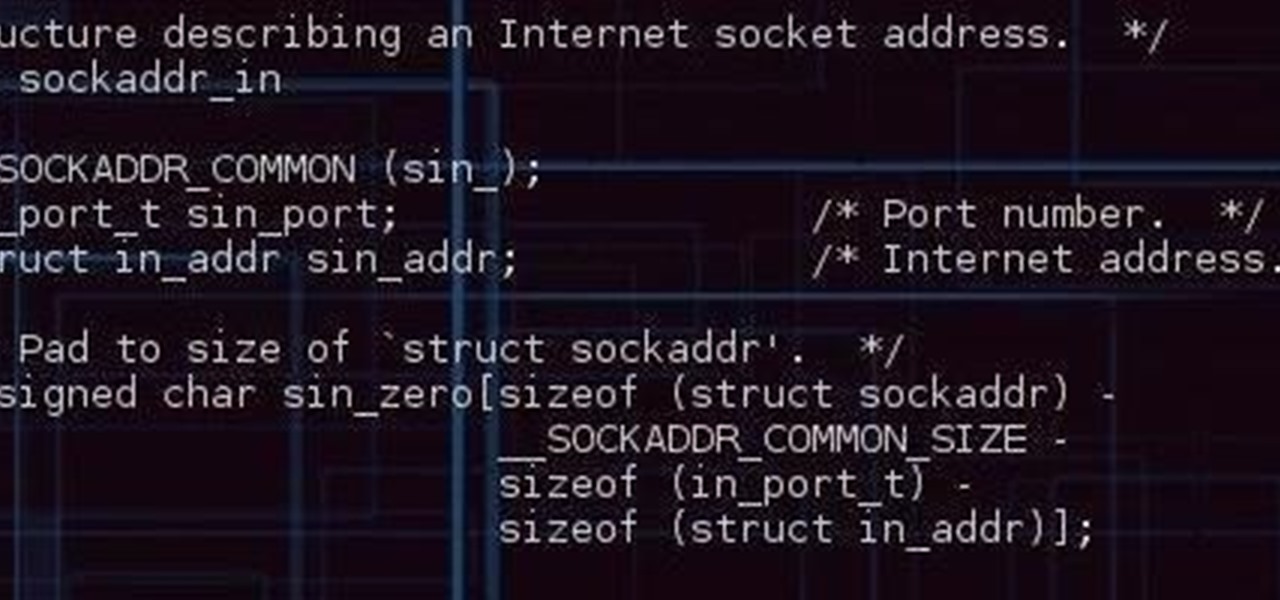
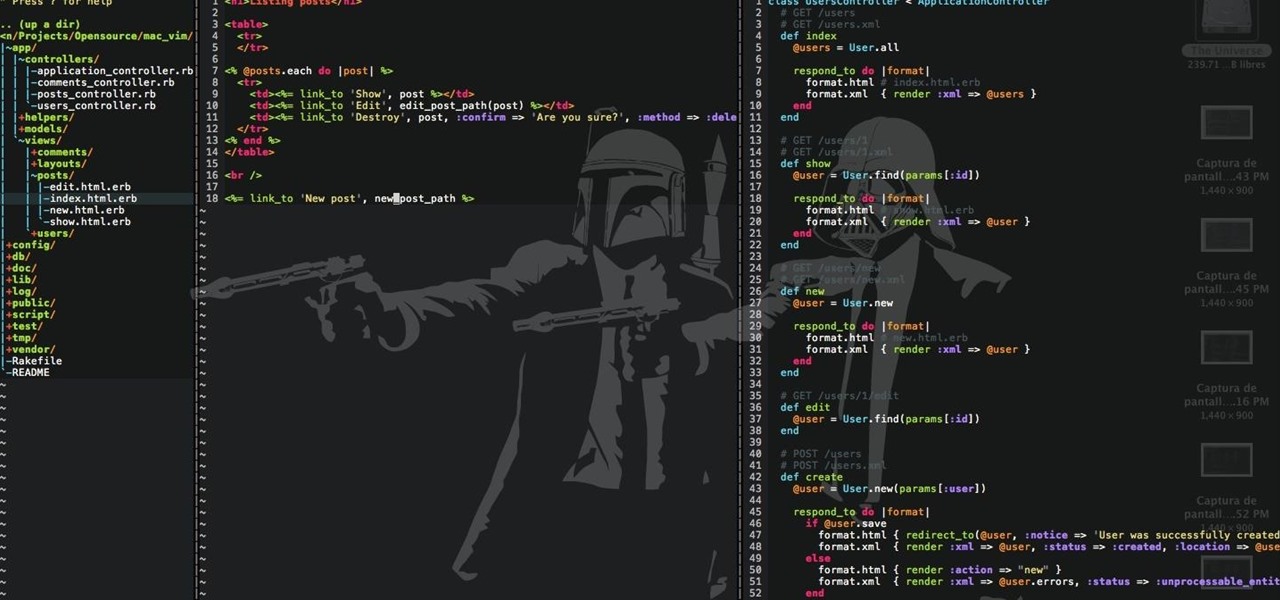
Alright so last time I gave you a homework assignment. This week we're gonna look at my version of the UDP-Flooder.

Welcome back, my budding hackers! Metasploit, one of my favorite hacking/pentesting tools, has so many capabilities that even after my many tutorials on it, I have only scratched the surface of it capabilities. For instance, it can be used with Nexpose for vulnerability scanning, with Nmap for port scanning, and with its numerous auxiliary modules, nearly unlimited other hacking related capabilities.

In my last tutorial I very briefly introduced Zanti , but in this tutorial I will start to show its many features. The first step on hacking is recon . You could use Nmap , but the problem with Nmap on Android is that by itself, in order to gain full functionality your phone must be rooted. Thank goodness for a few geniuses in Zanti's dev team whom managed to implant full fuctionality of Nmap in Zanti without rooting your phone. With that being said, boot up your Android phone and lets start ...

Samsung makes some wonderful phones, but one thing I've noticed is that battery life can start to degrade over time, causing the phone to die a lot faster than it used to. If you've been experiencing this issue, and have asked yourself, "Why does my Galaxy S5 die so fast?" there are a few likely causes—and we've got you covered with troubleshooting tips and simple fixes below.

Cord cutters are changing everything about TV—the more of us that sever ties with cable, the more changes we start to see. In fact, viewing habits have already changed so drastically that waiting a week to see the next episode in a series is no longer acceptable, as binge watching has completely eclipsed this old-fashioned format.

Hello there Nullbytes, In my previous tutorial found here,

Hello there Nullbyte users! This will be my first article here.

Welcome back! Sorry I've been gone for so long, but if anyone has been keeping up with these articles, you'll know that when I get quiet, something is cooking under the surface. In other words, I've been working on a project lately, so I haven't had much time!

Before we dive into the world of frustration, I first would like to thank whoever of the admins and mods made the folder for Raspberry Pi in the How-To's, thank you. Now with that outta the way, this article is about Metasploit on Raspberry Pi (hence the title). I should say that I ran into a error, but I think I figured what the problem is. First of all this is not on Kali Linux, but on a regular Linux OS. With that said let's open up a terminal and begin.
This is for those using Kali Linux 2.0 that need to edit the CRDA values to get the increase in Txpower

Starting a few months back, you might have noticed that some text messages you received from certain friends or family members had blank or missing characters. This was because Apple included all of the new Unicode 8.0 emojis in an update to their iPhones, but Android devices didn't have some of these just yet, so they weren't capable of displaying them.

It's nearly impossible to keep a stovetop clean when cooking, at least, in my experience. No matter what I do, liquid and solid food bits fall to the surface and around the burners every single time, creating a hard-to-clean mess.

Say what you want about Samsung's TouchWiz UI being cluttered or overbearing, but one thing you can never complain about is a lack of features. In fact, it's been almost 8 months since I first took my Galaxy S6 Edge out of its box, but I'm still discovering features to this day.

With every version bump, Android gets a new Easter egg that can be accessed by tapping the "Android version" entry in Settings. For the most part, these have generally been little animations or live wallpapers that depict the Android code name, but starting with version 5.0 Lollipop, things got a bit more interesting.

Recently I was trying to install Kali Live on a USB drive with persistence and struggled to find a tutorial online that was simple and actually worked. After some trial and error I figured out how to do it correctly and decided to make an article for anyone who is experiencing the same difficulty I did. You will need an USB with at least 8GB. Mine is 132GB, nice and large.

After a few months, I get so fed up with hearing the same ringtone go off alongside each new notification that I'm forced to switch things up—only to end up repeating this whole process when the new one gets played out. And I'm sure people around me are equally sick of listening to that tired old tone towards the end as well. I mean, a decade later, I'm convinced that Nokia tone is permanently implanted in my brain.

Hello everybody Joe here. Today I will be demonstrating how you can find XSS vulnerabilities in a website and what you can do with them

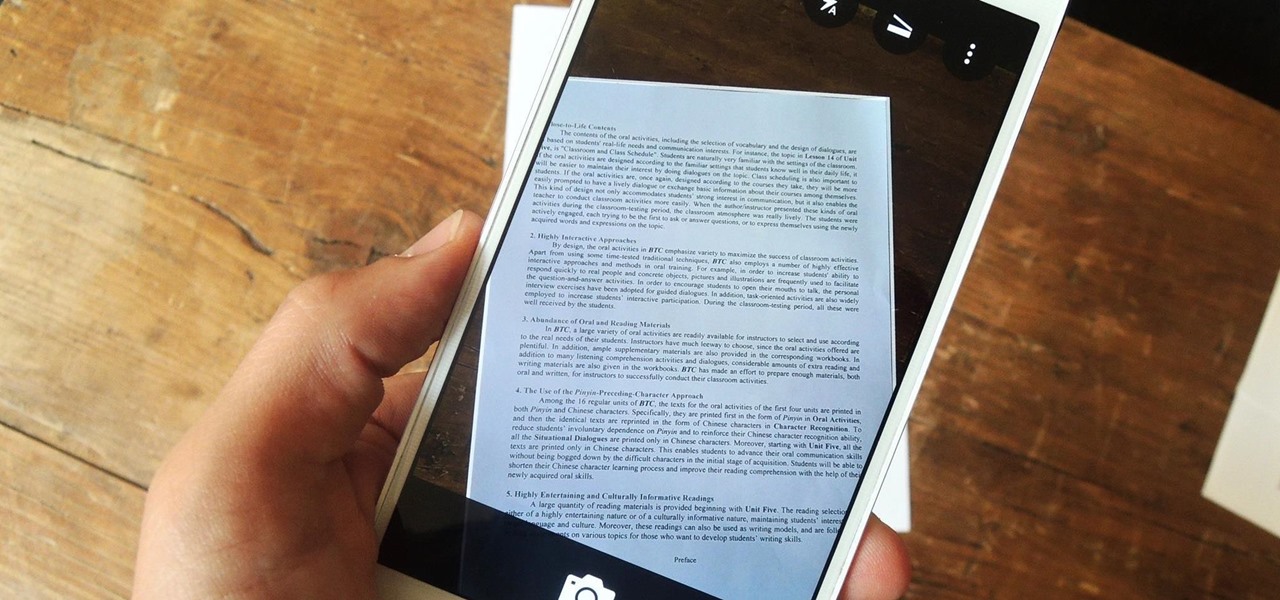
Scanners are much too cumbersome to fit in a pocket, but with the use of just one application, you can replace all that bulky hardware with your Android smartphone and take it with you wherever you go. All you need to do is find the scanning app that fulfills your needs. Here are our five favorites that are good for business pros and average joes alike.

Welcome back, my nascent hackers! Although my favorite TV show, Mr. Robot, had completed its first season already, I have not completed demonstrating the hacks that Elliot used in the show. (By the way, I can't wait for season 2!)

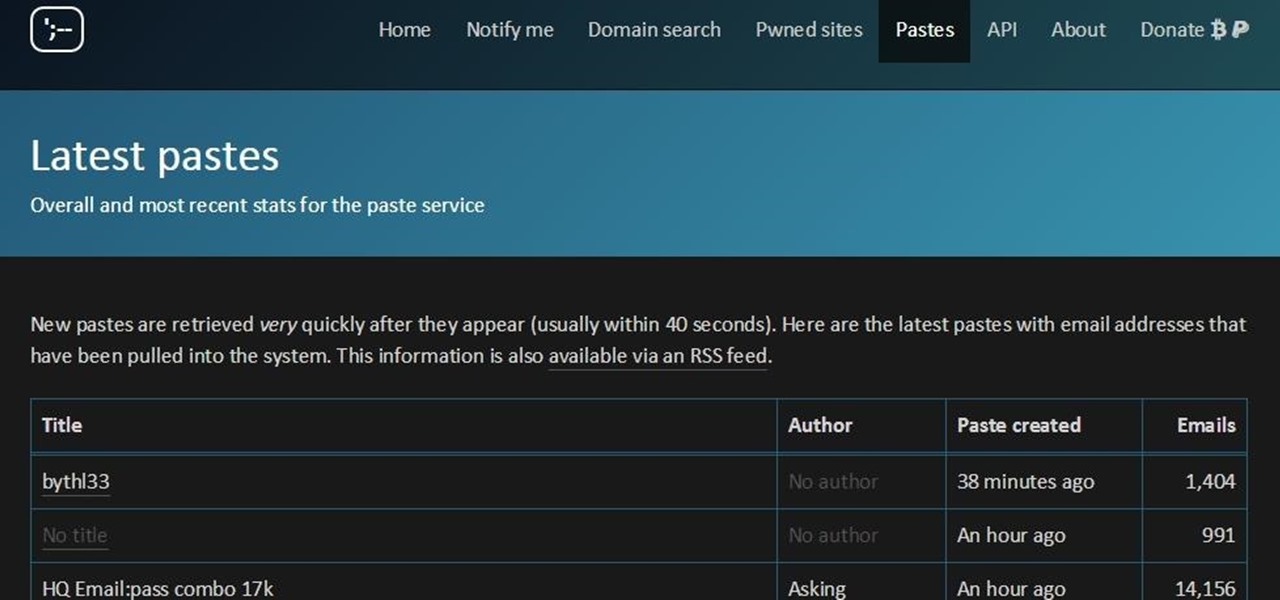
This is second post in my series of posts for finding hacked accounts online. Please do read the part 1 of the post at http://null-byte.wonderhowto.com/how-to/find-hacked-accounts-online-part-1-0164611/

You must have read news about hackers dumping the data online, recent one was Ashely Madison. It's only the big companies' data, which gets noticed once it is out. There are many other small leaks which don't even get a mention. So this article is the first one of my series which will help you to find hacked accounts. Some of you must already know about this, but this post is intended for the new learners. This also serves as an example of my learning how a good service can be used in other w...

I record close-cropped videos and take macro still shots with my smartphones on a daily basis, so as you would expect, I spend a lot of time cleaning these devices. Over the course of a couple years, I've fine-tuned my cleaning regimen, and at this point, it's down to a near-science.

In modern versions of Windows, Microsoft made quite a few changes to Windows Explorer, the first of which is a new name—File Explorer. Another huge change that most will notice is that File Explorer now has a new look sporting the Ribbon interface.

The horizontal dotted icon in your iPhone's status bar serves as an indicator of your device's network strength. And while it does help provide an approximation of how strong your signal is, swapping it out to display an actual numeric value is a lot more precise and can change up the look of your iPhone (or at least the status bar). The process is quick, painless, and you don't even need to jailbreak your phone.

You're smashing your keyboard to increase your screen brightness, yet it won't go any higher, but you know you've been able to set it higher before. Angered by this, you get up and move your laptop, only to suddenly notice that the display does in fact get a lot brighter.

I was a vegetarian from age 6 until age 23. When I started eating meat again for the first time in 17 years, most people I knew (including me) expected me to be pretty conservative about it: chicken breasts, hot dogs, and all the other "basic" meats that everyone loves.

More than likely, the first thing you noticed after booting up Windows 10 initially was a handful of new items in the taskbar across the bottom of your screen. Windows 8 users were probably glad to see the Start menu button back from the dead, but just to the right of that Windows logo are a pair of brand new entries.