CHICAGO (CBS) – Police Supt. Garry McCarthy said Sunday that a group of out-of-town protesters attacked a police van while hundreds of protesters were wandering around downtown Chicago for about 10 hours.
The United States asked Russia to send Iran a message that the upcoming round of nuclear talks is its last chance to avoid a military confrontation this year, Russian newspaper Kommersant reported Wednesday according to a diplomatic source.

Life on the frontier was hard, and it still is in the Zynga Facebook game FrontierVille. If your homestead has been attacked by foxes or wolves, this video will teach you how to beat them, clobbering their little furry butts clear of your homestead for good!

If you want to have a character get attacked by a predatory land animal in your movie, you are probably going to need to put some claw marks on their body to make it look realistic and visceral. This three-part video will show you how to create a really realistic open claw mark wound on an actor's face, or any other body part. It looks really, really good, now try it yourself and scare your family and friends!

Is your kitchen out of control cluttered? Do you have paper work, utensils, and junk mail scattered in the one room in your house that should act as your sustenance sanctuary? In this episode of Real Women Scrap, the hub of every household is attacked as well as other ways to unclutter your kitchen.

When in repose upon the toilet, the last thing most people want is for something to jump out at them. And that is exactly what will happen to them if you pull this prank. It turns out that the actual tape from a tape measure is a great little prank tool, and in this video you'll learn how to attach one to a roll of toilet paper so that when your victim attempts to wipe, they will be attacked by tape and scared... witless. Yes, witless.

The video explains how to hack the game Agony: The portal. First he clicked the start game and created new character by entering the name as test dummy and set the difficulty level as normal. The he clicked the start campaign. While entering the game he skipped the tutorial and directly he went into the game.

Sharks. The first thing that comes to mind is "Jaws", Steven Spielberg's horrifying shark film that scared generations of young adults from entering the ocean waters. But not all sharks are as violent (and hungry) as "Jaws", so jump in the water and know a few guidelines to stay safe. Escape a shark’s jaws of death with these lifesaving strategies.

Attention achievement hunters! In this next tutorial, you'll be finding out how to get the Crackshot achievement in the game Dead Space for the Xbox 360. To get it, you must achieve a perect score in the Shooting Gallery in the game.

Show your fellow dance warriors what you're made of! Perform an impressive hop on a handstand trick with help from this free lesson. In order to hop on a handstand, it's important to first know how to do a handstand, as well as what muscles to use. Discover how to use the shoulders and arms to hop on a handstand with help from this expert: CJ Kendricks is an instructor, entertainer and artist who has attacked the stage at the Dirty South Awards. Learn more dance moves from this expert by sear...

The Crip walk, or C-walk, is a popular west coast dance move that requires a great deal of balance, buoyancy and switching of the feet. Learn about different foot exchanges that are used to C-walk with help from this free lesson given by an expert.

All you break dance hopefuls out there, this free lesson is for you! In this break dancing tutorial, learn how to do the six step. Find out how to do floor work in break dancing and how to make it or fake it to look like a pro!

Throw yourself into the world of hip-hop with help from this free lesson. Hip-hop foot work can be broken down into simplified movements or moves that are abstract and contrived to the music being used. Find out how to do a hip-hop combination with help from this free lesson.

You want to dance like Usher? Usher is a performer who draws much of his influence from Michael Jackson, and one of his signature moves is a variation of the air walk. Find out how to pull off this moonwalk variation with help from this free dance lesson.

Looking to enter the world of the pop & lock? Learn the difference between the two with help from this free lesson. In dance, popping is all about popping the body by flexing muscles and grinding shoulders, while locking is a way to cut off flowing movements.

Looking to break into the break dancing world? In this video, learn some easy moves in break dancing with start with top rock basics, such as stepping out with the right foot, crossing the arms, crossing the left foot in front and opening the arms. Add flair to these dance floor friendly moves, with help from this free lesson.

In this video pest control specialist Mark Govan of ABC pest control shows you how to fight the war on fleas. Protect your home and animal from getting attacked by these blood suckers.Follow the advice in this video and make sure you prevent an invasion or attack on these annoying little creatures.

This walkthrough guide will cover the complete Overload DLC mission pack for the Mass Effect 2 action role-playing game on the Xbox 360. Overload became available for download in June 2010 on Xbox Live Arcade (XBLA), and features four different missions. Watch this series for all the gameplay action from Mahalo.

Of course, in a Star Wars story, one cannot hope to board a major ship and take it any major distance without being attacked by Rebel or Imperial forces, depending on your side. Star Wars: The Force Unleashed 2 is no exception, and in this video you'll learn how to deal by beating level 7: The Battle for the Salvation.

Achievement hunters, listen up! It's time to head into the Transformers' world with Transformers: War for Cybertron. This game takes place on the planet to both the Autobots and Decepticons and it gives you a first hand experience of what happened on that planet.

The moonwalk has been written in history and will go down as one of the most well-known dance crazes next to the Macarena and the jitterbug. In order to moonwalk like Michael Jackson, it's important to focus on the pivot and push of the feet and legs while sliding. Make your moonwalk smooth with the tips and tricks given in this free dance lesson.

Your sewing machine needs bobbin thread to create overlock stitches, so keep your machine going by learning to fill your bobbin.

Women's self defense strikes are extremely valuable in a world where women are attacked everyday. Learn self defense strikes, kicks and punches with tips from a martial arts expert in this free self defense video series.

Before you bite into that beautiful tomato in your garden, the tomato fruitworm, or the Colorado potato beetle, might have beat you to it.

Tired of being attacked by the goblin army in Terraria? Here's a sure-fire, or rather sure-lava, method for defeating them. Watch this video to learn how to design a lava trap that will make the goblin army vulnerable to your attacks.

This video discusses basic techniques for diving and defensive volleyball positioning when being attacked by the left, right, and middle hitter of the opposing team.

This week, the thread heads teach us how to make our t-shirts cooler, by cutting slits all over them. Not only are they stylish, but they make you look like Wolverine just attacked you. Awesome!

Sulfuric acid is mixed with sugar, which is attacked by the acid. The final products are carbon, water vapor, and sulfur dioxide gas.

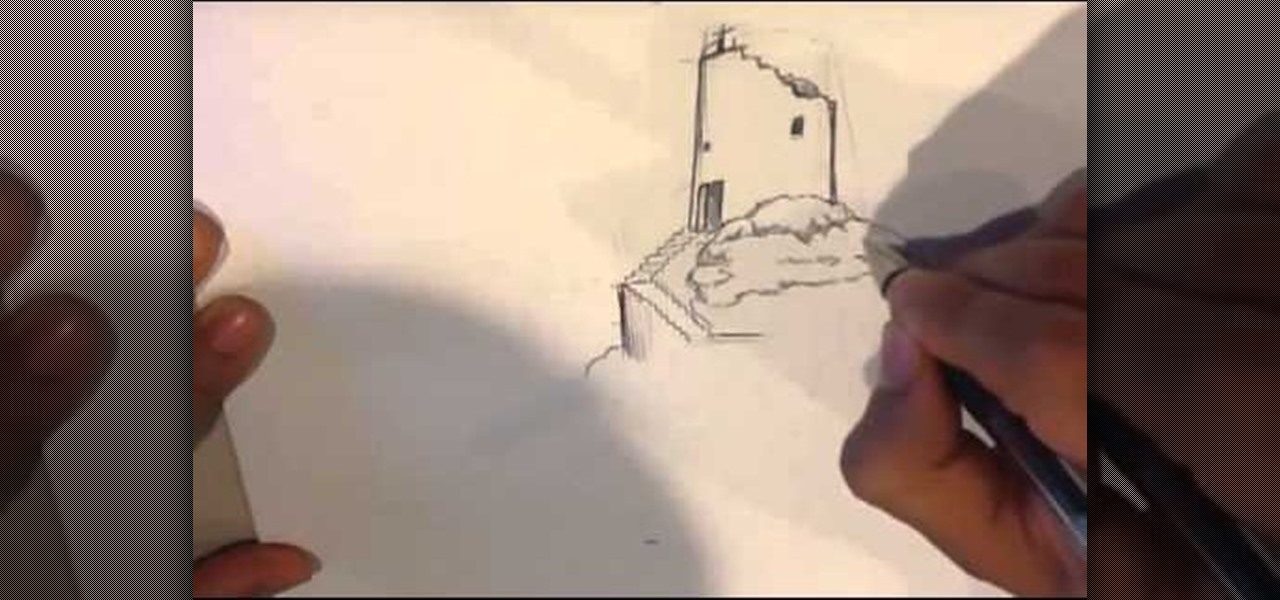
When the castle has been attacked there are only ruins left. Here is the drawing video by which i go over drawing medieval ruins. Goes with other how to draw fantasy , art videos, and art tutorials. I go through my thought process in detail at :

As was mentioned by the great OTW last week, TOR, aka The Onion Router, has had its integrity attacked by the NSA. In an attempt to reduce the anonymity granted by the service, the NSA has opened a great many nodes of their own. The purpose is presumably to trace the origin of a communication by compromising some entrance and exit nodes. Once both are compromised, it is much easier to correlate traffic with a particular individual.

As many of you know, I have been running a couple of series here on Null Byte about digital forensics called Digital Forensics for the Aspiring Hacker and Digital Forensics Using Kali. Although many readers have seemed to enjoy these series, just as many seem to be pondering, "Why should I study digital forensics?"

CEO's of IT companies doesn't know this because they are not a hacker. Only a true hacker can become a successful Security head officer.

In recent weeks, major bank websites around the world have experienced outages after being have been hit with Distributed Denial of Service (DDoS) attacks. Although few, if any, of these banks have been totally knocked offline, these DoS attacks have dramatically slowed the response time of their websites to legitimate customers. The most recent victim was the Royal Bank of Scotland. Due to this attack, RBS customers were unable to access their accounts for about an hour last week.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

Depending on how many Watch-compatible apps you have, the Home screen on your Apple Watch is either insanely clean or absurdly messy. When I first synced my Watch with my iPhone, I was attacked with a huge honeycomb of apps, strewn across my Home screen in no particular order.

Design flaws in many routers can allow hackers to steal Wi-Fi credentials, even if WPA or WPA2 encryption is used with a strong password. While this tactic used to take up to 8 hours, the newer WPS Pixie-Dust attack can crack networks in seconds. To do this, a modern wireless attack framework called Airgeddon is used to find vulnerable networks, and then Bully is used to crack them.

The public leaks of NSA tools and information have led to the release of previously secret zero-day exploits such as EternalBlue, which was used in the notorious WannaCry ransomware attack. Despite multiple patches being released, many users have failed to update their systems, so many devices are still vulnerable to these now-public attacks.

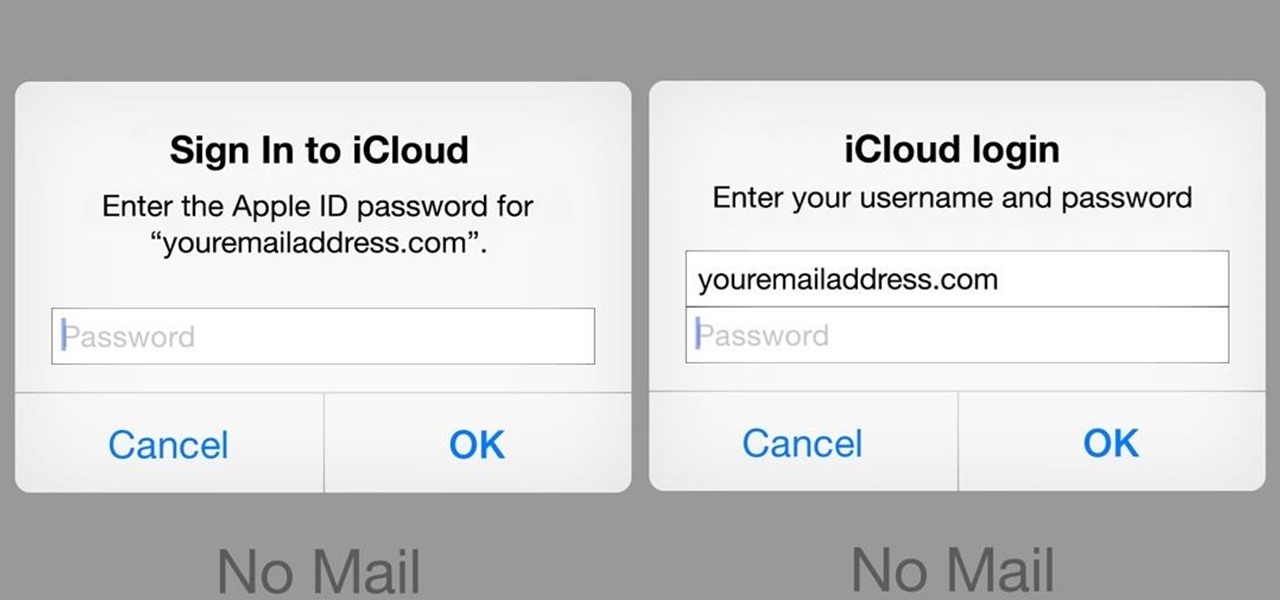
A recently discovered bug in iOS 8's Mail app by Jan Soucek can allow the maliciously-minded to quite easily phish your iCloud password without you ever thinking something has gone awry. Using a bug that allows remote HTML content to be loaded in place of the original email content, unsuspecting victims would be prompted for iCloud credentials in a popup that resembles the native one found on iOS.

Rumor has it that a gang of hackers—or possibly, one lonesome individual—holds the power to remotely wipe millions of iPhones and iCloud accounts, unless Apple coughs up some ransom money by April 7.

Since the 1960s, bacteria have been hopping a ride into space on space vehicles and astronauts, and have been cultivated within experiments on space shuttles and the International Space Station (ISS). The extreme growing conditions and the low gravity environment on the Earth-orbiting vehicles offers a stable research platform for looking at bacteria in a different light.