Welcome back, my novice hackers! More and more, the world is turning to and adopting the smartphone platform as the digital device of choice. People are not only using smartphones for voice communication, but also web services, email, SMS, chatting, social networking, photography, payment services, and so on.

Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of modules: exploits and payloads. Remember, Metasploit has six types of modules:

Hello my anxious hackers, the week has started and here we begin a new series that I think will help many here and not only, for those that have the opportunity to follow our tutorials but they are not yet part of the community.

Greetings all. I'm back with another informational review of the diversity of utilities for use in the sphere of hacking at your disposal. Today we are going to cover the insides of CUPP (Common User Passwords Profiler) in its entirety. The tool is very basic in nature, as there is little to no configuration needed to get cracking (worst pun ever). So let's get started, shall we?

Greetings all. Before I get into the tutorial, I would like to mention that I am fairly new to Null Byte (been lurking for some time though), and what really appeals to me about this place is its tight, family-like community where everyone is always willing to help each other and the constant search for knowledge that inhabits this subdomain is a driving motivator for me to join in. I'm glad I arrived at the right time. Anyway, wipes tears (not really)...

Welcome back, my hacker novitiates! There are many ways to hack databases, and most of these techniques require SQL injection (SQLi), which is a way of sending SQL commands back to the database from a web form or other input. In this tutorial, we will use SQL injection to get access to the underlying server. So instead of getting access to the database and its data, we will use the database as an intermediary to gain access to the underlying server.

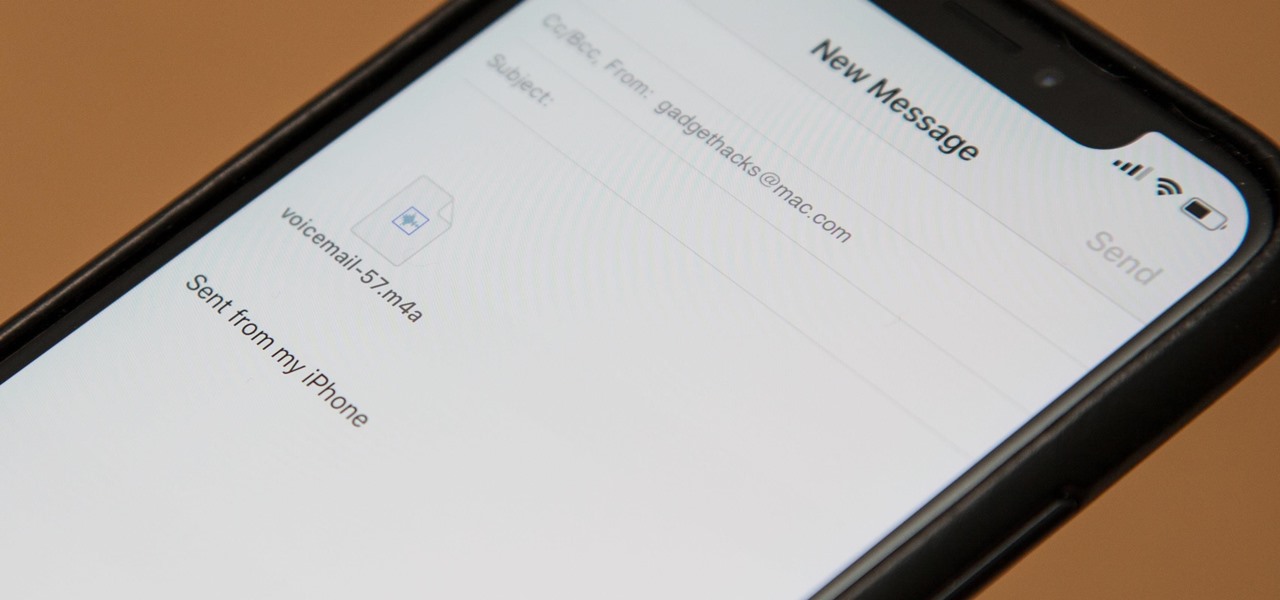
Eventually, your voicemail inbox on your iPhone will get full, and you'll have to delete some messages in order to make way for new ones. If all the voicemails you currently have are super important, you're not going to want to delete them before saving them first, of course. Luckily, this is a super simple task, and you can even forward them to someone else if needed.

Welcome back, my fledgling hackers! In this series, I am trying to develop your knowledge of digital forensics, which is valuable whether you're choosing a career in it or just want to know how your hacker activity can be traced. Few professional digital forensic investigators have a hacking background, but the best ones do.

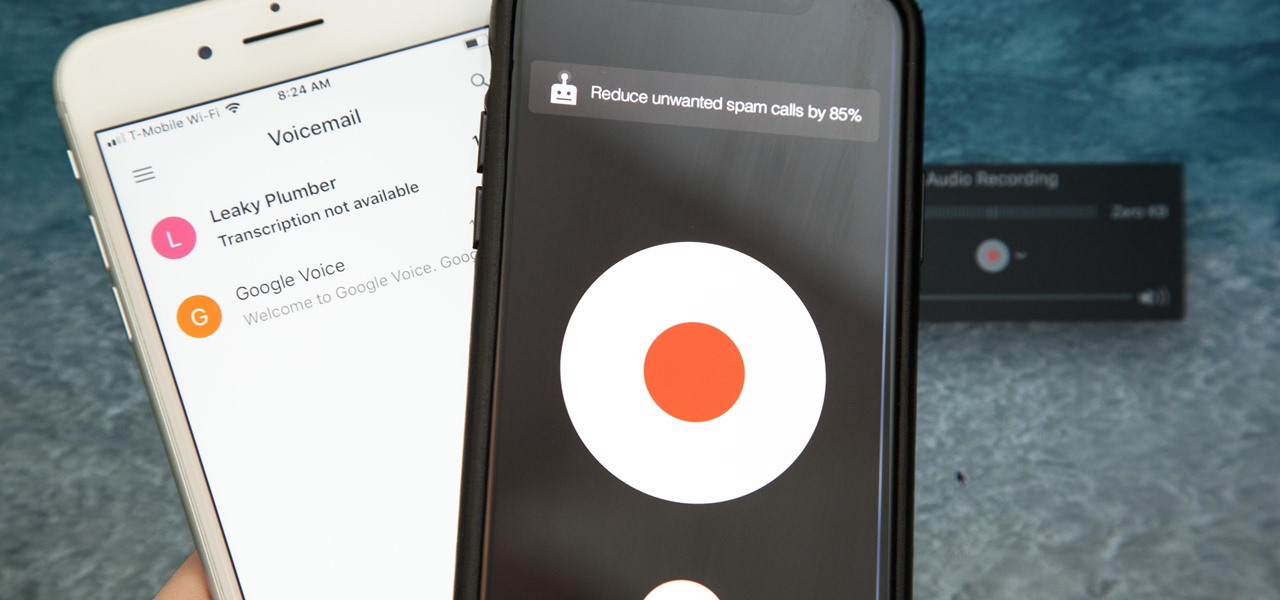
Unruly customers. Crazy exes. Horrible bosses. When you need proof of insanity or just want it for your records, recording a phone call is a must. Problem is, it's not the easiest thing to do on an iPhone — but it's completely possible.

Welcome back, my tenderfoot hackers! One of the issues we often encounter with Metasploit is how to add new modules. Although Rapid7 (Metasploit's owner and developer) periodically updates Metasploit with new exploits, payloads, and other modules, at times, new modules appear that are not added to the Metasploit repository.

As someone with a pretty nice TV, I've never found the allure in purchasing a projector. While they're certainly smaller and sleeker than a television, and more portable, they can be pricey and produce a less than stellar image. And who really buys a projector anyways? They're for school, they're for work, they're for theaters, but they're not really for my apartment, right?

Chromecasts can make for some fun nights. Whether you're setting up a collaborative YouTube watch list, letting everyone add to a giant party playlist, or playing games like Cardcast and Big Web Quiz, Google's streaming media stick is a hit by all accounts.

Podcasts are back. The Rich Eisen Show, The Joe Rogan Experience and StarTalk Radio with Neil deGrasse Tyson make up just a tiny fraction of what's become an incredibly dense market, with these being some of the most popular available right now.

Every time my Galaxy Note 3 boots up, I'm greeted by the monotonous and slightly annoying AT&T sound. If you're as tired of the stock boot up sound as I am, then follow along with me below to see how to change it to whatever sound you want, no matter what carrier version you have.

Now that you've updated your iPad, iPhone, or iPod touch to iOS 8, there's a lot of cool new things to explore. If you felt a little overwhelmed from all of the detailed information available in our Coolest Hidden Features of iOS 8 post, then I've got a simple breakdown of all of the new features available with quick links to their walkthroughs and pictures, if available. Watch the short video roundup, or skip below for the list.

What if someone asks you to do a Nmap scan but you left your pc at home? What if a golden opportunity shows during a pentest but you were walking around the building, taking a break?

The new HTC One and Nexus series devices have already replaced their physical navigation keys with soft keys, and it's inevitable that we'll see more and more of this on future mobiles. Samsung continues to buck the trend entirely, but no manufacturer as gone as far as to remove the volume rockers.

Some people put up their holiday decorations as soon as Thanksgiving is over. Some wait until Christmas Eve. Right now, the only thing in my whole apartment that would tip you off is a tiny little fake tree on the counter. I've been planning on decorating all month, but I haven't quite gotten around to it yet.

To really customize your Samsung Galaxy S3, you'll need to be rooted, because most of the coolest mods and hacks require root access. If you haven't rooted yet, you're just barely touching the surface of what your GS3 can do for you.

Welcome back, my fledgling hackers! If you're like most aspiring hackers, at one time or another you've probably spent too much time playing Call of Duty and not enough time preparing for your final exams.

Duct tape is the king of all household items. You can use duct tape for practically anything, like this sweet wallet. But duct tape isn't the only crafty tape out there; masking tape holds its own, too.

Lightning has struck, but not everyone is excited. Apple's new 8-pin Lightning connector for the iPhone 5 has replaced the aging 30-pin connector. Many users have concerns that their current third-party devices will no longer operate properly with the smaller all-digital design, not to mention the expensive price tag for each adapter. What Does This Mean for the User?

There's nothing worse than holding an ice cold brewski on a hot summer day and having no way to open it. If you're a Bud fan, you'll have no problem opening the bottle because most mass-market beers have twist-off caps. But if you have a taste for finer, more expensive brews, you'll more than likely run into the pry-off caps. Pry-offs are used mainly because companies believe it provides a better seal against one of beer's greatest enemies—oxygen. Plus it's a cheaper alternative for craft bre...

If you just got some banging new subs for the trunk of your car, then you're just about ready for the ultimate car stereo. But what kind of amp are you going to get to power those subwoofer speakers? Learn about the basics of car amplifiers in this video from Sonic Electronix, where they discusses the purpose of a car amplifier, as well as the parts of the amplifier. This includes the terminals, adjustments, types of amplifiers, and amplifier channels. Before putting together your first after...

Word 2008 for Mac is jam-packed with tons of cool and useful features and tools that you can use to make a great looking document. Starting with the pre-made templates is the best way to go, and from there, customize it the best you can, anyway you can. The Microsoft Office for Mac team shows you all the great features in this how-to video.

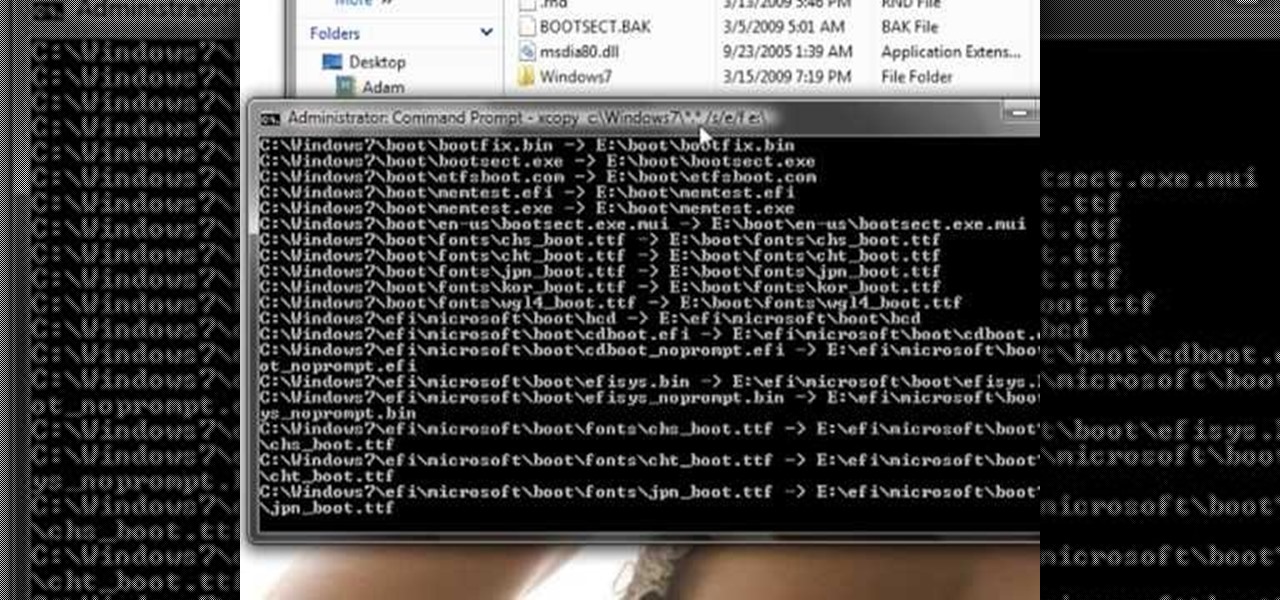
This guide works 100% for Vista & Windows 7, unlike most of the guides out there. The method is very simple and hassle free. Needless to say, your motherboard should support USB Boot feature to make use of the bootable USB drive.

Check out this video iPhone tutorial and learn how to enable MMS pciture messaging on your 3G/GS. Windows XP/Vista 32 Bit Tutorial

There are many applications you can use to record and edit audio on your computer. This video discusses two others besides Audacity – QuickTime Pro for Mac and Windows, and GarageBand, which is only available for the Mac.

Check out this video to learn how to level the bad audio off a cheap digital camera preventing extreme highs and lows. In this episode of How In The Hell, Nick Allain shows how to level the audio from video taken with a digital camera at a live concert using a free program called Audacity.

Right out of the box, iPhone is incredibly easy to use. If you want to get the most out of every feature, you’ve come to the right place. This video tutorial straight from Apple will teach you how to send SMS and MMS messages on the Apple iPhone 3G. The iPhone redefines what a mobile phone can do.

If you have ever wondered about the functionality of slating during a film shoot, what a shooting script or line script is and how to keep a shot log, then this may be the perfect video tutorial for you, in two parts.

Learn how to use Audacity, a free audio editing application that can be used to record music, podcasts, and more. You will learn how to install the LAME Encoder, set your preferences, save the project, record, preview your recordings, edit content, remove noise, adjust volume, time shift, and exporting. Each of these is an important part of the podcast creation process and you will learn to do it all in this Audacity video series.

In this video tutorial, you will learn how to mount and unmount an .ISO, .bin and .cue image with daemon tools. This is useful because when you download a game, movie or an application, you usually get an .ISO, .bin or .cue file.

This tutorial shows you how to reverse the audio and video of your footage in Premiere.

In this simple and straight forward tutorial you will learn how to record audio voice overs directly into Sony Vegas 7.

How to install a video and/or audio card into your custom built DIY PC.

In this video series, watch as computer, internet and software expert Matt Nichols teaches how to use BearShare to download music. Learn the basics of BearShare software, how to download BearShare, how to install BearShare, how to search for songs to download, how to download music, how to get a monthly subscription to BearShare, how to use the playlist, how to burn CD's using BearShare, and how to use BearShare for social networking. File-sharing is a great way to learn about new music and s...

Samsung decided to jump into the foldable category early, announcing the Galaxy Fold in February 2019. After a major hiccup, Samsung released the phone four months later to praise. But Samsung's not finished with foldables, as the new Galaxy Z Flip is just on the horizon.

What better band than Pink Floyd, the pioneers of psychedelic and progressive rock, to show the music industry how to reinvent album art for the augmented reality age?

Surprising? No. Exciting? Absolutely. After a grand introduction by at the Apple event on September 10, 2019, the iPhone 11 is finally here. We may have known nearly everything about this new iOS device ahead of time, thanks to the usual surge of reliable leaks and rumors.