WordPress did not become what is arguably the most popular blogging and CMS platform on the planet because it was difficult to use. Rather, its user-friendly and rich feature set led to it finding a home on somewhere north of 70 million websites—and that's just counting blogs hosted on WordPress.com.

Metasploit is an extremely popular pentesting tool capable of enumeration, exploitation, and injecting shell code, and is a part of almost every hacking toolkit. So there's no way I could leave this out of our series on getting your Mac set up for hacking.
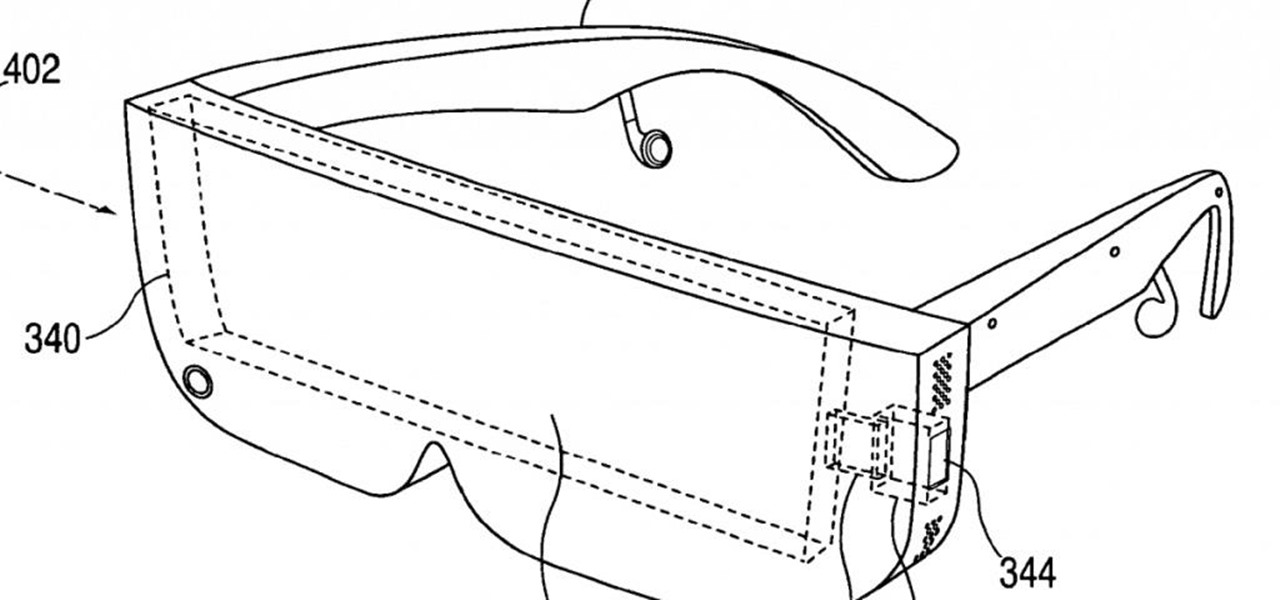
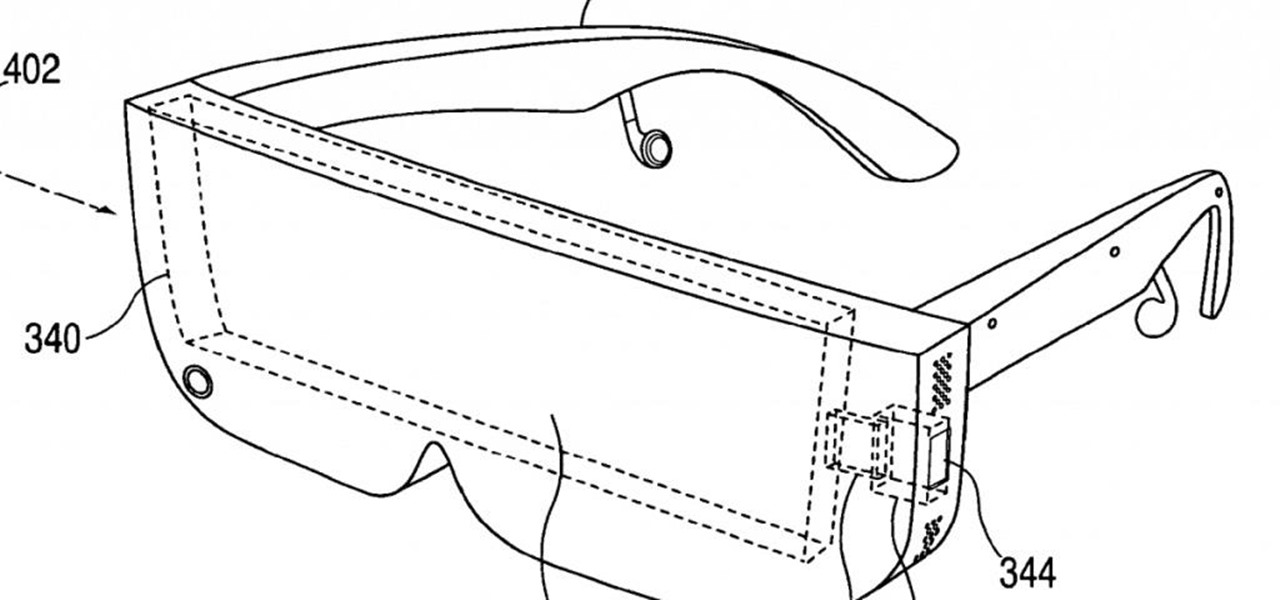
Apple's plans for virtual, mixed, and augmented reality have remained a mystery for some time, but now we at least have some idea of what they're thinking about. UploadVR uncovered a patent showing a VR headset design that looks like a thick pair of sunglasses and utilizes an iPhone to provide an experience similar to the Samsung Gear VR.

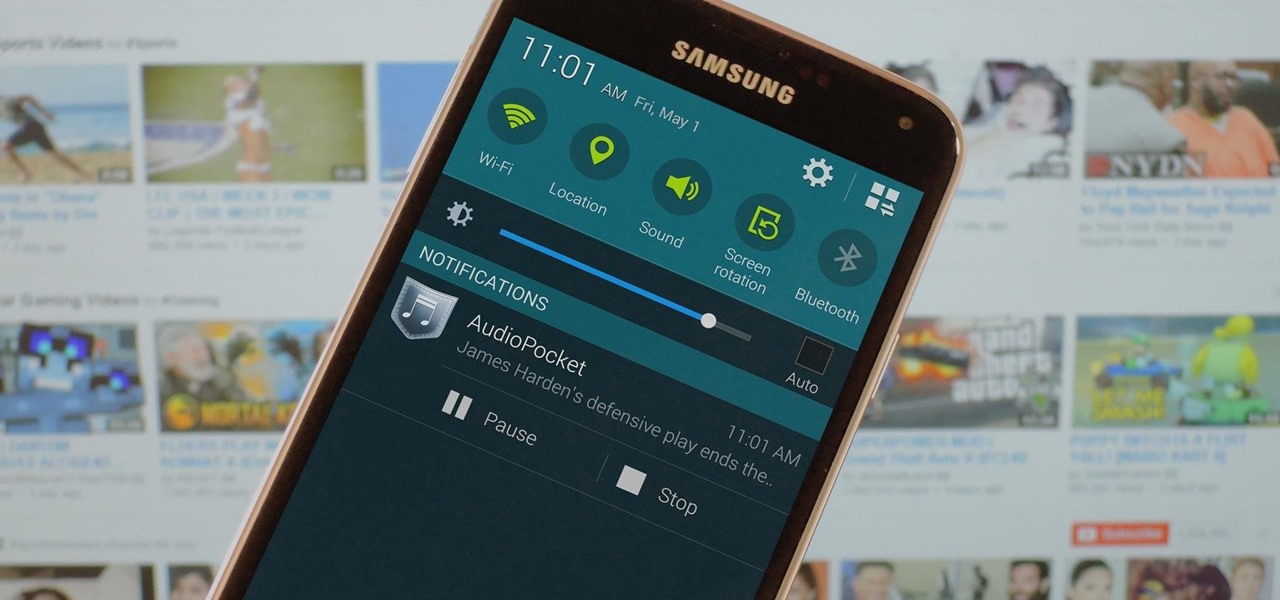
Over the years, we've covered many different methods for enabling background playback for YouTube videos on Android, but none have ever been as easy as this: Simply watch the videos with Firefox for Android, and they'll continue playing when you leave the app.

One of the major criticisms of virtual reality, and much modern technology in general, is the antisocial nature it creates. But vTime wants to overcome the isolating nature of VR headsets with a virtual hangout space for you and your friends.

Augmented reality (AR) generally exists through the lens of our smartphones as information layered on top of what the camera sees, but it doesn't have to. Developer Jon Cheng worked with an indoor climbing facility in Somerville, Massachussetts, called Brooklyn Boulders, to turn rock climbing into a real-world video game where participants compete in a time trial to hit virtual markers on the wall.

A lot more people are about to be able to use Android Auto. Google announced at I/O 2016 that you'll soon be able to use the app with only your phone, so you won't need a compatible car or third-party display unit. And if (or more likely, when) Google brings the app to iOS, Apple may lose the precious "infotainment" system battle very early in the game. The update isn't coming until later this year, but once it arrives, you'll be able to mount your phone and use Android Auto the same way that...

This is my first article on here, it's based off of a project that I'm working on at school which is on three ways to bypass windows user password's. If all goes as planned and you all would like I'll work on part two and part three and post them as soon as I can. I do have to give credit to Puppy Monkey Baby and The Defalt, both of whom are my classmates at college and have helped me with writing this article.

Welcome back, my budding hackers! In this series, I have been trying to familiarize you with the many features of the world's best framework for exploitation, hacking, and pentesting, Metasploit. There are so many features, and techniques for using those features, that few pentesters/hackers are aware of all of them.

Welcome back, my hacker novitiates! Often, to hack a website, we need to connect to and exploit a particular object within said website. It might be an admin panel or a subdirectory that is vulnerable to attack. The key, of course, is to find these objects, as they may be hidden.

Previously, you'd need to install the Google Cast extension to cast webpages from your Chrome web browser to your Chromecast-connected TV, but as of March 24th, you don't need it anymore. Casting now works natively in Google Chrome (which had been available in the Beta version for a few months), and you can activate the hidden feature right now.

Hello! This is my first post on this awesome website! I know that Windows exploits are less common than the more advanced hacks, but I found something I deem pretty cool and figured why not share it with you all. Alright, enough about me, lets begin.

According to the American Osteopathic Association, "1 in 5 teens has some form of hearing loss," and some experts believe it's because of an increase in headphones use. While I understand that music, movies, and video games help keep children preoccupied, there's no reason why they can't be entertained at a healthy hearing level.

In this article, we will explore the basics of radare2, a powerful package that comes with Kali. We are going to write a simple program, and then disassemble it, to see what is really doing in the processor.

Do you have a file (or many files) that, in the wrong hands, may cause you trouble? Don't worry about it, because I'll show you how to wipe it (or them) from your computer in order to leave no trace behind.

Welcome back, my amateur hackers! With Halloween right around the corner, I thought you could have a little fun with your newfound hacking skills using a hack that is guaranteed to freak out your boss, teacher, coworker, friend, etc.

ADB and Fastboot are probably the most essential tools for any Android aficionado. They can do everything from backing up your device to unlocking your bootloader with a few simple steps. This paves the way for many new tweaks and customizations that weren't possible before. The required platform works with the three most popular computer operating systems, too, which is good news for everyone.

Hello, ladies and gents! Today I will be discussing the fun and excitement of backdoor on an OSX system.

Imagine this scenario: You exploited a system using metasploit and you want to install a backdoor. You have a few options;

And we meet again Crackers! Welcome to my 7th post (Part-2), this tutorial will explain about some more basics of Batch Scripting, with C00L Scripts, which in turn will help you learn and understand better

Hi there, Crackers, Welcome to my 7th post (Part-1), this tutorial will explain about the basics of Batch Scripting.

When you think about it, YouTube may actually have one of the largest music collections on the planet. This is why, at $10 per month, Google's new YouTube Music Key subscription is a solid value for many users, especially with its inclusion of Google Play Music.

Welcome back, my neophyte hackers! In previous tutorials, we learned how to steal system tokens that we could use to access resources, how to use hashdump to pull password hashes from a local system, and how to grab password hashes from a local system and crack them.

Whether you drive a new or used car, discovering a new dent, scratch, or scuff mark can send you into a frustration spiral. While there are many DIY ways to deal with dents, scratches and scuff marks are trickier because using the wrong stuff could make your car's paint job look even worse.

CyanogenMod has been building upon open-source AOSP apps for many years now. They've made improvements to apps like the stock SMS client, the stock Audio Mixer, and a whole slew of others.

Just recently, Snapchat decided to implement a feature that it had long been lacking—the ability to play music and record a video at the same time. For those of us that are jailbroken, we've had this feature for some time, but now that everyone has the ability, how should you use it?

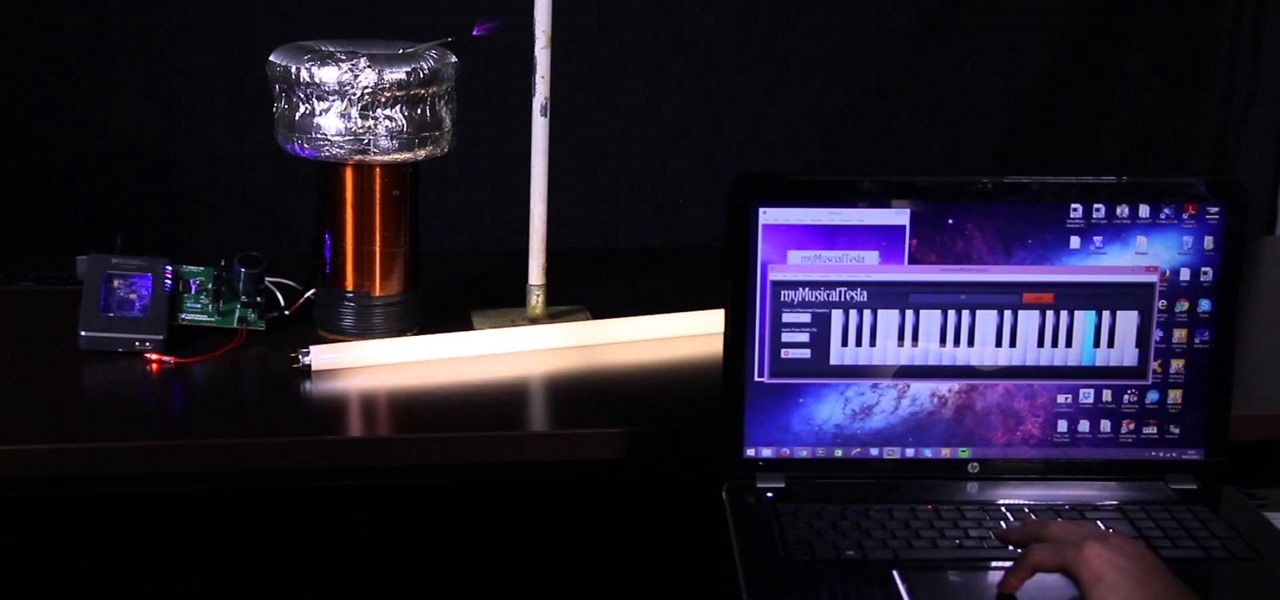
Video: . I made this Tesla Coil using the myRIO and LabVIEW. It uses electricity to play the music, which can be Star Wars, Harry Potter or even Hunger Games! The music is played by the spark heating the surrounding air (causing it to expand) then the spark turning off (causing the air to cool and contract). This expanding and contracting cause's longitudinal waves - or sound waves.

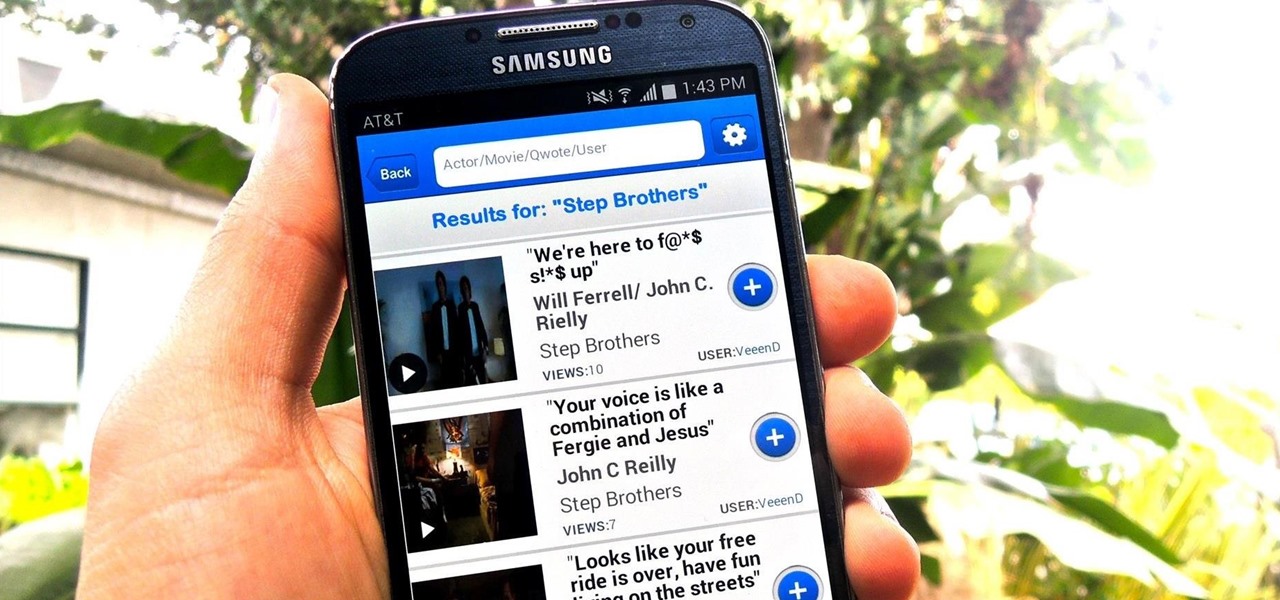
The Oscars are just around the corner, so it's the perfect time to remind people of your favorite movie moments, even if they're not exactly Oscar-worthy. But don't just settle on sending GIFs that don't include any of the fun audio, or resort to scouring YouTube for that one specific movie clip. Instead, take a look at Qwotes, a new mobile app from developer StudyUp.

No more carrying around heavy laptops and thousands of Linux Live CDs and USBs to always be ready for pentesting on the fly!

When Yosemite was released, a more detailed boot screen came to your Mac. So now, just like on Apple's mobile devices, you will see a loading bar telling you how far into the startup process you are. Apple also decided to add a black version of this boot screen to newer Macs, leaving those of us who purchased a computer before 2011 out of the loop.

You have to give Amazon credit where it's due. Aside from being a retail powerhouse, they're not averse to dipping their feet in new and sometimes strange areas. Take Fresh, the first major effort at bringing your local goods directly to you in same-day fashion. Or Amazon Dash, which aimed to make adding items to your cart a breeze by allowing for scanning goods or speaking them into a small, hand-held device. Along these lines, the company has now introduced an invite-only product, the Amazo...

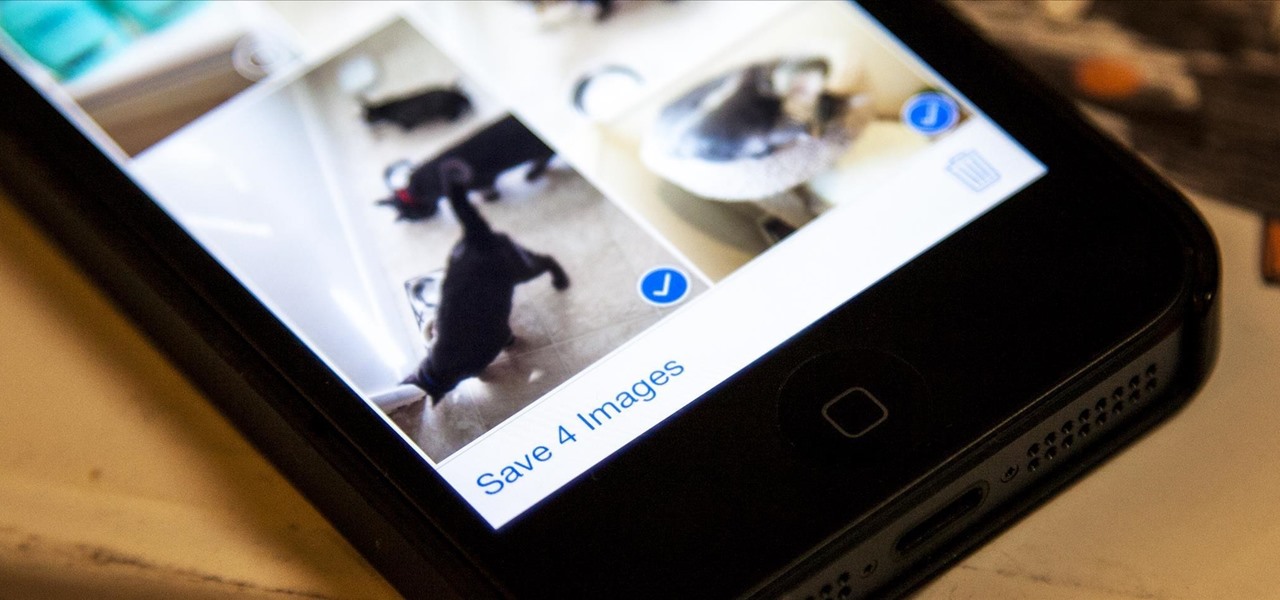
Viewing all of the attachments in a message thread within iOS 7 has never been particularly easy. To see every single picture and video dating back to the beginning of the conversation, you have to manually scroll through the entire conversation and refresh it until all of it appears on your screen. Depending on how long the conversation is, that could take some time.

Remember when MITMing people to pentest webapps and log-ins you had to fire Ettercap,Arpspoof, SSLstrip, then look for credentials in the captured packets?

Maybe it is narcissistic to take selfies, but it has become a socially accepted norm, no matter how stupid you might look doing it. Since so many people are seemingly in love with themselves and mobile photography, I thought it was about time to show you how to step up your selfie game.

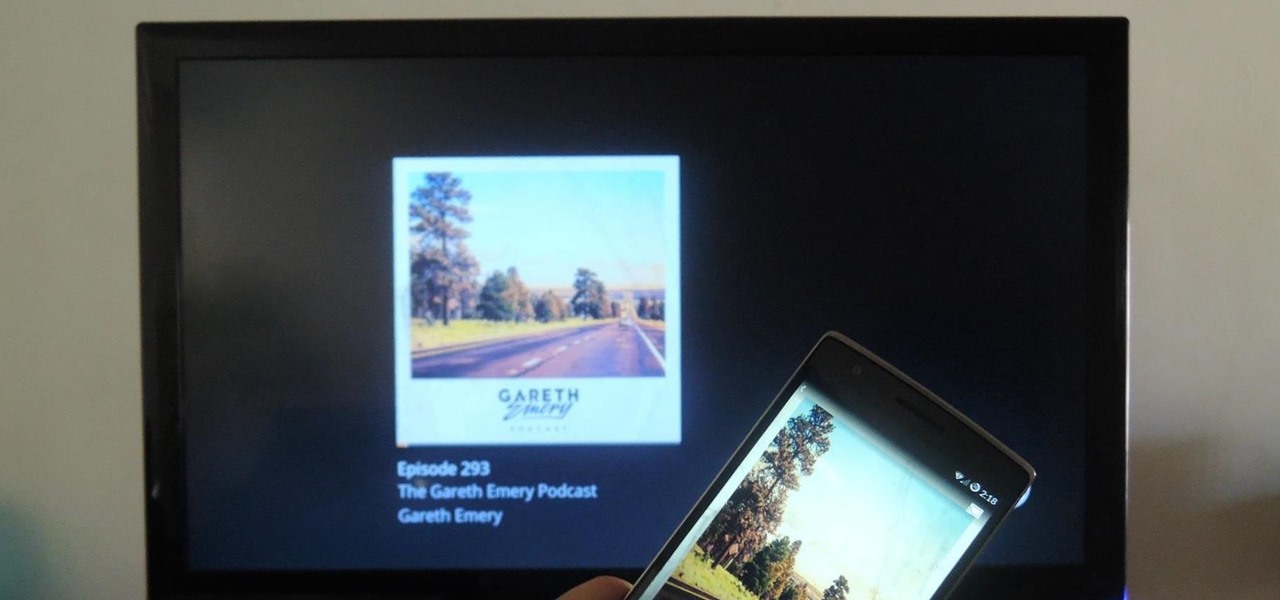
Podcasts have been around and popular for close to a decade now. For the uninitiated, podcasts are like radio shows that can be downloaded directly from the web and listened to on any device. Up until now, only paid apps allowed podcasts to be casted via Chromecast, but with the latest update to Xavier Guillemane's Podcast Addict, you can now do the same thing for free!

As I've said before, slowing down is not an option for me. At one point, I realized that there were plenty of files on my Mac that I didn't need any more, but too many to delete individually. In other cases, your Mac can be experiencing some major malfunctions: constant crashing, locked controls, slow boot times, missing files, etc.

Yesterday, I wanted to remove BackTrack from my system and install Kali, and at the same time didn't want to damage my Windows 7 or my hard drive. I searched a lot of articles, but almost all of them wanted me to have a backup Windows 7 CD, which I don't possess.

After a lengthy video and a series of leaks got us a good look at what we can expect from the new HTC One, codenamed M8, the guys over at GSMArena have brought it full circle.

Welcome back, my greenhorn hackers! Earlier in this series, I showed a you a couple of different ways of fingerprinting webservers. Probably the easiest way, is to use netcat and connect to port 80 and pull the webserver banner.