Though not as popular as Super Mario or Zelda, Konami's Contra nevertheless remains as one of the greatest titles that helped put Nintendo on the map. This retro shooter is set to make a comeback, and has been soft-launched in select Asian countries ahead of a worldwide release. Of course, you can try the game yourself right now, thanks to a nifty workaround.

Google and Apple are working to enable augmented reality content for the web, but startup 8th Wall has managed to launch a web AR platform that works on mobile browsers now.
Apple revealed three new iPhone models on Wednesday, Sept. 12, at its "Gather Round" event in Cupertino, as well as announced the official release date of iOS 12, its newest mobile operating system. If you missed it and want to watch the full event, here's how to do it on your computer, smartphone, or Apple TV.

Computer vision company Blippar has already dabbled with outdoor AR navigation, but now it wants to make it easier for people to make their way through indoor spaces with augmented reality.

I don't know about you, but nothing is more annoying than when my phone hits 15% and I'm nowhere near a charger. Not just because I know my phone will die soon, but until I reach a charger, I have to deal with the annoying low battery notification and LED light. Well, with Android 9.0 Pie, we finally can escape this.

Thanks to cloud storage's increasing accessibility, permanently losing photos is becoming less and less common. Still, if you accidentally delete a picture from your smartphone without first making a backup of some sort, that data is pretty much toast — unless we're talking about photos from WhatsApp.

Wi-Fi tools keep getting more and more accessible to beginners, and the LAZY script is a framework of serious penetration tools that can be explored easily from within it. This powerful and simple tool can be used for everything from installing new add-ons to grabbing a WPA handshake in a matter of seconds. Plus, it's easy to install, set up, and utilize.

Just a year after facing trade secret theft allegations from his former employer, ex-Meta Company employee Kevin Zhong and his new company are ready to ship the product that triggered the lawsuit.

The next big event Apple is holding is WWDC 2018, its Worldwide Developers Conference, is about to happen. If you want to see the first glimpse of iOS 12 for yourself, as well ARKit improvements, Apple Watch news, and maybe even some macOS announcements, here's how you can tune into the event right at home from your computer or mobile device.

Nearly one year after its announcement, AirPlay 2 has finally landed on iPhones everywhere. Not only can you easily control multiple speakers including Apple TVs and HomePods from your iPhone, but you can use Siri to help you get the job done. It's one of the iOS assistant's best features, and if you're running iOS 11.4 with a compatible speaker, you can try it out right now.

In this week of Snapchat lenses, there was a significant increase in ones that involve Marvel superheroes (the Infinity War effect), as well as ones with YouTubers. Classic sitcoms will also always do well, as evidenced by some of my previous roundups. Overall, lenses are doing well and only continuing to grow.

We watched the first piece of public-facing content Magic Leap has released so you don't have to, and, well, you didn't miss much.

Analysis of photographs and social connections can be a huge component of social engineering. Understanding who a person is, as well as who they know, can establish links within a company. This information could be used by hackers to execute elaborate social engineering attacks.

WhatsApp comes with a ton of great features that make it the go-to messaging app for millions of people around the world. Among these is the ingeniously simple Read Receipts that let you know your message has been viewed. If you want to read a message without alerting the sender, however, there are simple tricks you can perform to give yourself plausible deniability.

According to Indiana Jones, certain things belong in museums, but, thanks to augmented reality, you can now see some of the ancient treasures of the world in your own home via the Civilisations AR app from the BBC.

Coinhive, a JavaScript cryptocurrency miner, was reportedly discovered on the BlackBerry Mobile website. It was placed there by hackers who exploited a vulnerability in the site's e-commerce software that allowed them to anonymously mine cryptocurrency every time the website was viewed. There's no doubt Coinhive, an innovative mining method, is being abused and exploited by hackers in the wild.

Your home has walls for privacy, but Wi-Fi signals passing through them and can be detected up to a mile away with a directional Wi-Fi antenna and a direct line of sight. An amazing amount of information can be learned from this data, including when residents come and go, the manufacturer of all nearby wireless devices, and what on the network is in use at any given time.

A recent TED Talk makes a strong case for the healthcare industry to adopt augmented reality as a means to expanding access to surgical care across the globe.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

If CES 2018 is the starting gate for this year's race to release smartglasses, then Vuzix is already racing down the augmented reality track with its Blade smartglasses.

Format strings are a handy way for programmers to whip up a string from several variables. They are designed to save the programmer time and allow their code to look much cleaner. Unbeknownst to some programmers, format strings can also be used by an attacker to compromise their entire program. In this guide, we are going to look at just how we can use a format string to exploit a running program.

It finally happened. Magic Leap has given the world its first glimpse at its debut device, the Magic Leap One Creator Edition.

On Wednesday, Scope AR, makers of Remote AR, the augmented reality video conference calling and remote assistance solution, announced that the app is finally available for HoloLens. Next Reality had a chance to talk with the founder and CEO/CTO of Scope AR, Scott Montgomerie, inside this new version of Remote AR.

The public leaks of NSA tools and information have led to the release of previously secret zero-day exploits such as EternalBlue, which was used in the notorious WannaCry ransomware attack. Despite multiple patches being released, many users have failed to update their systems, so many devices are still vulnerable to these now-public attacks.

So, your grandmother finally wants to ditch her flip phone for a shiny new smartphone? Congratulations. But helping her get used to her new device, even when it's an iPhone, is no small task. Grandma mastered checking her email in late-2012 and just recently learned there's a thing called "Facebook." But we love grandma, and thanks to this guide, we can definitely make this happen for her.

Playlists are a vital feature for any music streaming service. For many, the ability to add and organize songs into the perfect order is a deciding factor in which streaming service to choose. The folks at Tidal (including owner Jay-Z) certainly recognize this, as they've provided users with the tools to not only create perfect playlists, but edit them as well.

Have you ever been listening to the radio and a song comes on that you can't identify? But you're driving, so you can't open your phone and use your favorite app to find the song's name. Well, with a feature called "Now Playing" on Pixel phones, Google has solved this problem.

The highly anticipated iPhone X is finally up for preorder, and it's been almost as exciting as we expected. With the dual cameras, bezel-less display, and high-tech facial recognition, there's almost nothing on the iPhone X that won't be liked. But around the same time as the iPhone X's announcement, another phone was revealed, and almost everyone seems to have forgotten about it. We didn't.

The dark web is an intimidating place for a newbie hacker, but it's a powerful tool once you've learned to navigate it safely. To help you out with that, this guide will cover some need-to-know information for traversing the dark corners of the internet while keeping your identity and data safe. (Hint: Using Tor is not enough.)

By default, iMovie for iPhone adds a dissolve (also called a crossfade) in between all of the video clips in your movie project's timeline, which is an effect that transitions gradually from the end of one clip to the beginning of another. However, iMovie does not add any beginning transitions to your first video clip or ending transitions to your last video clip. But that doesn't mean you can't.

Much like Xposed or Cydia, Magisk has an official repository that makes it easy to download root-level tweaks. These tweaks are called modules, and they can do anything from changing your emojis to installing high-level audio mods. But as it stands, a large number of Magisk modules are not hosted on the official repo just yet, so there are two primary ways to install them.

Unless you're a WhatsApp pro user, you may be surprised to know that there are text formatting options that you can apply to your messages. Markdown characters can help you emphasize certain words or phrases by making them italicized or bold, and it'll even let you cross out words and change the font. It's one of those nice touches that isn't available in most other messaging apps.

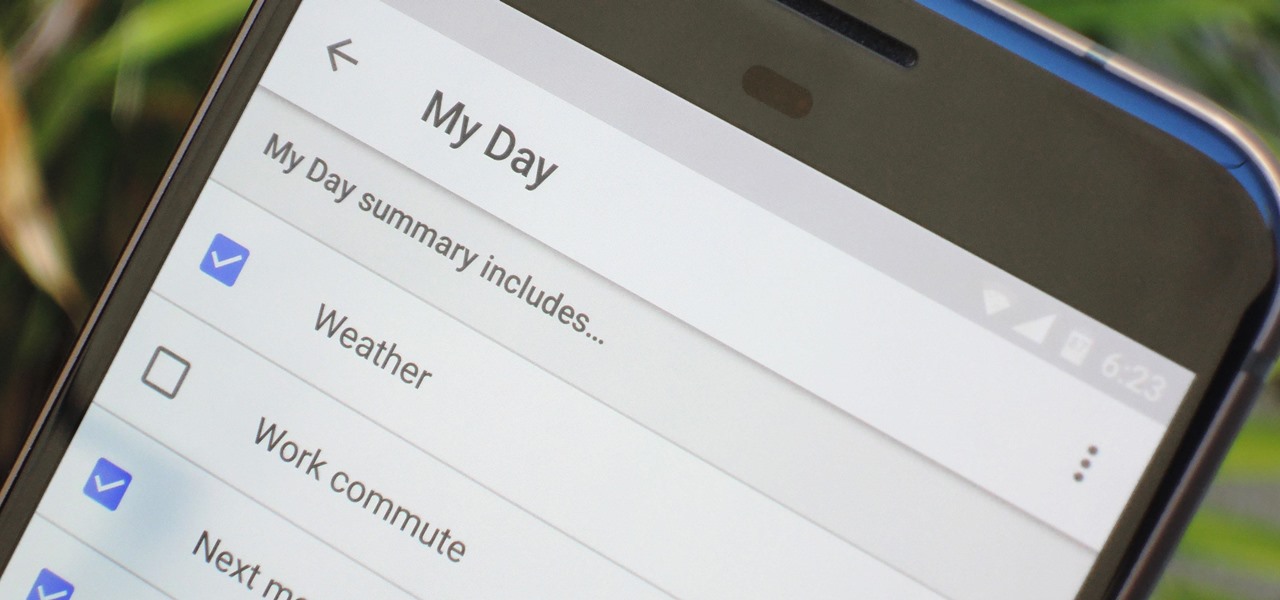
The Google Assistant comes in several different flavors. There's the baked-in Google app on Android, the dedicated Google Assistant app on iOS, and the Assistant-powered Google Home smart speaker. But no matter how you access it, your Assistant will only get better if you take some time to personalize things.

The augmented reality productivity app market for is a crowded space, so differentiation can be an advantage. Atheer is doing just that this week with their AiR Enterprise application.

When it comes to playing videos from your personal media library, VLC is hard to beat. But let's say you want to play videos from an Android device by connecting it to your TV — what app should you use then? VLC is still the answer, particularly once you've enabled its TV-friendly UI.

Most newer phones come with a grayscale mode that you can activate when you want to save some battery life. The way it works is simple: If your graphics chip only has to render elements in black and white instead of full 32-bit color, it won't consume as much power.

SoundCloud is a really interesting alternative to Spotify and Pandora in that it will never really give you the exact mainstream song that you want. If you're looking for new up-and-coming artists that are making some wonderful alternative remixes to mainstream music, then SoundCloud is the right music streaming app for you.

When the iPhone first came out, using them seemed like an impossibility to the visually impaired. Luckily, the iPhone now provides a multitude of resources to make sure that the visually impaired have accessibility to the phone.

Your Android phone could be listening to ultrasonic ad beacons behind your back. The unwelcome news comes year after app developer SilverPush promised to quit using its (creepy!) eavesdropping software.

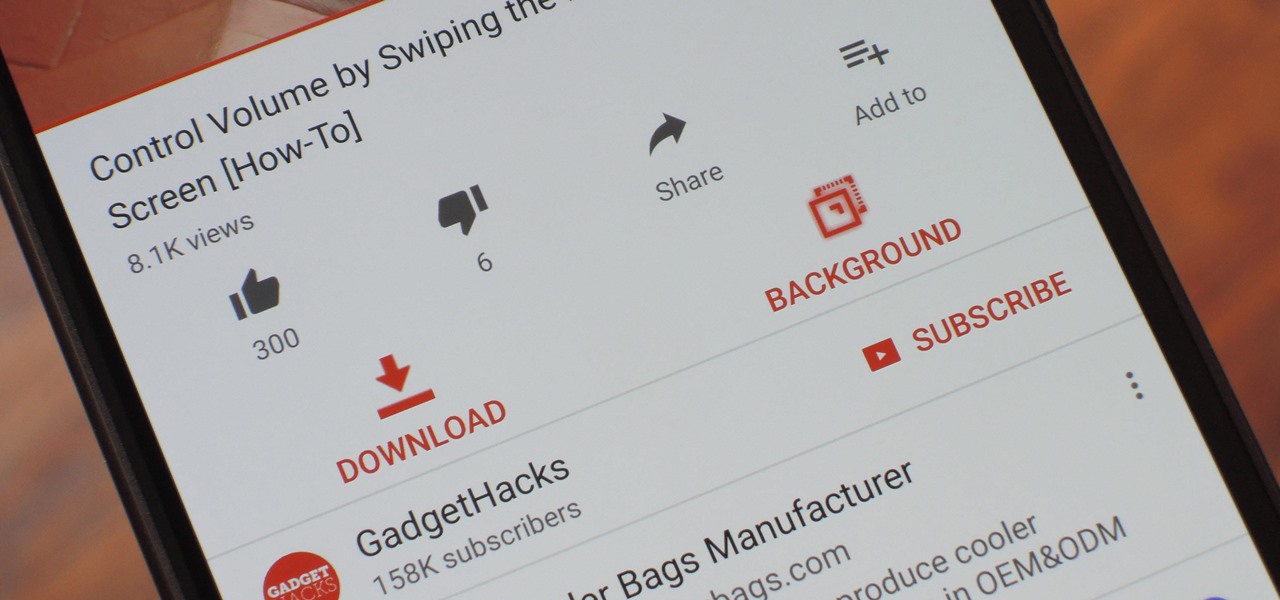
Recent launches of YouTube TV and YouTube Go created a bit of excitement on the web. Though the latter allows downloading, it doesn't allow background playback, as that would require a YouTube Red subscription for $10 a month. However, there's still a way to get both of these features without paying a dime.