In the last tutorial, we learned how to make functions and how they work on the high level. This time, we will take a peek under the hood again, stare deep into its soul and see its ugliness face to face to see how it works in the lower level.
Computer system authentication is critical to keeping systems safe from unwanted users, intruders, and abusers. Basically, authentication is the process of the potential user proving they are an authorized user.

ADB and Fastboot are probably the most essential tools for any Android aficionado. They can do everything from backing up your device to unlocking your bootloader with a few simple steps. This paves the way for many new tweaks and customizations that weren't possible before. The required platform works with the three most popular computer operating systems, too, which is good news for everyone.

Welcome back, my amateur hackers! As many of you know, Null Byte will soon be re-establishing its IRC channel. In preparation of that event, I want to show how to set up a secure IRC client with OTR, or Off the Record.

There is no greater food to master than steak. If you can make a steak that's only marginally better than your neighborhood Applebee's, you'll still have friends waiting outside your door for steak night. And if you can make steak as good as that expensive gourmet steakhouse you went to for your birthday? Well, your popularity is about to increase dramatically.

Given how much use it gets on a daily basis, the power button is always one of the first hardware features to call it quits on an Android phone or tablet. So if your power button is acting up, or you don't want it to, you can extend its lifetime by simply finding ways to use it less.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

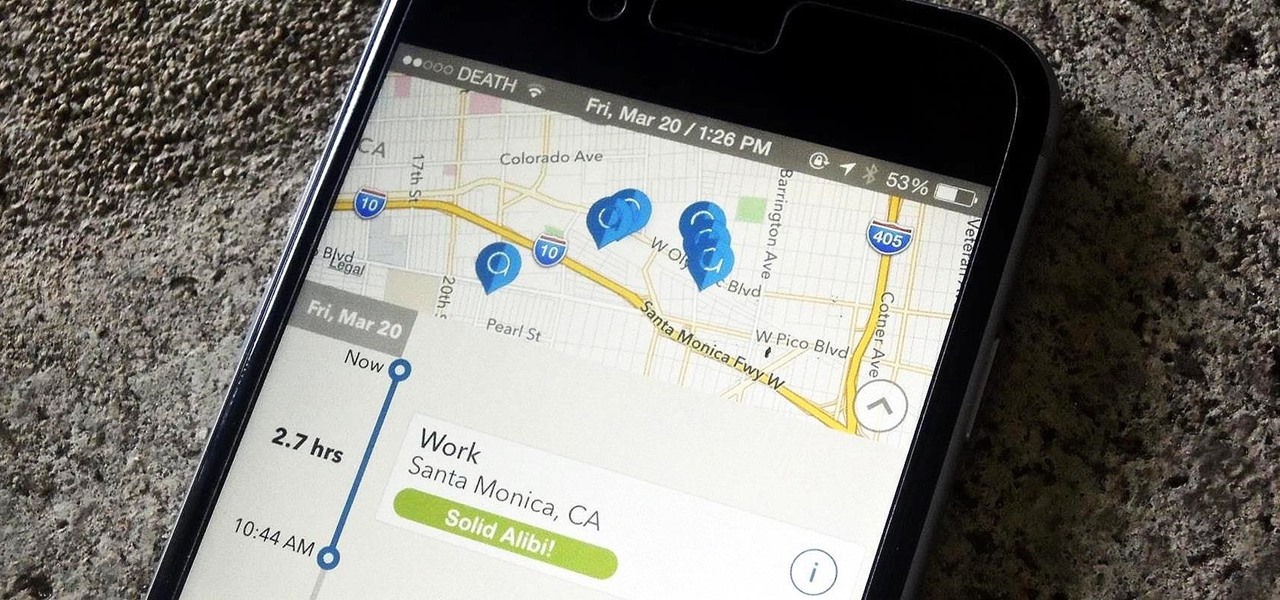
One of the biggest hits this past fall wasn't a movie, television show, or book—it was an unassuming podcast called Serial, which centered around an unsolved murder from 1999 of a high school student in Maryland.

The only mail I like getting comes in the form of an Amazon package, but when I go to my mailbox, it always ends up being a pile of credit card offers and catalogs I could never see myself ordering from. Those pieces of junk mail usually end up in the trash, which is horrible when you think about all the trees that had to get cut down in order to produce them.

Welcome back, my nascent hackers!

Many Nexus 6 owners, myself included, have already started to experience the dreaded burn-in issues that often come with AMOLED display technology. These displays are different than your typical LCD screen in that each pixel emits its own light instead of using a backlight, so this leaves AMOLED screens more susceptible to issues with dim or unresponsive pixels.

Seldom in recent history has a cyber security event caused so much media stir (maybe because it happened to a media company?) and international relations upheaval. Cyber security breaches seem to take place daily of major corporations, but the Sony hack seems to have captured the American imagination and, for that matter, the whole world's attention.

If you are having problems playing your sweep picking arpeggios fast and clean then you are not alone. Many guitarists have the same problem. I suffered from the same problem, years ago. In fact, playing sweep picking arpeggios with poor technique is one of the most common problems that I encounter with my guitar students. After helping them overcome these challenges I have discovered 2 different approaches to improving your sweep picking technique. The first will keep you frustrated with bad...

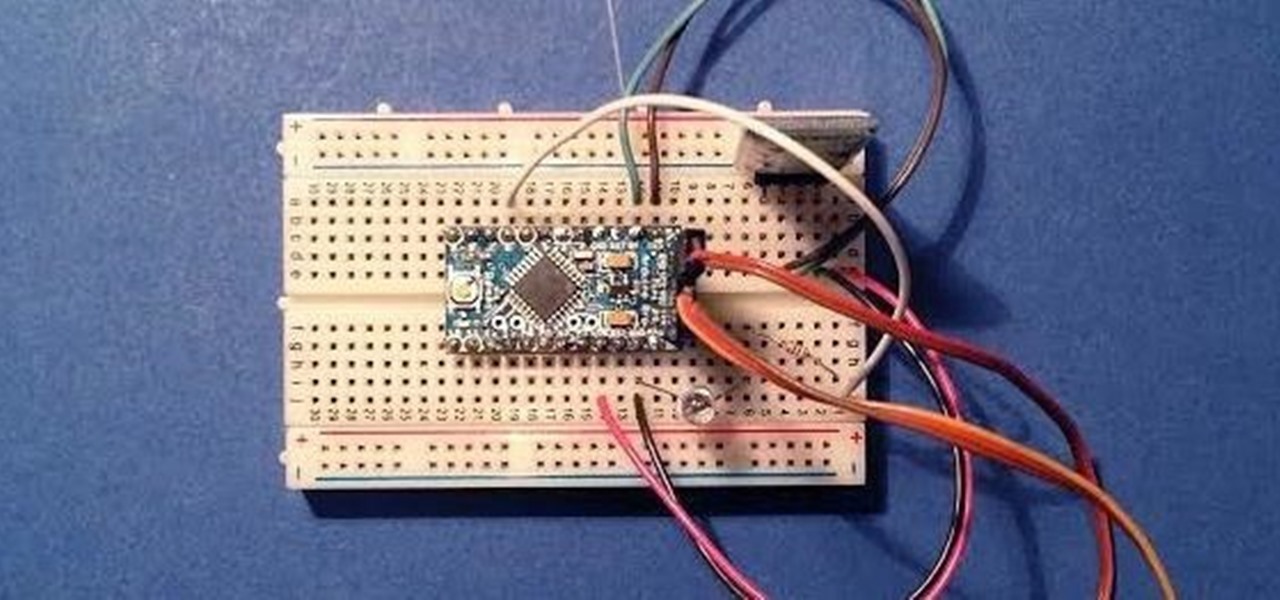
Since its creation, Arduino has been growing exponentially more popular as DIY enthusiasts and Makers alike realize its potential. As new versions of the device are released, many easy-to-use peripherals are showing up on the market also.

Welcome back, my hacker novitiates! When we are trying to find vulnerabilities in a website to attack, we need a solid web server vulnerability scanner. Internet-facing web apps can open enormous opportunities for us as they are often riven with vulnerabilities and can often offer an entire point to the internal network and resources.

There are a lot of manipulative people out there, but you don't have to let all of them push you around. It's time for the tables to turn.

While Google would like you to believe that Flash is incompatible on Android KitKat, there is a functional workaround that will get it up and running on your Samsung Galaxy Note 3's gorgeous screen in no time.

Tequila is a hard liquor that's often been misunderstood. Produced from the agave plant, this aged spirit has complex flavors that bloom the longer it's aged and can rival the finest scotch.

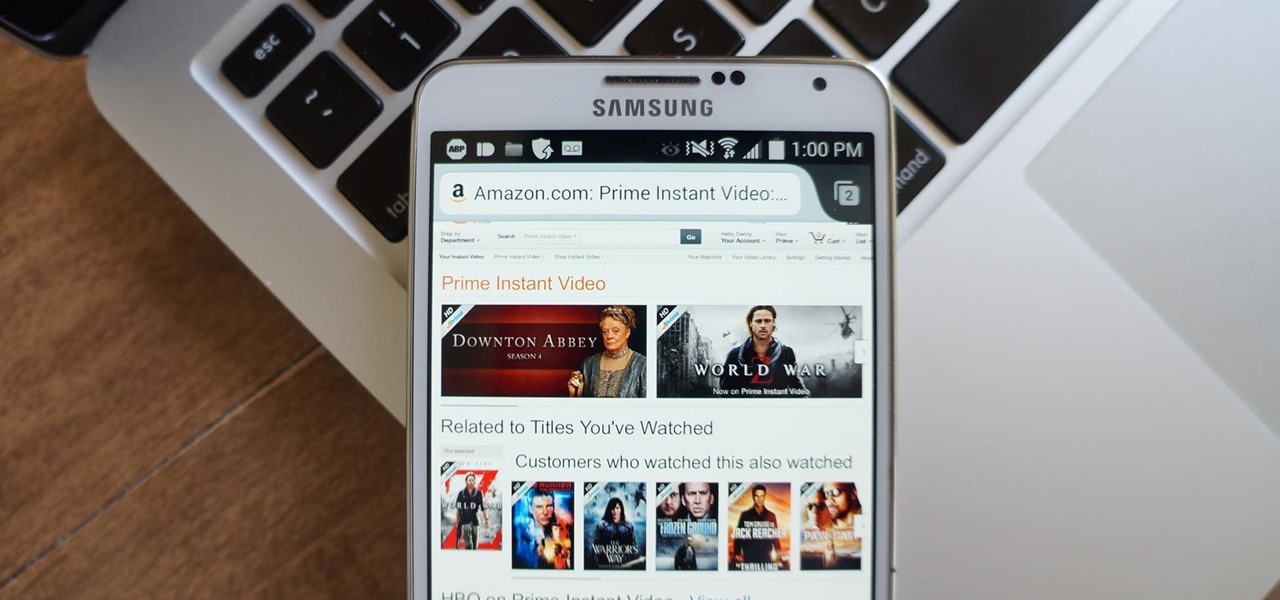
Reading is no longer a leisure activity—it's an on-the-go activity that requires speed and less attention. That's why speed reading apps are growing in popularity. As smartphones and tablets increasingly take over the traditional book market, reading skills need to be adjusted accordingly, so you can cram in 5 pages in-between texts and emails.

The new iOS 8 was just unveiled, and it looks pretty awesome. Apple showed off some of the enhancements and new features we can expect to receive in the fall at WWDC, and while not the huge facelift we saw with iOS 7, it does showcase what Apple does best—refinement. Continuity

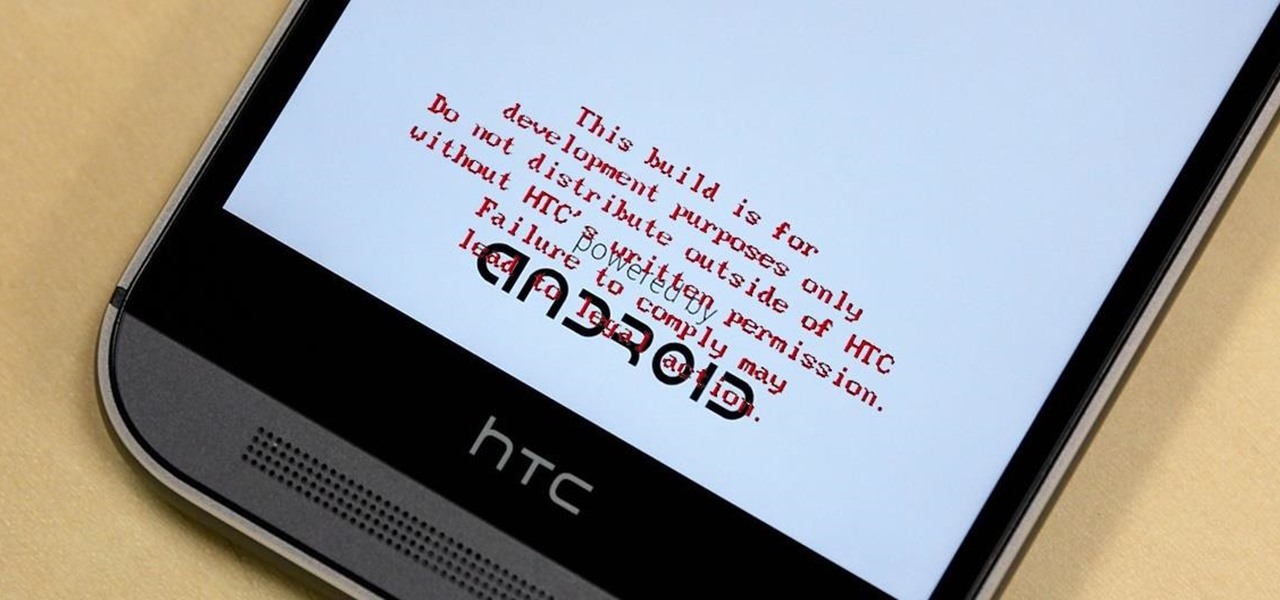
HTC thought it best to cover their own ass by placing a red warning whenever you start your device if you've unlocked your bootloader. While it may help them identify a tampered phone, it does not help you in any way. Luckily, XDA member santod040 created a modified HBOOT that removes the "This build is for development purposes only..." text for you. While this will modify HBOOT, it will not change your unlocked or S-Off status.

Welcome back, my aspiring hackers! Those of you who've been reading my tutorials for some time now know that I am adamant regarding the necessity of learning and using Linux to hack. There is no substitute, period.

Welcome back, my greenhorn hackers! Earlier in this series, I showed a you a couple of different ways of fingerprinting webservers. Probably the easiest way, is to use netcat and connect to port 80 and pull the webserver banner.

No matter how cool my 3D live wallpaper is, or how often my Google Now wallpapers automatically change, I always want more backgrounds. Zedge has made it easy for me to find new ones, and 500 Firepaper helps me keep my background lively with rotating wallpapers—but these aren't enough.

Welcome back, my greenhorn hackers! I've been writing these Linux tutorials in an attempt to fill the void in the education of some aspiring hackers into the Linux operating system. There is a lot to know, and in this tutorial, we'll look at Linux file permissions. Step 1: Checking Permissions

Ditching Sense (HTC's stock Android Launcher) is a great way to breathe new stock-like life into your HTC One smartphone without rooting, but even that has its limitations. If you really want the full Google experience, albeit with some extras, CyanogenMod has always been the go-to ROM. In effect, this will give you an experience similar to the Google Nexus or the new HTC One Google Edition.

Hello there, people. Today, I am going to show you how to extract the essence from a useful plant, using either alcohol or olive oil. This is how you take a plant and turn it into a useful (and preservable) medicine. For those of you who know nothing about herbal medicine, let me explain it for you in a nutshell...

There are lots of people who want to stay anonymous online, and lots of reasons they want to do this. Staying anonymous on the internet isn't easy, and it's probably possible to trace almost anyone with enough time and resources. A lot of people think that they're completely secure with just one method of cover. For example, a lot of people thought anyone using the Tor network was nearly untraceable, but then things like this often cast doubt on just how secure these networks are. Unless you ...

Before undertaking any electrical project, it is imperative that you know precisely what it is you're doing and to keep in mind that electricity can kill. With that said, this electrical tutorial presents a guide to identifying the switched live wire on a lighting circuit and also explains how to rewire a ceiling rose. For detailed, step-by-step instructions on completing this home project, take a look.

In Yoga Psychology, consciousness consists of body, mind, ego, intellect and self (the koshas). Rasas (emotional essences) are primarily a game of mind, but only become strong if the Ego identifies with them. Part of a Yoga class on Rasa Sadhana, the Tantric practice of emotional fasting.

Alopecia is also known as hair loss. he most common form of alopecia or hair loss that we see is alopecia areata. It usually shows itself as round patches of hair loss on the scalp, however, it can affect the facial hair and body hair. Learn some tips on how to slow and treat the loss of hair in this medical how-to video.

Rogaine is a popularly used produce for hair loss and regrowing hair. Rogaine is a topical form of minoxidil and its use on the scalp to help thicken the hair. Minoxidil was initially use for blood pressure medication and has discovered the patients that took minoxidil had hair growth on their bodies. Learn more about Rogaine and hair loss in this how-to video on beautification treatments.

Yes, you can have your cake and eat it too. There are a lot of light or nutritional alternatives to a lot of the desserts that we commonly use or eat. Saving room for dessert is a must for adding any treat to the end of a healthy meal. Learn some tips for buying dessert foods in this nutrition how-to video.

If you loved The Da Vinci Code by Dan Brown, then listen up— there's been a new discovery found hidden within Leonardo da Vinci's most famous painting— the Mona Lisa.

After performing a Vital Signs examination on a patient, usually, the next step for a doctor is performing the HEENT.

There's an iOS feature that benefits many users, but it's absolutely vital if you wear AirPods or other headphones models connected to your iPhone. A large number of iPhone users don't even know about it, especially since it's disabled by default and hidden deep in the system settings.

If you've recently built a Wi-Fi spy camera out of an ESP32-CAM, you can use it for a variety of things. A baby monitor at night, a security camera for catching package thieves, a hidden video streamer to catch someone going somewhere they shouldn't be — you could use it for pretty much anything. Best of all, this inexpensive camera module can perform facial detection and facial recognition!

Because of the way Google Play works, Android has a "bad app" problem. Google allows any developer to upload an app to the Play Store, regardless of if it works, how it looks, or whether or not it can harm users. Malware scanning happens primarily after apps are uploaded, and though Google has recently taken steps to safeguard users with its Play Protect program, you don't have to depend on them.

Throughout this NR50 series, we have talked about the incredible growth the augmented and mixed reality space has seen in the last year. More devices, software, developers, and use-cases seem to arrive daily. For this growth to have occurred, it took the work of many people, from many different backgrounds and skill sets — and Next Reality wants to recognize them for all that they have done and are doing.

Remember those old vinyl records? Remember jumping on the 8-track bandwagon? Switching over to cassette tapes? How much money you spent converting your music collection to compact discs? To MP3s?