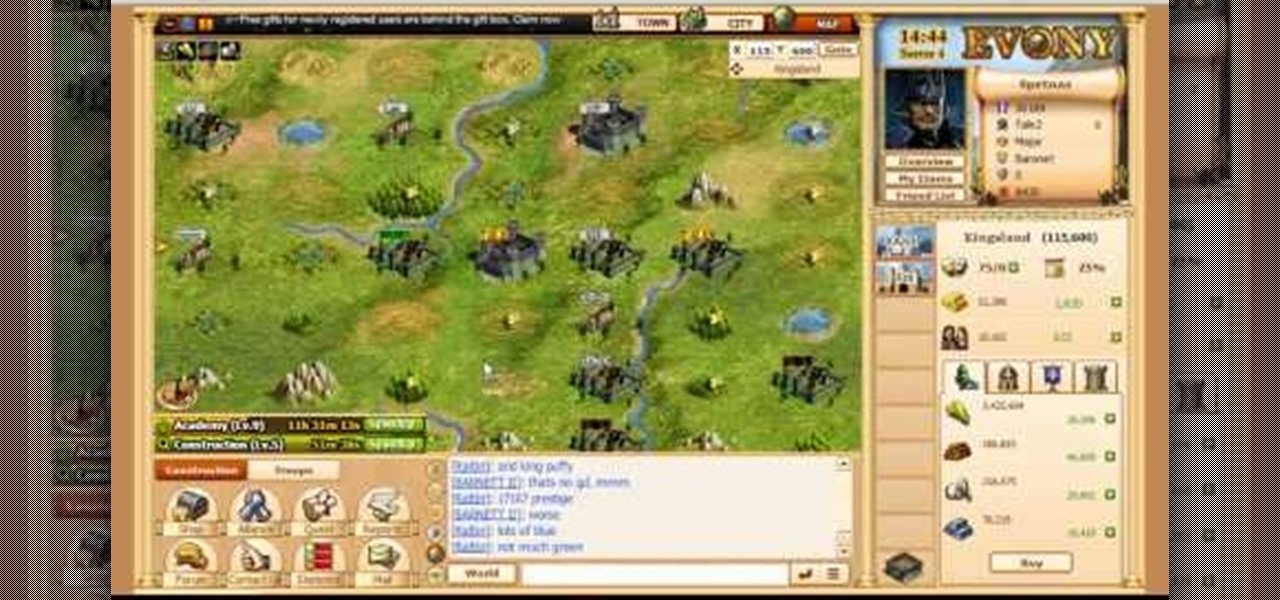
Learn everything you could possibly want to know about the internet, multiplayer game Evony with tutorials from EvonyTutorials. Watch this video tutorial to learn how to play Evony - military domination. See exactly what the game Evony is!

Complex shell scripts can be implanted into photo metadata and later used to exploit a MacBook. In addition to obfuscating the true nature of an attack, this technique can be used to evade network firewalls as well as vigilant sysadmins.

Hacker's are always looking for new ways to exploit systems and exfiltrate passwords, even in hashed form. Sophisticated brute-force attacks powered by high-end GPUs can perform millions of password attempts per second. But Ubuntu and Debian users aren't completely helpless. There are ways to harden the hashed password to better defend against Hashcat attacks.
Smartphones and laptops are constantly sending Wi-Fi radio signals, and many of these signals can be used to track us. In this guide, we'll program a cheap IoT device in Arduino to create hundreds of fake networks with common names; This will cause nearby devices to reveal their real trackable MAC address, and it can even let an attacker take over the phone's data connection with no warning.

Leaked databases get passed around the internet and no one seems to notice. We've become desensitized to the data breaches that occur on a daily basis because it happens so frequently. Join me as I illustrate why reusing passwords across multiple websites is a truly awful practice — and compromise hundreds of social media accounts in the process.

After a hacker has configured Metasploit on a remote private server, created a resource script for automation, and created a simple payload, he or she can begin the process of remotely controlling someone's Windows 10 computer with just a few moments of physical access — even if the computer is off.

Using just a small sticky note, we can trigger a chain of events that ultimately results in complete access to someone's entire digital and personal life.

JavaScript is one of the most common languages used on the web. It can automate and animate website components, manage website content, and carry out many other useful functions from within a webpage. The scripting language also has many functions which can be used for malicious purposes, including stealing a user's cookies containing passwords and other information.

Technology and nature, typically thought of as opposites, are coming together in a new London exhibit.

The Cloud Security Alliance (CSA), a leading IT trade association, has published its first report on risks and recommendations for connected-vehicle security, ahead of when driverless cars are about to see volume production in the near future.

With the Game Developers Conference (GDC) in San Fransisco just a few weeks away, Microsoft Senior Program Manager Vlad Kolesnikov has announced via Channel9 (Microsoft's developer news outlet) that not only will new low-cost virtual reality headsets be coming in March to developers, but that they will be at GDC, too.

You may not know what HTTP is exactly, but you definitely know that every single website you visit starts with it. Without the Hypertext Transfer Protocol, there'd be no easy way to view all the text, media, and data that you're able to see online. However, all communication between your browser and a website are unencrypted, which means it can be eavesdropped on.

Hello fellows nullbyters, first of i will start saying that im addicted to this community, i feel the challenge growing up so fast, all the newbies, amateurs,advanced and professionals hackers around trying their best to help the community, badly but we got some script-kids too but anyway, today we are going to learn how to install and use clanAV in kali linux.. INTRODUCTION

Those of you who have been a part of the Null Byte community for even a short while know that I sincerely and firmly believe that hacking is the most important skill set of the future.

Welcome Back !! TheGeeks. SQL Injection (SQLI) Part-1

When security firm Zimperium discovered Android's biggest security risk in years, it sent shock waves through the ecosystem. As a result, Google, LG, and even Samsung decided to change the way they issue updates to their devices, by pledging to release monthly security patches to plug up loopholes exactly like this one. Yeah, it's that big of a deal.

Who doesn't experience food cravings? Whether you're trying to adhere to a strict diet, or simply hoping to avoid sugary, fatty foods, curbing cravings can feel like a monumental task.

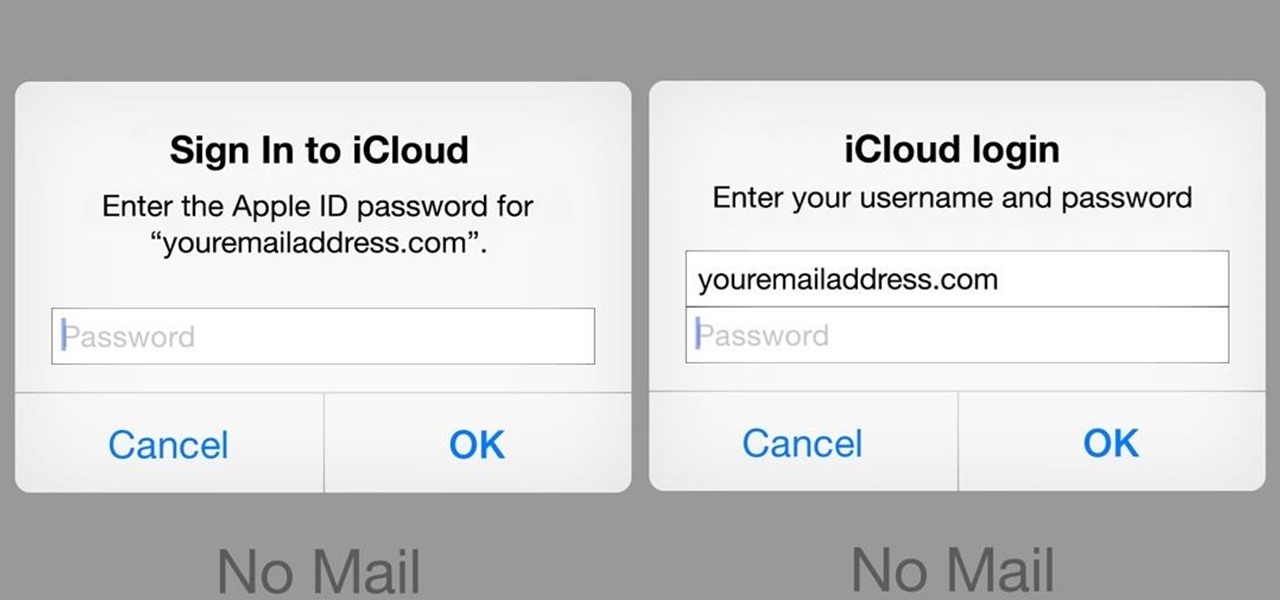
A recently discovered bug in iOS 8's Mail app by Jan Soucek can allow the maliciously-minded to quite easily phish your iCloud password without you ever thinking something has gone awry. Using a bug that allows remote HTML content to be loaded in place of the original email content, unsuspecting victims would be prompted for iCloud credentials in a popup that resembles the native one found on iOS.

It's been a while when the major web browsers first introduced HTTP Strict Transport Security, which made it more difficult to carry Man In The Middle (MITM) attacks (except IE, as always, which will support HSTS since Windows 10, surprised?).

Although this century is still young, with little fanfare we may have just witnessed the "Hack of the Century." AV software developer Kaspersky of Russia recently announced that they found that some hackers have stolen over $1 billion from banks around the world!

Hi! Let me get started on this subject as it is a very "touchy" subject. We all want to "hack" these days, and that's logical. Te be real honest here, i was inspired once by the words someone from the Null byte community said. In the (near) future, wars will be ended by computers and not a nuclear missile. That's something i really do believe in. But let us take a defensive measure instead of the offensive one. Sure, Full frontal bryte forcing is an option, but when it'll come that far we'll ...

Incorporating features such as CarPlay, UI enhancements such as the new call screen, and several bug fixes, iOS 7.1 was the first major update to Apple's operating system since iOS 7 was released in June of last year.

Welcome back, my newbie hackers! Hackers often are associated with clandestine and illegal activity, but that is not necessarily always the case. Hackers are increasingly being used and employed for law enforcement, national security, and other legitimate purposes. In this installment, we will look at how a single hacker could save the world from nuclear annihilation.

Wall framing. How to frame a wall. Whether you're re-sheeting an old wall or building a new timber frame wall, before you install the plasterboard or drywall, take the opportunity to have a really good think about what services or insulation qualities you might want to have in that space. There are issues to consider like electrical, plumbing, noggins for wall fixtures and insulation.

In this video, we learn how to use Ableton Live 8: Quantizing audio. To find the bars you want to use, find the up and down arrow keys. These will jump the loops back and forth based on the width of the loop race itself. Press play to search around for the best four bar section in your music. Now, set your first attack in your loop by zooming in on the hit. Hover over the audio and create a warp marker to drag from each of the bars. Label it as the beginning of your clip to the end, then save...

In this video tutorial, viewers learn how to bow the Erhu. When playing this instrument, keep the shoulders and both arms relaxed. The elbow moves the arm, the arm moves the wrist, the wrist moves the fingers and the fingers move the bow. There is a slight twitch of the wrist on attack of each stroke. The only pressure point is where you hold the bow. Practice bowing the whole length of the bow. Practice with various speeds. This video will benefit those viewers who are interested in playing ...

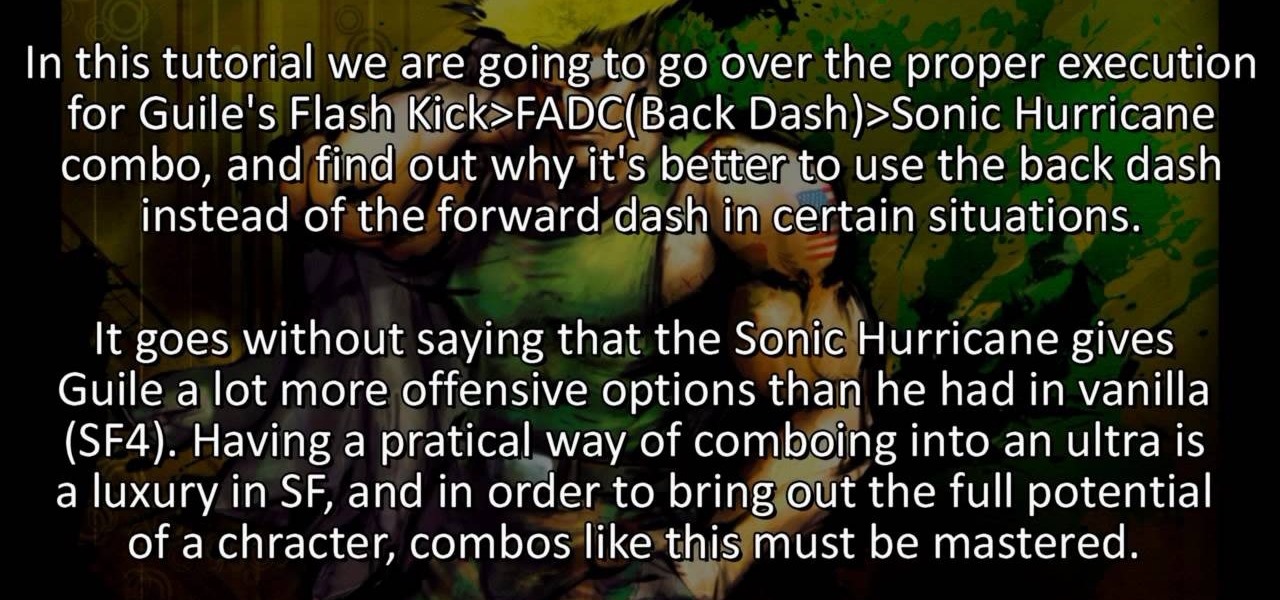
This might be the single best combo that Guile can do in Street Fighter 4, and you're gonna learn how to do it. It's a Flash Kick - Focus Attack Dash - Sonic Hurricane combo that is devastating and can be done quite fast with practice. Which is what you should be doing as soon as this video is over and you can get to the arcade. Unless you're watching this on your phone AT an arcade, you 21st century digital person.

Attention achievement hunters! In this next tutorial, you'll be finding out how to get the Crackshot achievement in the game Dead Space for the Xbox 360. To get it, you must achieve a perect score in the Shooting Gallery in the game.

Burgers are beloved by most Americans for the fact that there's a burger style for every person. Some people like their burgers without meat, some like them without cheese, and some want three times the meat for three times the juicy, heart attack goodness.

"Blah, I vant to suck your blood!" One of the most common and overused vampire lines out there! But who could blame them? Vampires are pretty interesting and cool creatures that have been around for centuries. What makes them so unique and different is that instead of preying on victims during the day, they use the night to hunt and attack its prey, feeding off their fear of the dark. Well at least in movies. In real life vampires don't exist. But it doesn't mean you can't dress or look like ...

Show your fellow dance warriors what you're made of! Perform an impressive hop on a handstand trick with help from this free lesson. In order to hop on a handstand, it's important to first know how to do a handstand, as well as what muscles to use. Discover how to use the shoulders and arms to hop on a handstand with help from this expert: CJ Kendricks is an instructor, entertainer and artist who has attacked the stage at the Dirty South Awards. Learn more dance moves from this expert by sear...

The Crip walk, or C-walk, is a popular west coast dance move that requires a great deal of balance, buoyancy and switching of the feet. Learn about different foot exchanges that are used to C-walk with help from this free lesson given by an expert.

All you break dance hopefuls out there, this free lesson is for you! In this break dancing tutorial, learn how to do the six step. Find out how to do floor work in break dancing and how to make it or fake it to look like a pro!

Throw yourself into the world of hip-hop with help from this free lesson. Hip-hop foot work can be broken down into simplified movements or moves that are abstract and contrived to the music being used. Find out how to do a hip-hop combination with help from this free lesson.

You want to dance like Usher? Usher is a performer who draws much of his influence from Michael Jackson, and one of his signature moves is a variation of the air walk. Find out how to pull off this moonwalk variation with help from this free dance lesson.

Looking to enter the world of the pop & lock? Learn the difference between the two with help from this free lesson. In dance, popping is all about popping the body by flexing muscles and grinding shoulders, while locking is a way to cut off flowing movements.

Looking to break into the break dancing world? In this video, learn some easy moves in break dancing with start with top rock basics, such as stepping out with the right foot, crossing the arms, crossing the left foot in front and opening the arms. Add flair to these dance floor friendly moves, with help from this free lesson.

This video answers some questions on how to identify some of the problems that occur in vegetable gardens: for example, if there are missing leaves on your tomato plant, then it is an indication that they are being eaten by something. In some cases, this pest is the Tomato Hornworm. The Mosaic Virus and Curly Top and Tomato Spotted Wilt also attacks tomato plants.

In this video tutorial, learn how to get auto tune, or the t-pain vocal effect, in Audacity using gsnap. To get the GSNAP (GSnap/Grymmjack skin), go here.

For Infinity Exists Full Disclosure's first Website Hacking episode, we demonstrate how to exploit a security vulnerability occurring in a website's database to extract password hashes. Sql (Structured Query Language) is a computer language designed for the retrieval and management of data in a system's database. The Attack, known as Sql Injection, manipulates Sql statements before they are sent to the Sql Server, allowing the Attacker to create, change, or retrieve data stored in the database.