
How To: Program a blackjack card counter with VB.Net
A VB.Net 2008 tutorial on how to make a program that can count cards in a blackjack game.


A VB.Net 2008 tutorial on how to make a program that can count cards in a blackjack game.

iMovie is the basic video editing software on MAC computers, the iPod Touch 4th generation, and the iPad 2. If you're new to film editing or just new to the program in general, this iMovie tutorial is a great introductory course to the program.
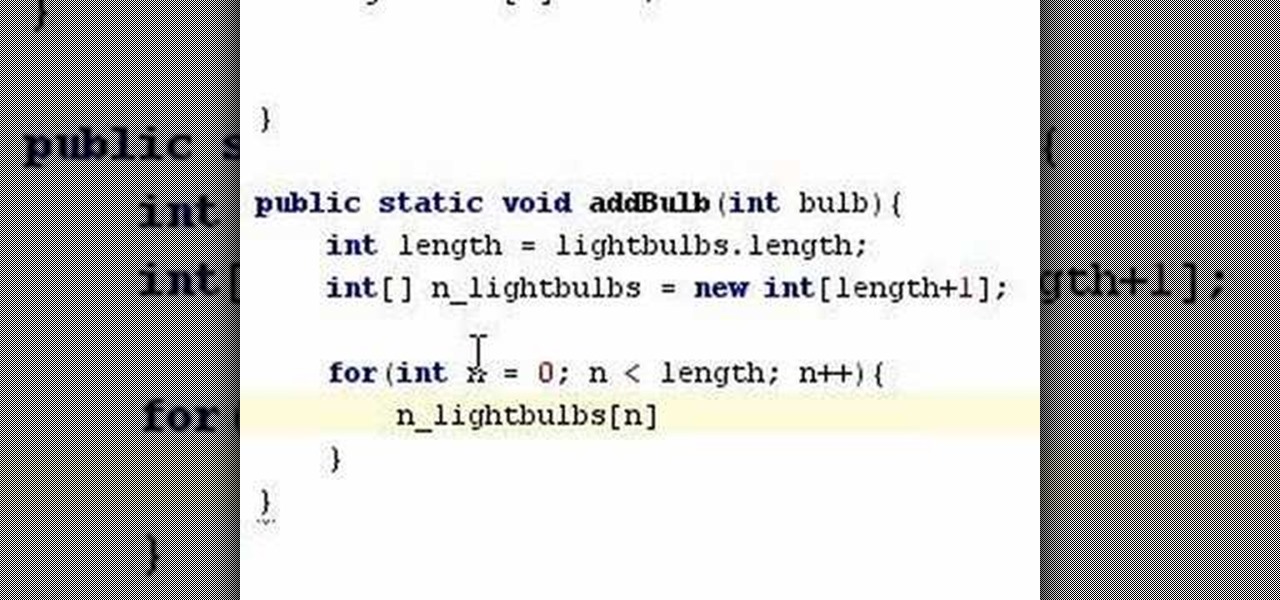
A tutorial on how to unroll and append elements to an array when programming in Java.

Learn to program If & Switch Statements in Java. This tutorial uses Java 1.6 with NetBeans 5.5.1 beta
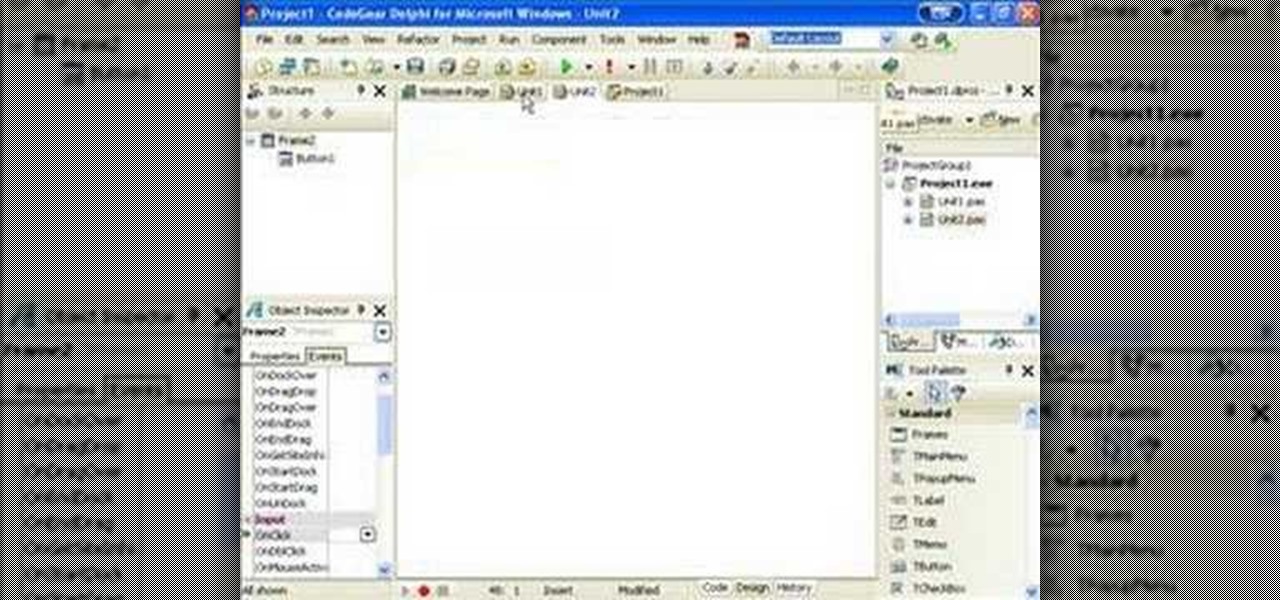
Delphi controls have an owner and parent property, find out what the difference is and how to use them when programming in Delphi.

You can connect your Nintendo Wii Wiimote to your PC using GlovePie input emulation software and a bluetooth connection. Learn how to program your PC to detect motion from dual input the Wiimote using GlovePie. You'll be able to connect two Wiimotes to your PC.

In this tutorial you will see how to use Jimmy's speed math program that he wrote in Flash. A download to the program is included. This is a GREAT way to help your kids or students (or maybe adults?) get better at math.

Microsoft Excel is one of the most powerful programs for modern businesses. By allowing you to manage, sort, and analyze large collections of data, Excel provides an essential service for any company interested in using the power of data science to its advantage.

Augmented reality gaming pioneer and Pokémon GO mastermind Niantic is putting the pieces on the gameboard to prepare developers and gamers for the launch of its AR cloud platform.

While MacOS computers have been spared from some of the most famous malware attacks, there is no shortage of malicious programs written for them. To keep your computer safe from some of the most common types of malware, we'll check out two free tools. These tools can automatically detect ransomware encrypting your files and watch for unauthorized access to your microphone and camera.

With $100 million in grant funding already available to developers via its MegaGrants program, Epic Games is sweetening the pot with some gear for Magic Leap developers.

Ten days after Magic Leap declared that it had selected the winners of its Independent Creators Program, the company has officially released an almost full list of grant recipients.

Format strings are a handy way for programmers to whip up a string from several variables. They are designed to save the programmer time and allow their code to look much cleaner. Unbeknownst to some programmers, format strings can also be used by an attacker to compromise their entire program. In this guide, we are going to look at just how we can use a format string to exploit a running program.

Being able to write your own hacking tools is what separates the script kiddies from the legendary hackers. While this can take many forms, one of the most coveted skills in hacking is the ability to dig through the binary files of a program and identify vulnerabilities at the lowest level. This is referred to as binary exploitation, and today we're going to check out a tool known as Protostar.
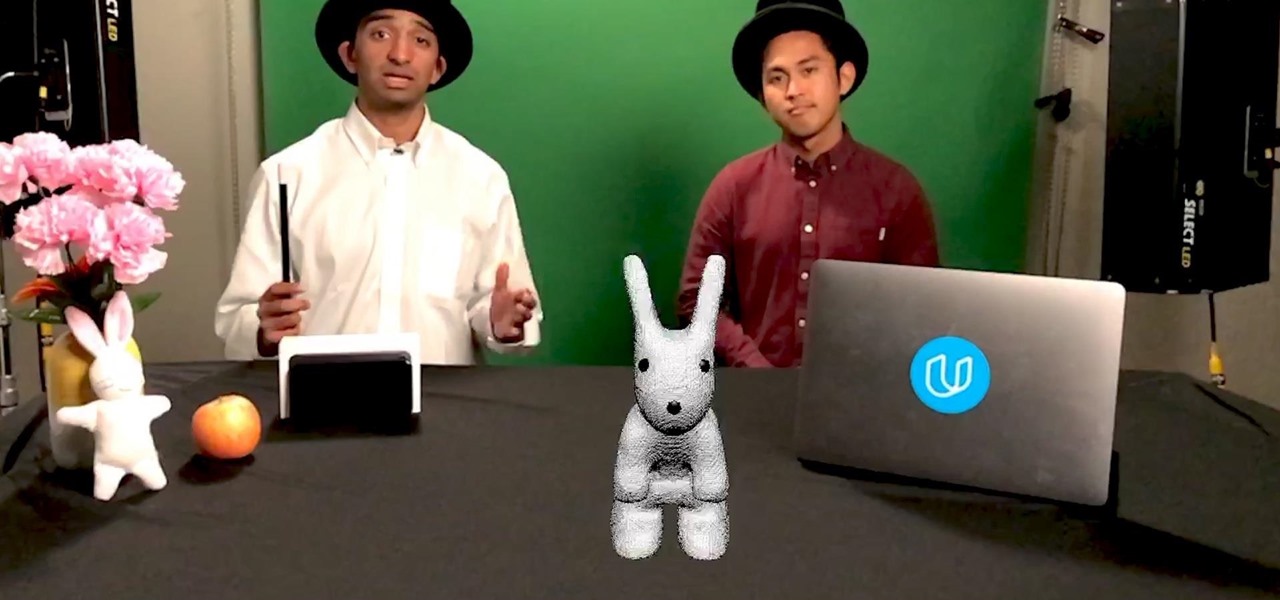
As demand for AR and VR developers continues to increase, particularly with the advent of Apple's ARKit platform, Unity has partnered with online learning company Udacity to help developers sharpen their skills for these jobs.

Google just bought a huge chunk of HTC for $1.1 billion. They're bringing in around 2,000 employees, mostly from the hardware division, and these folks will presumably work under hardware chief Rick Osterloh. There's a massive patent portfolio involved, too, so stop me if you've heard this before — Motorola, anyone?

The status of Uber's driverless program remains a big unknown amid the company's recent woes, but a reported multibillion-dollar shot in the arm by Japanese tech giant Softbank could change all that.

For companies wary of the temperature, PTC just made it easier for them to dip their toes in the waters of augmented reality.
Earlier this year, Google rolled out the first developer preview build of Android O. The new version added tons of cool features, but the downside was the fact that you needed to use Fastboot to manually install the update if you wanted to try it out. Thankfully, things just got a lot easier.

If you want to make some money from catching bugs and are sick of pentesting Facebook, Google, and Microsoft's products, Uber may be your new favorite playground.
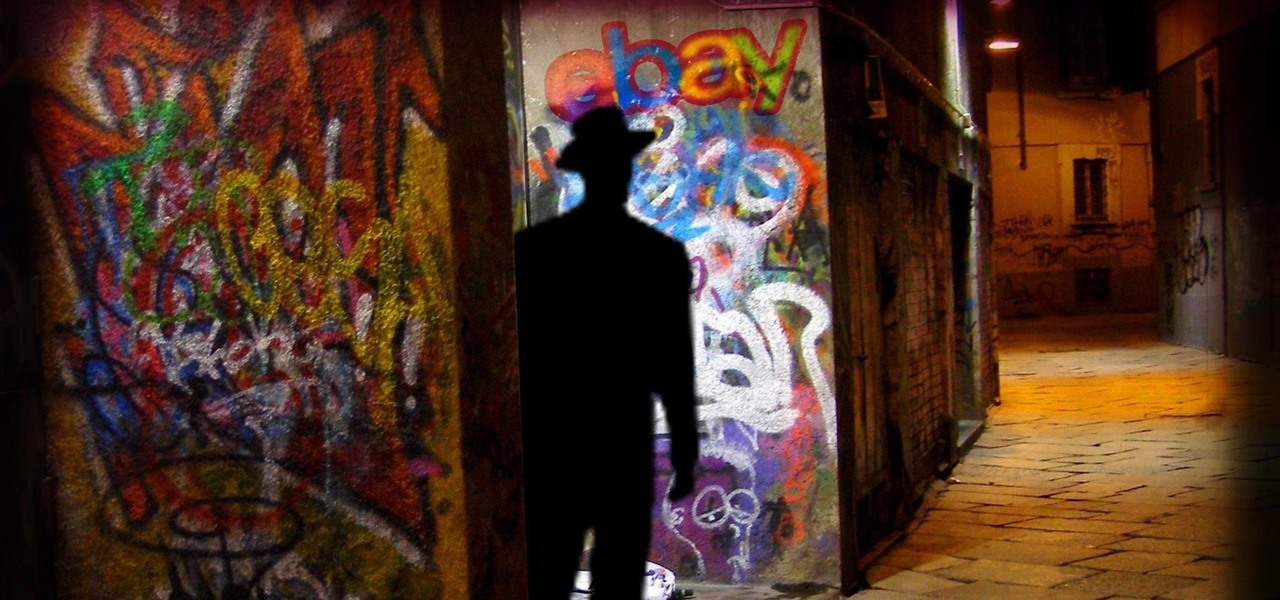
Researchers have discovered a "severe vulnerability" that allows attackers to use eBay to distribute malware, and the online auction company has no plans to fix the problem.

How's it goin'? In this tutorial, we will learn about the security issues of the popen and system functions. I've seen a few people attempting to run command line utilities or whatever it is they require with calls to these two functions but may not know the security implications which come along with it. I will show you using an example from the wargame IO Smash The Stack.

In many programs on Linux, you'll come across programs which allow you to specify additional arguments instead of just simply running the program by itself. If you've used the Kali distribution, I'm more than certain you'll have come across these with the command line tools, else if you have been following these tutorials, we have already come across three tools which also use the same technique, i.e. gcc, gdb and wc. How do we do this with C? Let's find out.

Welcome back, reader! In this tutorial, we will be covering our first program! So let's get to it. We all know the unspoken tradition of the first program when learning a language and of course, here we will respect and complete it. Fire up your favorite text editor (be it vim, emacs, gedit, it's all the same to me, no h8) and try to keep up.

This is my first ever how-to so I apologize in advance for any grammar mistakes or spelling errors. Introduction
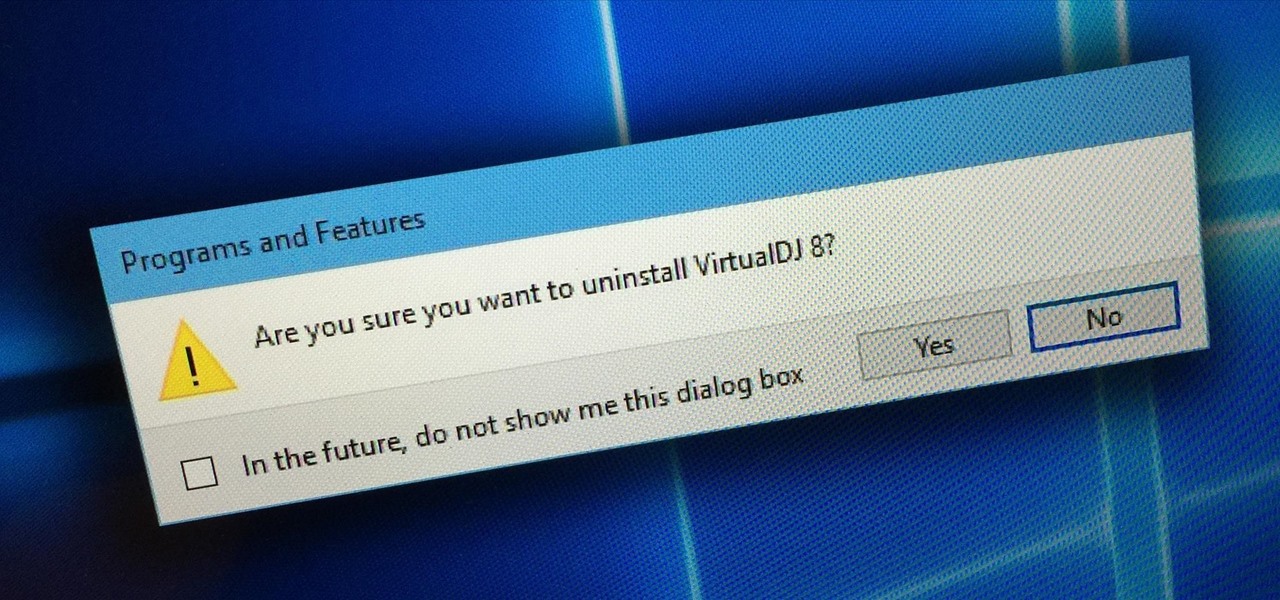
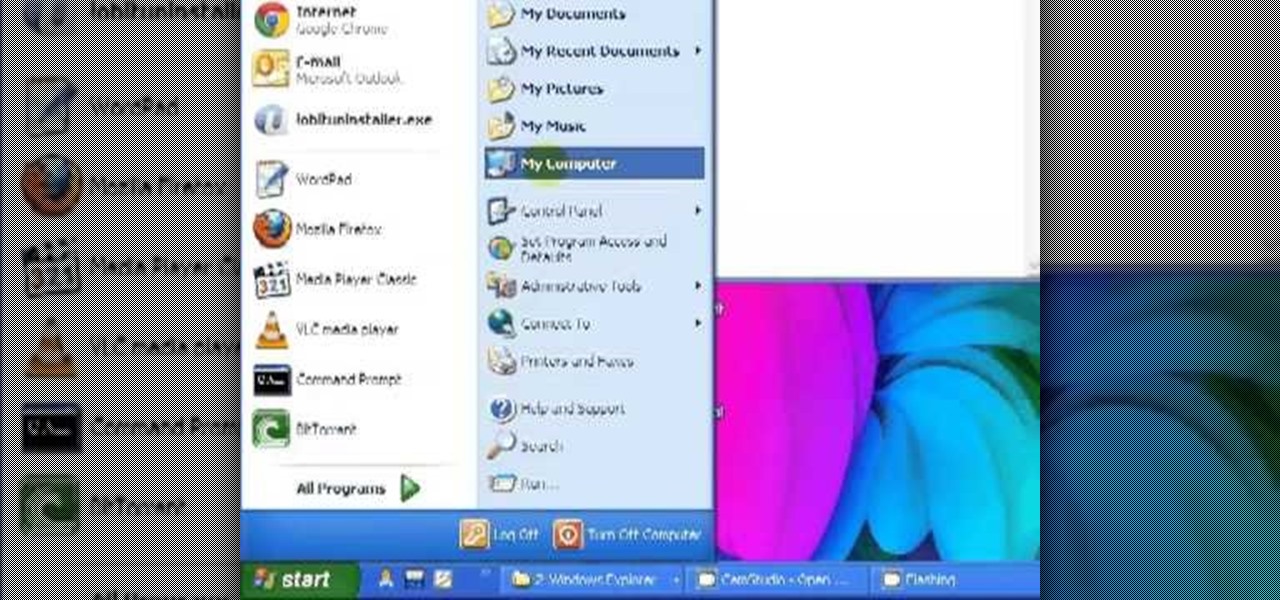
Uninstalling programs in Windows is not the nicest procedure. Some programs bundle a nice uninstaller with them which helps to ease the process. Other programs, mainly those that utilize the Windows Installer technology, begin the uninstall process right away. This can potentially be problematic for users who are trigger-happy with the mouse.

bObsweep robotic vacuums automatically clean whenever instructed to do so by an owner or because of a pre-programmed schedule.

In this simple tutorial you will be shown step-by-step how to write local shellcode for use on 64-Bit Linux systems. Shellcode is simple code, usually written in assembly that is used as payload in exploits such as buffer overflow attacks. Payloads are the arrow head of an exploit: though the rest of the arrow is important for the delivery of the attack, the arrow head deals the killing blow. In reality, payloads are slightly less exciting yet far more interesting and intelligent than medieva...

T-Mobile continues to make waves in the U.S. wireless market behind CEO John Legere's UnCarrier program. At the latest installment in a series of industry-challenging announcements, Uncarrier 5.0 unveiled Test Drive. The new program is set to allow would-be customers to try out the "latest generation" iPhone for seven days on T-Mobile's network without any financial commitments.
I have shown here to install Java development kit. It also contains the settings of path and classpath to prepare for java programming.

How much privacy are you getting as an AT&T customer? With the recent leaks confirming the National Security Agency's surveillance on AT&T users, and the ongoing trial of Jewel v. NSA, it seems not much at all.

When it comes to text documents and spreadsheets, Microsoft Office is the be-all and end-all office suite—but it's not cheap. Paying anywhere from $140 to $400 puts a big dent in your bank account, especially if you're a broke college student eating ramen for breakfast, lunch, and dinner. Something that I wish I would've known about during college is Microsoft's HUP (Home Use Program). With HUP, any employee or student of an organization that has a Microsoft volume license is eligible to purc...
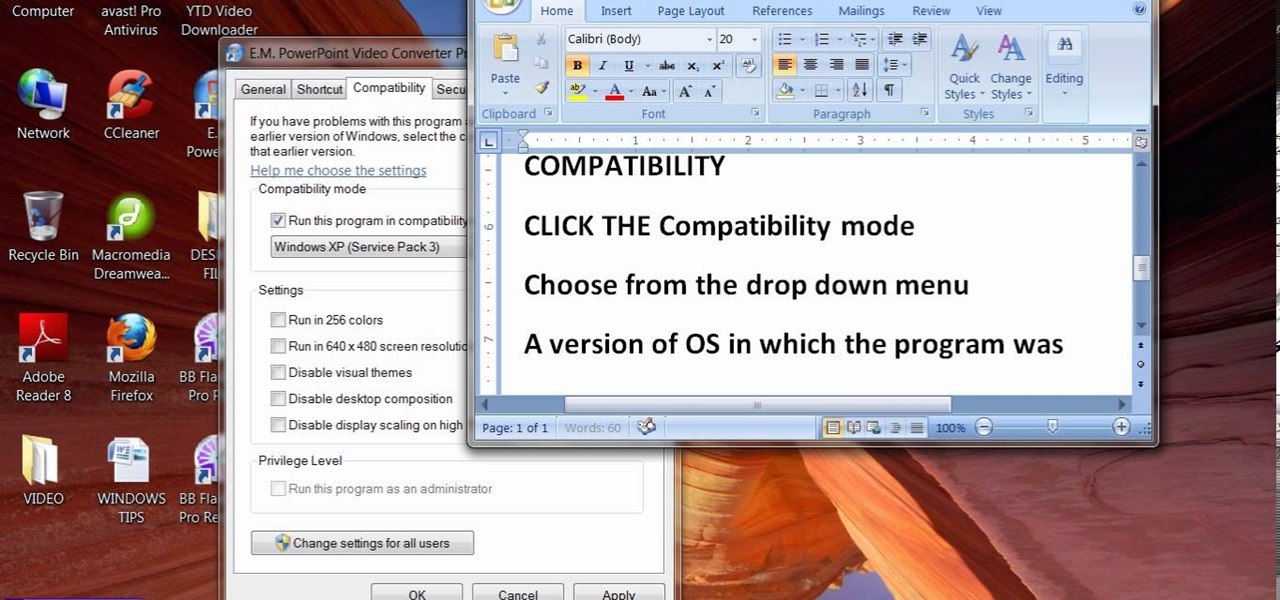
When people upgrade their windows few software don't run on new OS. How to fix the problem? Setting program compatibility solves the issue. Watch the video we made and submitted earlier in You tube.

In this video from macmostvideo we learn how to import unsupported video in iMovie. This happens sometimes when you buy a camera that is not compatible with iMovie. You can add certain video formats to your Mac to make your Mac understand these video formats that don't work with your iMovie. A common one is called mpeg2. You can get this trough Apple. In other cases you get the software with the camera. If you need to convert a video file, try to open it through QuickTime first. If that works...

In order to make Custom titles in IMovie '09, you will need the following: Seashore or any other compatible program.

In this video, we learn how to use Raw Therapee with Gimp. First, you need to go online to Raw Therapee, then download and install Raw Therapee. Once you have this, open it up and familiarize yourself with the layout of the software and where the different tools are at. Next, change your preferences and pick your settings throughout the different folders. Next, find GIMP through the program folders as your installation directory. Now, it will export your images to GIMP automatically. This way...
In this video tutorial, viewers learn how to play DVD movies on the computer for free. Usually, users will need to purchase expensive codes or plug-ins for a media player in order to play a DVD movie. This video introduces the VLC Media Player. This media player is able to play any DVD movie and is a free program. To download it, open your the Google website. Then search for the media player and select the first result. Then click on Download and install the program. This video will benefit h...
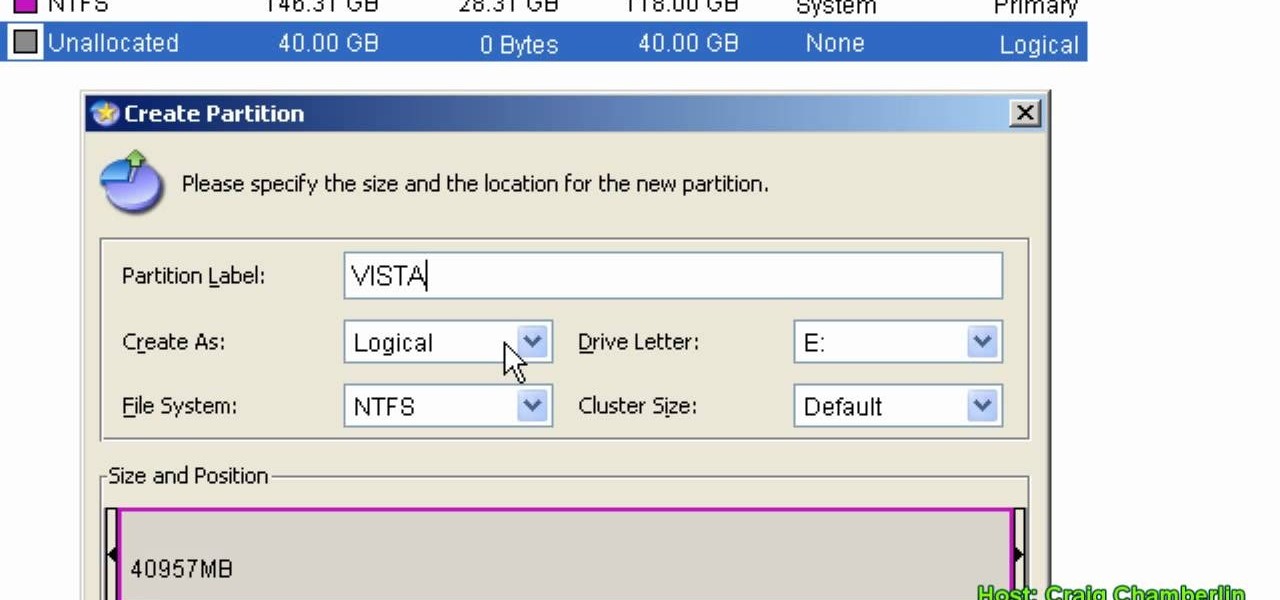
In this Computers & Programming video tutorial you will learn how to format a hard drive to boot a second operating system. First, do a Google search for EASEUS partition master, download and install it. Launch the program. Right click on the unallocated space on your hard drive and then click ‘create’. Now create a new partition for the new OS. Name it Vista, select ‘primary’ in the ‘create as’ window, choose ‘NTFS’ in the ‘file system’ window, select drive letter as ‘V...

Having downloadable files on your website is often an essential. It is an easy and fast way to share programs via the web and allow your visitors to experience software and files that you enjoy. In this tutorial, you will learn how to make a file downloadable for you website, so your visitors can easily download any file. This process is surprisingly straight forward and easy. You can follow this same process whether it is a text file, image, movie or music file. You will also learn how to tu...

This video shows us a tool that can be used to split and merge pdf files without having to buy any software.