
How To: Unlock your mobile phone and make it sim free
This is a demonstration of how to use a software program to unlock your mobile phone and make it sim free. Enjoy your free call!


This is a demonstration of how to use a software program to unlock your mobile phone and make it sim free. Enjoy your free call!

This tutorial demonstrates installing free HTML WYSIWYG Editor Software called Nvu so that you can get started with programming in HTML.
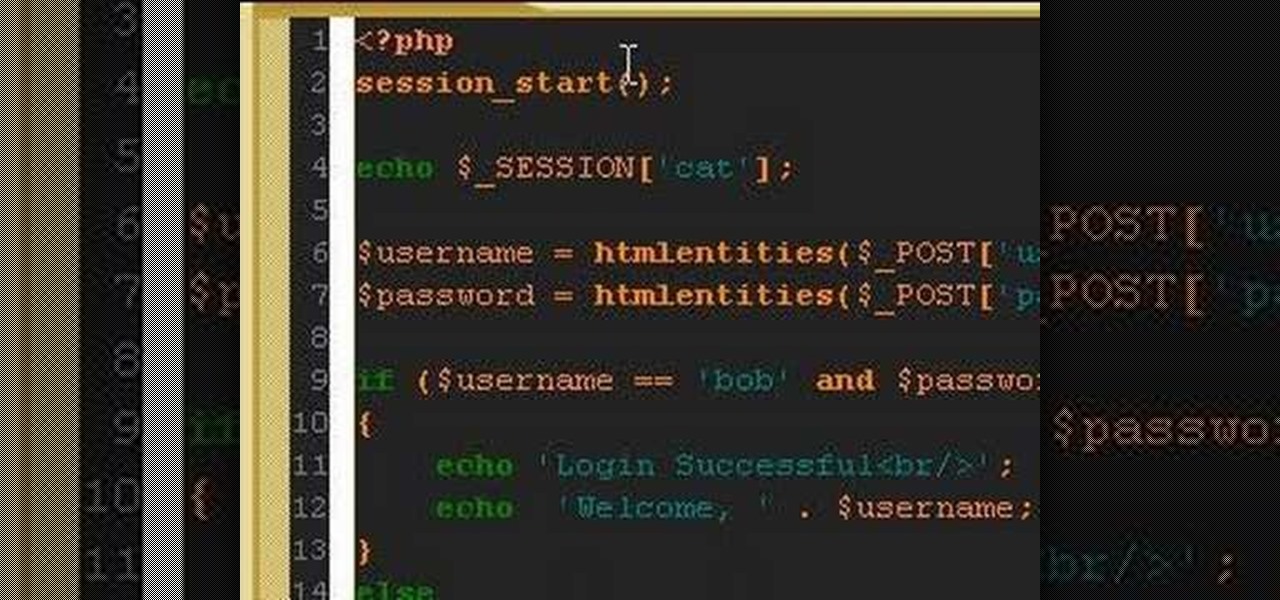
A PHP programming tutorial on creating login sessions to keep users logged in.

Learn all about your leopard gecko's eating requirements with this informative and easy-to-follow program that covers all the important topics of the gecko's diet, from vegetables, to vitamins, to mealworms, guided by Host Hillary Dupont and our senior herpetologist Ron Dupont.

Metacreations Bryce is a 3D terrain-generating application. You can build some beautiful landscapes, create animations, and even import 3D models from other programs.

How to program gravity effects in a Flash-base RPG.

In this tutorial will teach you how to program in Flash and ActionScript to move a character with the arrow keys and make him jump with the space bar.
This video shows you how to download and play TV and movie files on your computer using two programs: Joost and Miro.

Bob and Brett show you two different record modes in your Pro Tools interface - Quick punch and the Transport window.

Bob and Brett show you how to add tracks to your Pro Tools program and how to use them. You are only as limited as your hardware!

Build power and speed with this Plyometrics workout video. These exercises should be done 2-3 times 3 times a week. Of course in order to lose weight with any strength training program it is important to also do cardio workouts at least 3 times a week.

The GNU Image Manipulation Program, or GIMP, is a raster graphics editor application with some support for vector graphics. This video teaches you how to use the GIMP photo editor to edit a series of photos via layering. Learn to put a sumo wrestler over a bridge!

This tutorial explains how to use the free Hotkeybind macro. It allows you to open programs or insert text with a just a keystroke.

Jeff Schell shows you some of the options and configurations available when working with images that do not match the dimensions of your program monitor in Premiere Pro CS3. In addition, Jeff will introduce you to the 'Automate to Timeline" feature that helps you quickly create a photo montage or slide show with the click of a button.

Learn how to use Virtualdub - a free video editing program available online. Learn how to use Virutualdub to edit videos and convert video file formats.

This Pamie Demo shows how to setup, install and run a simple automation script. It shows you: how to install Pamie, how to create a Pamie test script to Automate a form using PythonWin IDE, how to write the script and how to run the test. The volume is really low so crank your speakers way up and make sure you have the proper Python and programs downloaded.

Going to the doctor can be an unsettling event for any child. This program is about preparing your toddler for a visit to the doctor.

It's no secret that more and more talented computer science gurus and programmers are turning toward high-paying careers in engineering. Today's engineers stand at the forefront of some of the world's most important and exciting technological innovations — ranging from self-driving cars and surgical robots to large-scale construction projects and even space exploration—and our reliance on these talented data-driven professionals is only going to grow in the coming years.

The only thing better than programming MicroPython is programming MicroPython over Wi-Fi. So once you set up MicroPython on a microcontroller and have it on its own power source, you won't need to use a data cable to connect to it whenever you need to interact with it, program it, upload files, or grab data.

Choosing which programming language to learn next can be a truly daunting task. That's the case regardless of whether you're a Null Byter just beginning a career in development and cybersecurity or you're a seasoned ethical hacking and penetration tester with years of extensive coding experience under your belt. On that note, we recommend Python for anyone who hasn't mastered it yet.

It's finally here. After years of rumors and speculation, Apple unveiled the new iPhone SE on April 15. While it doesn't have a 4-inch display like the original SE, it's the smallest new iPhone you can buy today, with the chipset of the iPhone 11, 11 Pro, and 11 Pro Max. So, when can you get your hands on it?

Hackers and makers are often grouped under the same label. While hackers draw on computer science skills to write programs and find bugs, makers use electrical engineering to create hardware prototypes from microprocessor boards like the Arduino. We'll exercise both sets of skills to program a $6 NodeMCU to display the status of a Wi-Fi link via an LED, allowing us to monitor for jamming attacks.
With the release of Android 9.0 Pie, Google's focusing on digital health. Digital Wellbeing is a new set of features designed to help you curb your own smartphone addiction. Starting now, the beta version is available, and Google's looking for testers.

While our time with the Protostar VM from Exploit Exercises was lovely, we must move on to bigger things and harder challenges. Exploit Exercises' Fusion VM offers some more challenging binary exploitation levels for us to tackle. The biggest change is that these levels are all network services, which means we'll write our first remote exploits.

With four major carriers, buying an iPhone X or iPhone 8 can be more complicated than you'd think. While Apple has its own iPhone upgrade program, AT&T, Sprint, Verizon, and T-Mobile all have versions of their own. Which plan you choose depends on your needs and, of course, your carrier. However, getting around to upgrading can be challenging to say the least.

Apple officially unveiled the long-awaited iPhone X, its tenth-anniversary edition iPhone, on September 12. With preorder and release dates just around the corner, you'll want to brush up on all things iPhone X to make sure you get your hands on one as soon as possible. After all, preorders start Friday, October 27.

Outside of early military applications, augmented reality is a relatively new technology. It stands to reason that the next company to make a splash in AR would be a startup, and Techstars wants to help.

Gaining access to a system is always exciting, but where do you go from there? Root or bust. Sure, a compromised host is a great way to run a botnet, or do some other boring, nefarious thing—but as hackers, we want root. We also want to take the easiest path possible, search out low-hanging fruit, and exploit them. SUID programs are the lowest of the low-hanging fruit.
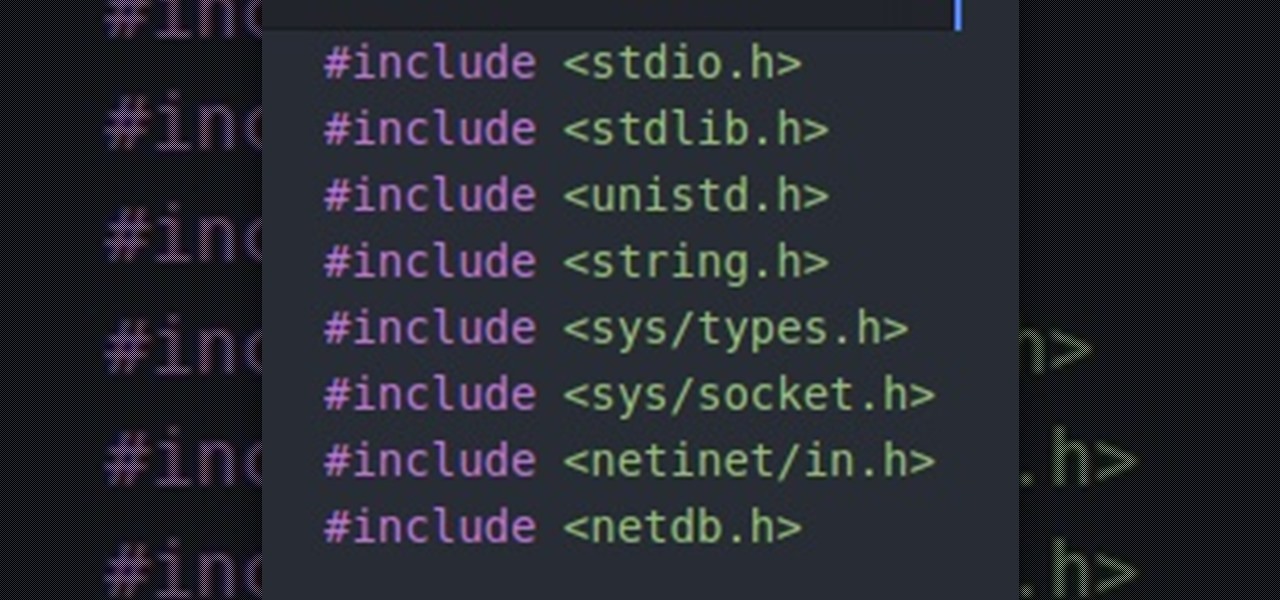
Hello people, I'm back for Part-3. In this part, as promised, we are going to create a client program and then we are going to test it with our server program made in Part-2.

"It just ticked me off," he said. In March 2011, Neil Singh paid $50 to back the Hanfree iPad stand on Kickstarter. The project was funded at $35,000, but production stalled, and the delivery estimates kept getting pushed back.

It's been a while since I wrote up an article for this series but I did say that I'd be covering some WinAPI. So if you're interested in programming for the Windows platform, hop aboard and follow along.
We knew it was coming eventually, but this is a bit out of left field—early builds of the next version of Android have been released almost two months ahead of schedule. Android N, as it's being called for now, is already available for the last two generations of Nexus devices, though it's just an early preview build for now.

Welcome back to another episode of Java Tutorials, In today's tutorial, we'll be learning about what methods are, proper syntax when writing Methods, and why they are beneficial in a program's code.

I saw many people asking for a Tutorial about writing their own Remote Administration Tool, so I now introduce you in a basic kind of RAT. This program is not for real use, but for learning how you could write this kind of tool. It will be basicly coded and not very refined. I used Python 3, so you have to install it if you want to use this program unchanged. Also this RAT is for Windows and almost all features won't work under Linux.

The digital pen on the Surface Pro 4 and Surface Book is an indispensable tool for serious note-takers and artists alike.
Welcome back Hackers\Newbies!

This is a short explanation and tutorial on how to grab saved passwords from Google Chrome, ideally from a meterpreter session. The idea behind this is to understand how saved passwords work and how to keep them safe. Let's have some fun :D Understanding Google Chrome Saved Passwords

Hi nullbytes! I've been recently reading the whole Linux Basics for the Aspiring Hacker series and felt like it was missing some stuff I know, so I felt like sharing it with anyone who might find it useful too.

Welcome to the sequel to the latest post on writing 64 bit shellcode! This tutorial will assume that you are aware of everything mentioned in the last one, as I will try to make this tutorial void of formalities and straight to the point! If you have not read the last one, I suggest doing so unless you are familiar with basic assembly programming and system calls. This is by no means rocket science, so therefore I will simply repeat my TL;DR from last time before we get started, so that the a...

Hello my fellow hackers, Welcome to my republished revision of the ruby programming language, Part 1.