If you're a ladies man like me then this next tip could save you from sorely embarrassing yourself. Here's the problem: You think you are texting Kelly M from New Year's when you're actually texting Kelly F from that one bar. Needless to say this could cause a problem with your relationships.
For a photo- and video-sharing app based around privacy, Snapchat sure has a lot of security holes floating around. At one time, you were able to take screenshots of Snapchats in iOS 7 without the sender knowing, which is something that you can still do on rooted Android devices.

Instagram recently released their new Instagram Direct messaging feature in their Android and iOS apps, which lets users share private photos and videos directly with individuals or groups of up to 15 users. However, there are no restrictions on who you can send private photos or videos to.
"Ain't No Sunshine" might just be a classic song to you, but for me and my Samsung Galaxy S3, it means so much more. For the most part, my GS3 does a decent job at automatically adjusting the brightness of the screen when I'm in normal lighting, but when I'm in little or no lighting, or there's just way to much, I usually have to switch over to manual to get the right balance. Luckily, we're not stuck with Samsung's built-in auto brightness feature. There are some really good third-party solu...

If you're constantly going from dark to brightly lit areas, you've probably noticed that the stock auto brightness feature on your Samsung Galaxy Note 2 doesn't work that well. Either the screen is really dim and unreadable, or it's just way too damn bright. Sure, you can disable auto brightness, but then you have to manually adjust the brightness all of the time for that perfect comfort level. This isn't really all that bad of an option, but don't be surprised when you see this: However, the...

We all know about PRISM. The Surveillance Program allowing the U.S Government to access private user information. Such as, Google Searches, Tweets, Facebook Posts, Private Images, and other private user data. "Hiding" yourself can be very difficult, but it is possible. I'm here to show you How to Become Anonymous & Browse the Internet Safely.

Welcome back, my fellow hackerians! Today we'll be hacking Facebook profiles on your local network. You may think, "How is this useful, nobody but me is using my network." Well, you can use this on other Wi-Fi networks that are available for free (like at Starbucks) and crack their precious Facebook profile!

When the HTC One was announced, the fact that its IR transmitter was a side note more than a main feature made me dismiss it. When Samsung included one in the GS4, it became even less impressive. However, now that I actually have a One, I find that the "TV" app is way more than just one of Samsung's "S"-gimmicks. Step 1: Set Up Your Service Provider

Facebook Home was just released in the Google Play Store a couple days ago, and for those of you eagerly waiting to get it on your Nexus 7, you'll unfortunately be stuck with this message: The new Facebook Home launcher app is blocked on the Nexus 7, because Facebook only released it for a few select Android phones. Home for tablets probably won't appear for months, but that's okay, because you don't have to wait that long! In this article, I'm going to show you how to get Facebook Home insta...

"Dude-man-bro, are you going to Coachella this year?" If I got a dollar for every time I was asked that question, I might just have enough money to actually buy the dang ticket. Concerts have been, for a very long time now, a great way to spend a night or a weekend having fun with friends and listening to some great tunes.

For the most part, nobody makes money off of Facebook. Sure, some people make a living by updating pages for businesses and celebrities, but hardly anyone gets a dime from the site itself.

Facebook has been looking to launch a new product for a while now, and it seems they've finally realized what they're best at—being as creepy as possible. If you thought your boss checking out your girlfriend's beach photos was weird, Facebook's new Graph Search has only upped the ante. Now, I don't want to be an alarmist, because I'm sure there are a bunch of great things a Facebook search would find. If you're single, perhaps you could search "Girls that are single that like Goodfellas." Th...

Finding love is tough. Movies like The Notebook and Twilight have ruined the expectations of love and relationships for us guys. Some women's ideal love situation is being kissed by a glittery sparkling vampire. "I know we only met a few seconds ago, but I'm deeply in love with you."

Many social networks have become a part of our daily routine. Checking Facebook or sending out a Tweet are things millions of people do every single day. So, one would think that having a great app offering for Windows 8 would be a no-brainer. But, and this is a huge but, there are still no official Twitter or Facebook apps for Windows 8.

TIFF 2012 Wrap-Up - Pounds Personally Gained: 4.5

As if you needed another reason to lock down your Facebook profile, the company's sketchy new partnership with data mining firm Datalogix is geared towards giving advertisers more information on what you're doing—even when you're not online. It's just not enough that they can target ads based on your preferences, now they want to know how those ads are influencing your buying habits in the real world.

There have been plenty of headlines recently about fake followers in both politics and entertainment. Everyone gets hit by a spam account here and there, but when a large percentage of someone's followers are fake, it can look pretty bad, especially with influential people being accused of buying their followers to look more popular.

If you've read anything in the news about Skype recently, it probably hasn't been good. First, there was the controversy over the company listening to and recording users' conversations. Now, there's a new spam tool for Skype that can harvest usernames, see whether or not you're online, and even parse your log files. Image by Lloyd Dewolf

Most of the time, asking to borrow someone's car will elicit a really long string of excuses. But unlike letting your buddy use your car, which usually gets you nothing more than an empty tank, GM has found a way to make car sharing beneficial for everyone involved. If you're one of the 6 million people who have a GM vehicle that's connected to OnStar, you're in luck: according to an OnStar employee, you can make up to $1,000 a month just by letting other people rent out your car when you're ...

So, you want to go a step further past the "Remove from Friends" option in Facebook? That would be blocking them, and it's one of the simplest things to do in Facebook. That's why this is such a short video— because it's easy to find and do. Simply go the bottom-left of your friend's profile until you see "Report/Block this Person". Click on that option and choose what you want to do and click "Submit". That's it. The perfect way to get rid of spammers and exes.

If you use Facebook more than you probably should, then you may have noticed all of those emails they send you. You'll get one when somebody comments on your wall, when someone comments on a comment you wrote on somebody else's comment, when somebody comments on a photo someone else tagged you in, when some… well, you get the idea… a LOT of freaking emails!

In this how to video, you will learn how to tag pictures on Facebook. To do this, first open up Facebook and log in to your account. Next, click on a friend's profile page and look for a picture that you may be on. Once you are there, select tag and the click on your face in the picture. From there, type in your name and click okay. Once you are done tagging, click done tagging. You have now successfully tagged yourself in a photo in Facebook. Now when you mouse over your face, a square will ...

In this video, we learn how to block annoying applications on Facebook. Instead of just deleting these, you can block them so they won't show up on your page anymore! First, click on where it says "via (application name)" it will take you to the application's Facebook page. On the left hand side of the page, underneath the profile picture, there will be a button that says "block this application". Once you click this, you will just need to confirm that you want to block it and those types of ...

In this tutorial, we learn how to integrate Facebook chat with iChat. To do this, go into your Facebook account and copy your profile name. Now, go into your iChat account and click on "preferences". Next, click on the "add" button and select "jabber" from the drop down menu. Now, add your account name with "@chat.facebook.com" and type in your Facebook password the same as you would do so in Facebook. Under server options, enter "chat.facebook.com" and the port will be 5212. Now your Faceboo...

This fast tutorial will show viewers the basics of how to use Facebook for those who are new to using the website. After creating an account and logging into Facebook, you will see your homepage, which has most of the new information regarding your friends and their recent activity. Clicking on the links at the top of the page will allow you to access pages such as your own profile, where you can display information about yourself, such as where you work or your date of birth. After watching ...

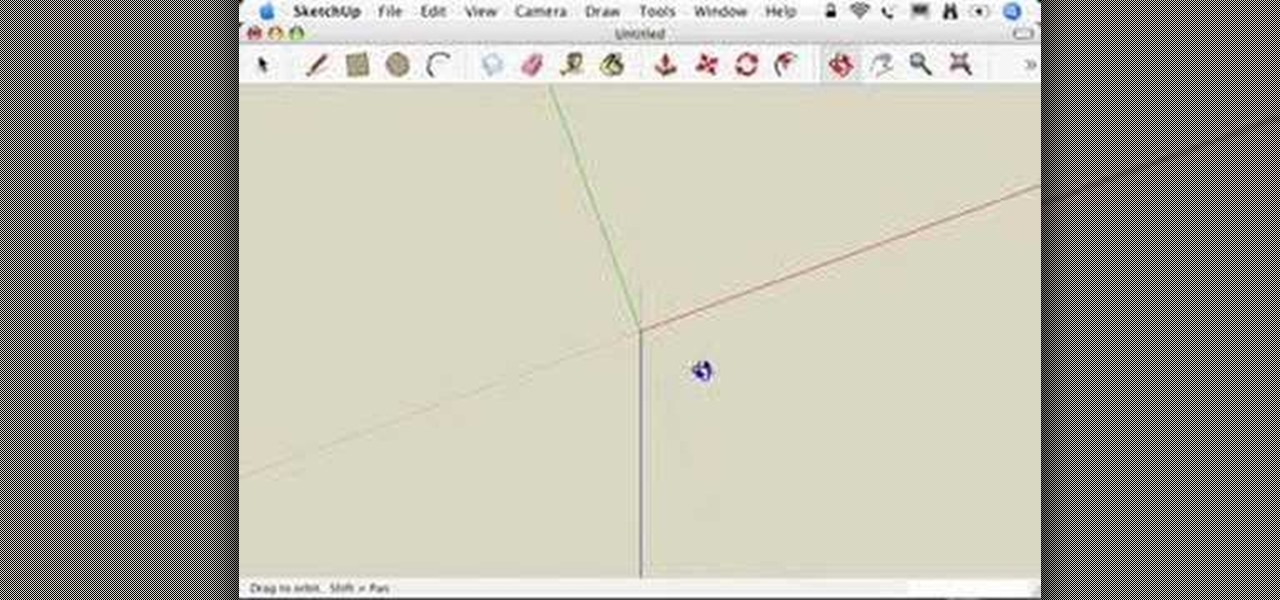
This video series takes you through every step of building a building in SketchUp and is taken from chapter 4 of "Google SketchUp for Dummies" in case you want to follow along. PART 1 explains how to switch to a 2D view to get you ready to build the floor plan. It's a good idea to have accurate measurements of everything you want to build before starting this project. PART 2 familiarizes you with the tools available in SketchUp to help you create your floorplan. PART 3 shows you how to draw t...

Sending Christmas cards via snail mail is so passé. Why spend the time and money for a bougie photoshoot, saccharine card design, and postage when you can use augmented reality to instantly dress up photos and videos to send to friends and family instead?

There's no doubt iOS 13 has dominated the talk around the Apple community this month. Since the announcement and release of the first developer beta, we iPhone users have had a treasure trove of new features and changes to explore and discuss. Now the fun continues with iOS 13 dev beta 2. Who's ready to start up the conversation all over again?

Gathering information on an online target can be a time-consuming activity, especially if you only need specific pieces of information about a target with a lot of subdomains. We can use a web crawler designed for OSINT called Photon to do the heavy lifting, sifting through URLs on our behalf to retrieve information of value to a hacker.

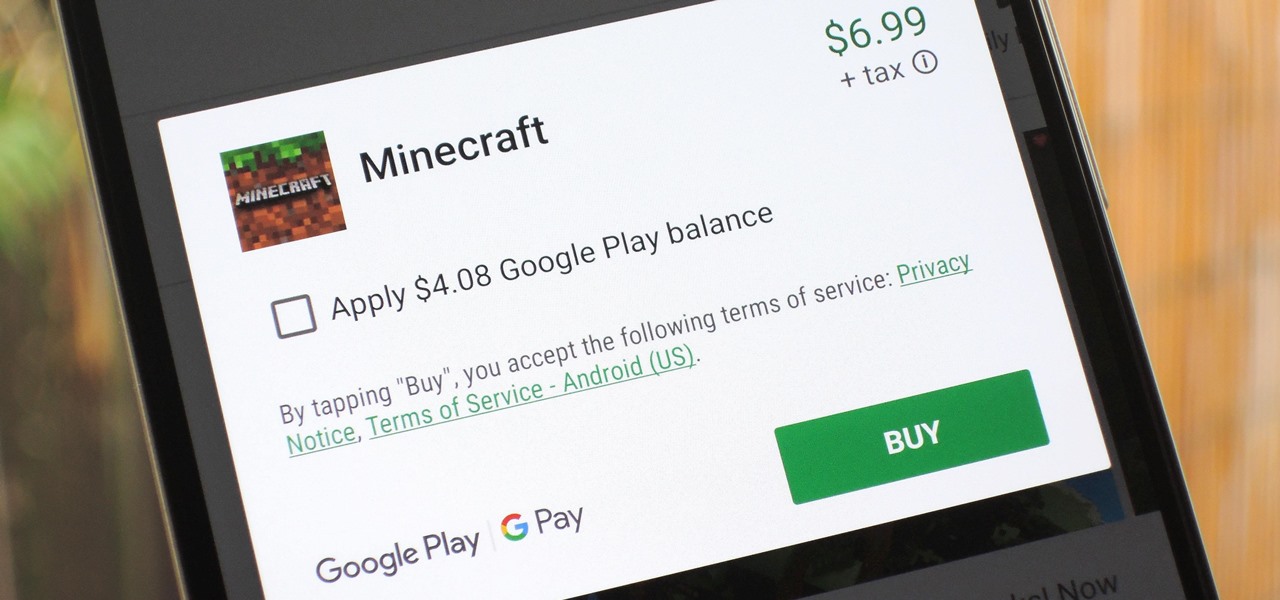
The iTunes App Store makes it easy to buy an app or game on someone else's behalf, and it's a great way to send an iPhone user a thoughtful gift. The Google Play Store doesn't have such functionality, but there are still a few workarounds to accomplish the same goal: gifting an app to an Android user.

One of the best ways to improve your skills as a hacker is to learn to combine different avenues of attack to achieve success. What if it were possible to get a victim to connect to our machine and execute a chosen payload on our behalf? This is indeed possible with the almighty Metasploit and the aid of a technique known as command injection.

It's always a good idea to know how an attack works at the very basic level. Manual techniques for exploitation often find holes that even the most sophisticated tool cannot. Sometimes, though, using one of these tools can make things so much easier, especially if one has a solid foundation of how it works. One such tool can help us perform a cross-site request forgery with minimal difficulty.

Web 2.0 technology has provided a convenient way to post videos online, keep up with old friends on social media, and even bank from the comfort of your web browser. But when applications are poorly designed or incorrectly configured, certain flaws can be exploited. One such flaw, known as CSRF, allows an attacker to use a legitimate user's session to execute unauthorized requests to the server.

According to Google at their 2018 I/O conference, Google Assistant is now available on over 500 million devices. Now that the assistant is available on iPhones as well, Google has to give iOS users a reason to switch to its assistant over the built-in Siri. Today, Google has eight more reasons for users to do so.

Proxies can be quicker to use than a VPN for specific applications, like web browsers or torrent clients. Both services will hide your true IP address, but a VPN is slowed down because it encrypts all data through a VPN network, while a proxy just acts as a middleman for fetching and returning requests from a server on your behalf. When speed is needed, go proxy.

Six people have died from fungal infections in Pittsburgh hospitals since 2014—that fact is indisputable. The rest of the situation is much vaguer. A lawsuit has been filed against the hospitals on behalf of some of the deceased patients, alleging that moldy hospital linens are to blame. While the lawyers argue over who's at fault, let's look at how this could have happened.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Audiobooks are great because they require little-to-no effort on your behalf. When driving in traffic, why not listen to George R.R. Martin's lengthy A Feast for Crows instead of repetitive, commercial-laden radio? Maybe it harks back to prepubescent bedtime readings, but having things read to me is a very satisfying experience.

Facebook will let you do pretty much anything via a text message, but unless you still have a flip phone, it's more of a novelty than actually useful.