
How To: Survive a killer bee attack
Africanized honeybees, also called killer bees, can be far more aggressive than other types. Here's how to survive when they're on the rampage.


Africanized honeybees, also called killer bees, can be far more aggressive than other types. Here's how to survive when they're on the rampage.

If you're worried about the security of your Mac, there are easy measures to prevent the most dangerous attacks. Named after the tactic of accessing an unattended computer in a hotel room, we can thwart "evil maid" attacks with Do Not Disturb and LuLu, free macOS tools by Objective-See that keep an eye on unattended computers and flag suspicious network connections that indicate a malware infection.

It only takes a few commands to manipulate a MacBook's secure HTTPS traffic and pluck login passwords out of the encrypted data. Let's take Facebook and Gmail hacking to the next level by intercepting Safari and Google Chrome web traffic in real time.

Beginners learning brute-forcing attacks against WPA handshakes are often let down by the limitations of default wordlists like RockYou based on stolen passwords. The science of brute-forcing goes beyond using these default lists, allowing us to be more efficient by making customized wordlists. Using the Mentalist, we can generate millions of likely passwords based on details about the target.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

In the midst of outlining plans to release Pokémon Go in China and debut its new Harry Potter game during the back half of 2018, Niantic CEO John Hanke turned to the dark arts by taking a swipe at the company's AR gaming competition.

The Chinese government's tight restrictions on gathering data by foreign firms for 3D mapping, the lifeblood of machine-taught driverless systems, could at least slow down access to the market by Waymo, Tesla, General Motors (GM), Ford, and other players hoping to make inroads there.
Heart disease is the leading cause of death of men and women in the US. Over half a million Americans die from it annually. Atherosclerosis — a build up of plaque in the arteries — is a common feature of heart disease and can be caused by smoking, fats and cholesterol in the blood, diabetes, and high blood pressure.

Millions of dollars continue to pour into the Chinese driverless market. Now, according to research firm CB Insights, $929 million have been invested in the first quarter of this year.

Beijing- and Seattle-based DataMesh have announced the release of a new enterprise geared mixed reality middleware — MeshExpert. This solution for collaborative interaction with dynamic data is made up of two primary components: MeshExpert Live!, a 4K mixed reality capture system built off of the Microsoft Spectator View, and MeshExpert DataMix, which offers the ability to blend different types of data with XR and mobile hardware.

The Raspberry Pi is a credit card-sized computer that can crack Wi-Fi, clone key cards, break into laptops, and even clone an existing Wi-Fi network to trick users into connecting to the Pi instead. It can jam Wi-Fi for blocks, track cell phones, listen in on police scanners, broadcast an FM radio signal, and apparently even fly a goddamn missile into a helicopter.

When I tried to set up an eviltwin for a MitM-constelation in kali 2.0, I couldn't provide internet to the victim. The origin was the brctl bridging. I have read many tutorials but all of them where explained in backtrack and older versions of kali. So i was searching for a solution without using brctl and this solution will be explained now. This will just work on unencrypted wireless-environments.

Researchers at the cyber security firm Zimperium have recently uncovered a vulnerability in roughly 95% of Android devices that has the potential to allow hackers to take total control over your phone with a simple picture message (MMS). The gritty details of this exploit have not been made public yet, but hackers now know the general framework for this type of attack, so you can be certain that they'll hammer out the details in no time.

Welcome back, my novice hackers! Before we try to attack a website, it's worthwhile understanding the structure, directories, and files that the website uses. In this way, we can begin to map an attack strategy that will be most effective.

Welcome back, my tenderfoot hackers! So many readers in the Null Byte community have been asking me questions about evading detection and hacking undetected that I decided to start a new series on digital forensics.

Welcome back, my fellow hackerians! Today we'll be hacking Facebook profiles on your local network. You may think, "How is this useful, nobody but me is using my network." Well, you can use this on other Wi-Fi networks that are available for free (like at Starbucks) and crack their precious Facebook profile!

The newest trend in couture? It's called 'trashion' - high fashion using trashy things. And we mean trashy! This tutorial shows you how to make a ball gown using trash bags, duct tape and newspapers. You'll also want a dressmaker's dummy to construct your dress around - or at least a model who's okay with standing still for a long period of time. Use the trash bags to form the dress, and then attack the newspapers over it layer by layer. You're ready for your debut!
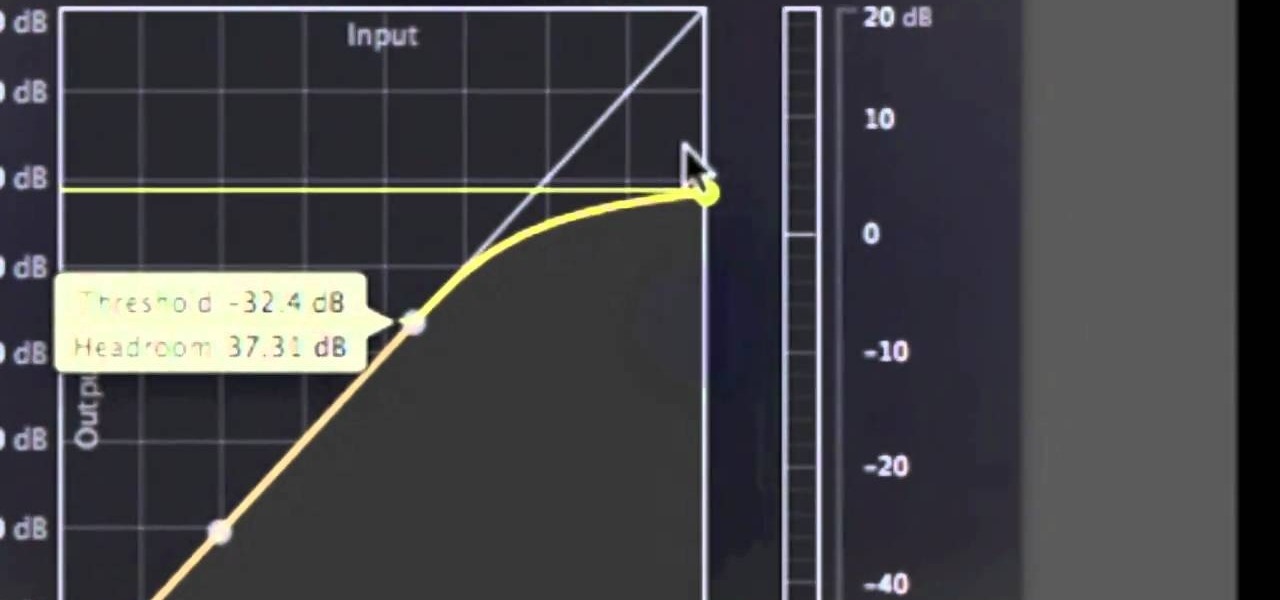
It's called the AUDynamicProcessor, and it's very helpful when it comes to mastering your songs in GarageBand. In this video tutorial, you'll learn how to utilize and manipulate the sound dynamics of your songs in GarageBand using the AUDynamicProcessor filter, which effects the high and low ends of audio.

In this tutorial, we learn how to get the Phoenix achievement in Soul Calibur IV. To do this, you will need to win with all your equipment destroyed. Hit high and do low attacks to help you get the advantage. Don't fight and just stand there until all your equipment is gone. Go to the Tower of Lost Souls and do this on Floor 11 to help you get this achievement more easily. After the opponent knocks off your equipment, you will be able to start fighting and hurting the other person until they ...

In this video, we learn how to do Andres Iniesta's signature soccer move La Croqueta. First, while you are on the field and have the ball, you need to turn and control it. Pay attention to those around you and move around them. Move the ball from left to right around the people coming towards you. Attack the open space to free yourself up and get away from crowds of the opponents. Once you do this, you will be close to the goal. Finish off the shot by kicking the ball into the goal. From here...

In this video, we learn how to use a sidechain gate on synths & drums in Ableton. First, drag a gate device onto your synth track. This will turn down the volume of the synthesizer device very quickly. Once you do this, you will have a sidechain view, turn it on by clicking the green button. Then, bring the attack down to 0 ms and bring your hold down to 3.9 ms. When this plays, you will hear an electronica type of beat. This is a simple way to make your synth lines more exciting. Save this w...

When in repose upon the toilet, the last thing most people want is for something to jump out at them. And that is exactly what will happen to them if you pull this prank. It turns out that the actual tape from a tape measure is a great little prank tool, and in this video you'll learn how to attach one to a roll of toilet paper so that when your victim attempts to wipe, they will be attacked by tape and scared... witless. Yes, witless.

Fries are such a killer food. They're beloved as the favorite "vegetable" of kids and adults everywhere, yet they are one of the absolute worst foods you can eat if you want to, you know, live past 40, containing high levels of saturated and trans fats that clog your arteries and lead to lots of gnarly diseases.

After 12 years Starcraft 2 is finally here to blow your mind. If you're looking for help with the game, you've come to the right place. We have tons of videos about how to do just about everything in the game. We have strategies for winning campaign and multiplayer games. We have guides to using the immensely powerful level editor. We'll even teach you how to build a Terran Barracks out of Legos. This video will show you how to use the Protoss High Templar's Psionic Storm ability most effecti...
In this video, we learn how to defeat Aster Protoflorian in Final fantasy XIII. First, activate the aerosol to make yourself stronger. Now, switch over to medic anytime you get hurt from the monster. Take hits where you can and use your different tools to help attack him further. Slash and burn when you can, then use double doses. Libra him when you get a chance, then Libra him again and he will turn red. Now he will have different weaknesses, so watch out for these. The best way to defeat hi...

This video makes suggestions in how to choose colorful flowers and shrubs in your garden. Bowle’s Mauve is a purple flowering plant that will grow and bloom until fall. It will become bushy. Another colorful choice is the Rock Rose, a pinkish flower. The Blue Salvia has blue flowers. A Bank’s Rose, only bloom for a short time. It has yellow or white flowers. Aphids tend to attack it, but it is hearty.

This video is demonstrated completely through visual movement and accompanied with a brief written description. A young man speeds down the soccer field with a ball and scores a goal. His signature move leading up to the goal is broken down into very specific methods of movement, the first of which is a high speed attack as he races down the field. The next method to this signature move is the weight shift, in which the goal scorer shifts his weight, along with the ball, from foot to foot to ...

This video shows how to do audio side chain compression to improve your production audio mix. Side chain compression is an easy way to balance the base and the drums. Using a compressor, you can cause your base to drop in volume when the drums are hitting so that one is not over-powering the other. This video walks you through step by step instructions for configuring your compressor to balance based on threshold level, the attack time, and release time. This is an excellent source of audio p...
Learn everything you could possibly want to know about the internet, multiplayer game Evony with tutorials from EvonyTutorials. Watch this video tutorial to learn how to play Evony - military domination. See exactly what the game Evony is!

Reconnaissance is one of the most important and often the most time consuming, part of planning an attack against a target.

Complex shell scripts can be implanted into photo metadata and later used to exploit a MacBook. In addition to obfuscating the true nature of an attack, this technique can be used to evade network firewalls as well as vigilant sysadmins.

Hacker's are always looking for new ways to exploit systems and exfiltrate passwords, even in hashed form. Sophisticated brute-force attacks powered by high-end GPUs can perform millions of password attempts per second. But Ubuntu and Debian users aren't completely helpless. There are ways to harden the hashed password to better defend against Hashcat attacks.
Smartphones and laptops are constantly sending Wi-Fi radio signals, and many of these signals can be used to track us. In this guide, we'll program a cheap IoT device in Arduino to create hundreds of fake networks with common names; This will cause nearby devices to reveal their real trackable MAC address, and it can even let an attacker take over the phone's data connection with no warning.

Leaked databases get passed around the internet and no one seems to notice. We've become desensitized to the data breaches that occur on a daily basis because it happens so frequently. Join me as I illustrate why reusing passwords across multiple websites is a truly awful practice — and compromise hundreds of social media accounts in the process.

After a hacker has configured Metasploit on a remote private server, created a resource script for automation, and created a simple payload, he or she can begin the process of remotely controlling someone's Windows 10 computer with just a few moments of physical access — even if the computer is off.

Using just a small sticky note, we can trigger a chain of events that ultimately results in complete access to someone's entire digital and personal life.

JavaScript is one of the most common languages used on the web. It can automate and animate website components, manage website content, and carry out many other useful functions from within a webpage. The scripting language also has many functions which can be used for malicious purposes, including stealing a user's cookies containing passwords and other information.

The Cloud Security Alliance (CSA), a leading IT trade association, has published its first report on risks and recommendations for connected-vehicle security, ahead of when driverless cars are about to see volume production in the near future.

You may not know what HTTP is exactly, but you definitely know that every single website you visit starts with it. Without the Hypertext Transfer Protocol, there'd be no easy way to view all the text, media, and data that you're able to see online. However, all communication between your browser and a website are unencrypted, which means it can be eavesdropped on.

Good day to everyone, today I will present some basic and advanced concepts that targets sophisticated attacks on the social basis, also I will write about some steps that can prevent this attacks from occuring, basically we will examine Social Engineering from the angle of attacker and victim, some people who are interested in security and work for middle-sized companys can learn and use something interesting from this post.