
How To: Tie the "glo bug yarn egg" for fly fishing
The Glo Bug Yarn Egg. Tie it. Then it's hook, line, and sinker. This pattern is a standard for steelhead, salmon, and trout


The Glo Bug Yarn Egg. Tie it. Then it's hook, line, and sinker. This pattern is a standard for steelhead, salmon, and trout

Create a 2-axis chart in Excel 2007 combining a column chart and line chart

This tutorial shows you how to correct converging vertical lines (extreme perspective) or surface edges on photos using Photoshop tools.

Learn how to do add a bass line while beatboxing.
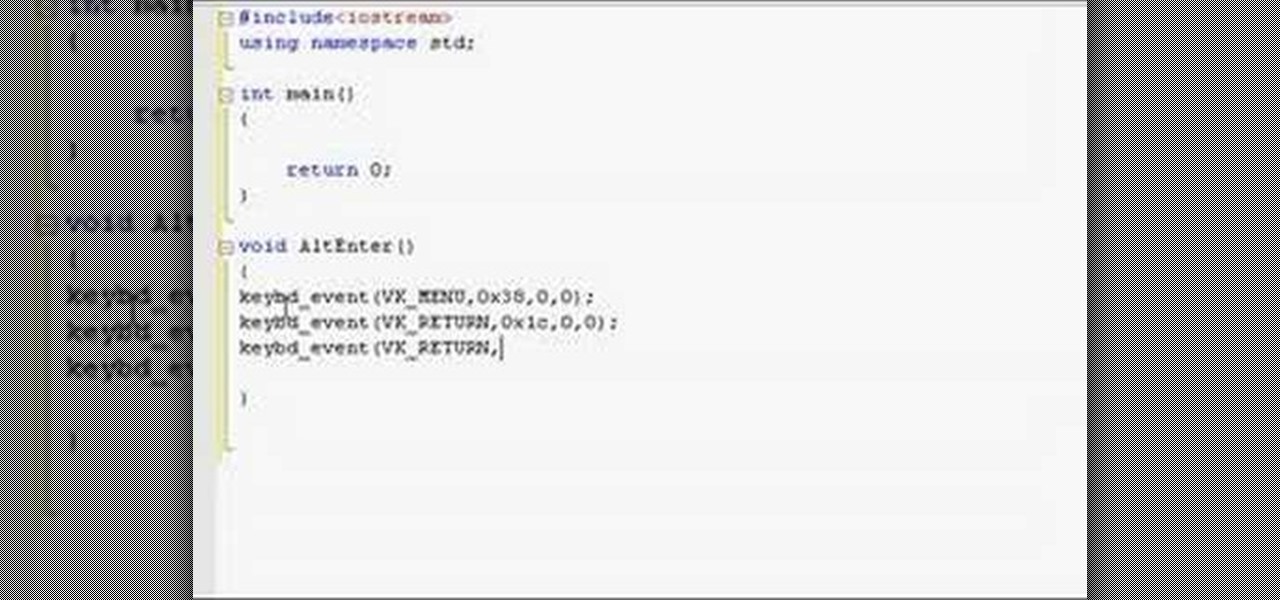
This C++ programming tutorial goes through the use of functions, pointers, how to make fullscreen, and changing colors per line.

It is very hard to see the blood line in a dark toenail. This video will show you how to trim or cut a dark toenail without hurting the rabbit or bunny.

Learn how to use this v-cut passing drill in order to help your players improve their passing skills on the basketball court.

Learn how to explode from half court to the three point line and practice your three point shots in this 3 point shot off the fast break basketball drill.

Practice your soloing skills and record melodic lead lines over your favorite song or backing track by importing pre-recorded tracks into Logic.

Develop your technique and learn how to get your lead lines to come through clean and strong using rockin' Minor Pentatonic fingering exercises.

Learn some basic plumbing skills. Watch this video to learn how to glue PVC joint pipes together to form your drain lines.

This video shows you the proper technique to draining the engine fluids from the radiator and connected hoses before removing the engine for disassembly. Explains the process for using your specific engine repair manual to label all of the wiring, vacuum lines and hoses so that installation later will be smooth.

This video demonstrates how to perform the overturned back sacada. This move is one that the follower does and the key points for success are to focus on the spiral energy of the step and stretch the step. The leader should pay close attention to the line taken.

With any drawing tool you would expect to be able to create lines with arrowheads. In this tutorial Terry White will not only show you how to do it in Illustrator, but he will also show you how to give your arrows a little flare by reshaping them with the Pencil Tool. That's right, he's found a great use for the tool that no one likes to use.

A very important thing to keep in mind when you're creating images from scratch or even putting things into existing images is the concept of perspective. Bert goes back to basics to teach this concept, starting with a horizon line and adherence to the rules of mother nature.

You can learn how to create an impossible shape out of paper. All you need is a piece of paper and scissors. First, you cut along the 2/3 lines of the paper. Then you flip one half of the paper over, and you have created an impossible shape.

You can practice skating backwards. There is a drill you can do. Set up five to ten sticks in a straight line and begin to c cut thrust down the length of the ice.

During our last adventure into the realm of format string exploitation, we learned how we can manipulate format specifiers to rewrite a program's memory with an arbitrary value. While that's all well and good, arbitrary values are boring. We want to gain full control over the values we write, and today we are going to learn how to do just that.

Format strings are a handy way for programmers to whip up a string from several variables. They are designed to save the programmer time and allow their code to look much cleaner. Unbeknownst to some programmers, format strings can also be used by an attacker to compromise their entire program. In this guide, we are going to look at just how we can use a format string to exploit a running program.

An attacker with shell access to a Linux server can manipulate, or perhaps even ruin, anything they have access to. While many more subtle attacks could provide significant value to a hacker, most attacks also leave traces. These traces, of course, can also be manipulated and avoided through methods such as shell scripting.

If you've spent countless hours scrolling through Instagram feeds full of selfies, then I'm sure you know that some are, well ... better than others. There are so many different things you can do to start taking better selfies to post on social media. One really easy way is to start shooting in VSCO.

While Lyme disease can be disabling, the wrong treatment for the infection can be fatal.

Robots are always really cool, if you ask me. Sometimes they're made out of Legos, and that's even cooler.

The drag on your fishing reel is what keeps big fish from breaking your line. Properly setting the drag could prevent you from losing that trophy fish.

Welcome back, my tenderfoot hackers! As you should know from before, Snort is the most widely deployed intrusion detection system (IDS) in the world, and every hacker and IT security professional should be familiar with it. Hackers need to understand it for evasion, and IT security professionals to prevent intrusions. So a basic understanding of this ubiquitous IDS is crucial.
Welcome back, NB community, to my series on sorting. I introduced in my last article the concept of complexity. When I say complexity, I'm talking about time complexity.

Welcome back! Sorry for the dry spell, but I've been rather busy setting up some side projects! If you remember back to a few training sessions ago, we covered basic file I/O. This is a very important step in making our scripts applicable in a real life scenario, and today we're going to further these concepts.

Hello again! In this tutorial, we are going to go over something called "operators" which will help us build upon conditions of control structures and also some variable manipulation. Without further ado, let's dive in!
I was bored when I found this piece of literature: ==Phrack Inc.==

Hello fellow training hackers. I do not know if many of you are familiar with ruby, but since it is a useful scripting language, that hasn't been covered too much here on Null Byte, I thought why not do some How-tos about it now and then.

Manufacturers like Samsung and LG have added their own implementation of multi-window features to Android for years now, but with the release of version 6.0 Marshmallow, Google has finally gotten around to working the same feature into stock Android.

See how to make homemade "ice" candles out of taper candles (or wax flakes). Cut up the taper candles, heat them until melted, then pour into a container lined with ice (chipped ice, not cubes) with the wick dangling in from above. The ice will create an interesting design in the candle.

Sadness won over the worried world with her downtrodden, mopey attitude in Inside Out, the widely popular animated film from Pixar and Disney. She's relatable, helping us to connect with all of our bouts of tears, sour attitudes, and blue feelings—and this Halloween, you can embody Sadness with this easy DIY makeup tutorial via Rotoscopers.

Practically every smartphone comes with a built-in camera app, but these apps are generally created by the device's manufacturer. And let's face it, manufacturers are hardware companies first and foremost, so they don't always produce the best software.

Step 1: Draw Horizontal Lines for Uniform Size Overall Hi, This is a tutorial video to write your name in Graffiti.

Easy Square Knot Bracelet with beaded lines. To make this bracelet you only need to know how to make a square knot. This is a good bracelet for beginners in macrame.

What Is IPython? IPython is a richly featured replacement for the standard python interpreter. It offers a wider range of functionality, that the standard

Welcome back, my greenhorn hackers!

Getting on the phone for customer service can be extremely frustrating. First you've got to find the correct phone number for your region (good luck trying to get customer service from a sales department), then you have to listen to the annoying automated system to navigate your way to the department you want. More often than not, you'll be stuck with some elevator music while you wait to speak to an actual human.

If you've ever attempted to report a bug to a developer, no doubt you've heard the response, "Get a logcat." This is infinitely important to a developer because of the fact that a logcat captures a full report of every command that was recently executed on your Android device, and it allows them to see exactly where something went wrong.