Phone numbers often contain clues to the owner's identity and can bring up a lot of data during an OSINT investigation. Starting with a phone number, we can search through a large number of online databases with only a few clicks to discover information about a phone number. It can include the carrier, the owner's name and address, and even connected online accounts.

Cross-site scripting is one of the most common vulnerabilities found on the web today, with repercussions of this type of flaw ranging from harmless defacement to sensitive data exposure. Probing for XSS can be tedious and time-consuming for an attacker, but luckily there are tools available to make things a little easier, including Burp Suite, Wfuzz, and XSStrike.

With just one line of Ruby code embedded into a fake PDF, a hacker can remotely control any Mac computer from anywhere in the world. Creating the command is the easy part, but getting the target to open the code is where a hacker will need to get creative.

Web 2.0 technology has provided a convenient way to post videos online, keep up with old friends on social media, and even bank from the comfort of your web browser. But when applications are poorly designed or incorrectly configured, certain flaws can be exploited. One such flaw, known as CSRF, allows an attacker to use a legitimate user's session to execute unauthorized requests to the server.

If you need to hack an Android device, try a remote administration tool. Known more familiarly as a RAT, there are open-source RATs that are barebones and exorbitantly priced RATs that are more polished. There are also low-cost and polished RATs that aren't intended to be RATs at all, such as Cerberus, an anti-theft solution available right on Google Play.

If you're using a mobile device, it's a pretty safe bet that your apps are sending lots of information back and forth from their servers. To make sure there is no inappropriate data collection going on, it's worth setting up a web proxy to spy on this traffic, so you know exactly which apps are "phoning home" and when.

We need to take our privacy and security much more seriously. Whether it's malware-infected apps or the mishandling of our data by companies like Facebook, there are threats all around us in this digital world. Fortunately, some smartphones are simply designed to protect us better.

As cheesy as it sounds, #HODL became a thing for a reason. A lack of discipline when dealing with cryptocurrencies can lead to impulse buys and panic selling, and ultimately, depleted funds. Luckily, Coinbase has a way to safeguard your cryptocurrency savings to not only protect them against thieves, but to also help you resist the urge to sell off your investments.

Privacy and security go hand in hand, especially for smartphones. When it comes to privacy, you decide what personal information about yourself is out there to discover. Security, on the other hand, is all about enforcing those privacy decisions.

Your smartphone stays with you everywhere you go, so it's only a matter of time before you spill coffee all over it or drop it on the ground. For some of you, it has already happened, perhaps even multiple times. That's why we thought it was important to find out which flagship phones are the most life-proof.

Welcome back, my tenderfoot hackers! Generally, you will want to perform a vulnerability scan before doing a penetration test. Vulnerability scanners contain a database of all known vulnerabilities and will scan your machine or network to see whether those vulnerabilities appear to exist. If they do, it is your job to test whether they are real and can be exploited.

Welcome back, my tenderfoot hackers! Well, the first season of Mr. Robot just ended and Elliot and fsociety successfully took down Evil Corp! They have effectively destroyed over 70% of the world's consumer and student debt! Free at last! Free at last! Of course, global financial markets crashed as well, but that's another story.

Downloading YouTube videos for offline use to watch later has always been a problematic endeavor. Dedicated third-party apps don't last long in the App Store, web-based converters aren't very functional on mobile, and rogue apps outside the App Store are tricky to sideload and open up the possibility of vulnerabilities. But that doesn't mean you still don't have a few good options.

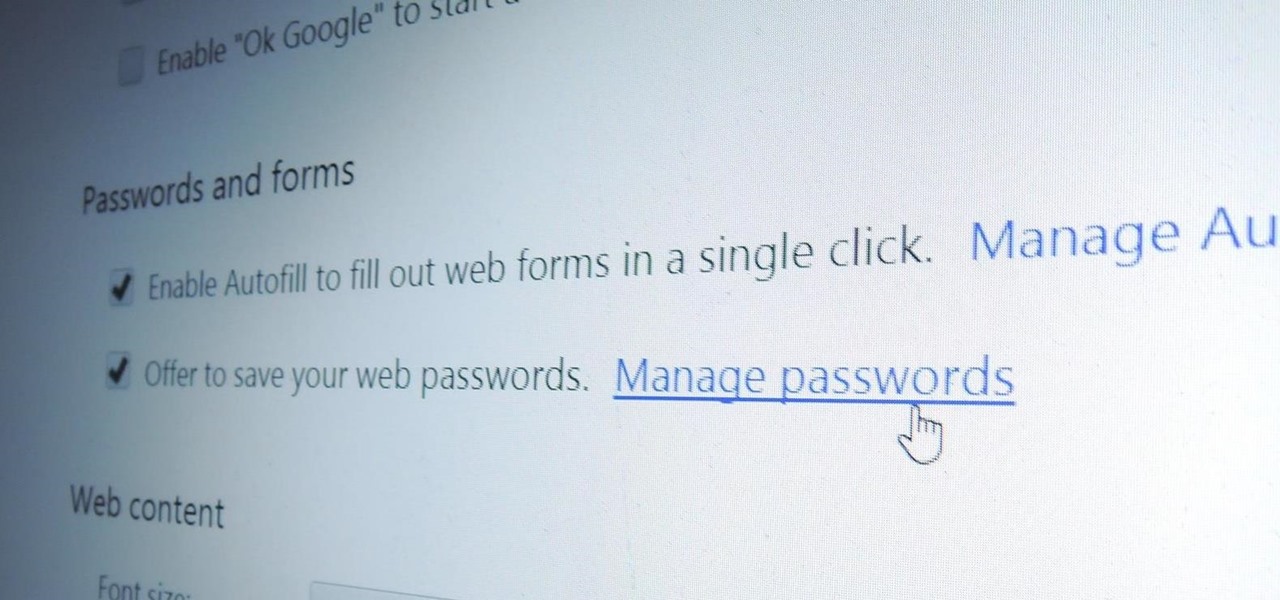
Chrome, Firefox, and Safari all provide built-in features that allow you to save your username and password for your favorite sites, making the process for entering your credentials a breeze when you revisit them.

As I've explained before, black app backgrounds save you a bit of battery life on your Samsung Galaxy S5. This is because the AMOLED display on your S5 does not have to power pixels or a backlight for portions of the screen that are black.

With a root bounty of over $18,000 up for the taking, developers were highly motivated to get the AT&T and Verizon Wireless variants of the Samsung Galaxy S5 rooted. Legendary hacker George Hotz, aka Geohot, has won the race and can now step up to claim his prize.

A friend of mine has a crazy amount of Reddit karma and gold, and yesterday he let me in on his secret. This person, who will remain unnamed for obvious reasons, created a Python script called Reddit Karma Crawler that finds rising posts before they get too popular.

Welcome back, my novice hackers! There are SOOOO many ways to hack a system or network, which means you need to think creatively in order to be successful.

From personal photos and videos to online banking passwords saved in your web browser, your phone has all kinds of sensitive data that needs to be protected. One of the best things you can do for your Samsung Galaxy S4's data is have a lock screen with a hard-to-guess PIN or password.

TouchDevelop is a browser-based programming tool that allows anyone to build your own Windows 8 apps directly from any touchscreen device, including iPad, iPhone, Windows Phone, Android, PC and Macs. Once the script is created and the app proves to work, it can be placed in the Windows Store for free or purchase.

People are always looking for ways to save money, and for the most part, saving money and cheating the system are synonymous when it comes to things like free internet access. Practically every new gadget is capable of connecting to the web, which means more and more people are looking for ways around those hefty internet bills.

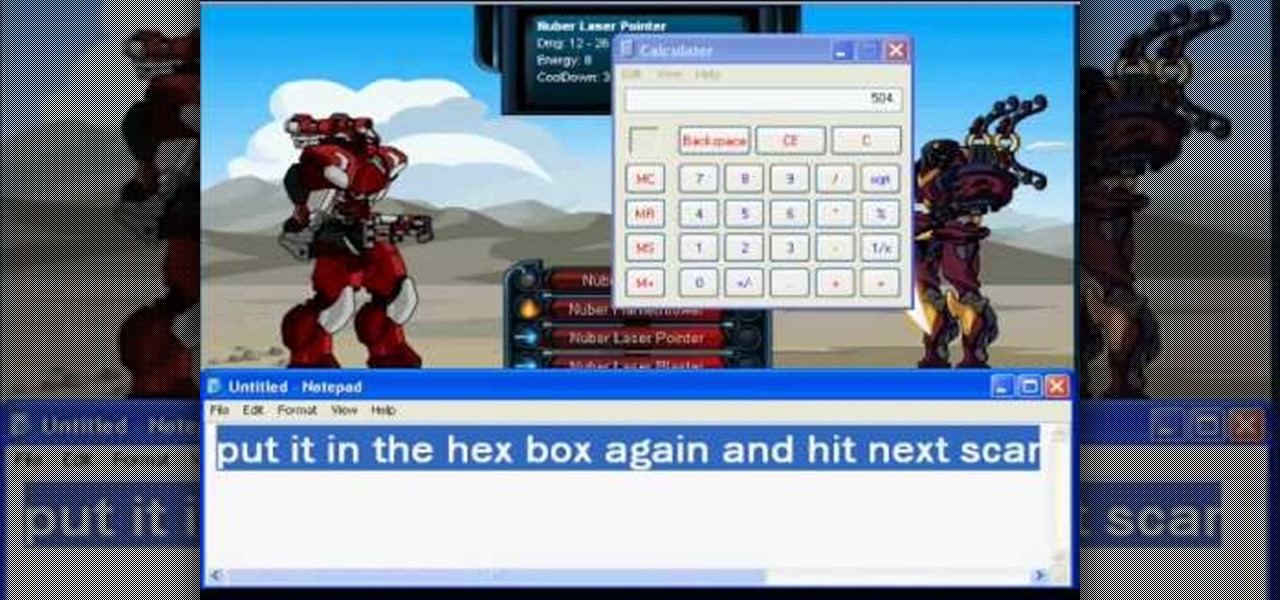
Be careful, because you could get banned if you get caught using Cheat Engine on this game! Make sure that you have the most current version of the program, and are playing your game in a browser like Mozilla Firefox.

You can hack into nearly any Facebook or Flash based game on the Internet - no cheat codes or special strategies needed. All you really need is the free game hack program Cheat Engine, and a compatible browser like Firefox.

This tutorial assumes you already have Cheat Engine (version 5.5. works best) and a CE compatible browser, and that you want to rapidly increase your levels within the game DragonFable. If that's all true, then watch this video and find out how!

It doesn't matter how tough the monster is you're facing, you'll be able to take them down completely with just one hit! All you need is Cheat Engine (version 5.4 or 5.5) and a compatible browser to execute this hack.

My Empire is a fun little Flash game you can play directly from your browser - and if you're looking for ways to advance faster in the game, there's always Cheat Engine. This tutorial shows you how to hack the game for more gold coins!

With Cheat Engine, you can hack nearly browser based or PC game. This tutorial shows you all the nifty things this program can do, like giving yourself infinite health, all the special powers in the game or other easy hacks.

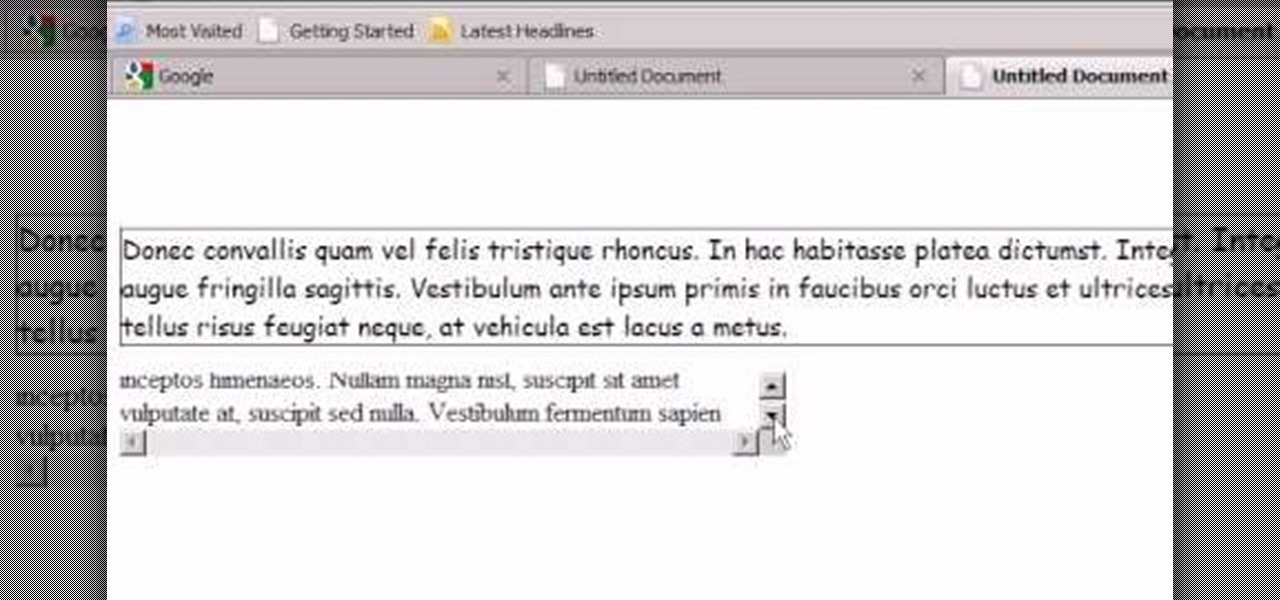
When you load Firefox, you're automatically taken to whatever homepage you've set up, or the automatic homepage. But what if you wanted to make a couple home pages? How about three or four? Well, you can, and this video will outline the process of setting up multiple home pages in Mozilla Firefox.

Have you zoomed way in to read a poorly-made webpage in the browser on your Mac and left yourself with no idea how to return the page to normal size? This video will tell you that all you need to do is hit Apple-0 and you're set.

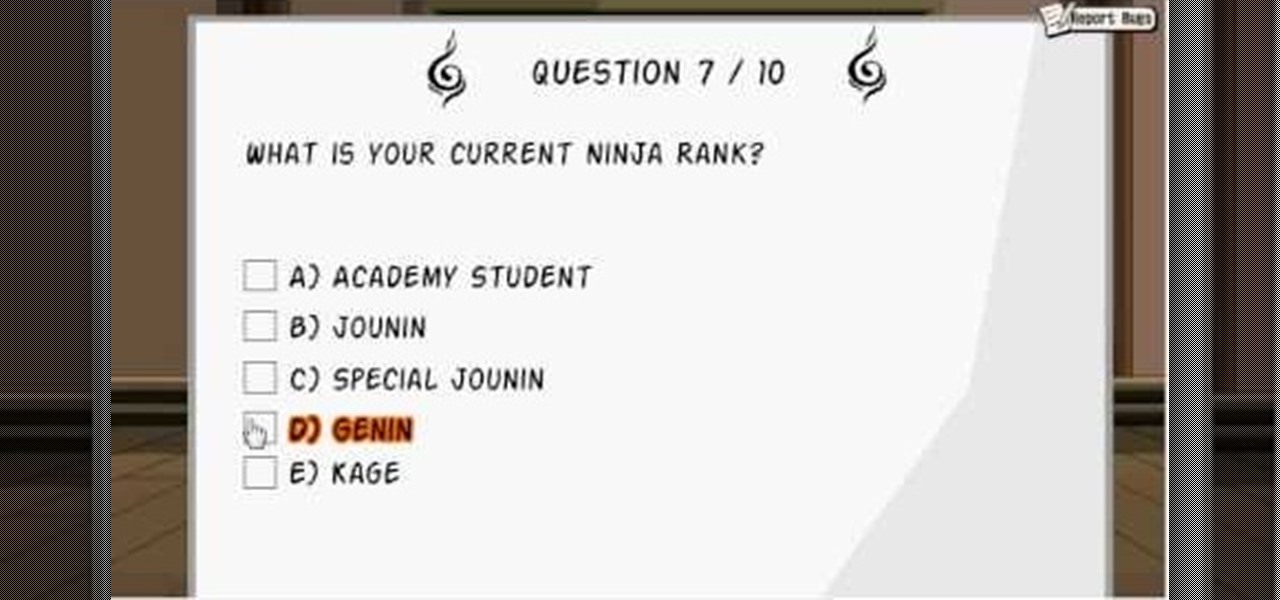
The chunin exam. It's one of the hardest parts of Ninja Saga. Can you pass the test? Or do you need a little help on this exam?

Watch this video tutorial to learn how to level hack Restaurant Life (12/05/09). 1. Open RL and Cheat Engine 5.5, then point CE 5.5 to the process of your browser.

We look at a nice and easy to use software on a modified Firefox browser where you can surf anonymous via the tor network.

Step1. First of all you need to remove all the borders. Scroll up and then select all the text lines that have 'border' mentioned and then delete them.

Disk space is a valuable commodity on your PC, and if you're running low, it's time to sell some of that unneeded property! This video shows you the steps to freeing up space on the hard drive of your Windows XP or Vista computer. There are many areas in Windows from which you can delete temporary files and hence, decrease your overall disk usage.

Instagram is one of the hottest mobile apps to date, yet they have no way to upload photos straight from your computer. You can log into the Instagram web app to like and comment on photos in your feed, but that's about it. Fortunately, there are third-party apps that let you do more on Instagram from your Mac or Windows computer, so you can enjoy Instagram pics on the big screen instead of your tiny iPhone or Android device.

So, you're browsing the web on your iPhone using Safari, and you come across a picture you really want to keep forever and ever… what do you do? You can save it directly to your phone! But how do you download that web image? Best Buy has answers. The Best Buy Mobile team explains how simple it is to save web images from Safari on your Apple iPhone.

If your not sure how to steam your media files to your Playstation3 this video will explain three different ways to achieve just this. Your options will include using a thumb drive, a personal web server or get the appropriate software.

In this brief video tutorial, you'll see how to properly use Agilent's InfiniiMax Active Probes for oscilloscopes, with multiple probe heads to connect to your high speed signals under various probing use models. First, begin by learning to use Agilent's Browser Probe Head under both handheld and probe stand use models. Also, see the use of their Solder-In Probe Head and the Socketed Probe Head. Then they conclude by showing how to use the SMA Probe Head.

This tutorial demonstrates how to use Microsoft Internet Explorer and Mozilla Firefox. Learn more about web browsers in this free instructional video series.

Step by step instructions on Traktor DJ Studio 3 mixing software from DJ Beef from setting up the sound card,headphones, using FX's, looping, browser controls, pitch bend, sync, and more.