Convenience is a big deal these days. You can buy single-serving or single-use sizes of just about anything, from fruits and vegetables to sanitizing wipes, and, apparently, even bananas. Uhh, it already has a wrapper...

Using the Cydia App, you can delete individual calls in your recent caller list. This enables you to delete single calls, line by line, instead of having to clear your entire recent call list.

Improve you crocheting skills by making fun shapes. This how to video is a tutorial that will show you how to crochet a triangle with the single crochet stitch. Crochet several of them, bind them together and create larger handmade projects.

Improve you crocheting skills by learning decorative stitches. This how to video is a tutorial that will show you how to crochet a curly cue with single crochet stitches. Watch and see how simple it is to add even more personal touches to your work.

Improve you crocheting skills by learning different edging techniques. This how to video is a tutorial that will show you how to crochet a reverse single crochet edging. Watch, learn and maybe you can crochet your own decorative edgings.

This video is three slow motion vids of double clutch, single clutch and heel and toe. If you have a vague understanding of how to do these race driving techniques, but want to see a really clear, slowed down version of exactly what should happen, this video will really help.

Joanne and Lauren bring you a lesson from the MMA (Mixed Martial Arts) Girls series. In this video the sexy ladies demonstrate how to do the side control escape and maneuver to a single knee takedown.

Watch this instructional crochet video demonstrating a crochet circle worked into a single chain stitch.

Apple's macOS operating system is just as vulnerable to attacks as any Windows 10 computer or Android smartphone. Hacker's can embed backdoors, evade antivirus with simple commands, and utilize USB flash drives to completely compromise a MacBook. In this always-updated guide, we'll outline dozens of macOS-specific attacks penetration testers should know about.

The mere mention of "cupcake" conjures up visions of frosting-topped treats served to partygoers and birthday-havers by the dozens. After all, how many cupcake pans have you seen with less than 12 spots? Sixers are fairly common, yes, but what if you just want to bake one or two cupcakes to enjoy alone or with a pal?

Welcome back, my hackers apprentices! To own a network and retrieve the key data, we only need to find ONE weak link in the network. It makes little sense to beat our heads against heavily fortified systems like the file and database server when we can take advantage of the biggest weak link of all—humans.

After years of user complaints, Samsung is finally letting us remap the Bixby button without the need of a third-party app. The new feature requires One UI a simple app update to Bixby, but there's one major downside: Samsung won't let you remap the button to open other digital assistants like Amazon Echo, Microsoft Cortana, and Google Assistant. Luckily, there's an easy workaround.

So, you're scanning the internet for some cool articles to read during your lunch break and you come across something pretty interesting—"The 50 Most Incredible Things Every Person with a Brain Should Know." That sounds interesting, so you click, and boom, you are hit with the utterly obnoxious Page 1 of 50. Really?

Plagiarism is a serious offense, even if you are copying from the web. With this tutorial, learn how to cite websites properly using MLA format and avoid any trouble.

In iOS 13, Apple finally took the built in Files app from an extremely rudimentary file browser to a full featured app that can serve the needs of most any user. Among the new features is the ability to compress a file or series of files into a standard ZIP archive right from your iPhone.

On the surface, AppleCare+ seems like an expensive and gimmicky option to tack onto your already pricey iPhone 11, 11 Pro, or 11 Pro Max. Upon further inspection, however, you'll see that its seemingly expensive price tag is chump change compared to the fees you'll have to pay if you end up having to repair your premium device outside its one-year warranty.

Computer vision technology maker uSens, Inc. has unveiled uSens Fingo, a camera module that enables tracking of hand and head movements for PC-based, mobile augmented, and virtual reality platforms.

When using Linux, we often need to install new software, a script, or numerous large files. To make things easier on us, these files are usually compressed and combined together into a single file with a .tar extension, which makes them easier to download, since it's one smaller file.

Website Design Tutorial for Xara Web Designer learning how to switch between single page view vs. multi-page view. When working with your web design it is important to understand, which website design view is best for completing your project. This web design tutorial covers two of in my opinion the most important views for your web design work environment.

The 280-character limit for tweets on Twitter is double what it used to be back in the day, but it's still not enough to express in-depth thoughts, ideas, commentary, rants, blogs, stories, and the like. These tweetstorms, as they're called, are the reason why Twitter created its threads feature.

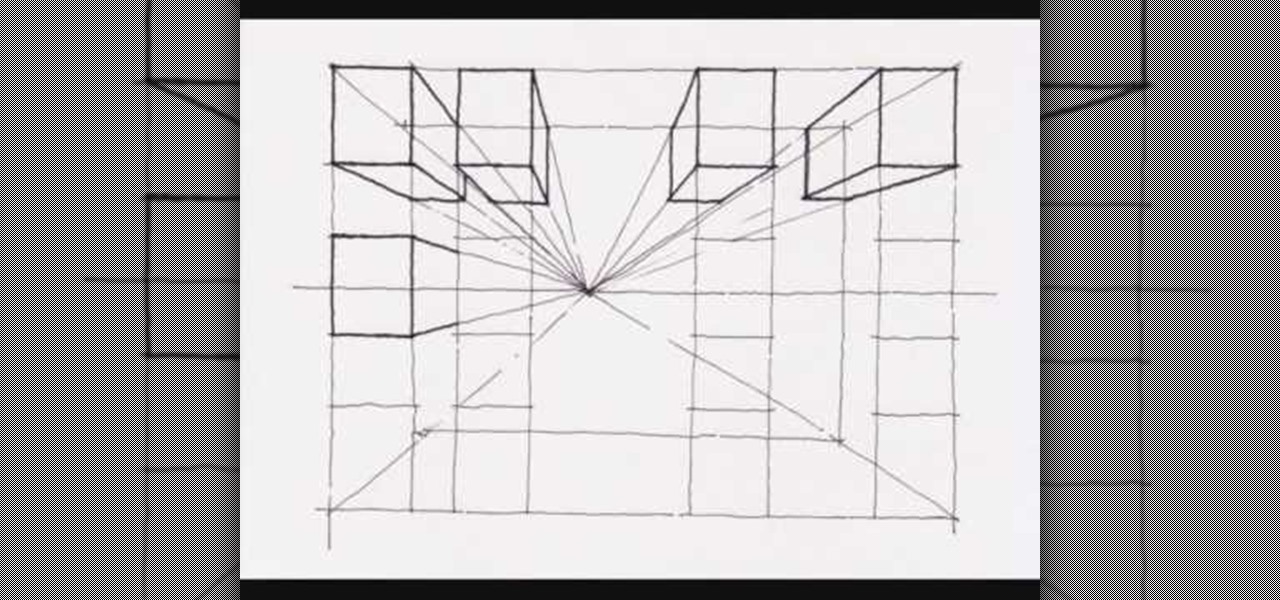
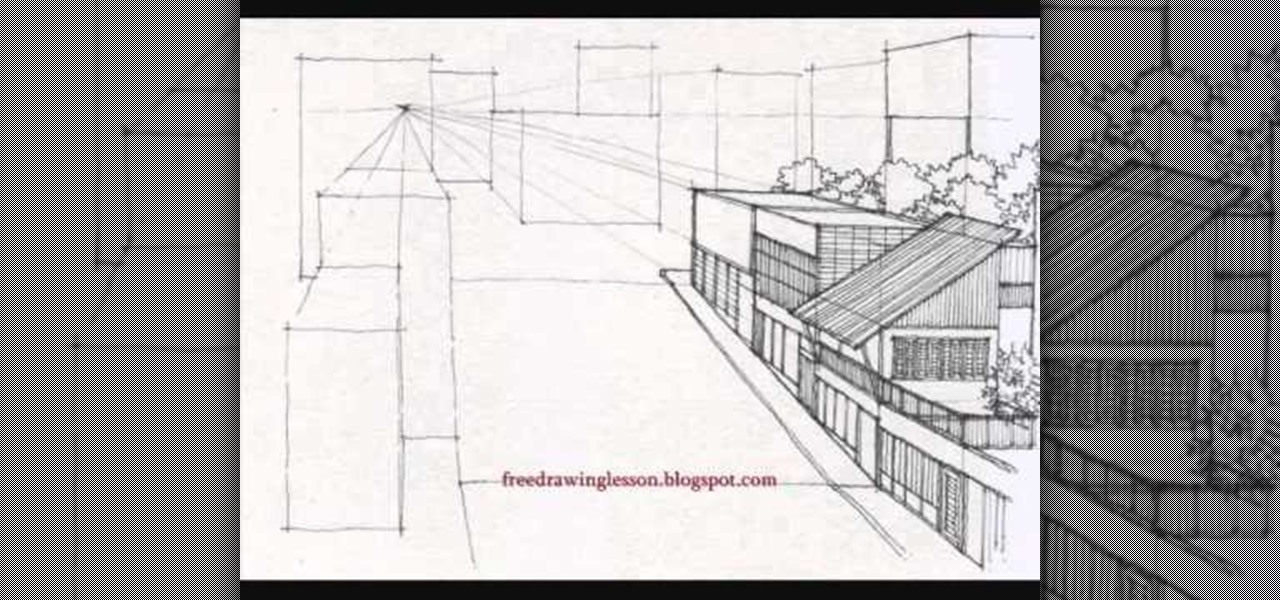
This video demonstrates how to create a one point perspective drawing. You begin by making a horizon line across your paper and adding diagonal lines from the corners which will all converge at a single point along your horizon line. You can then create boxes by creating squares or rectangles around the lines extending from the central point. The outer edges of your rectangle can further be connected to your single point in order to create a 3-dimensional shape for the boxes and cubes which y...

Artists discovered the almighty vanishing point during the early Renaissance and haven't stopped using it since. The genius of the vanishing point is that it gives a three dimensional quality to a two dimensional space, meaning increased depth perception and more believability.

In this video, Shirley shows her viewers an effective way to multiply your red fountain grass in order to create more grass from a single plant. After the growing season, find a large, overgrown patch of grass and use a shovel to dig out a section by the roots. After planting the grass in a pot, it is crucial that you shear the top of the plant so that the grass is only 4 to 5 inches tall. This will ensure that the plant focuses on growing roots rather than its blades at the moment. This meth...

This crocheting tutorial demonstrates how to do a chainless single crochet foundation. Foundation stitches replace the traditional foundation chain as well as the first row of stitches. It comes in handy when you don't know how many stitches you need to "cast on" for your project. The traditional method creates a tighter row. This method creates a stretchier row that will more closely match the rest of your rows. Watch this crochet how-to video to learn more about chainless crocheting.

Hacker's are always looking for new ways to exploit systems and exfiltrate passwords, even in hashed form. Sophisticated brute-force attacks powered by high-end GPUs can perform millions of password attempts per second. But Ubuntu and Debian users aren't completely helpless. There are ways to harden the hashed password to better defend against Hashcat attacks.

A powered-off MacBook can be compromised in less than three minutes. With just a few commands, it's possible for a hacker to extract a target's password hash and crack it without their knowledge.

Sometimes the best place to hide something is where people least expect it, so in this project, we're making a super secret safe that only you'll know about.

With technology giants like Apple and Google finally entering the fray, the move toward mass adoption of augmented reality is ramping up. Apple's ARKit and Google's ARCore will allow entirely new categories of apps to be made. Unfortunately, in a world of heavy competition, getting these two frameworks to work together wasn't a priority for either company.

For reasons unknown, Microsoft decided to change the way the Guest account feature in the new Windows 10 operating system works. In previous versions, the Guest account feature allowed you to set up a limited account for other users so they don't have access to your important documents and settings. Now, the process requires assigning an email to a new account and configuring share settings.

As far as wallets go, mine is as full as they come; think something like George Castanza's overstuffed wallet on Seinfeld. I've got receipts, pictures, and tickets jammed inside, but what takes up the bulk of the space are all of the cards—credit, debit, gift, rewards, customer loyalty... I've got pretty much any card you can think of squeezed in. While it is a strain on my rear end, there's nothing I can do besides keep some of the cards elsewhere. However, looking for them when I need them ...

Despite their awkward appearance, Apple's AirPods have become the earbuds of choice for working out, largely thanks to quality audio without any wires to tangle. However, at $159 to start, they aren't exactly for everyone.

A stager is a small piece of software that's typically used by malware to hide what's happening in the early stages of infection and to download a larger payload later.

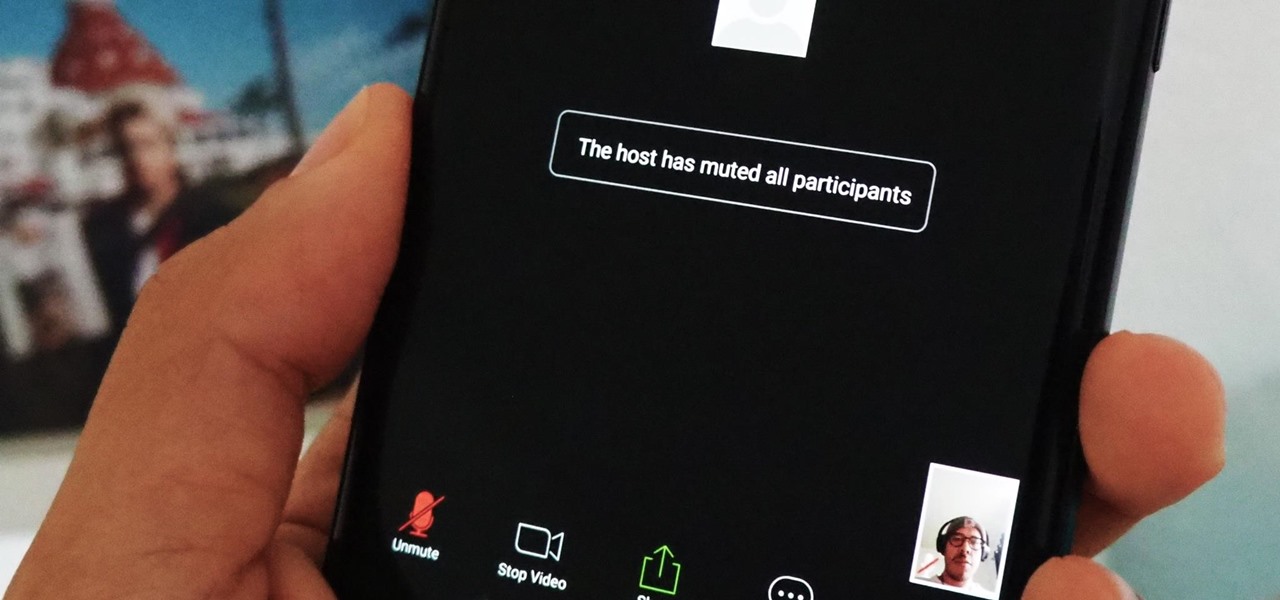
If you're using or need to use Zoom, the popular video teleconferencing service, you've almost certainly heard about "Zoombombing" by now. While Zoom has been adding security measures to address the problem, there are other things you can do to prevent or stop Zoombombers in their tracks so that your video meetings and chats go undisturbed and uninterrupted.

Apple has implemented a new sensor on the rear camera of its fourth-generation iPad Pro, and it's pretty exciting. It's called the LiDAR Scanner, a scanning "light-detection and ranging" sensor, and you may very well be acquainted with it if you follow any driverless car news. Will we also get it on the upcoming iPhone 12 Pro?

We've all been there — using Google Maps for navigation and waiting for the app to find our location. As we drive around, we keep hoping it will get a lock in time to make the next turn. Well in the US, we finally have a solution to this problem, and it's the OnePlus 7 Pro.

Backdooring a powered-off MacBook is easy when a few minutes of physical access is allowed. That attack works well if the hacker also shares a Wi-Fi network with the victim, but this time, I'll show how to remotely establish a connection to the backdoored MacBook as it moves between different Wi-Fi networks.

Single sign-on (SSO) lets users login across different sites without having to manage multiple accounts. I'm sure most of us appreciate the convenience of seeing "Sign in with …" buttons that let us login with a single username. Hackers, however, see a possible avenue for exploitation, and you'll soon learn how an attacker can exploit a SAML vulnerability to assume another user's identity.

Over the years, the internet has become a dangerous place. As its popularity has increased, it has attracted more hackers looking to make a quick buck. However, as our dependency on the web grows, it becomes increasingly difficult to sever all ties. This means we have to protect one of our weakest points, the password.

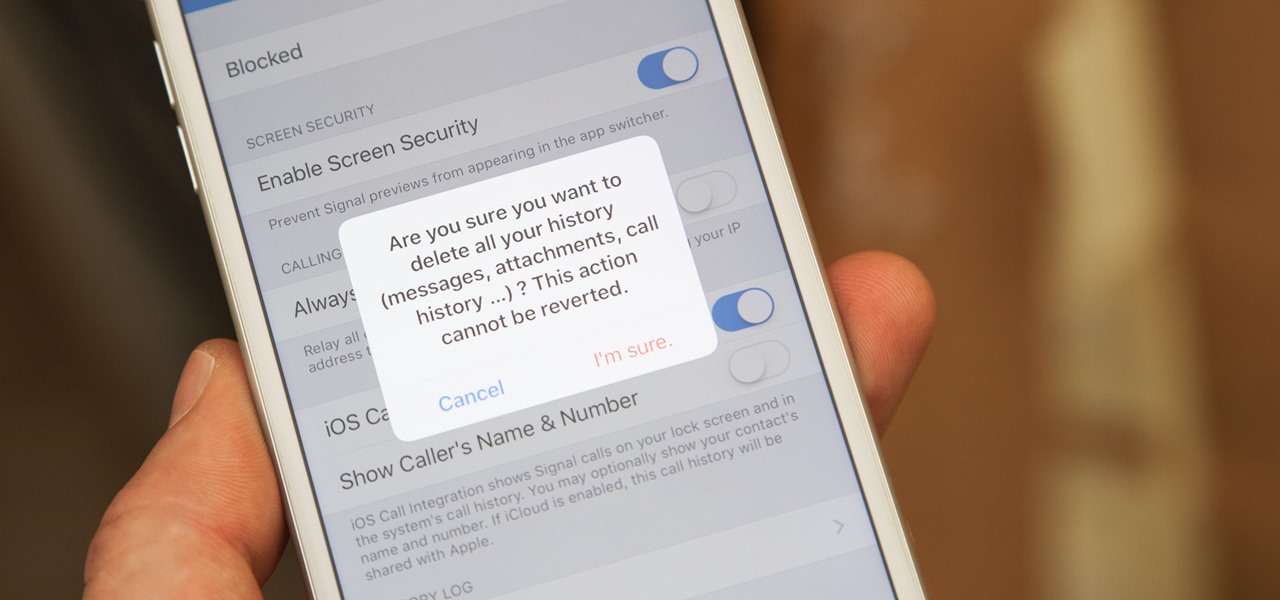
If thieves, hackers, law enforcement, or other would-be enemies should ever gain entry to your smartphone, they could also access conversations you've had in Signal Private Messenger. To better secure your encrypted communications, you can password-protect the whole app and its contents — but only on Android. Even then, it's necessary to perform data deletion on a periodic basis, if not immediately.

Often, the most frustrating part of crafting the perfect dinner is feeling like you have to clean every single pot and pan in your kitchen after cooking just one meal. With so many components, it can feel like each step of a single dish requires its very own pot.